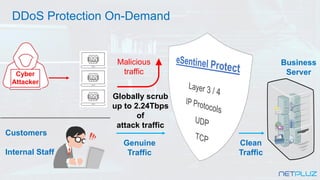
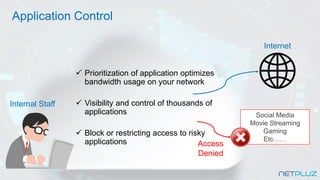
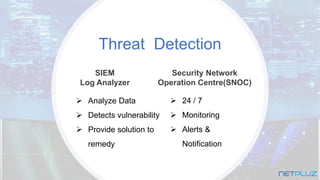
The document outlines the features of the Esentinel 360° managed cybersecurity integrated platform, highlighting its capabilities in attack prevention, including DDoS protection and various security features such as intrusion prevention and anti-virus. It emphasizes the system's 24/7 monitoring, customizable policies, and vulnerability assessment services, catering to businesses needing comprehensive cybersecurity support. The service is marketed at a starting price of $199 per month with added benefits like alerts, monthly reporting, and a focus on enhancing business security.