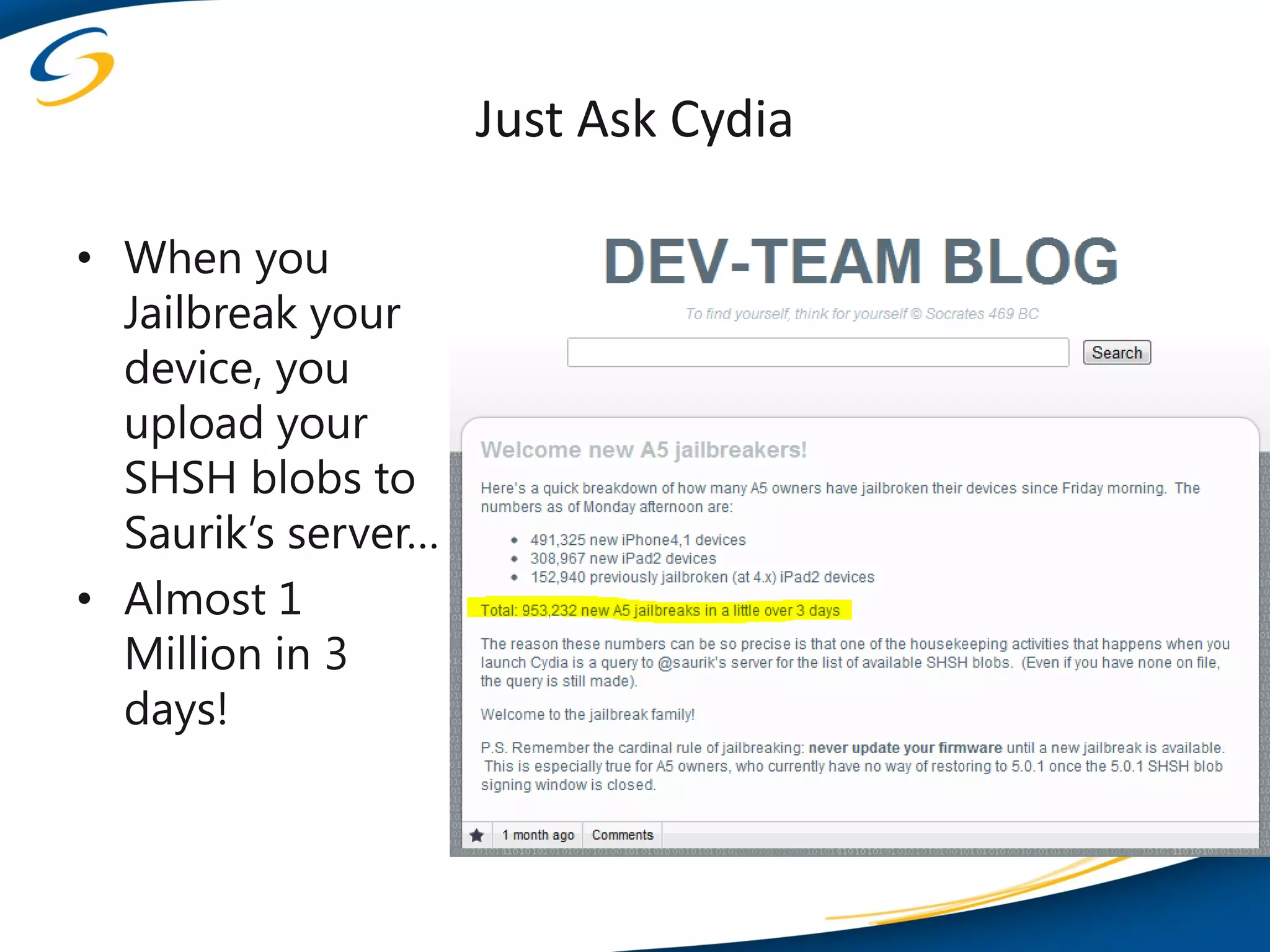
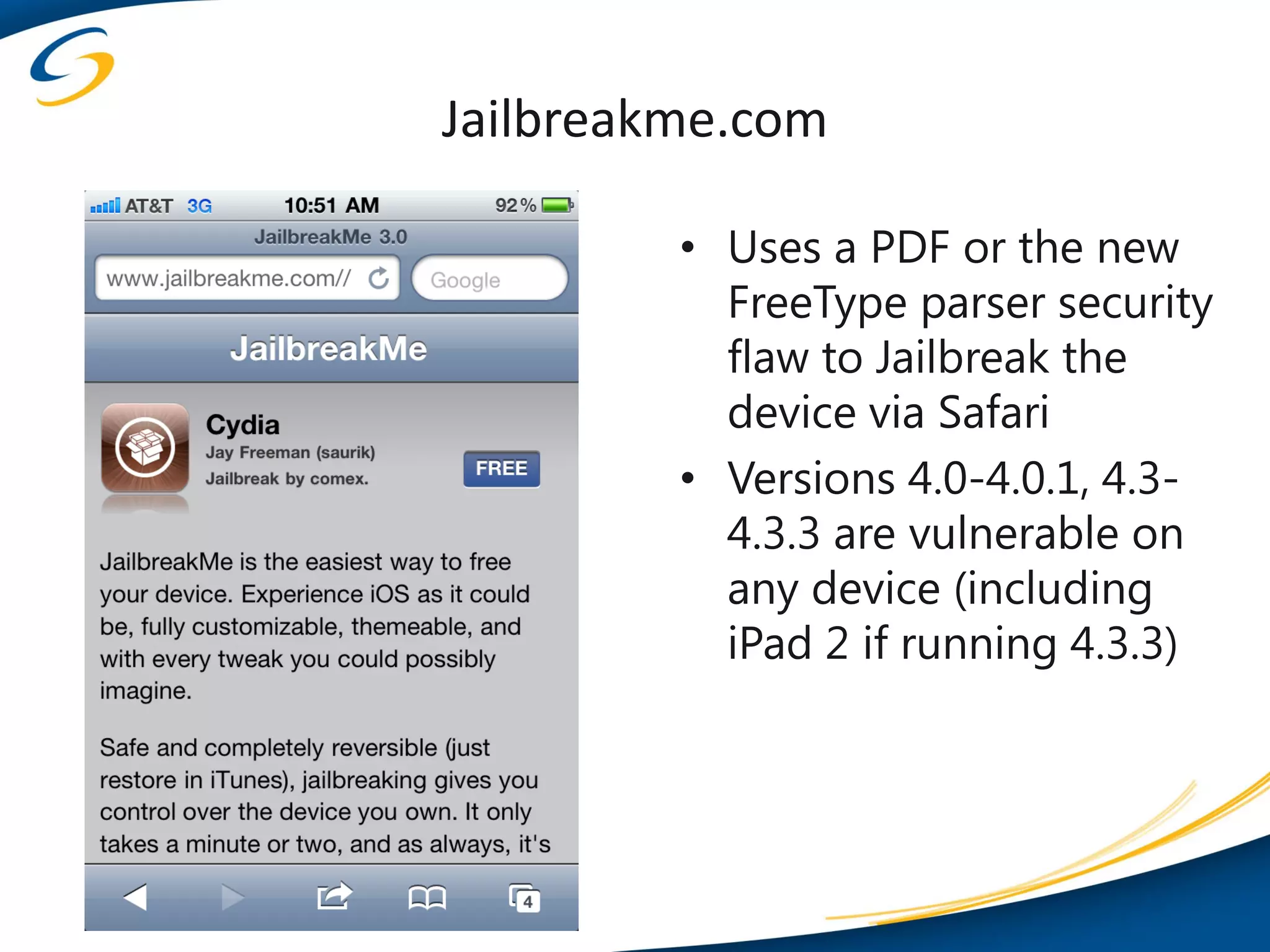
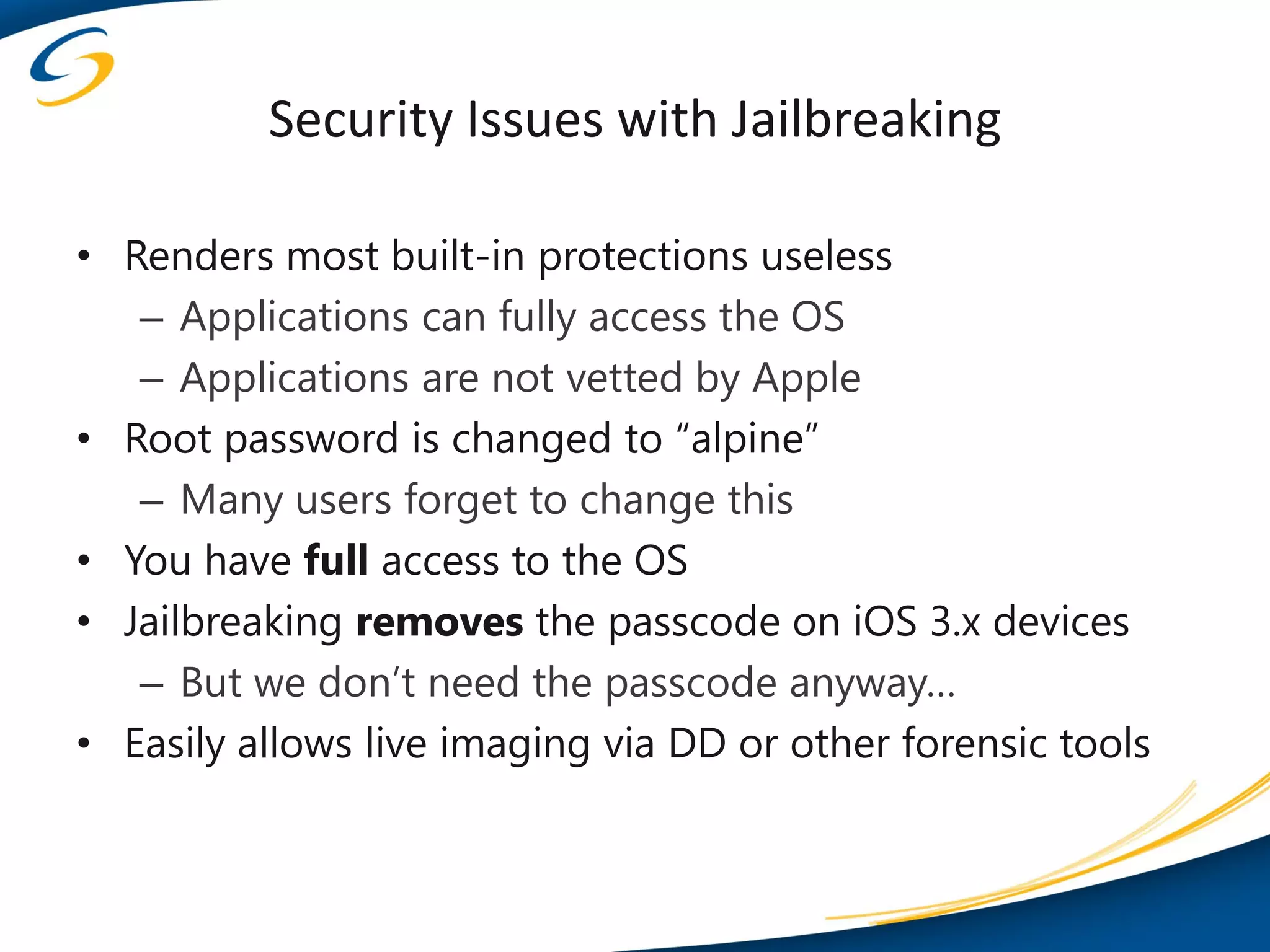
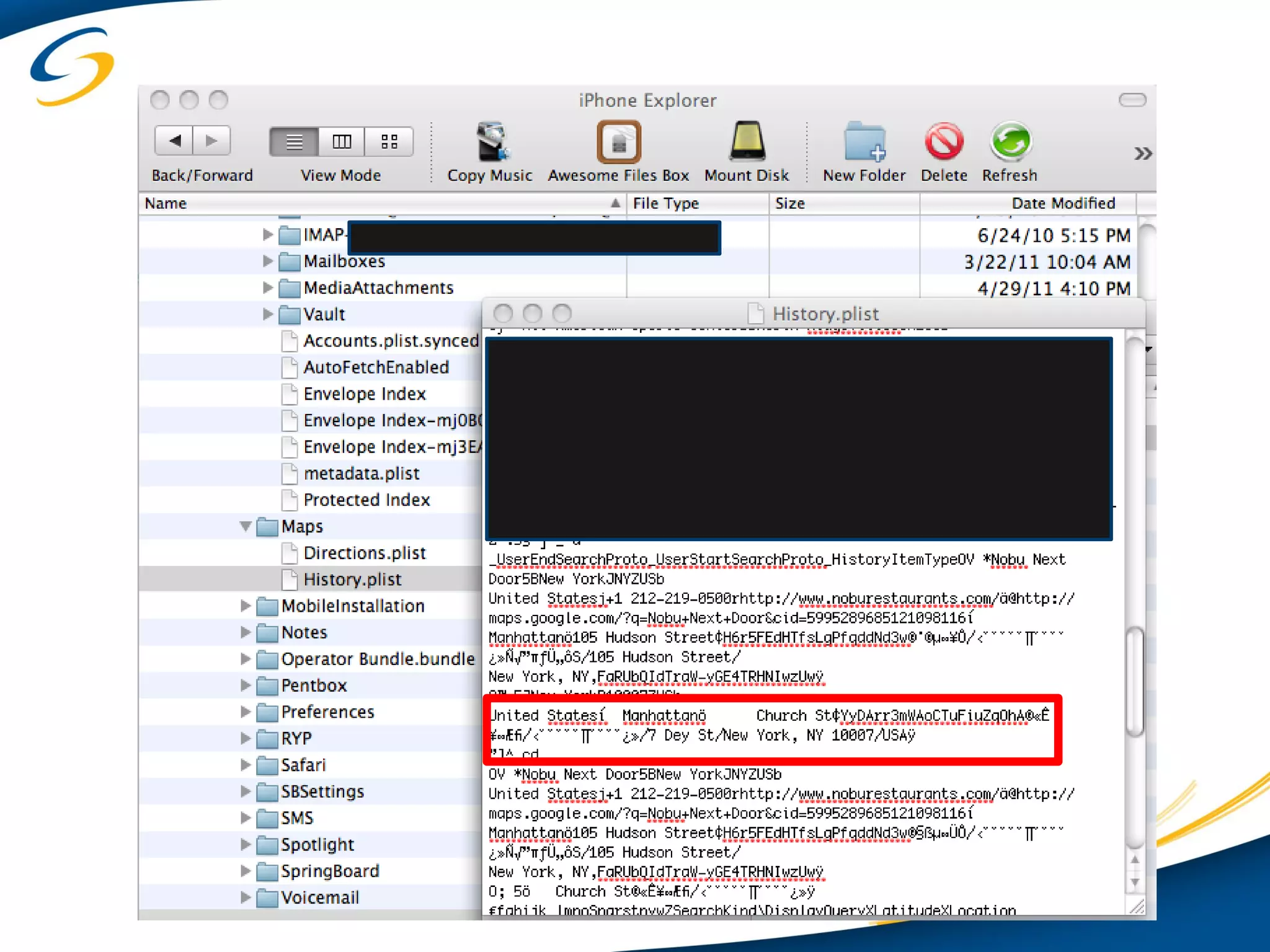
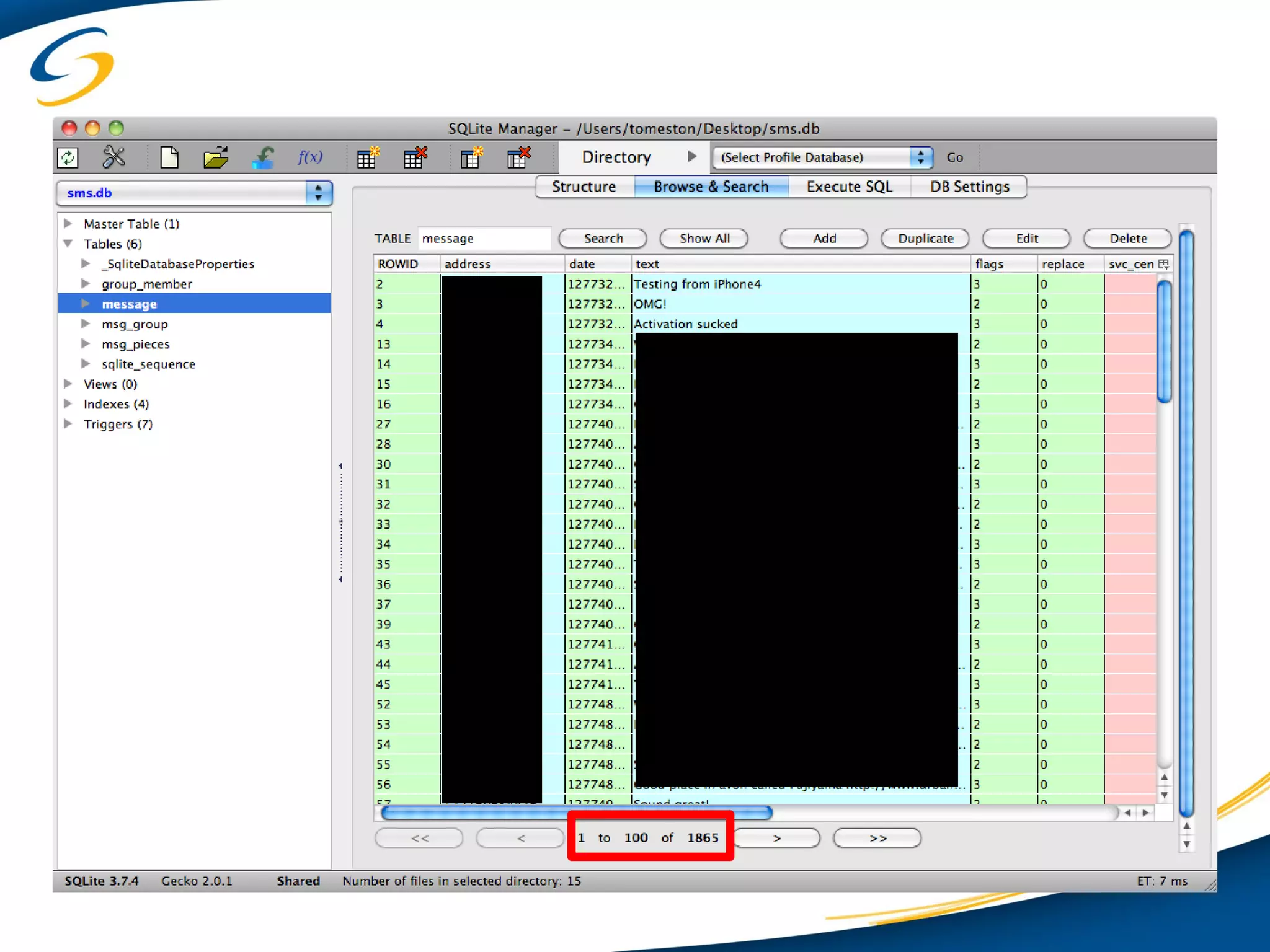
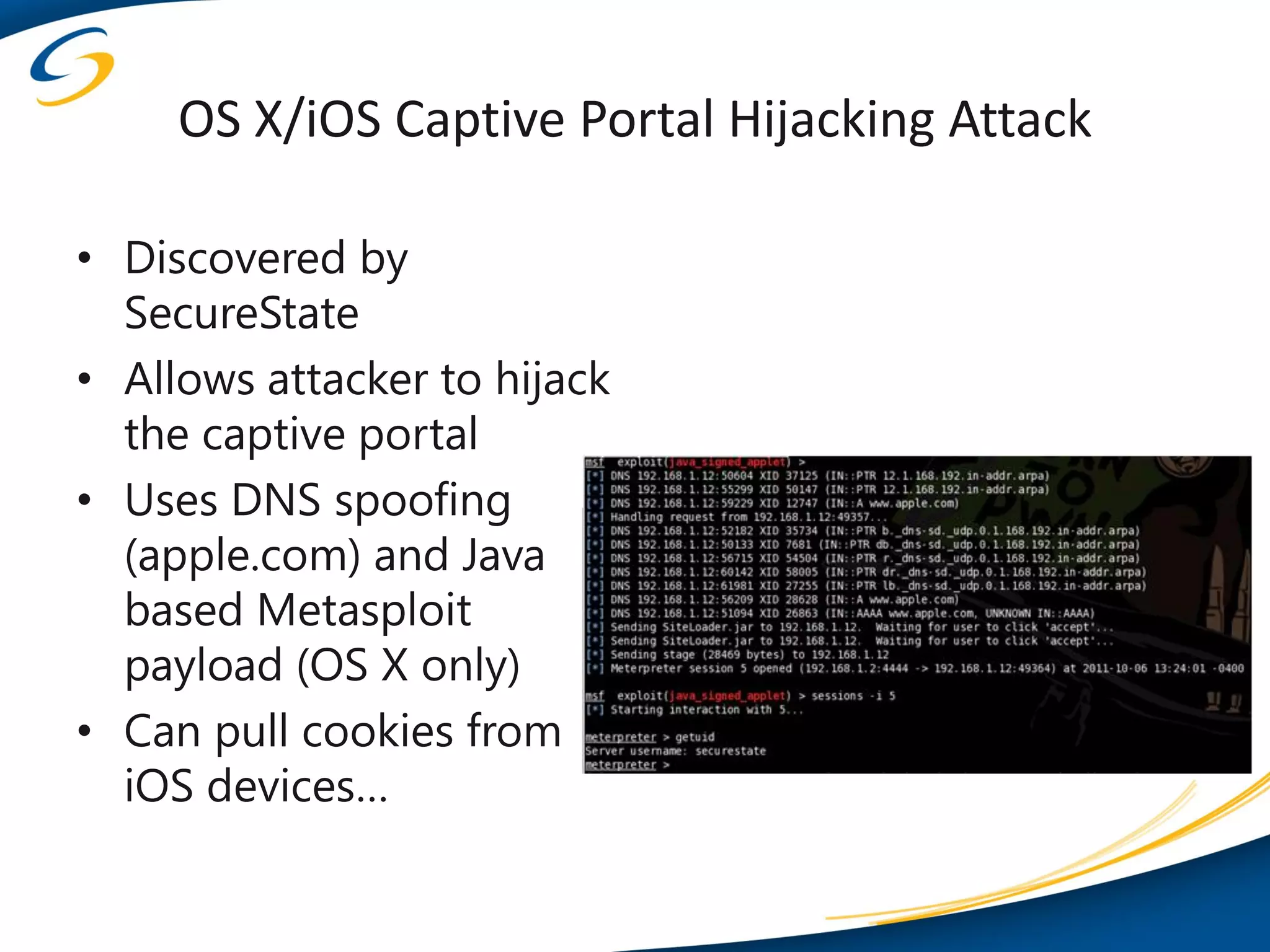
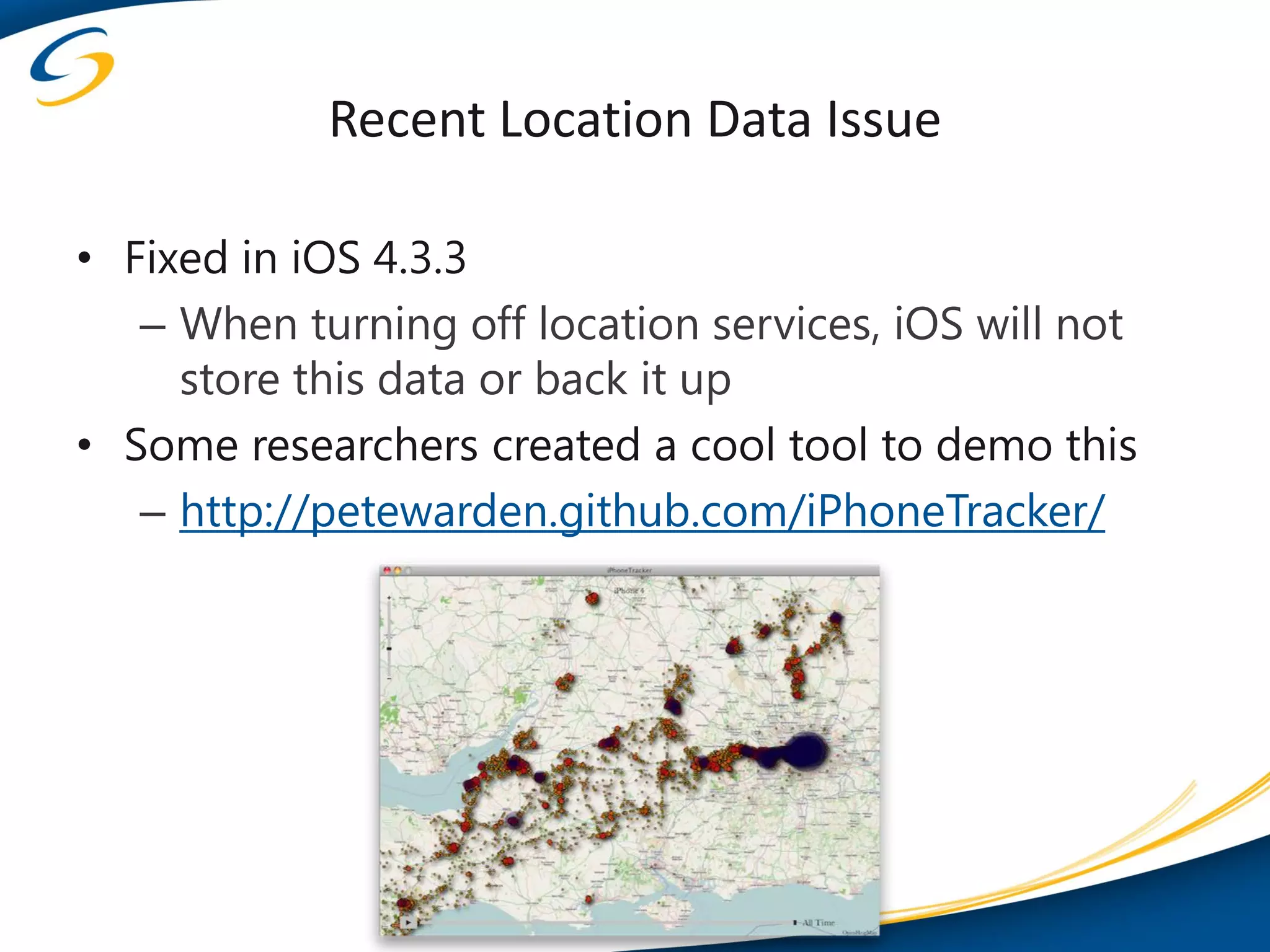
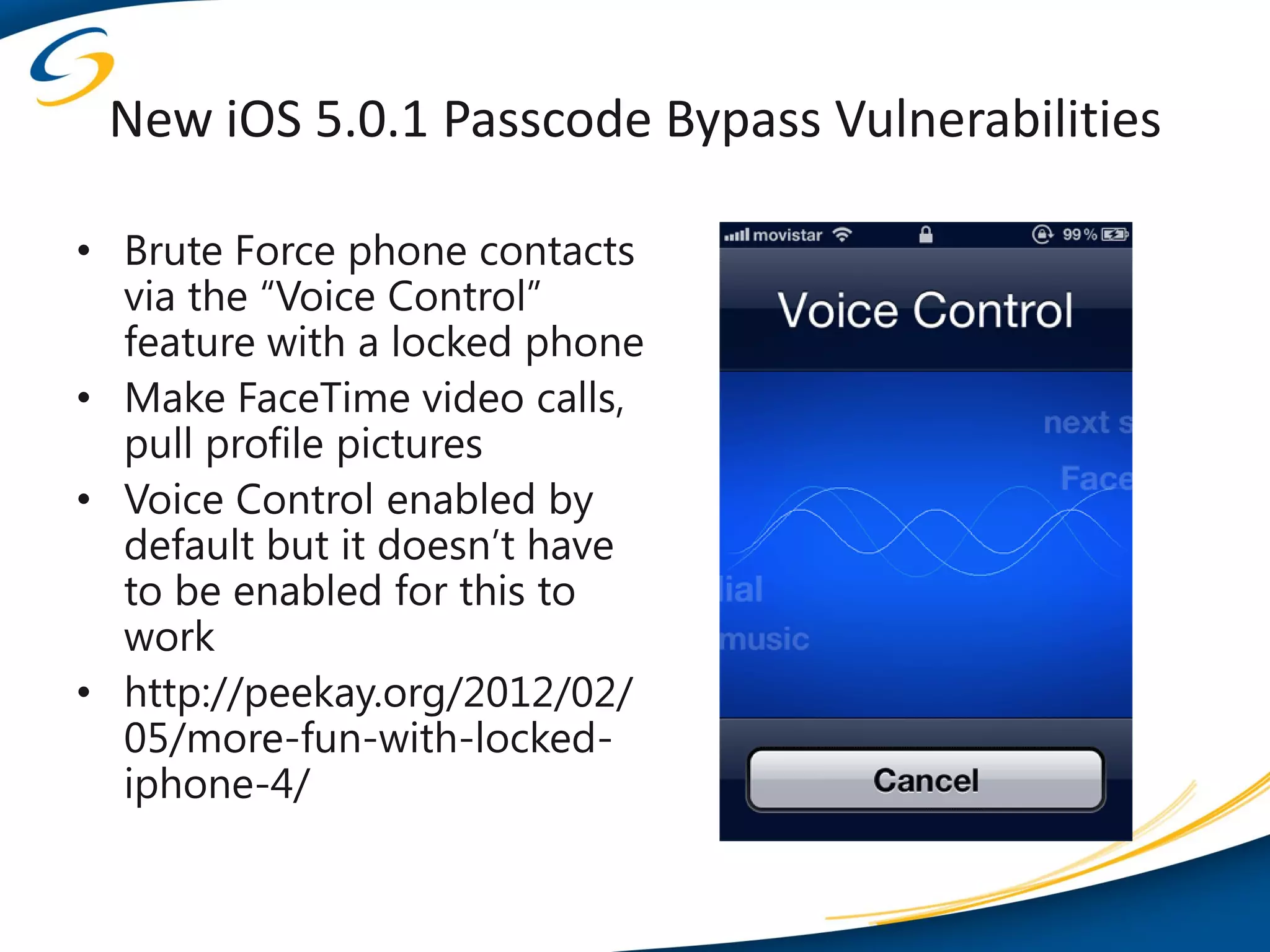
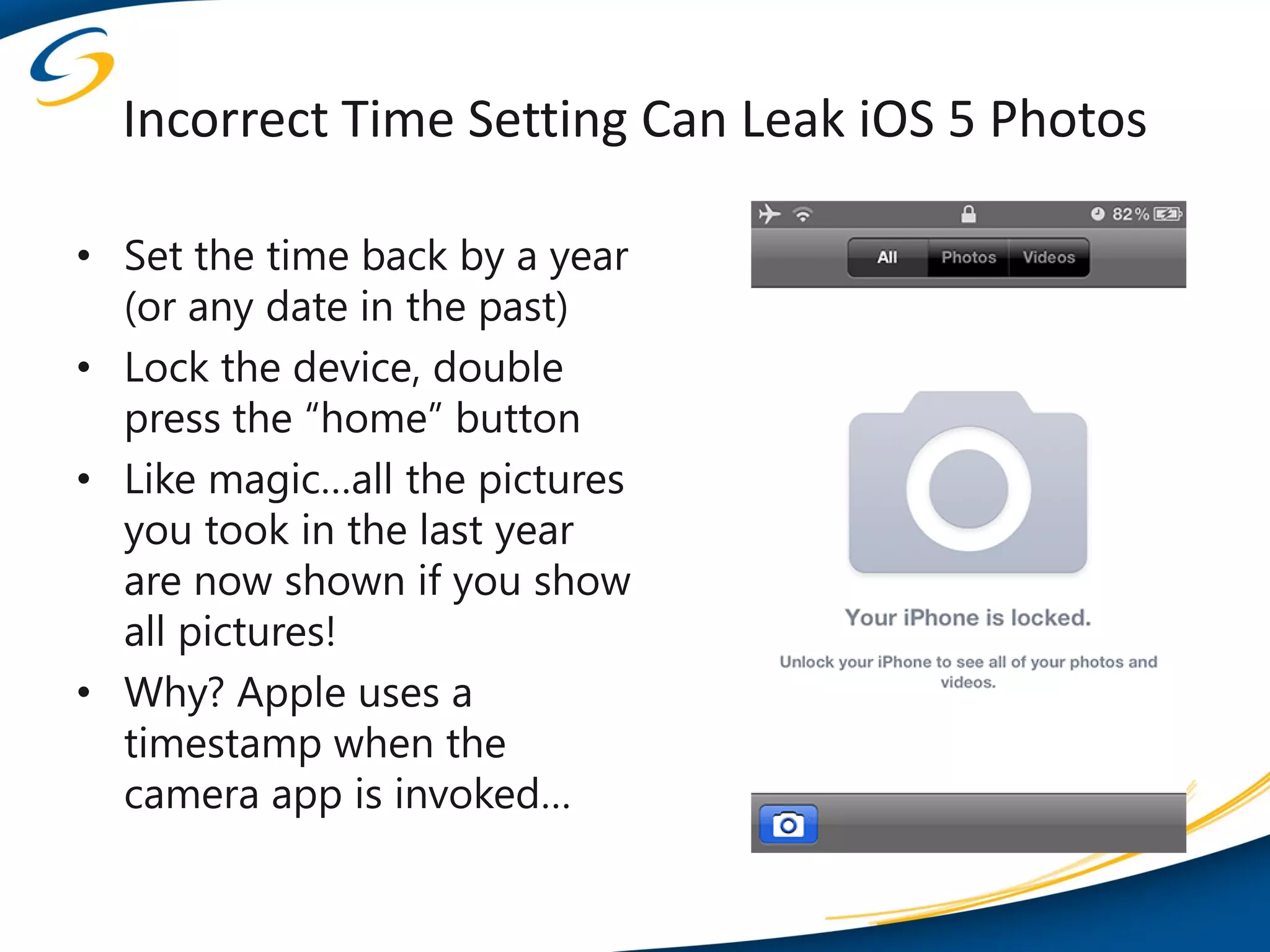
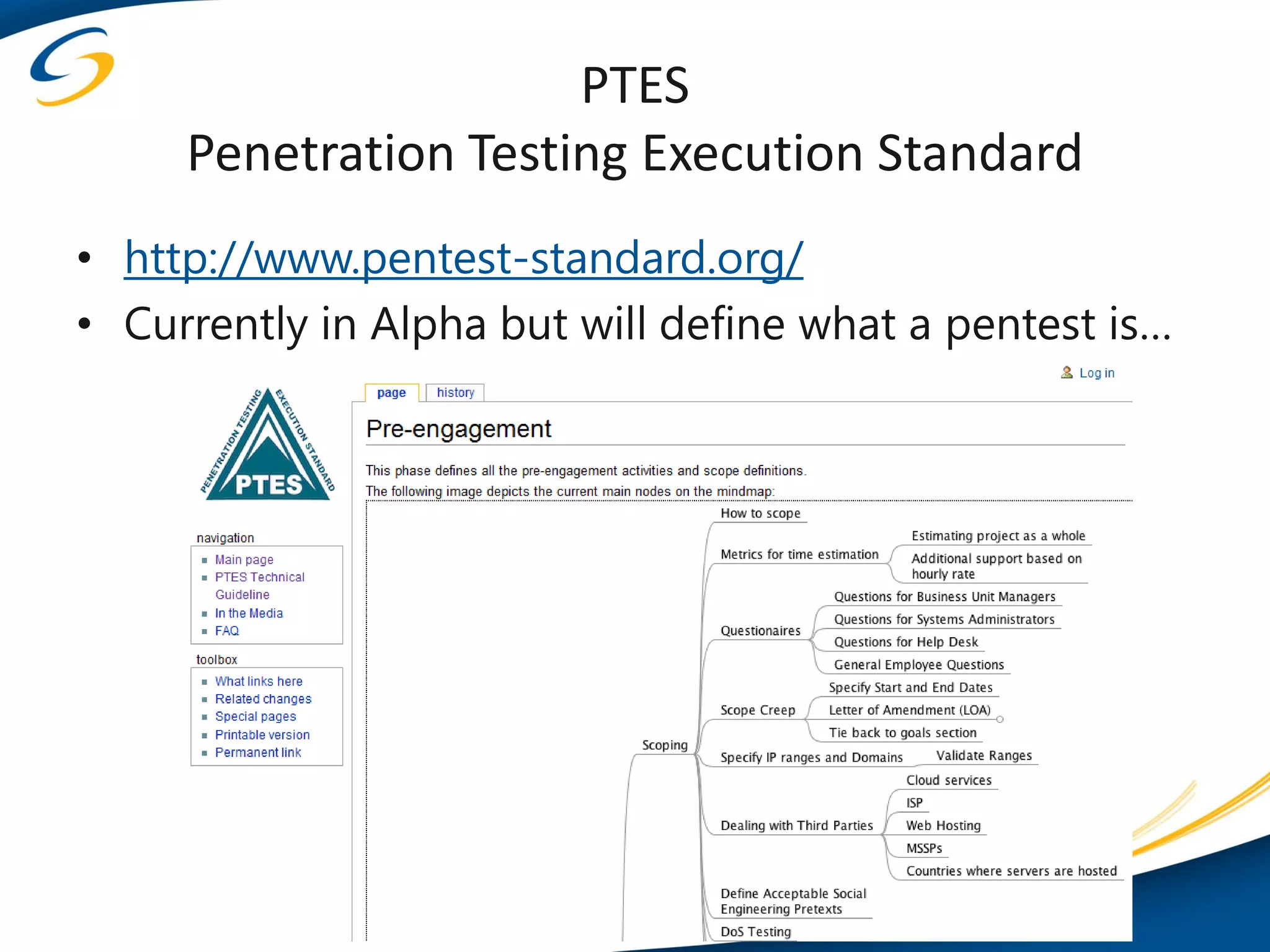
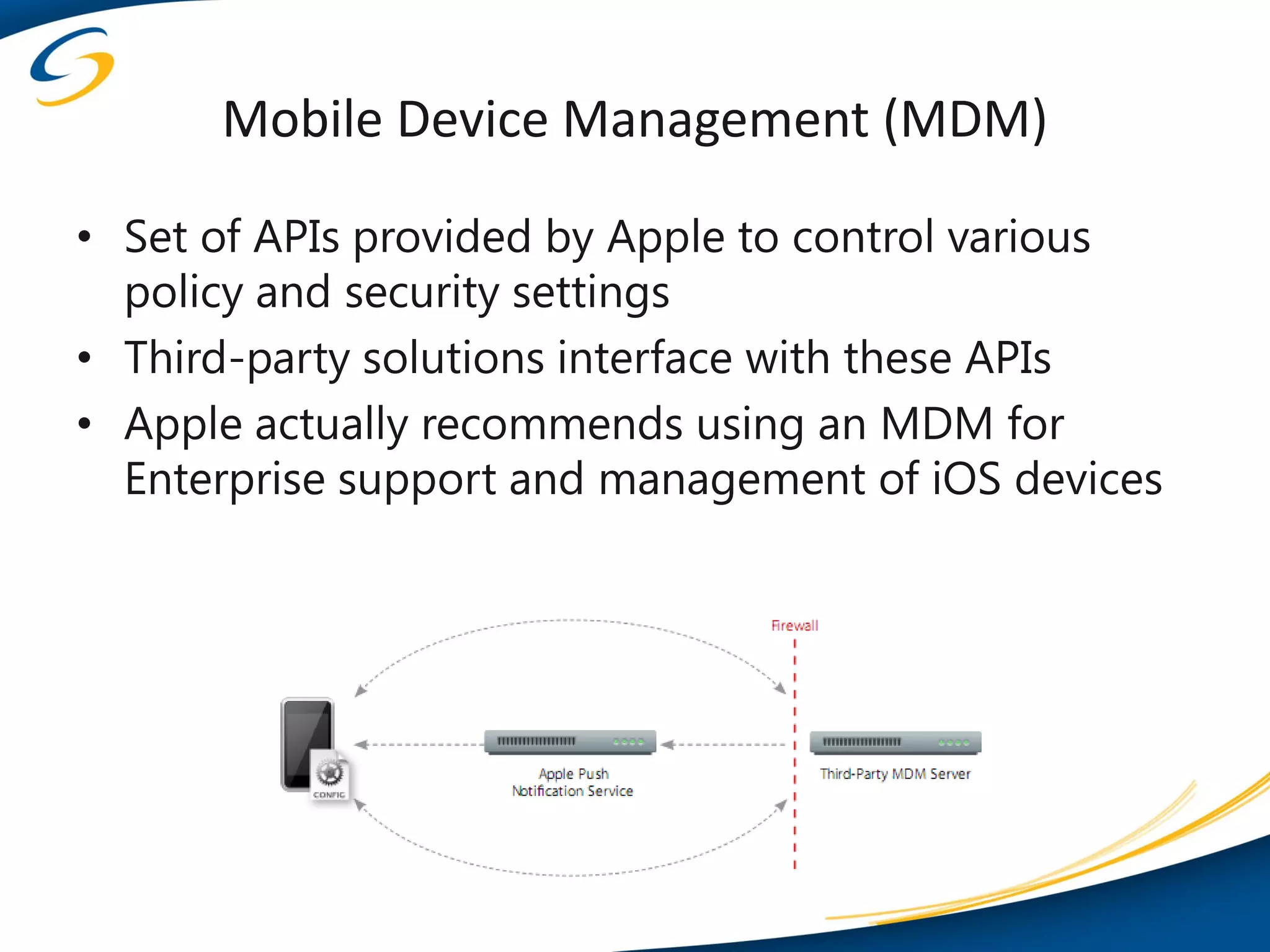
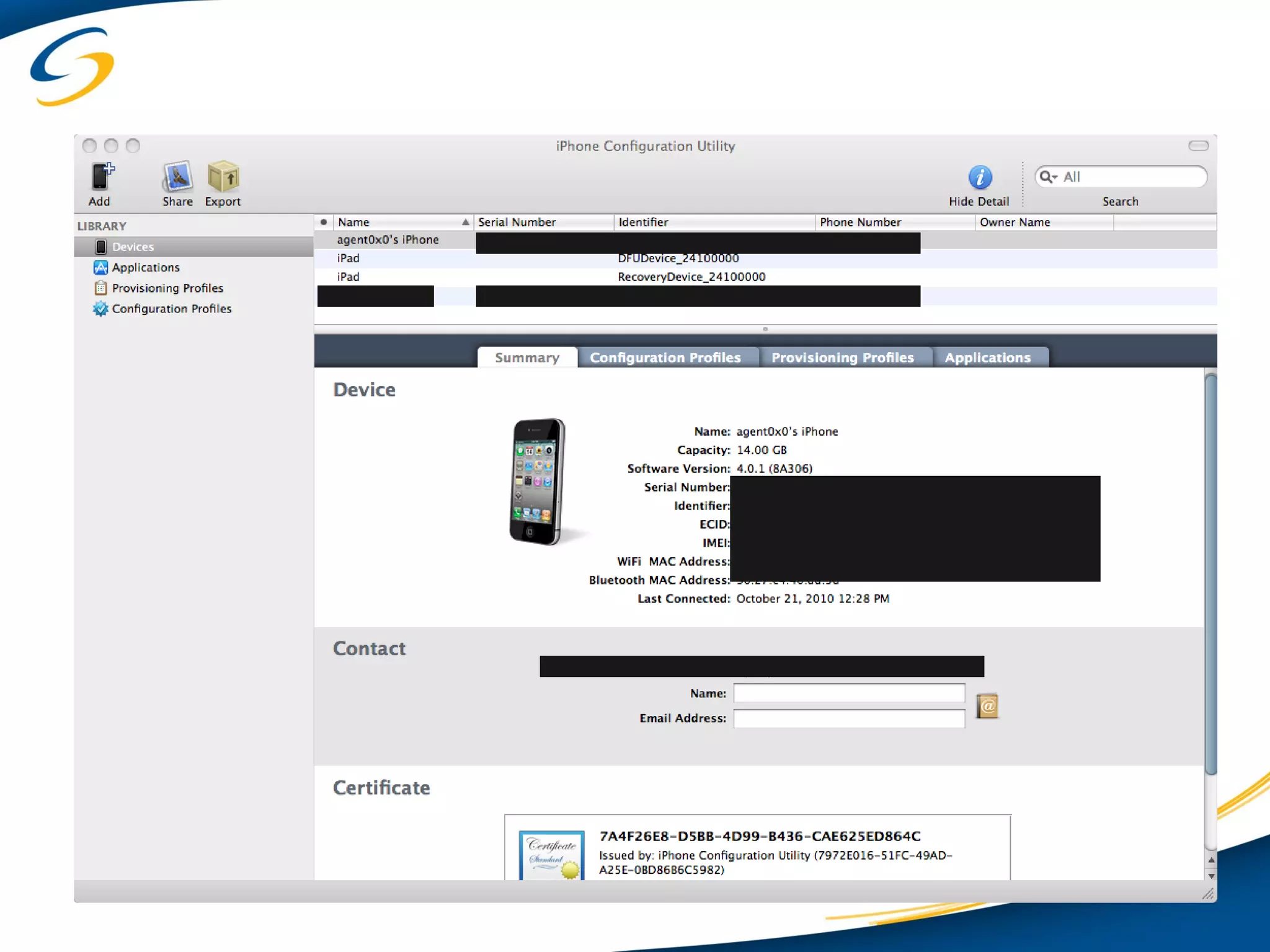
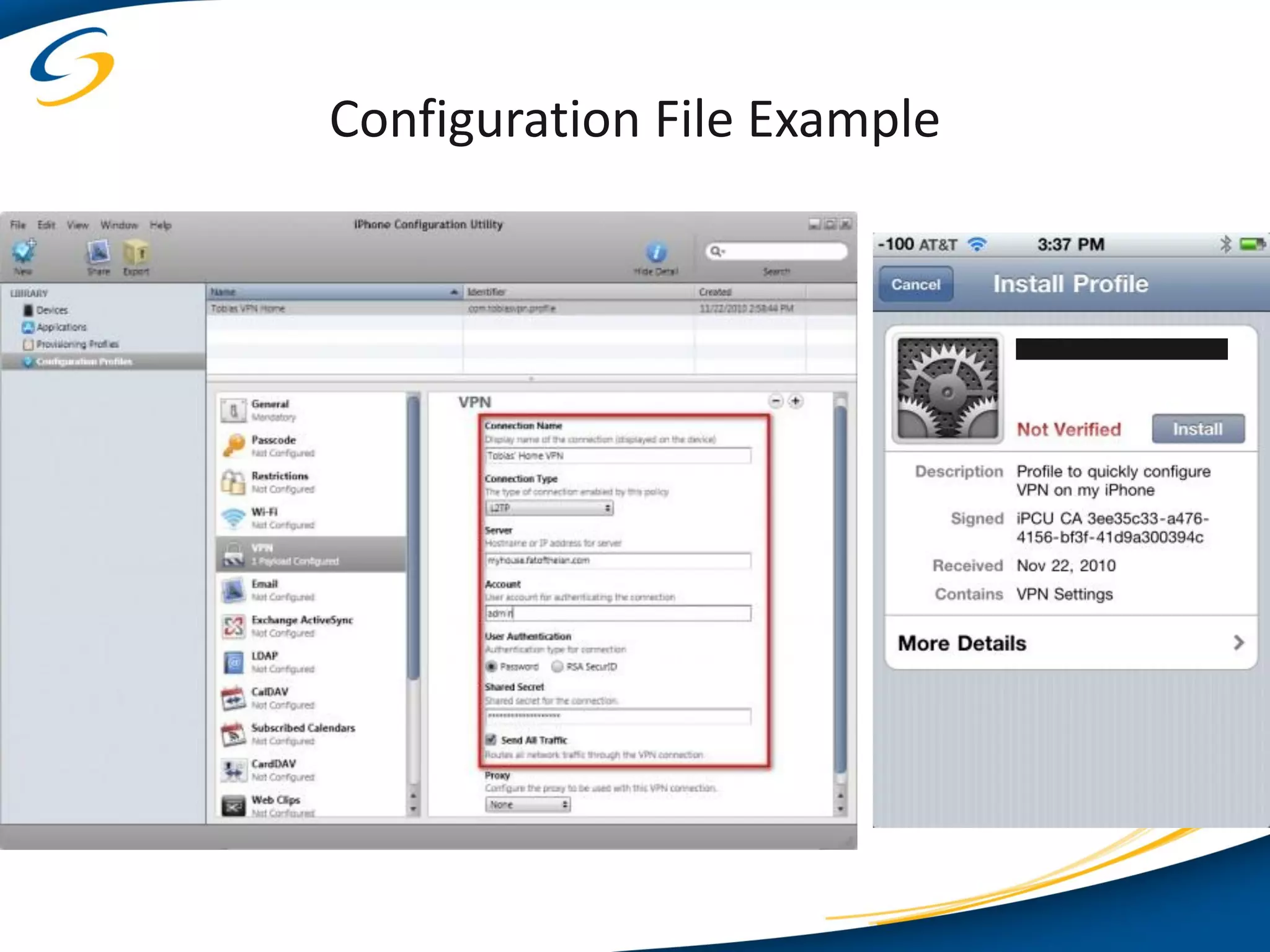
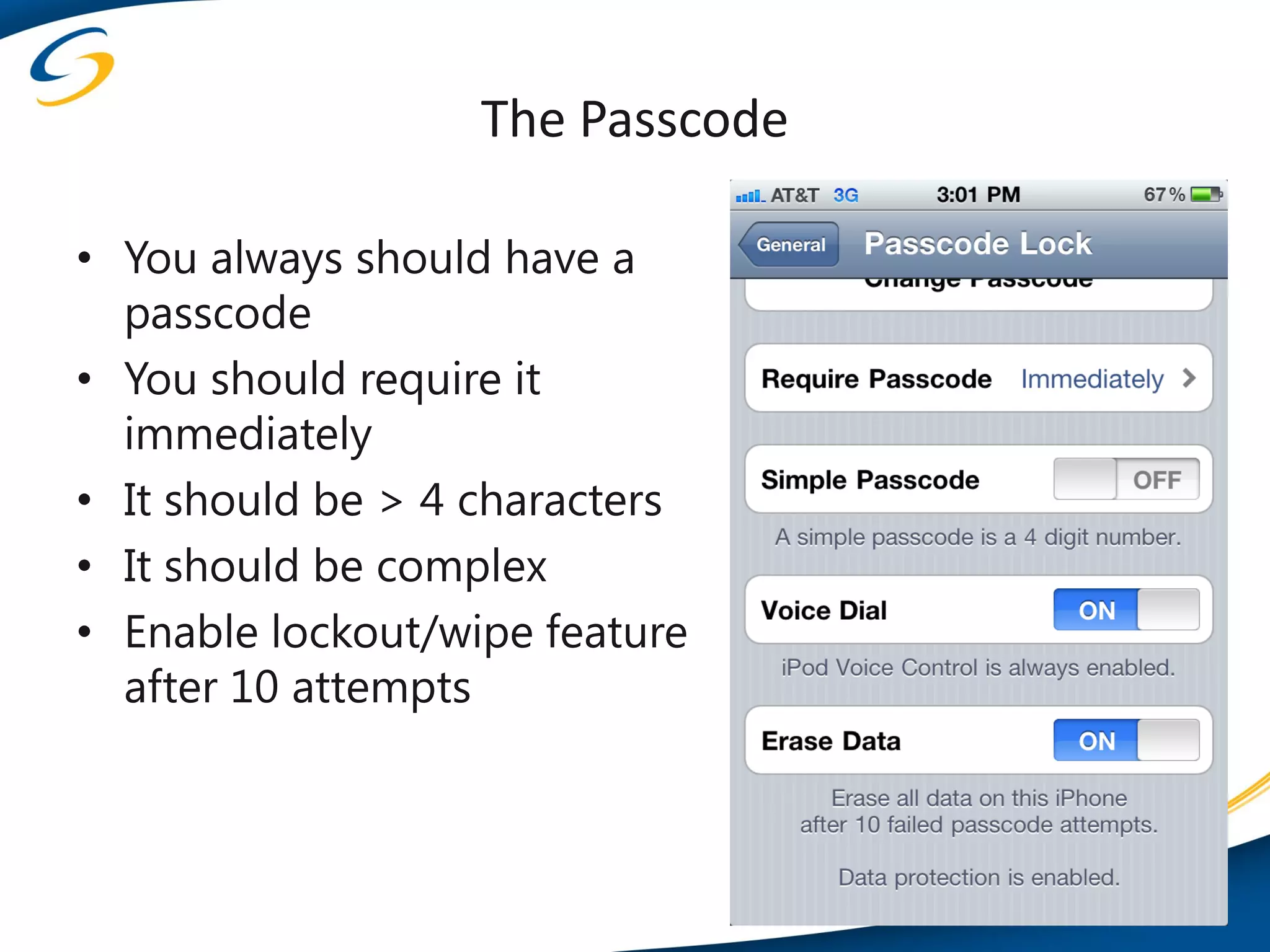
The document discusses the security landscape of Apple iOS devices within enterprise environments, covering topics such as current device states, real-world attacks, and assessment methodologies. It highlights the importance of evaluating iOS deployments due to vulnerabilities, user behavior like jailbreaking, and the need for robust management practices. Additionally, it outlines defensive techniques, hardening practices, and the relevance of mobile device management solutions for ensuring device security.