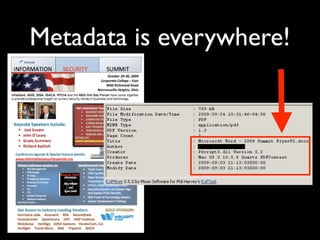
The document discusses open source intelligence (OSINT), focusing on methods for gathering, monitoring, and removing information related to companies from various online sources. It highlights the importance of understanding metadata, monitoring social media, and formulating an internet posting policy for employees. The document offers practical tools and strategies, as well as recommendations for effective monitoring and handling of online presence.