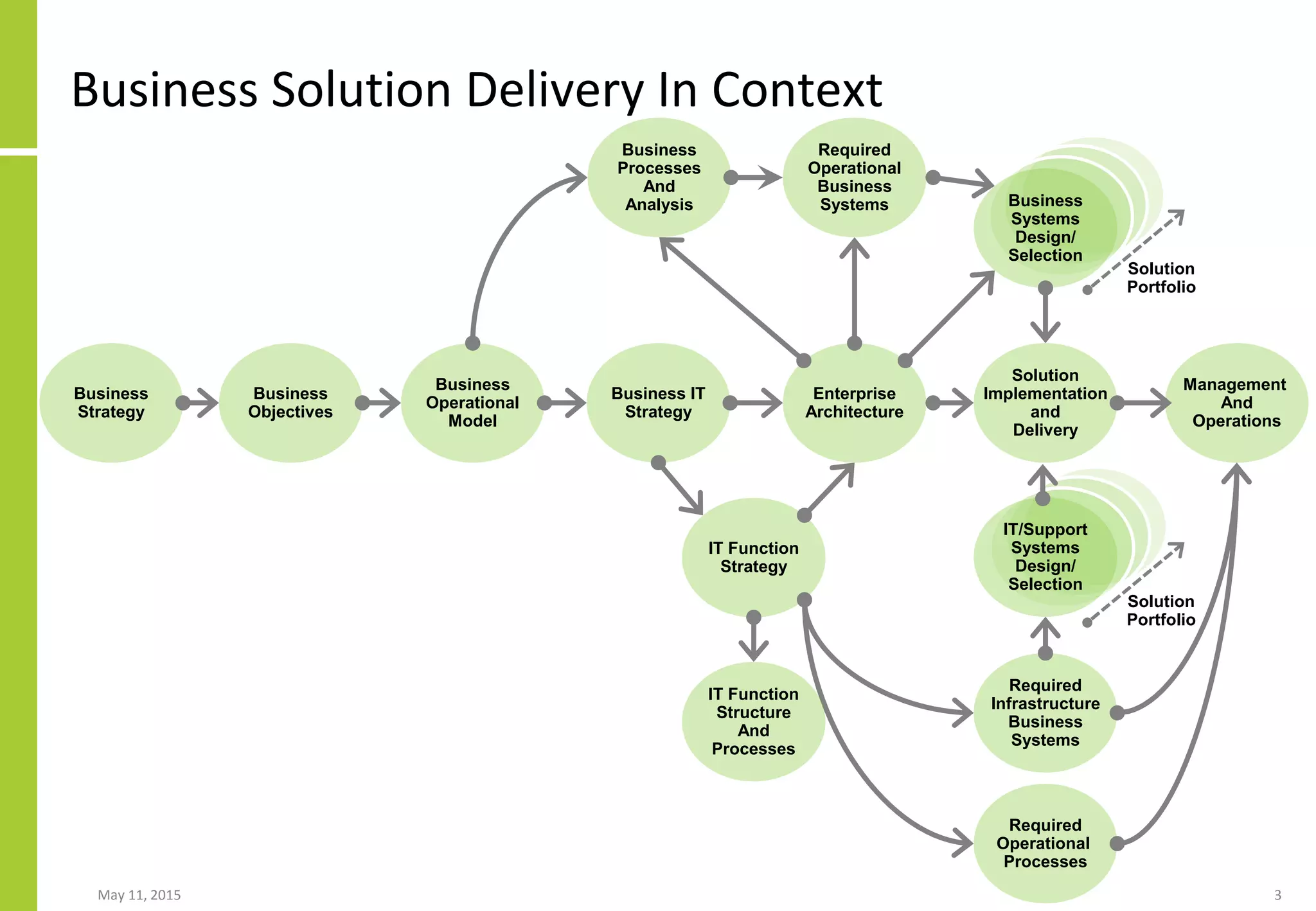
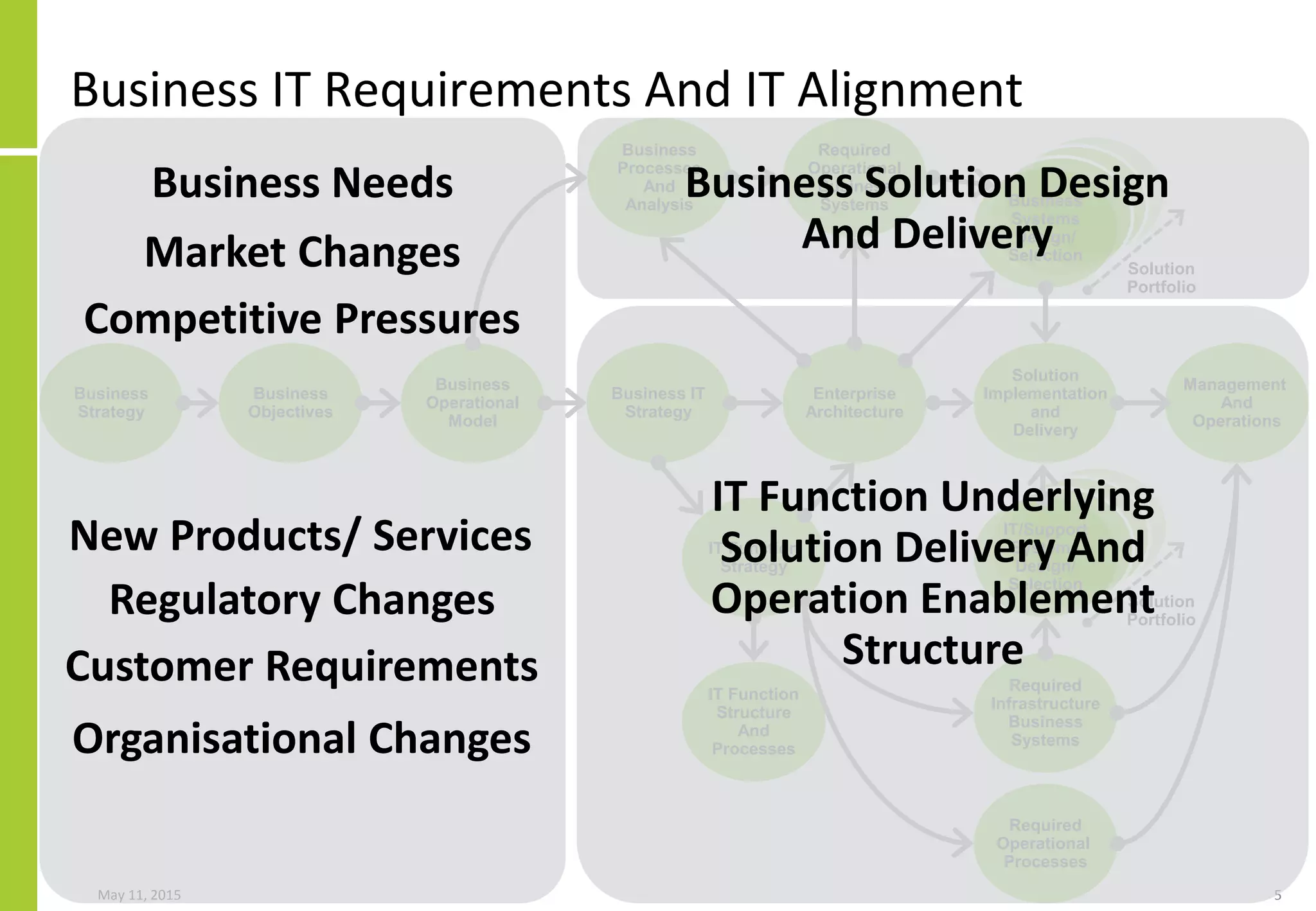
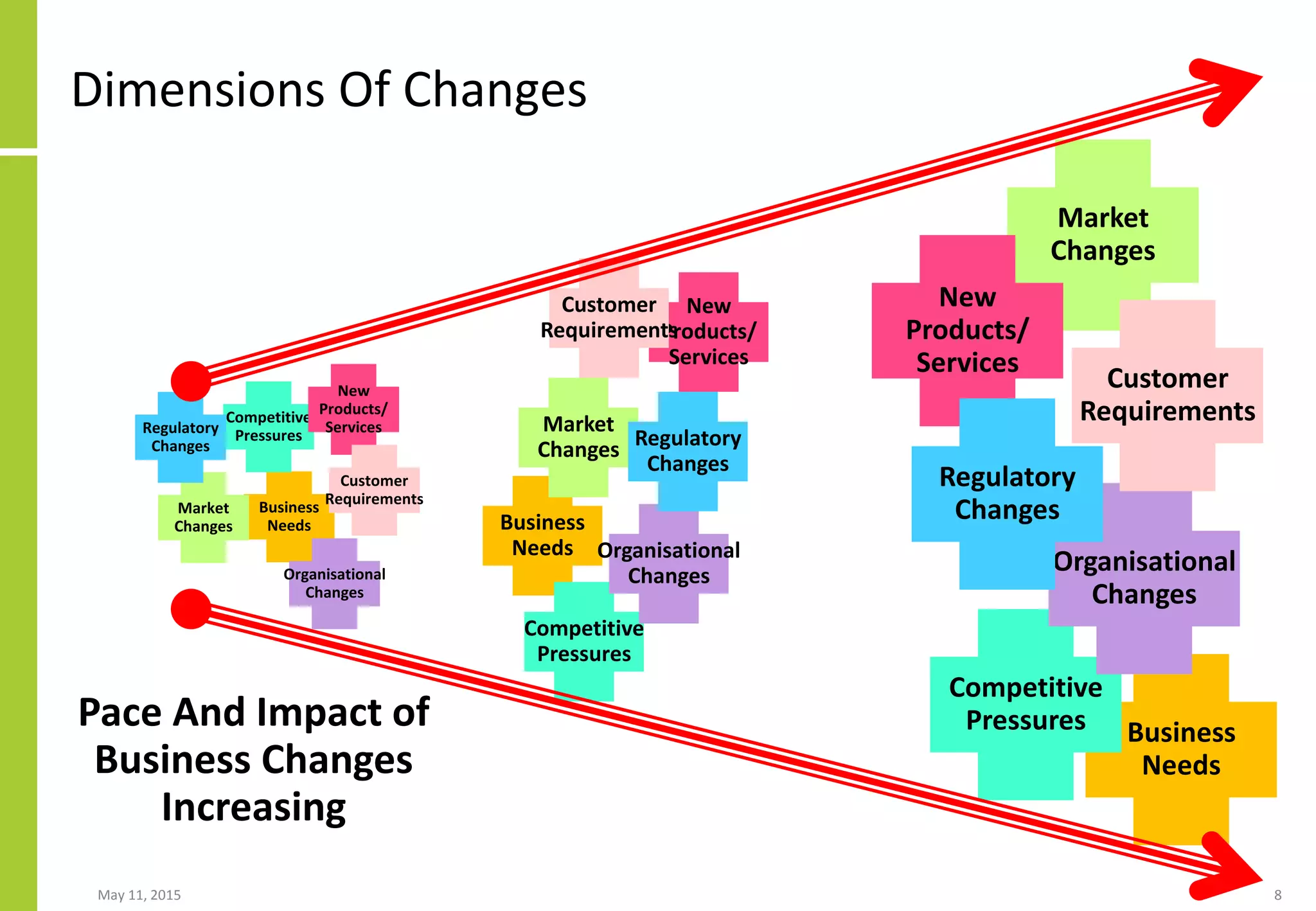
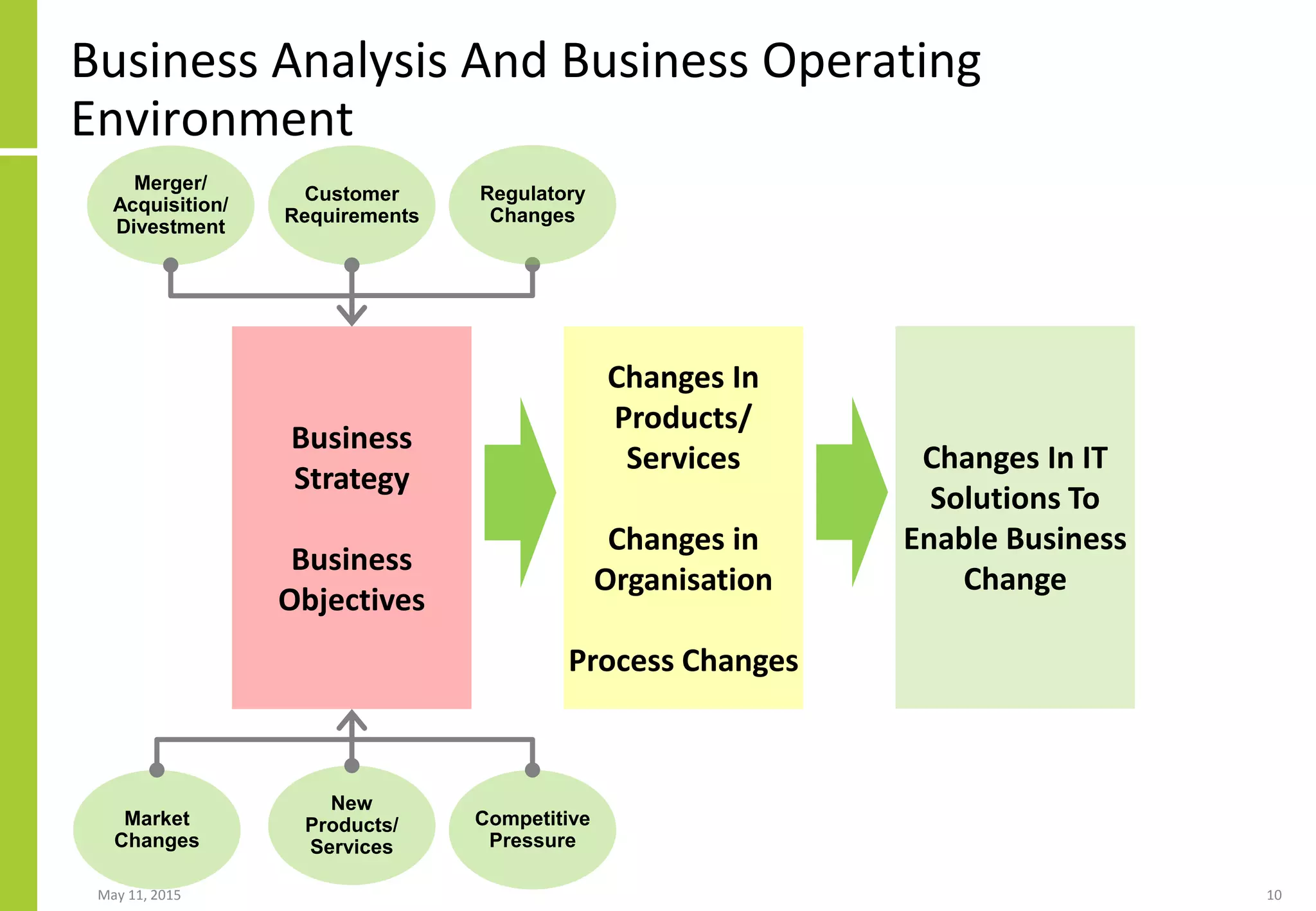
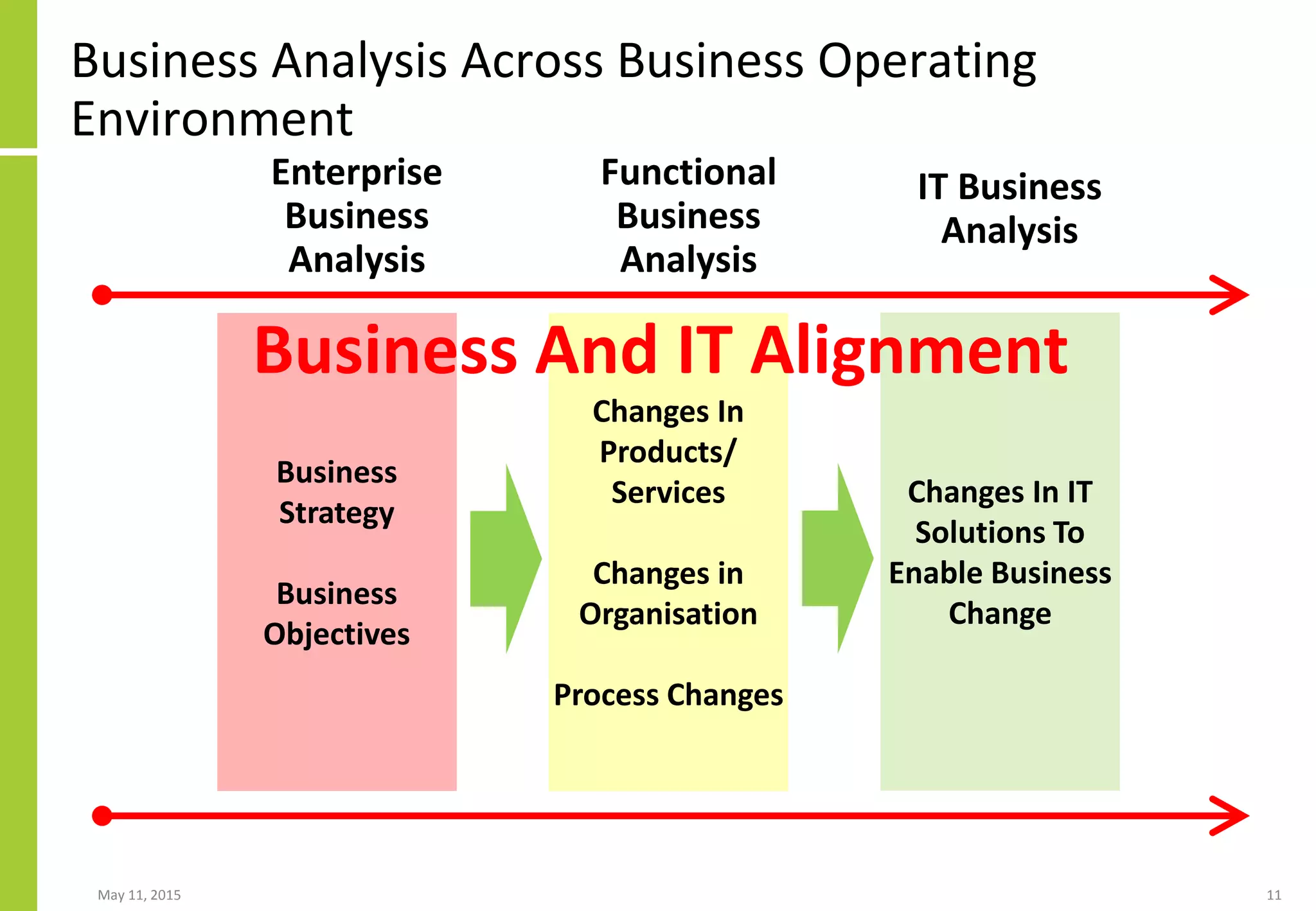
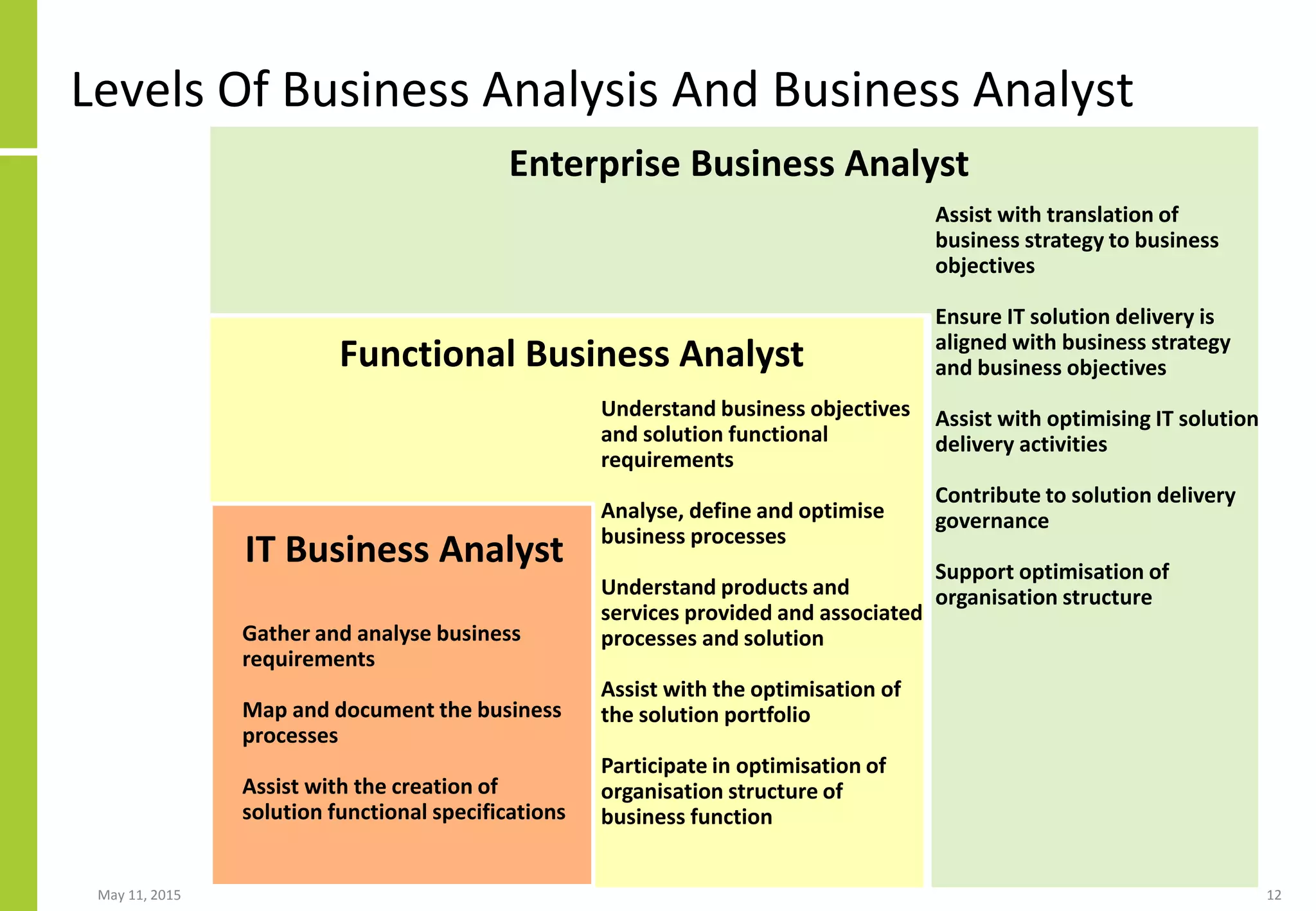
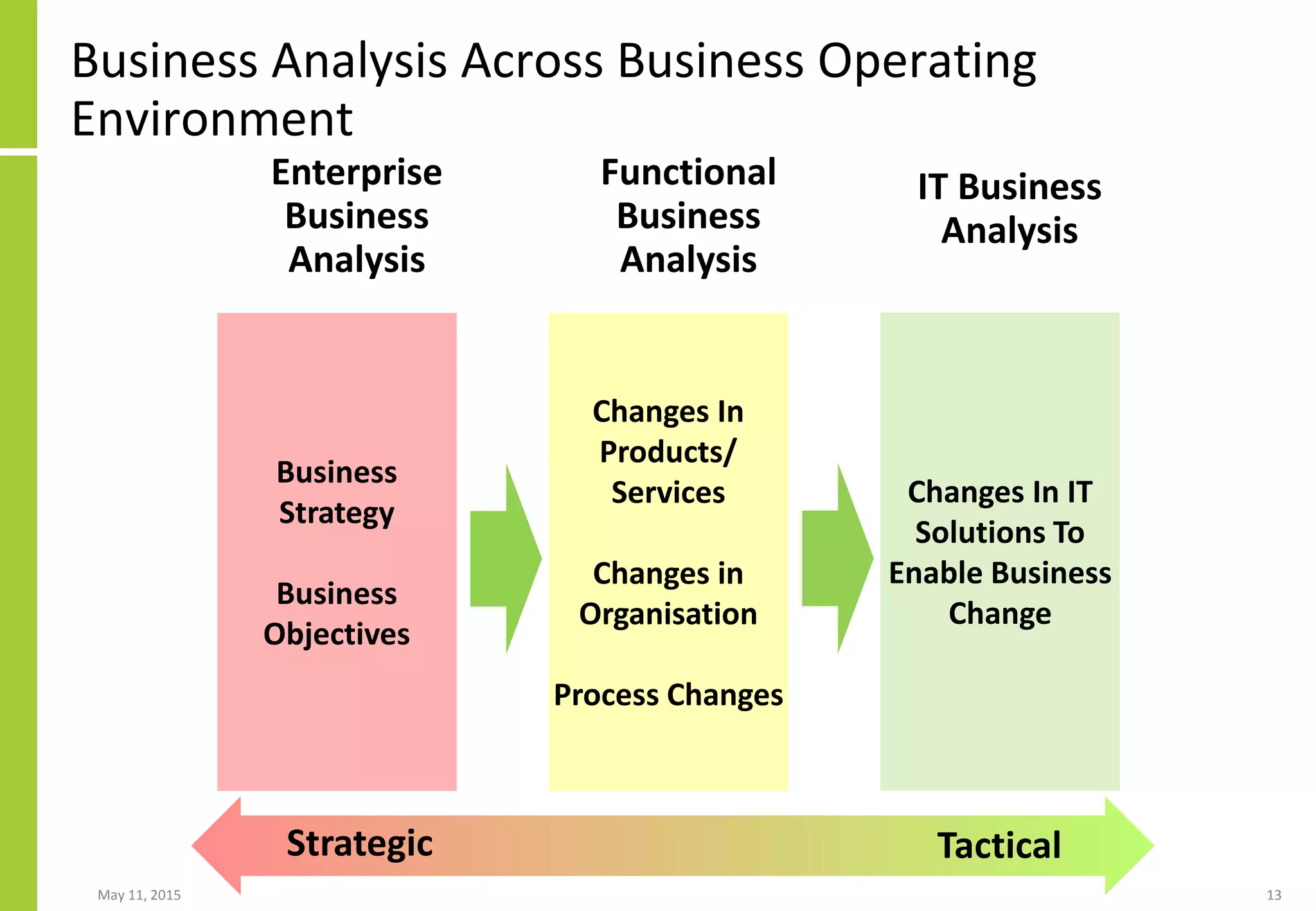
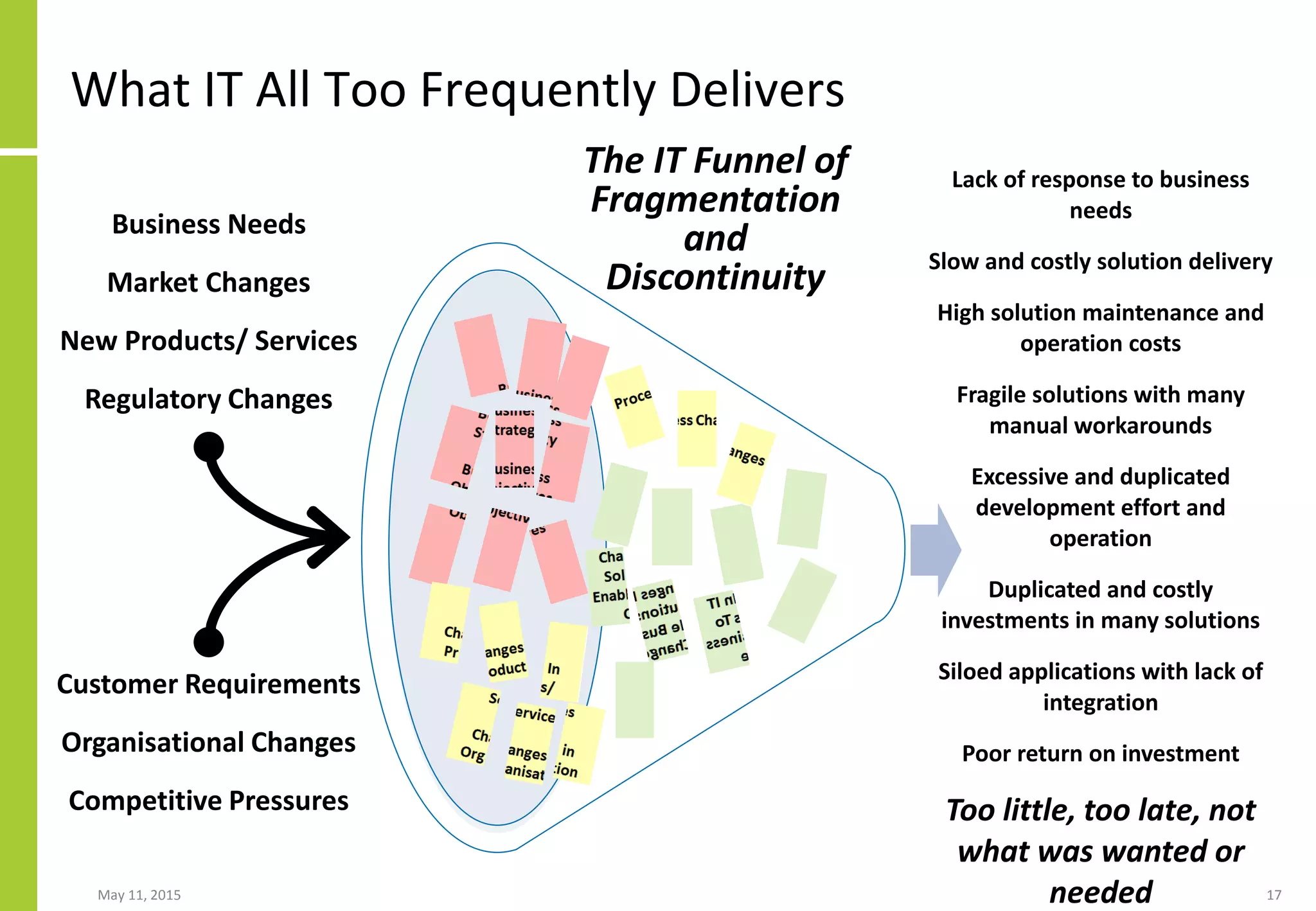
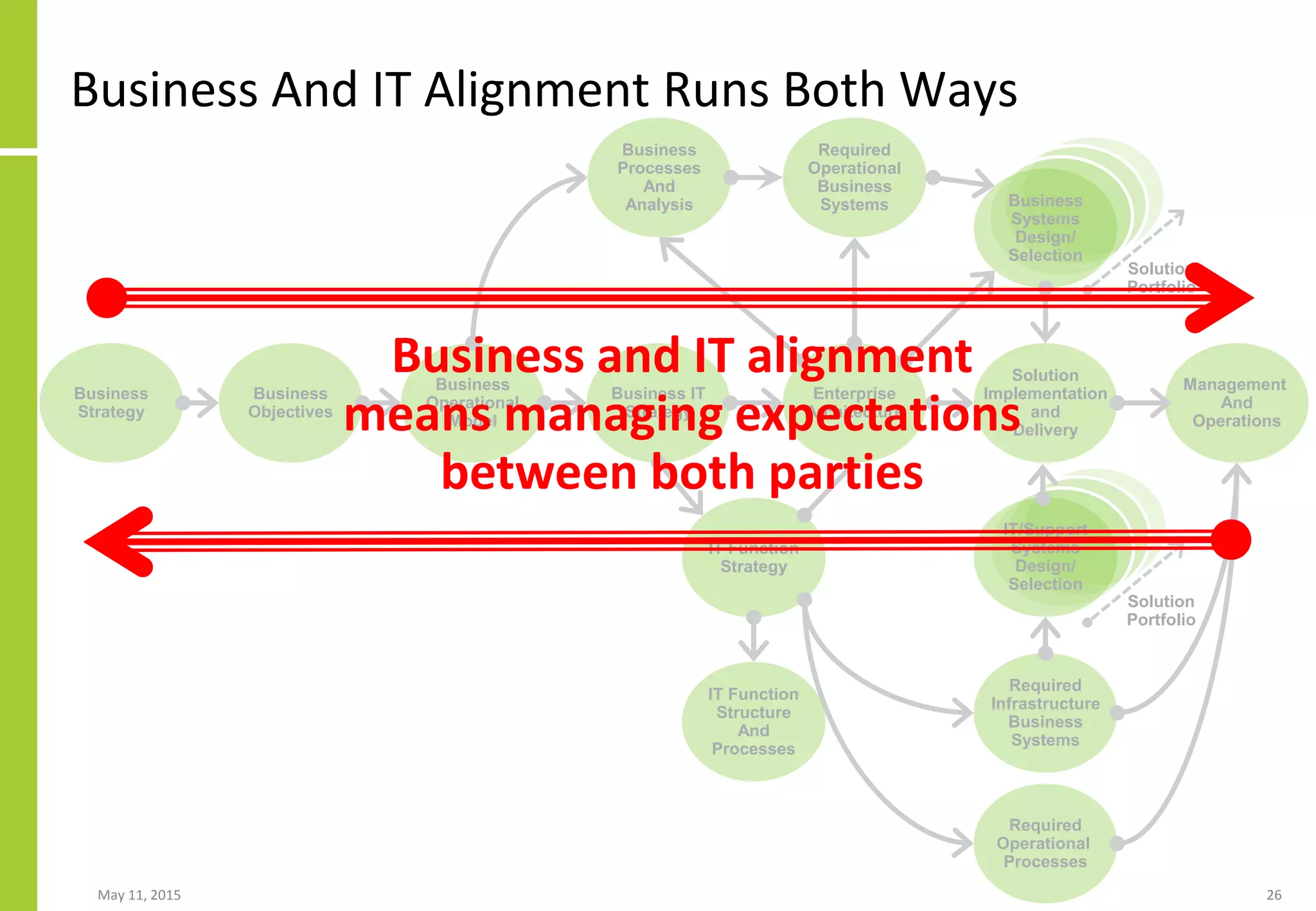
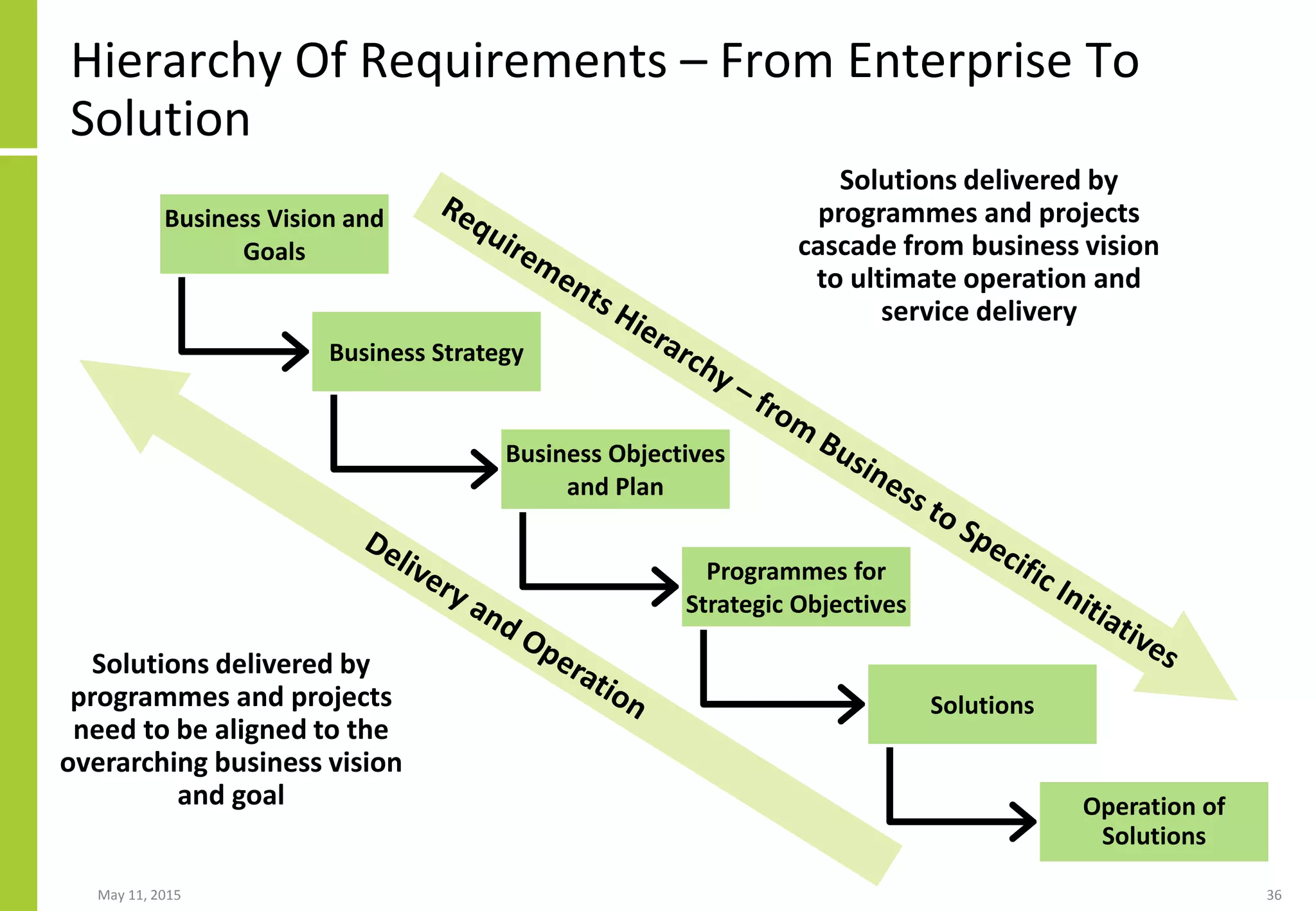
This document discusses the role and importance of enterprise business analysis as a strategic capability for achieving business and IT alignment and driving innovation. Some key points:
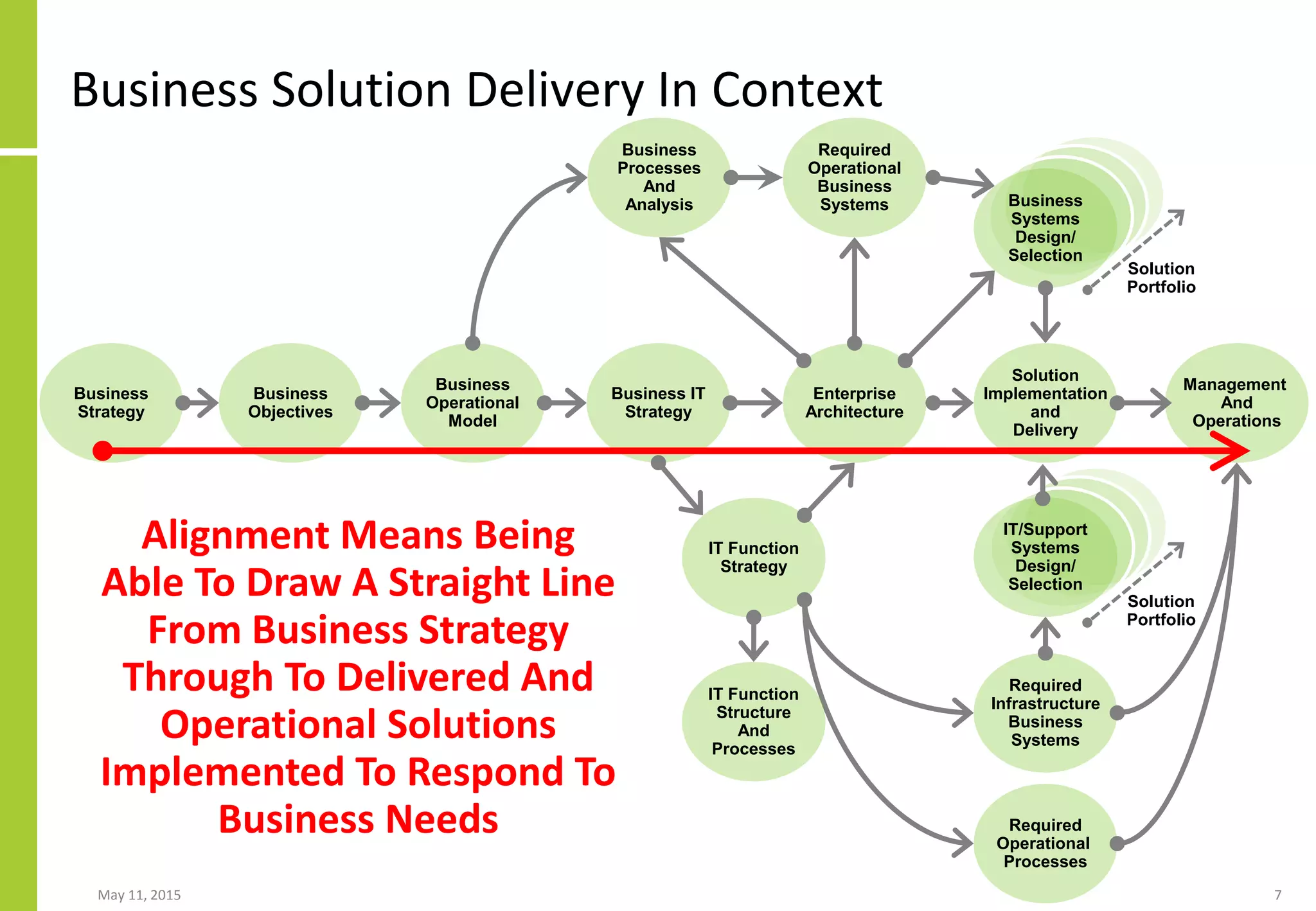
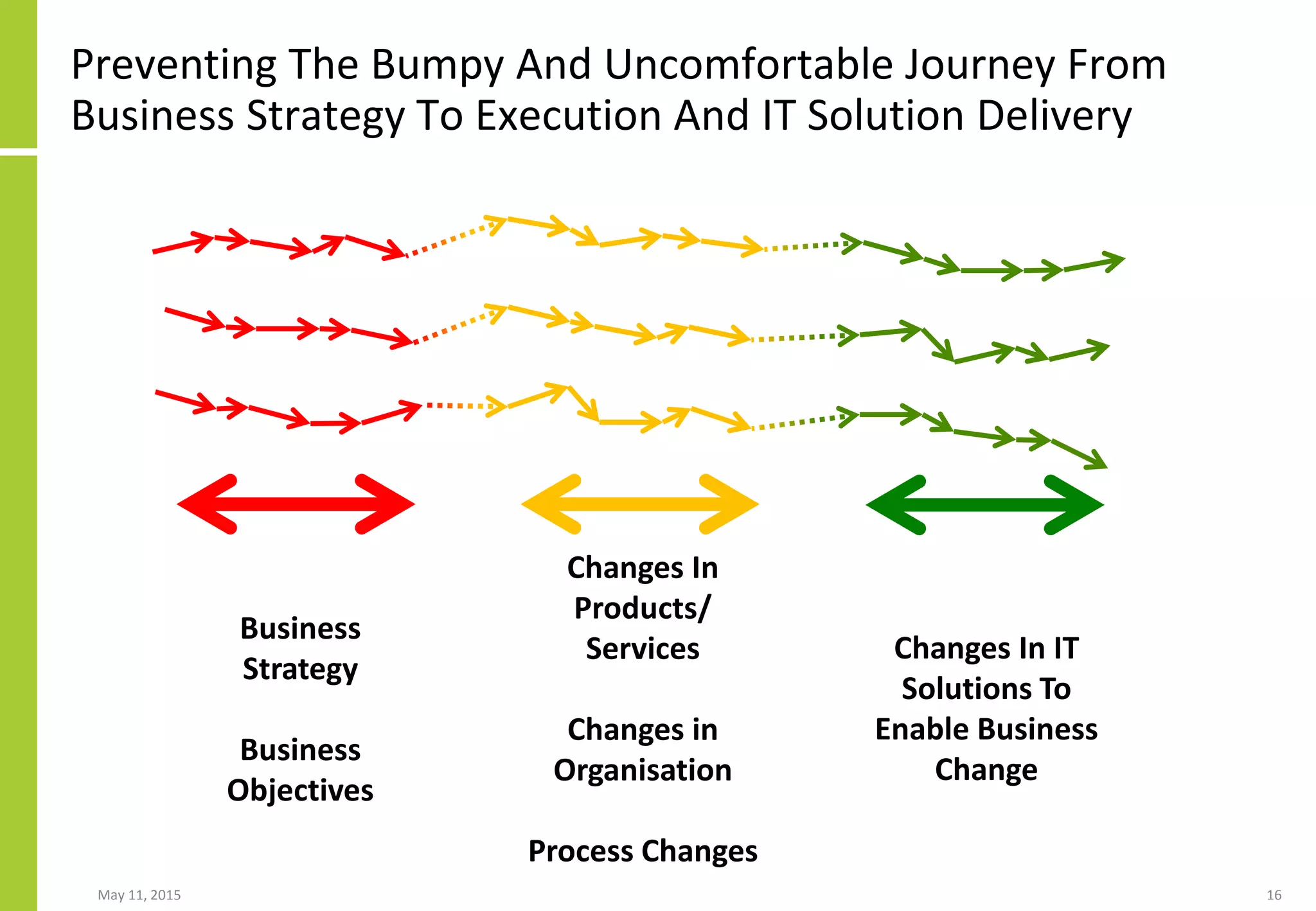
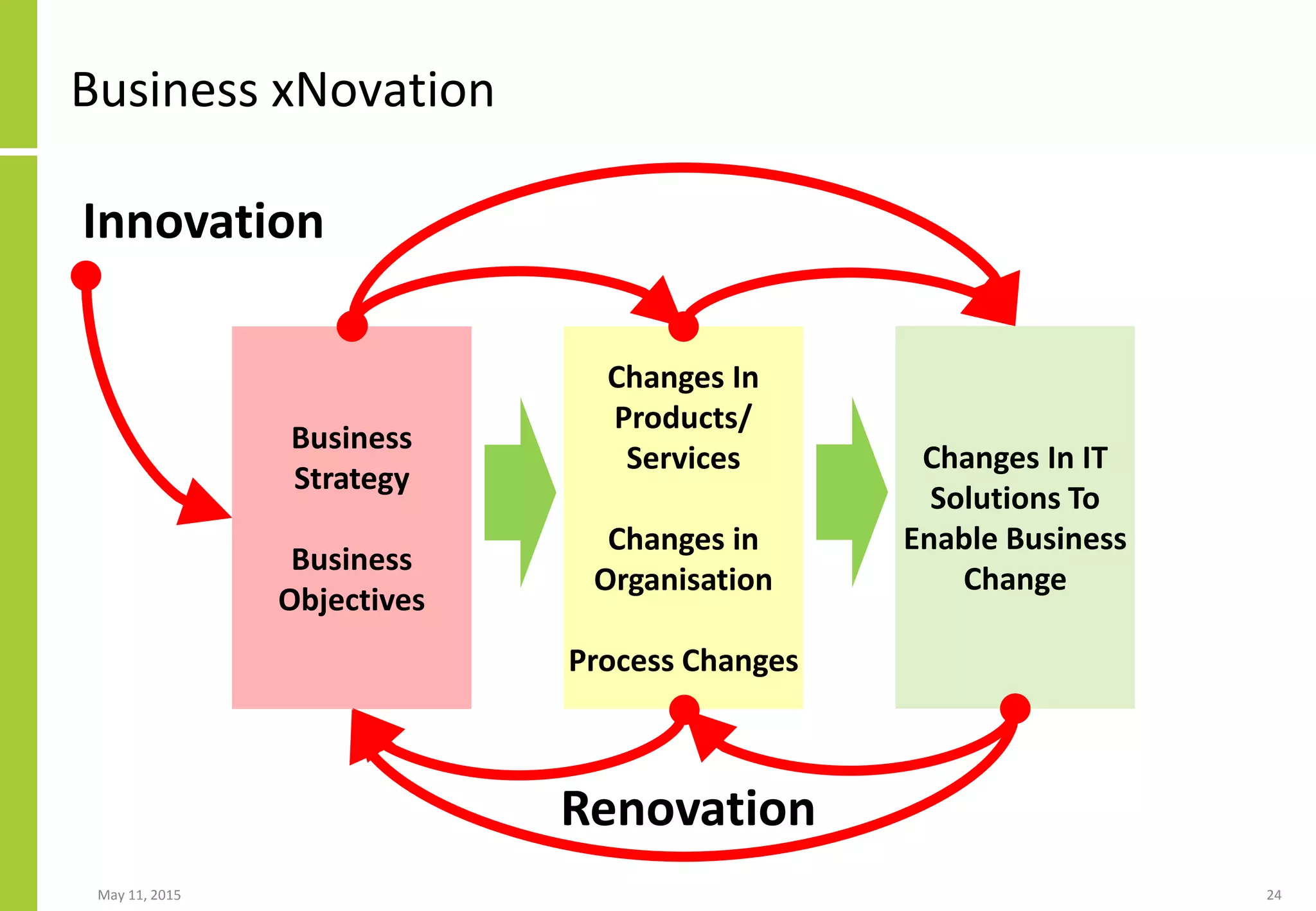
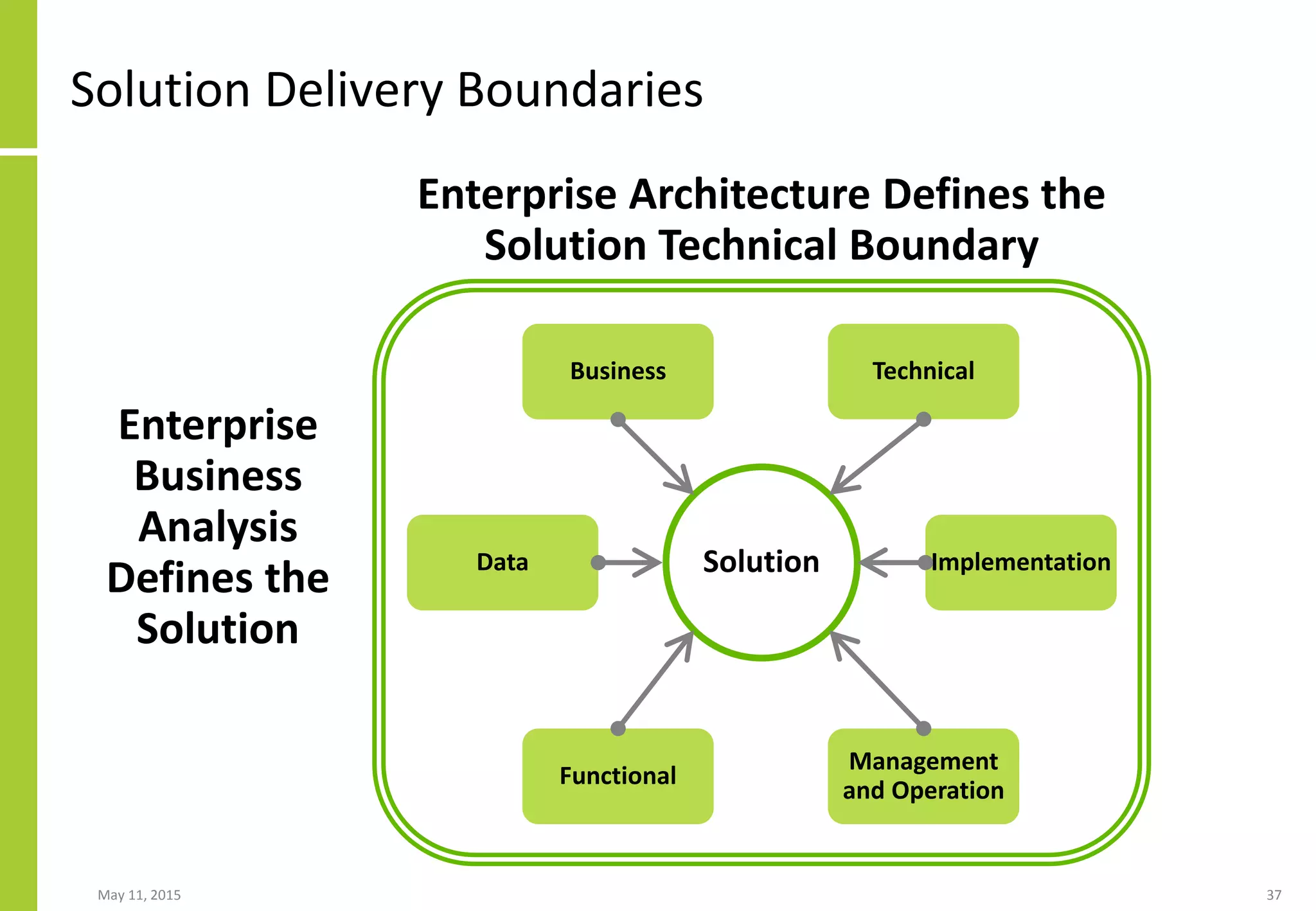
- Enterprise business analysis can help translate business strategy into objectives, ensure IT solution delivery is aligned to strategy/objectives, and contribute to solution delivery governance.
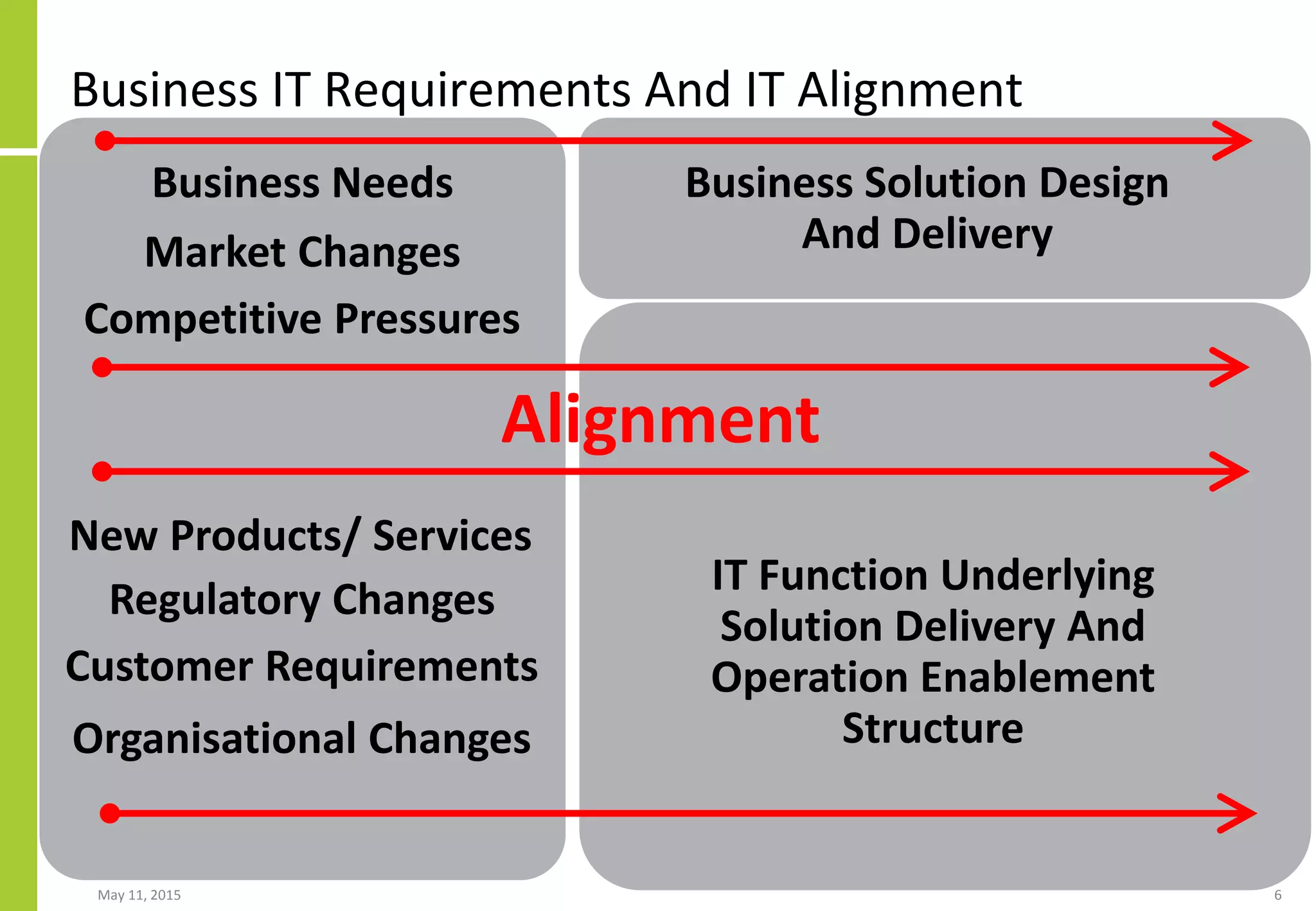
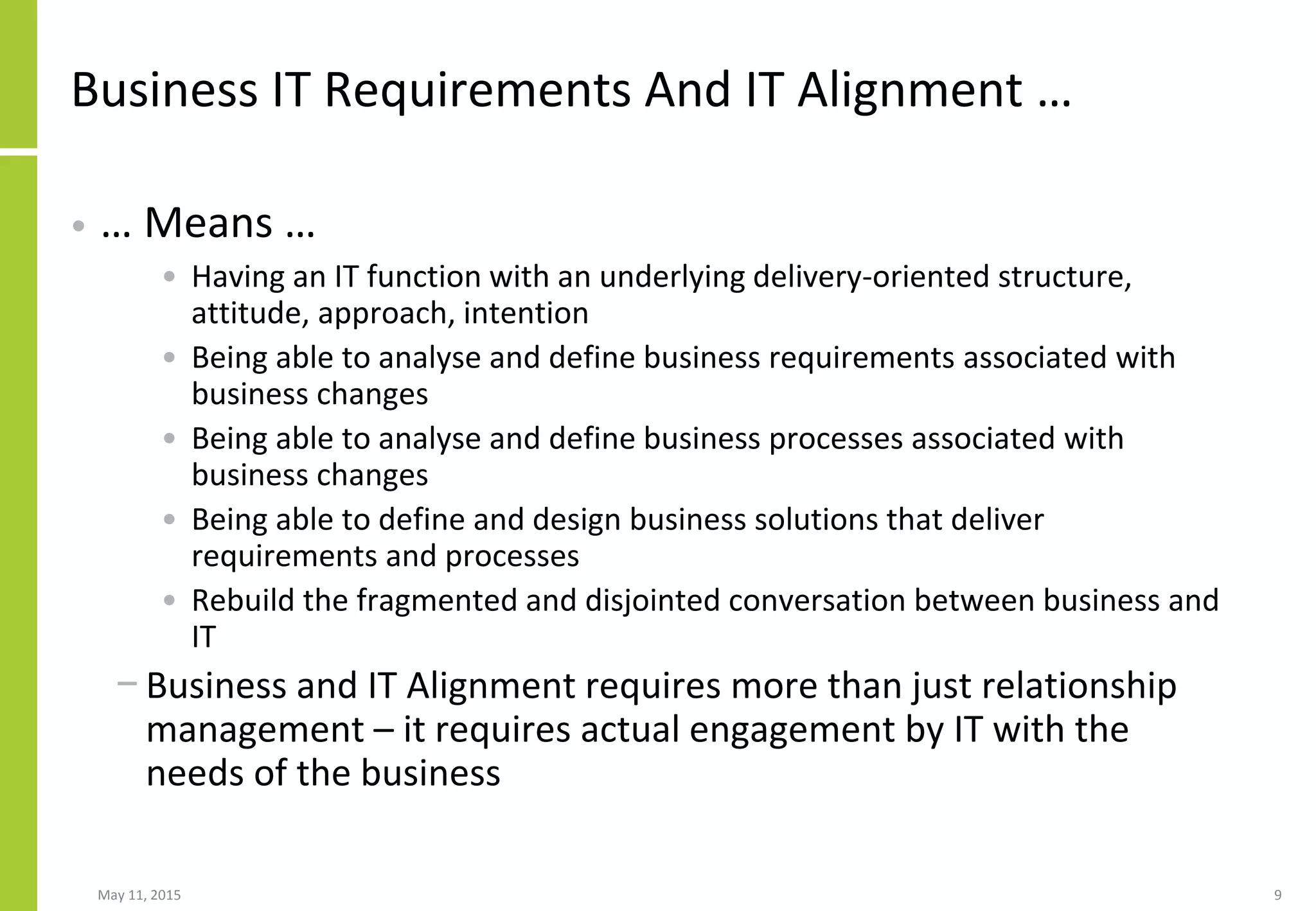
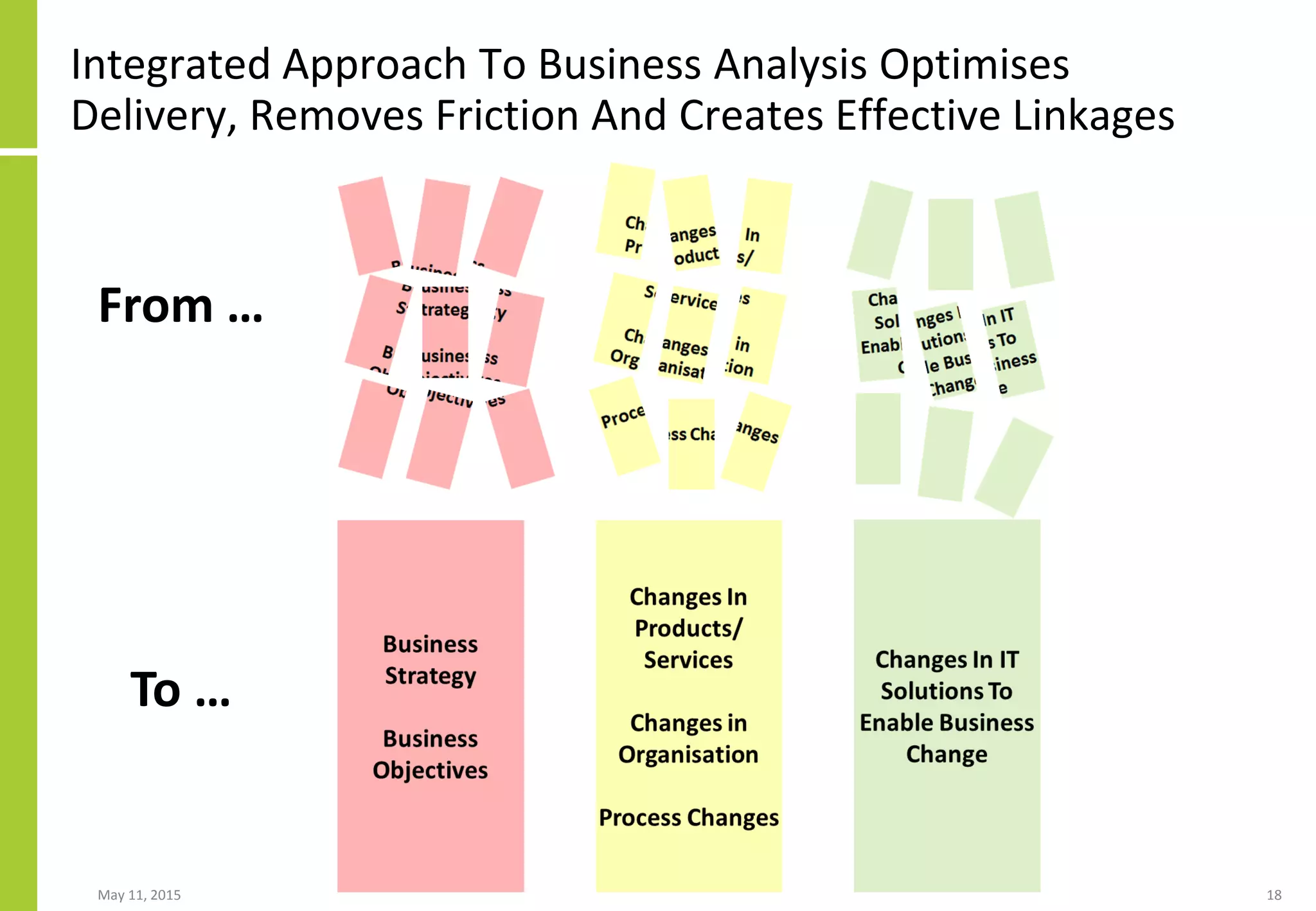
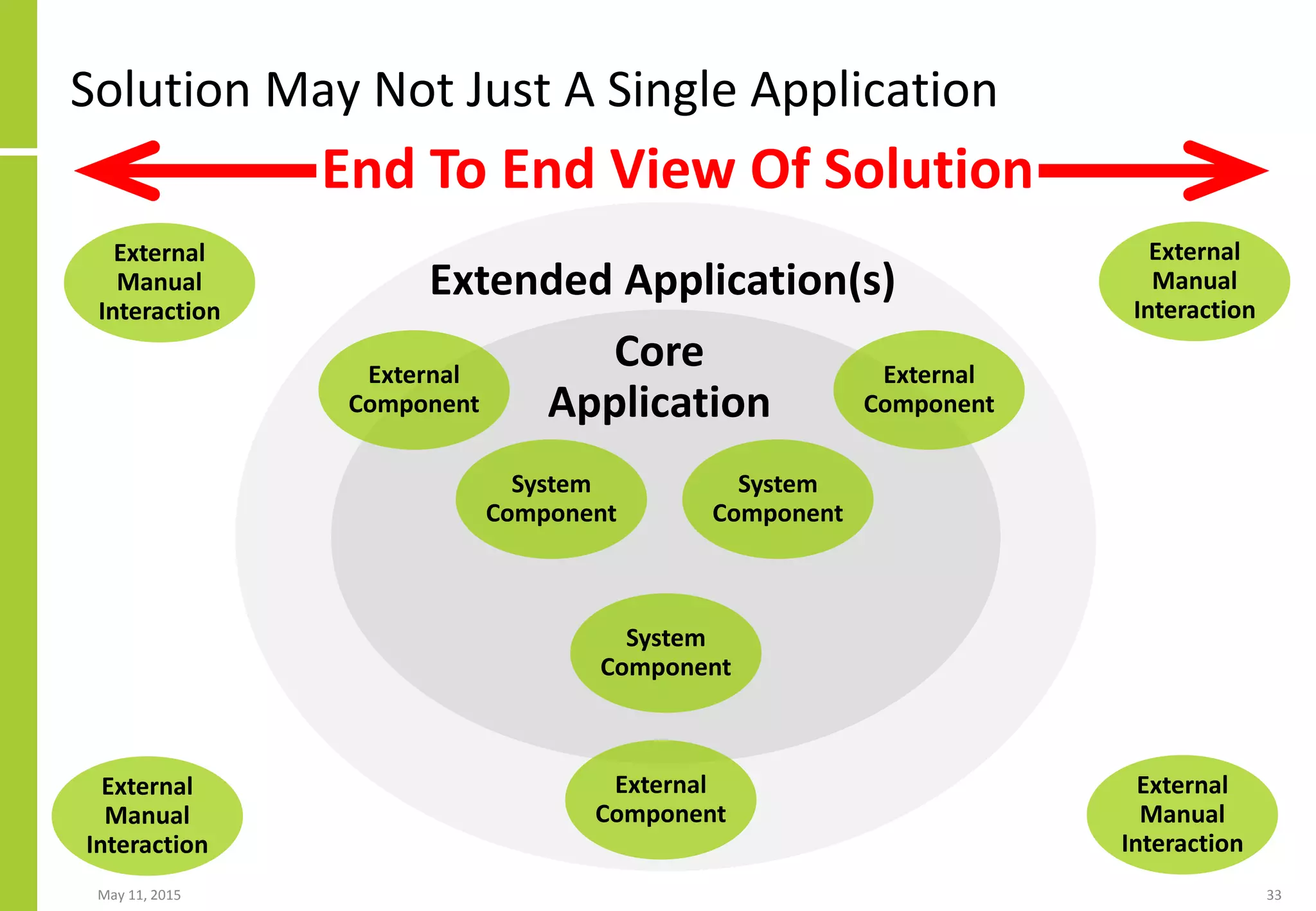
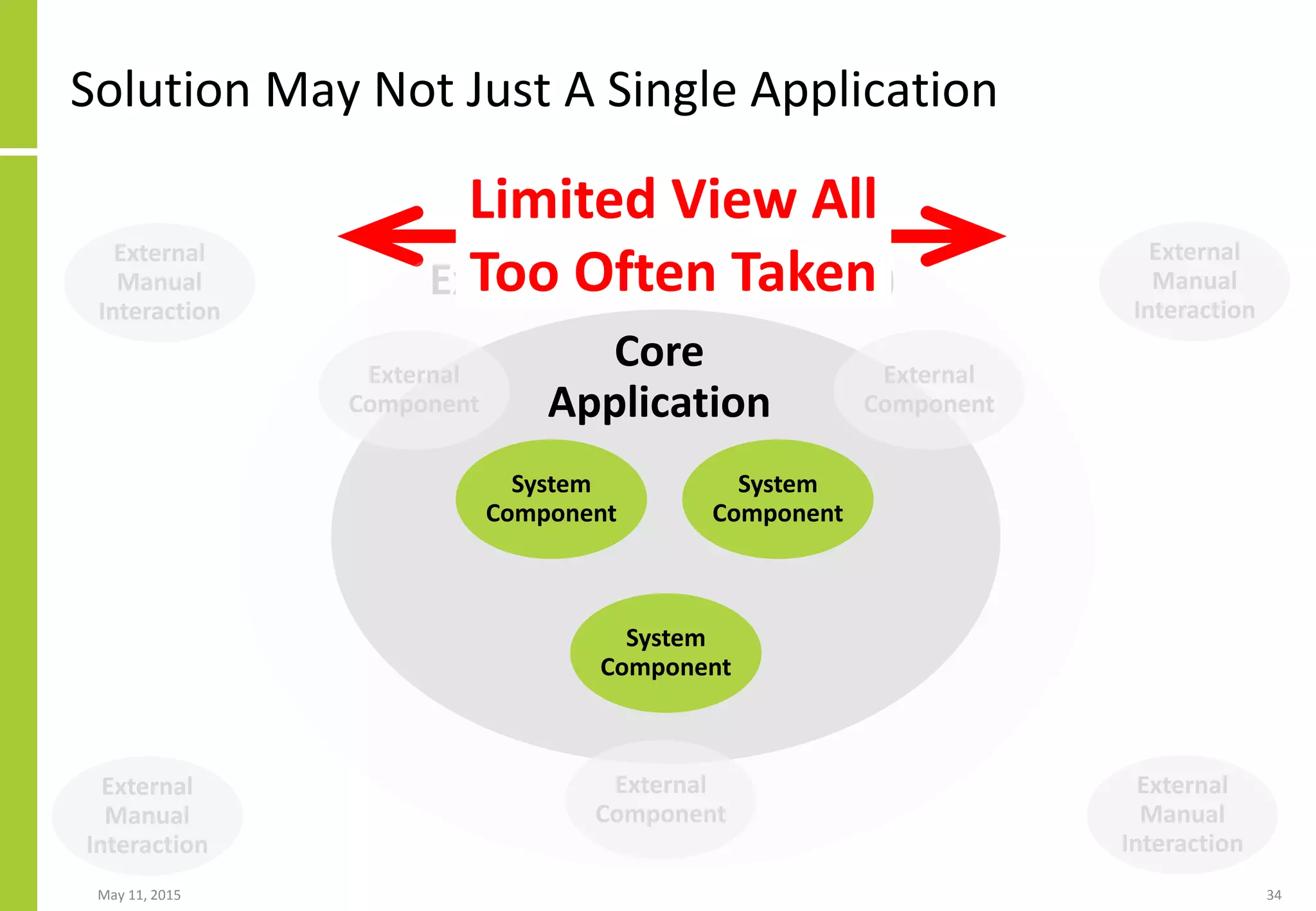
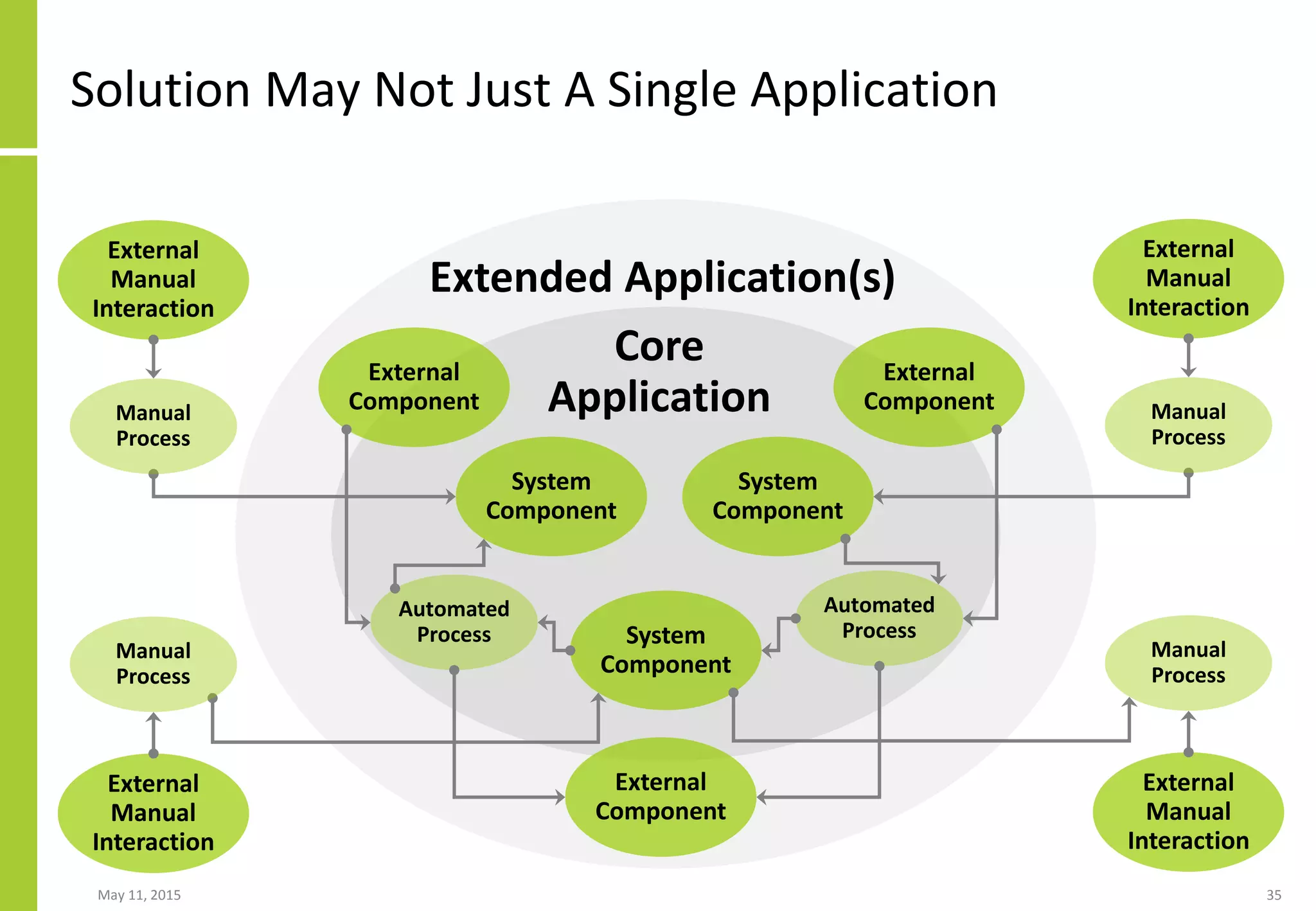
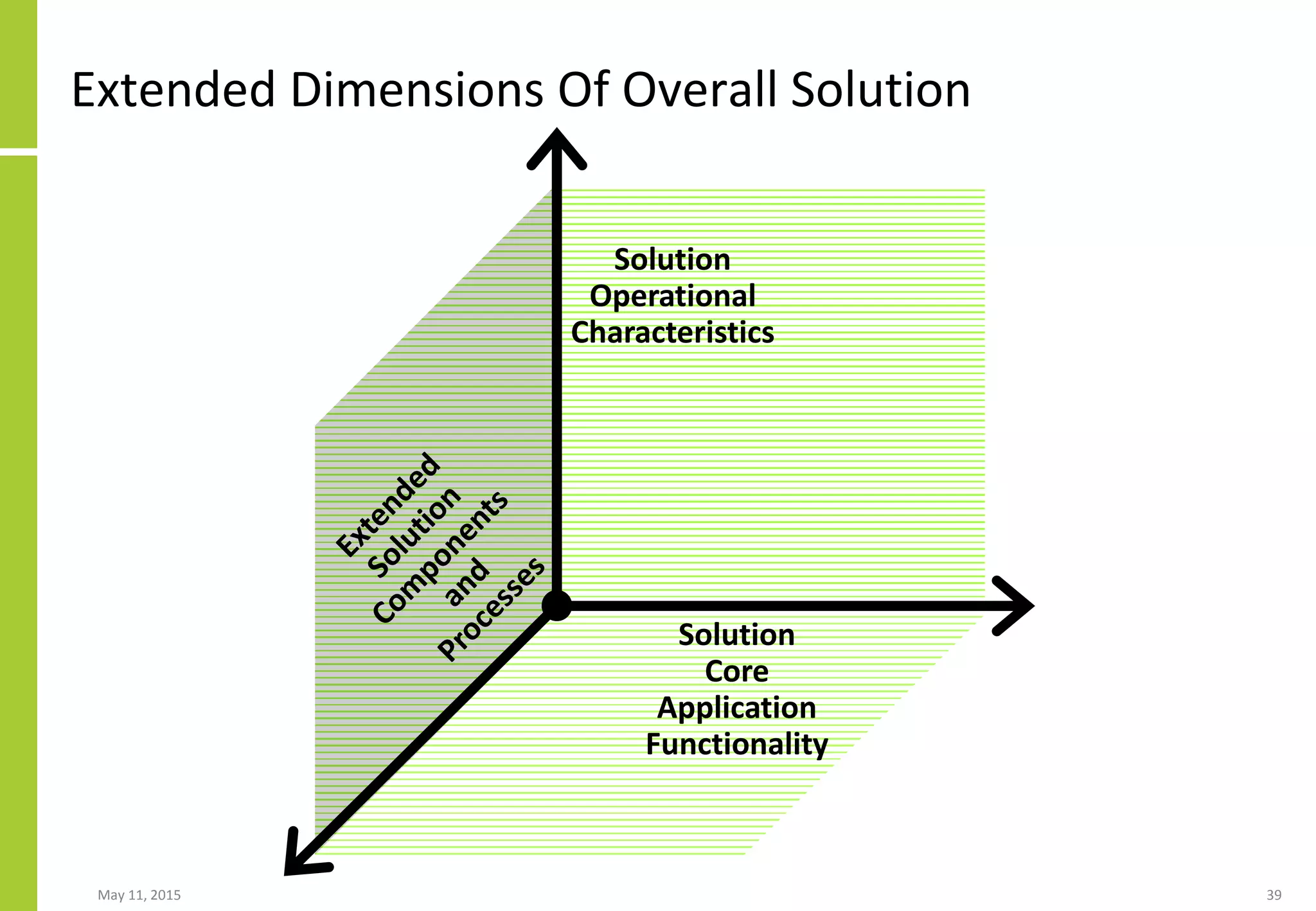
- It involves analyzing business requirements and processes associated with changes, defining business solutions to deliver requirements/processes, and rebuilding the conversation between business and IT.
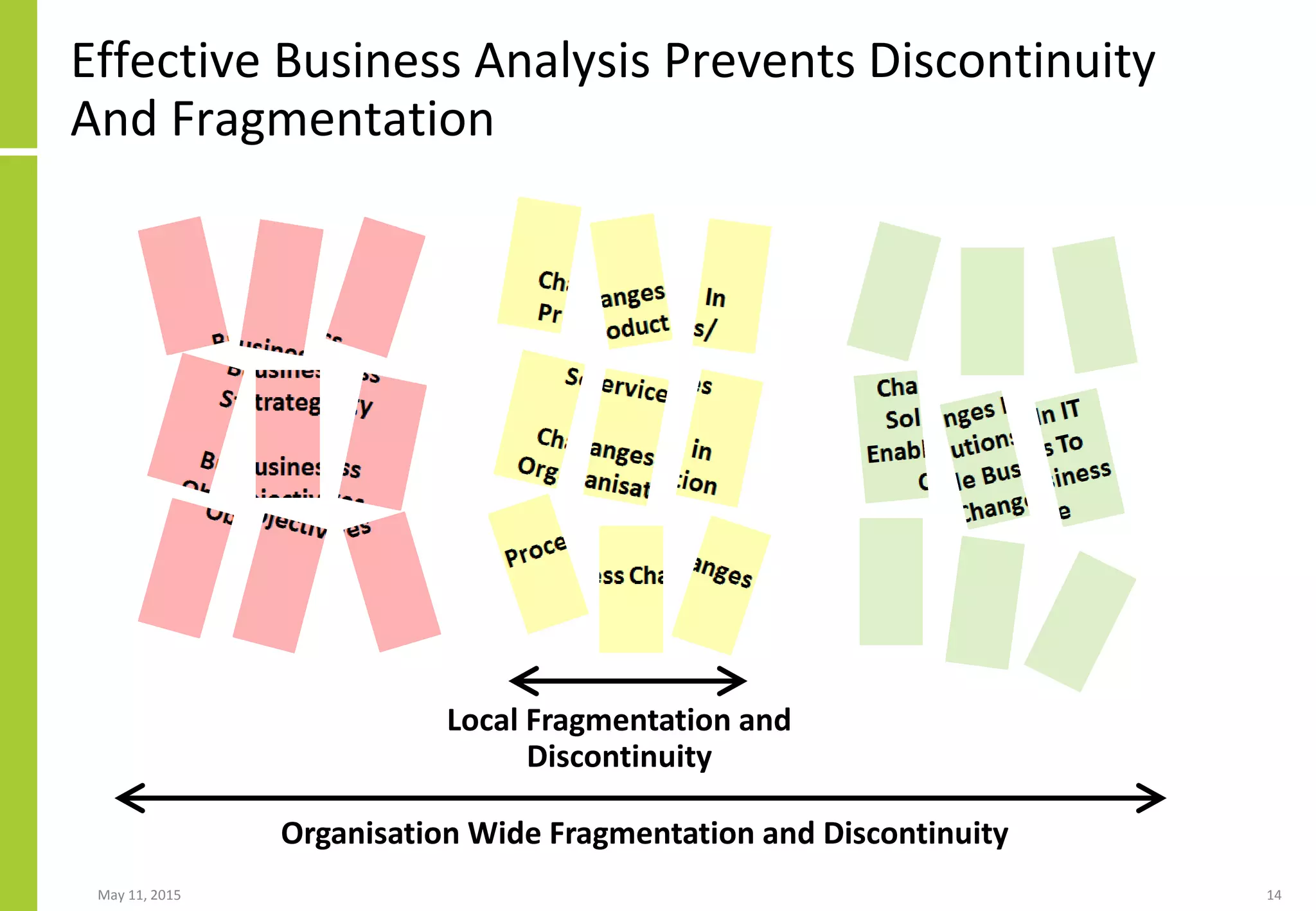
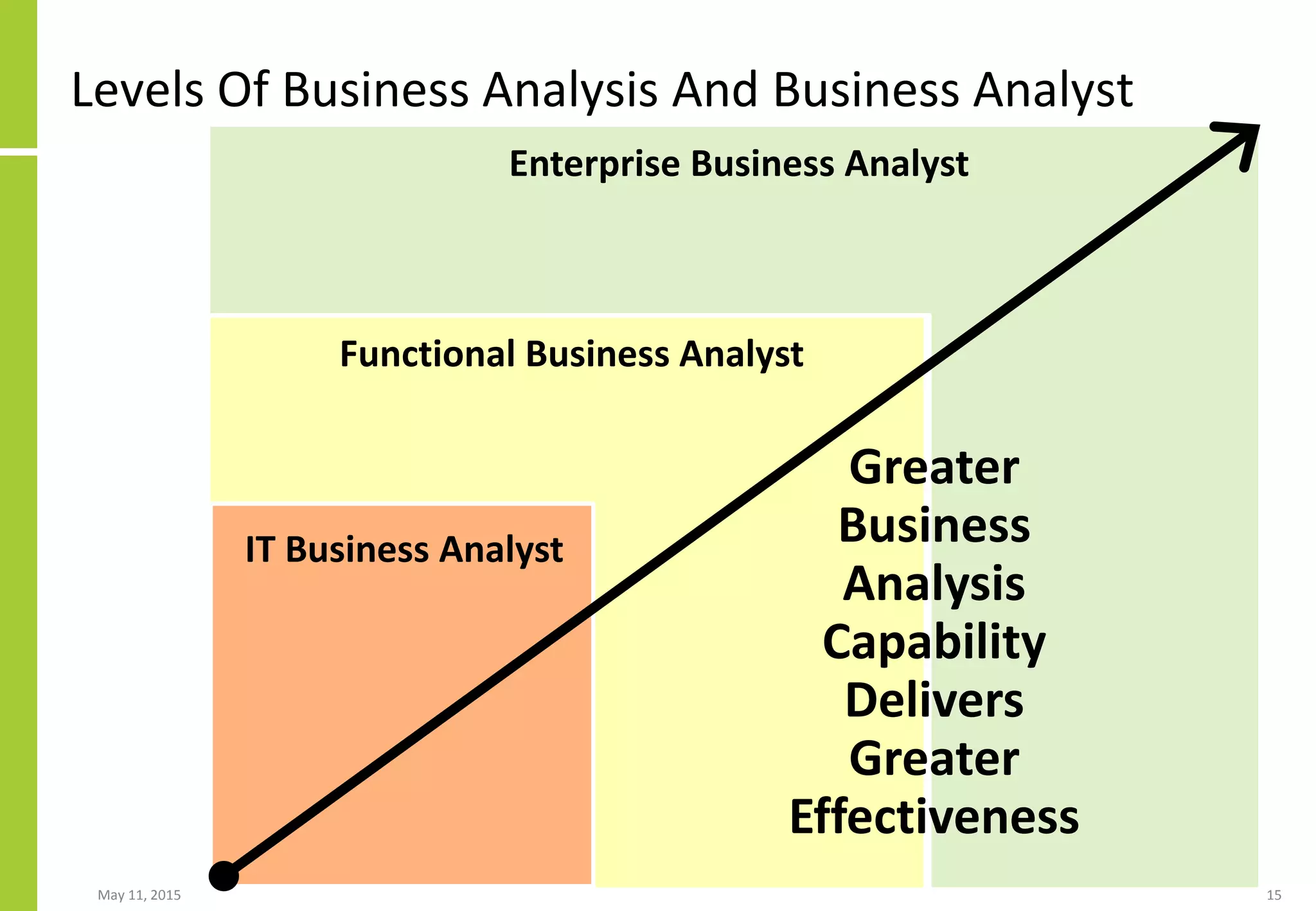
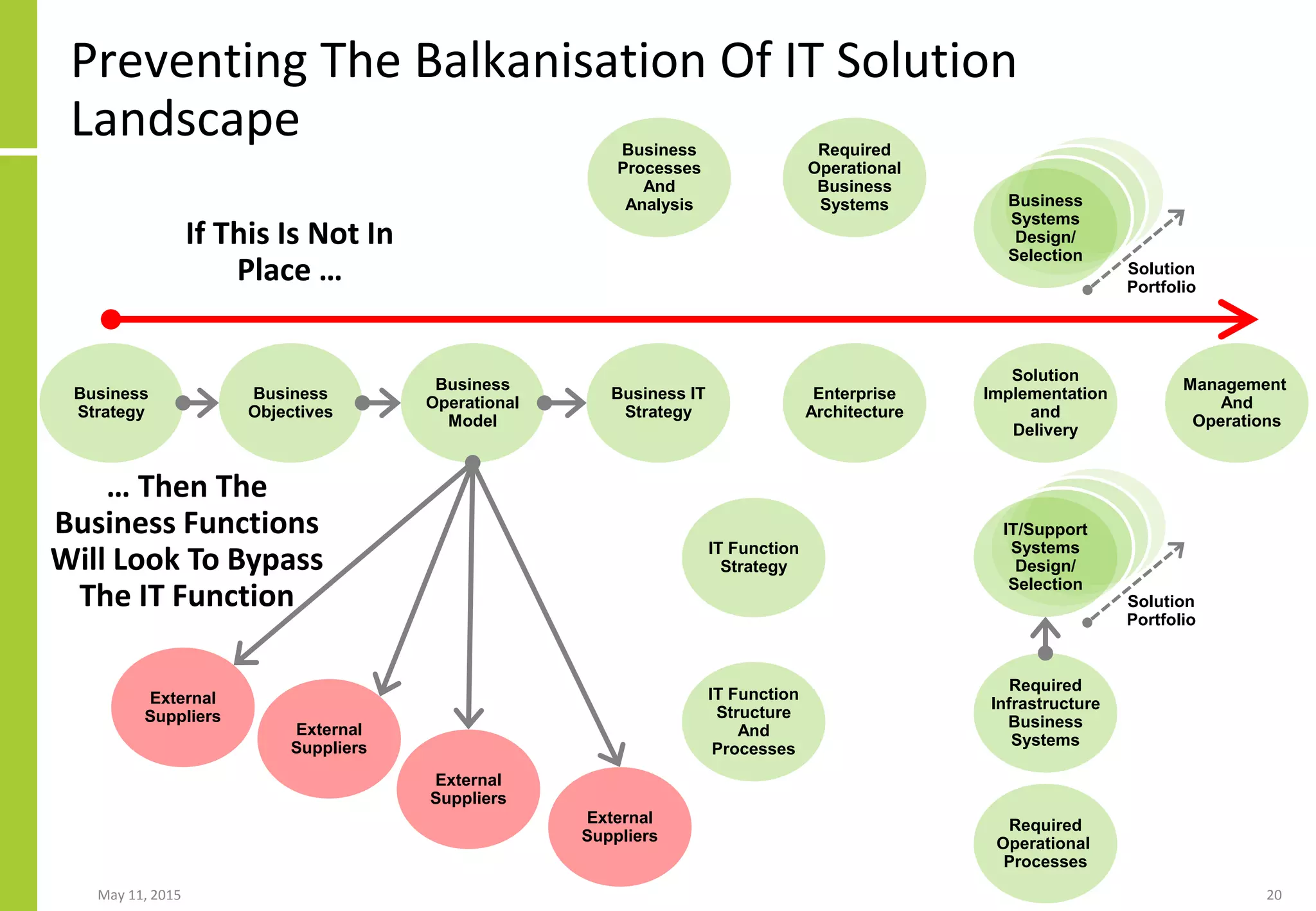
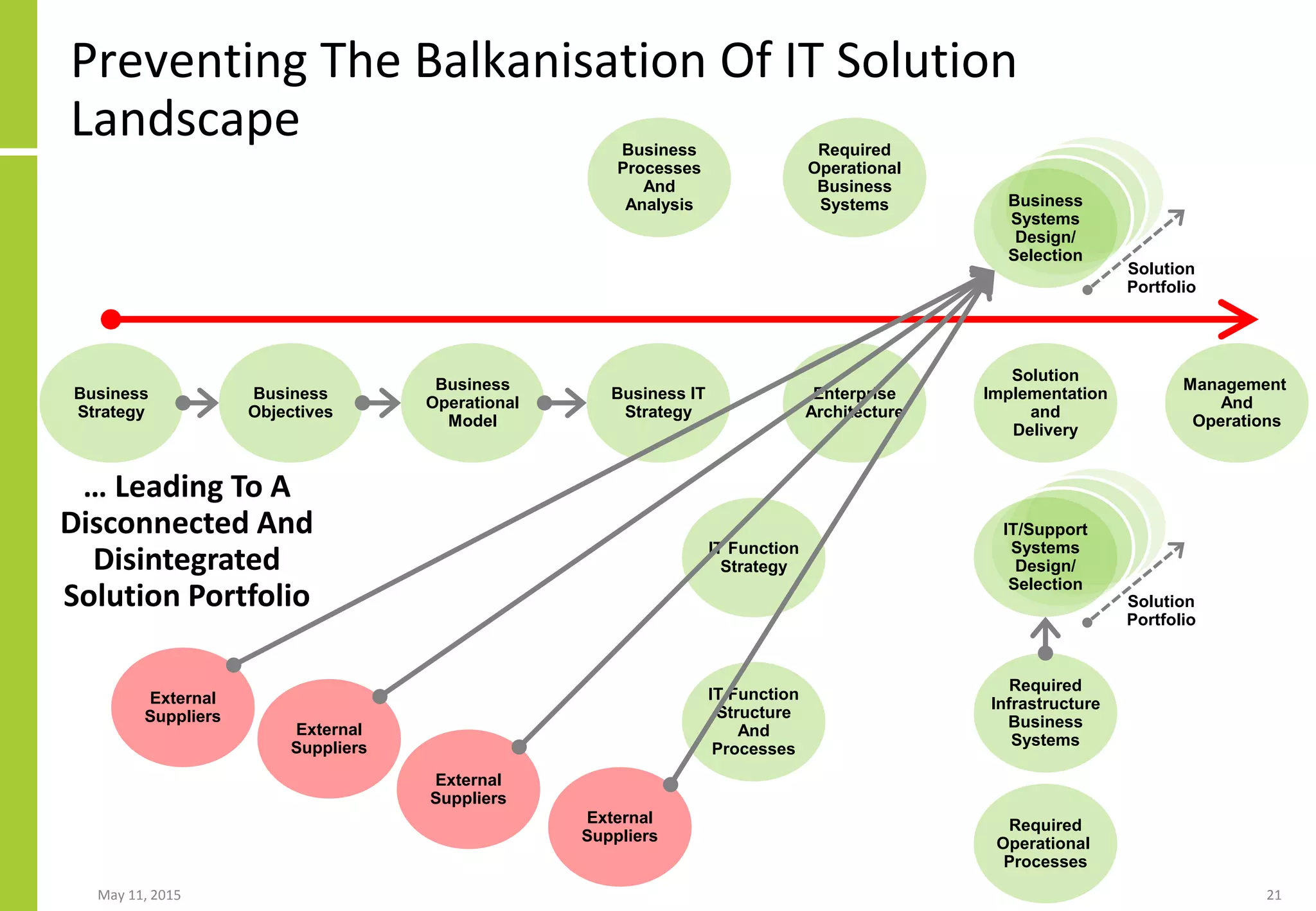
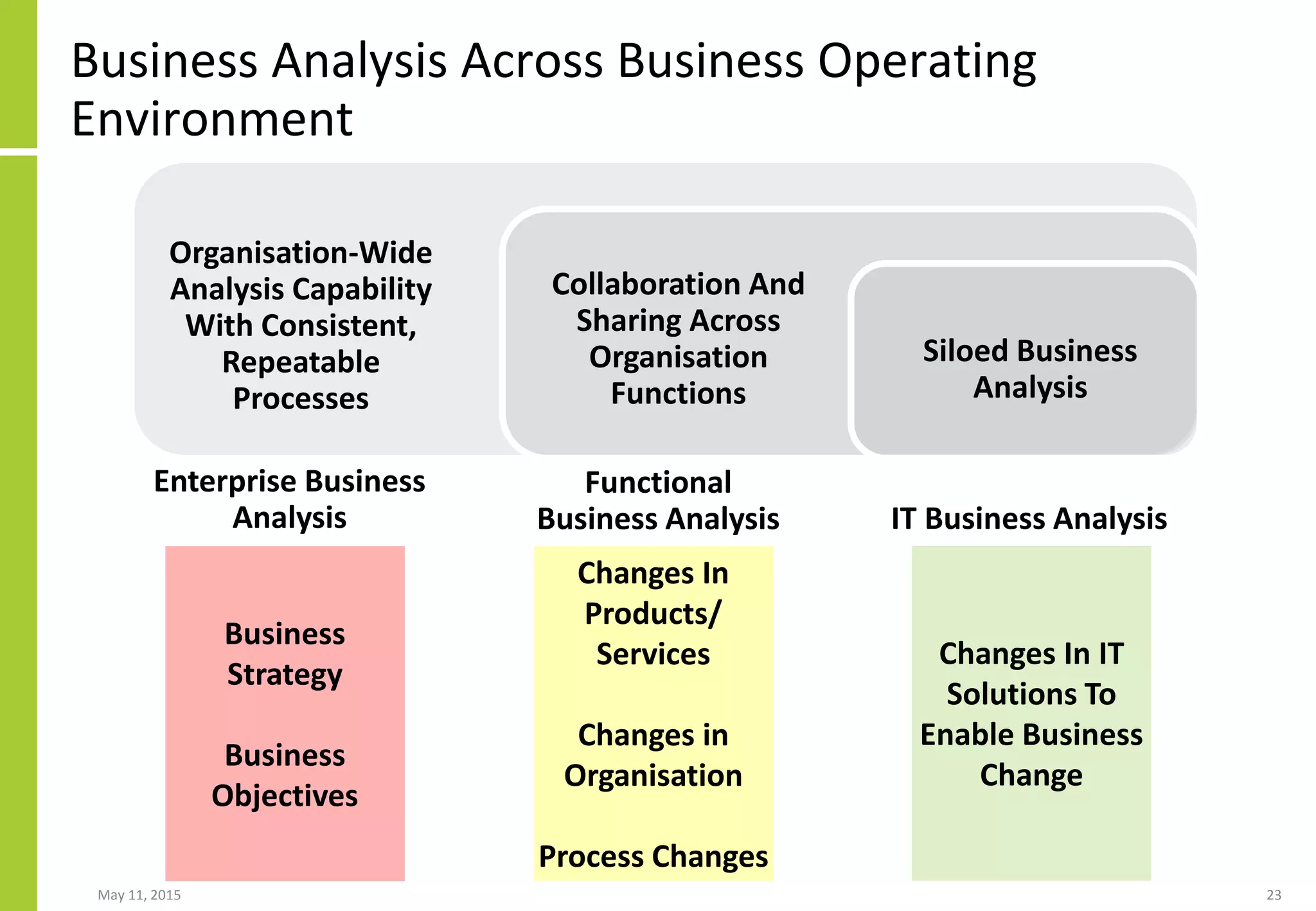
- Multiple levels of business analysis (enterprise, functional, IT) are needed to effectively prevent fragmentation across the organization and deliver solutions in response to business needs from strategy through delivery.
- Without this capability, IT risks delivering solutions that are not