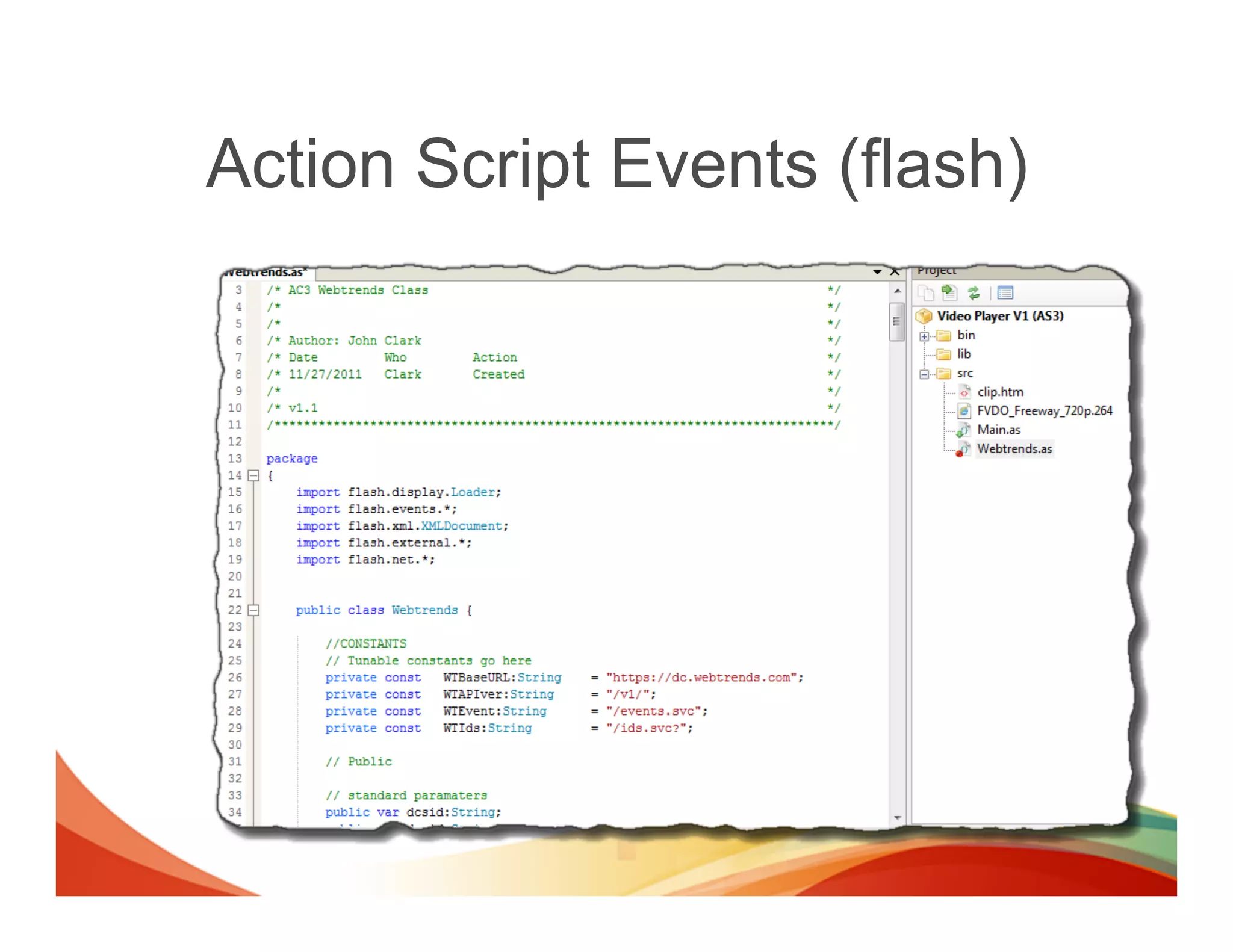
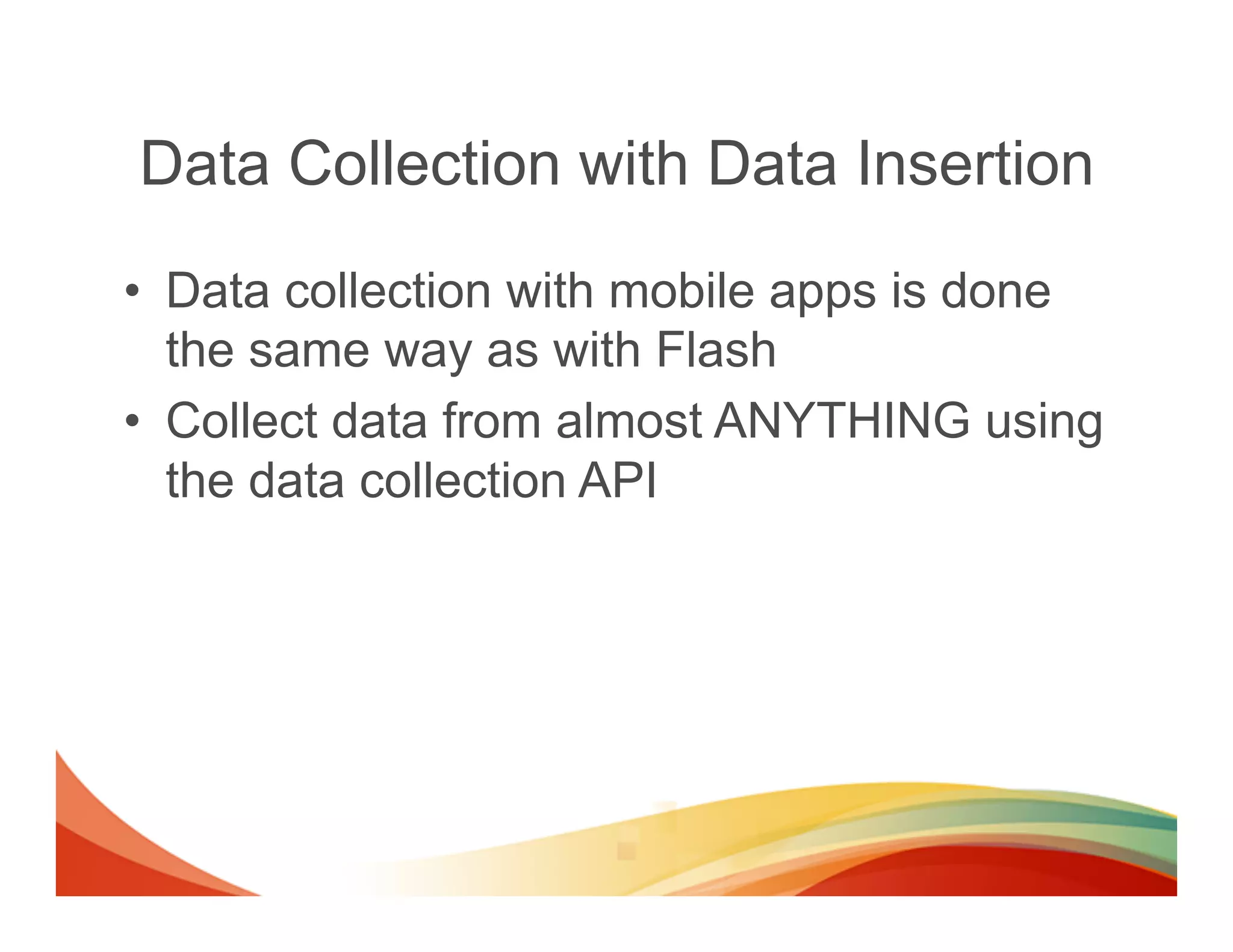
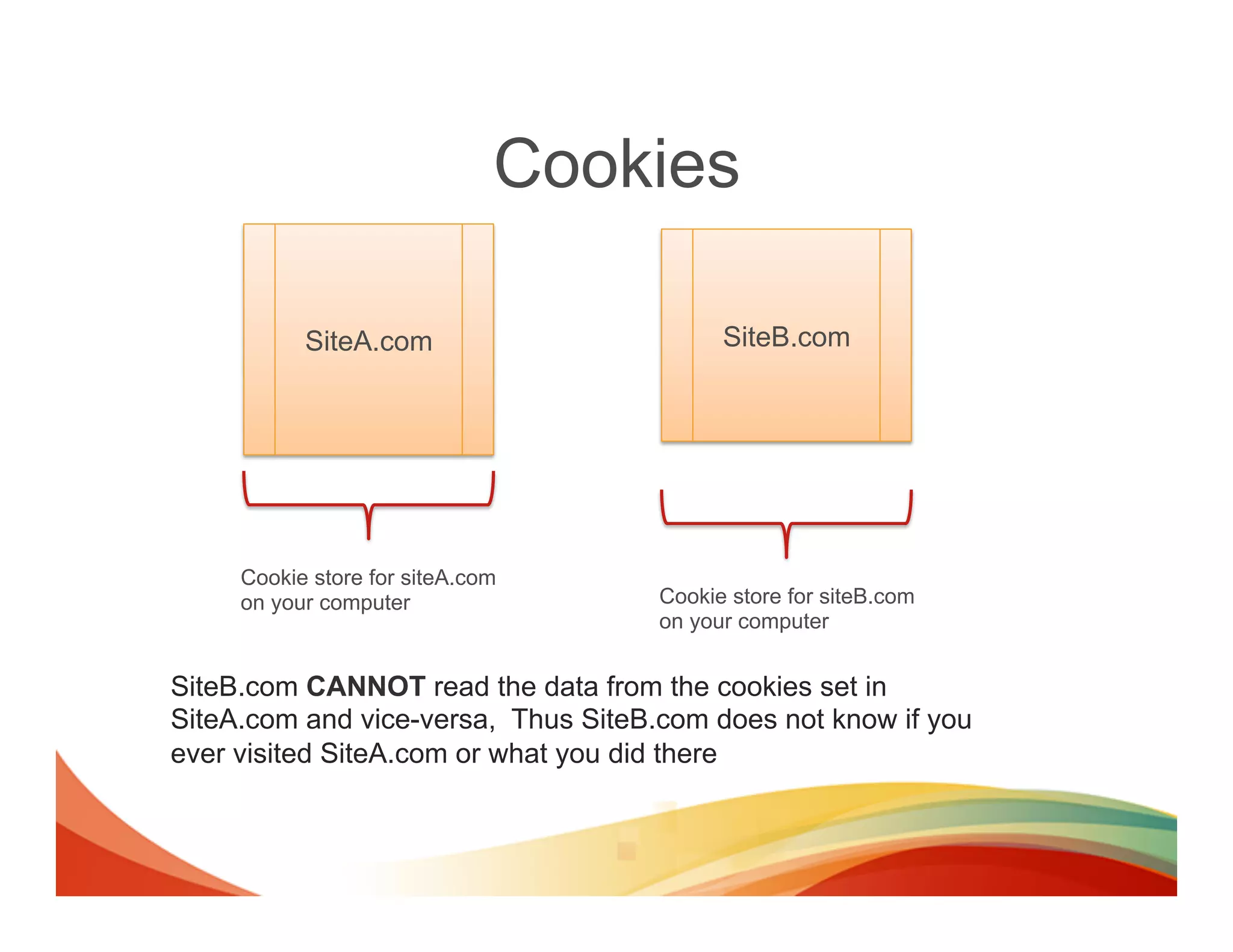
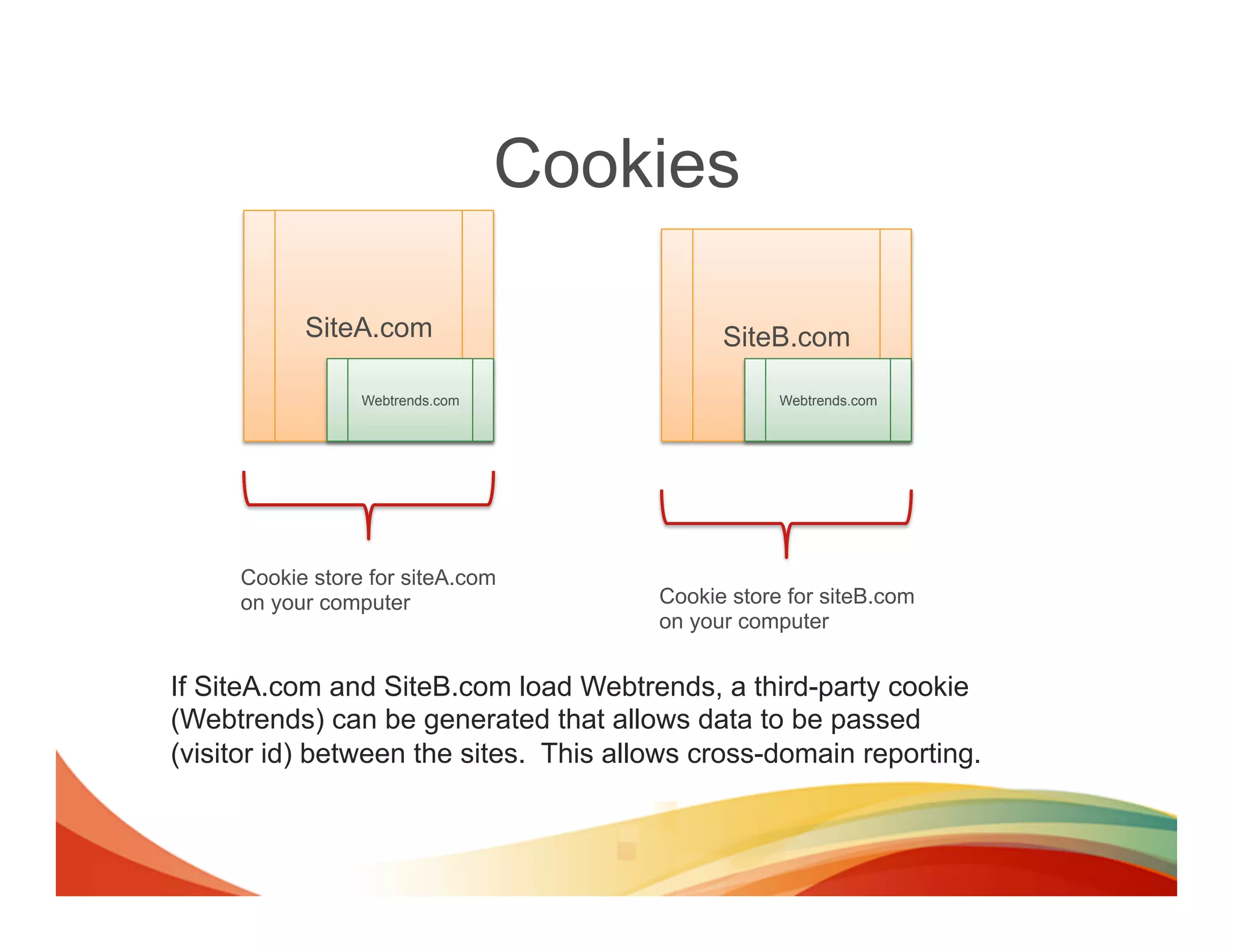
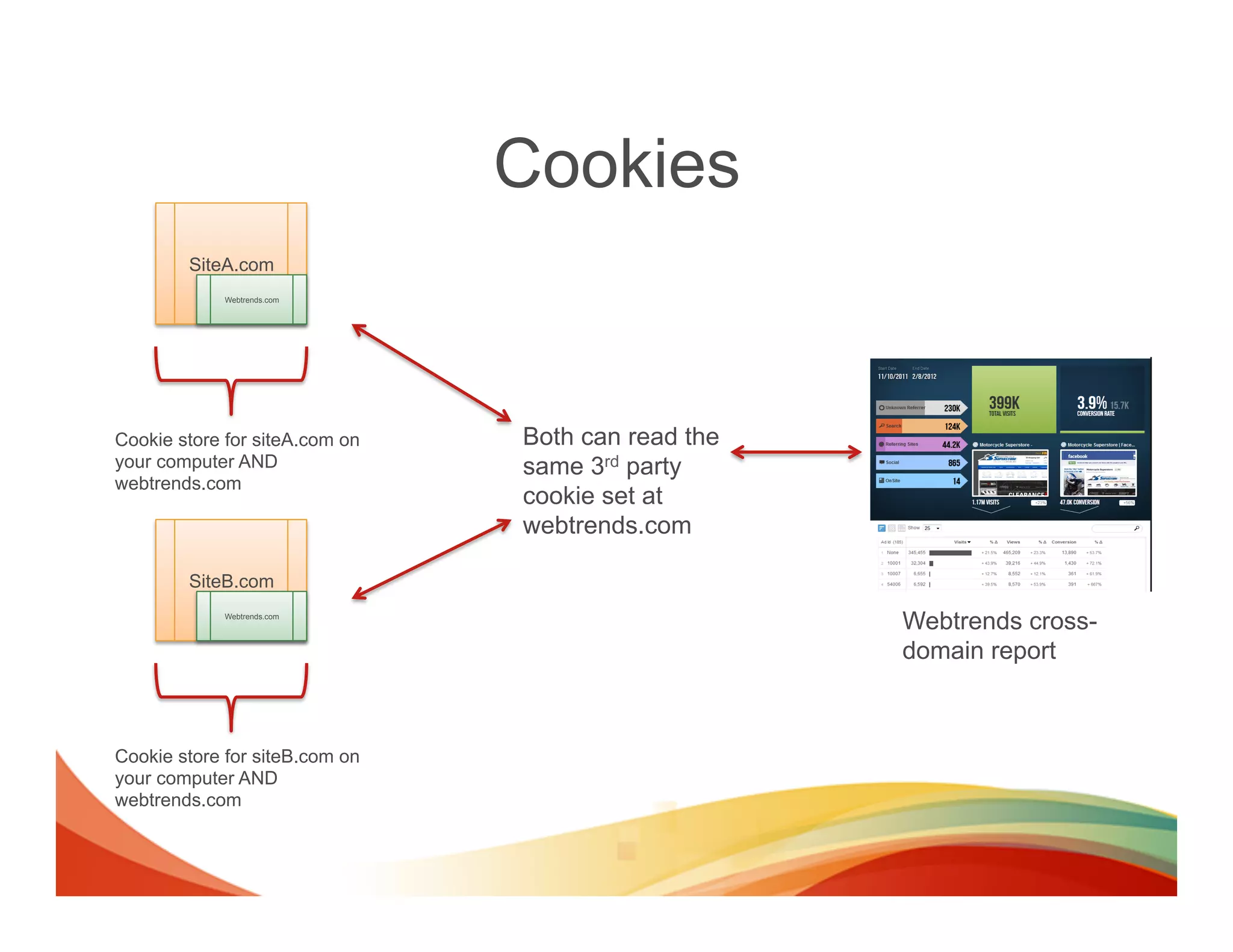
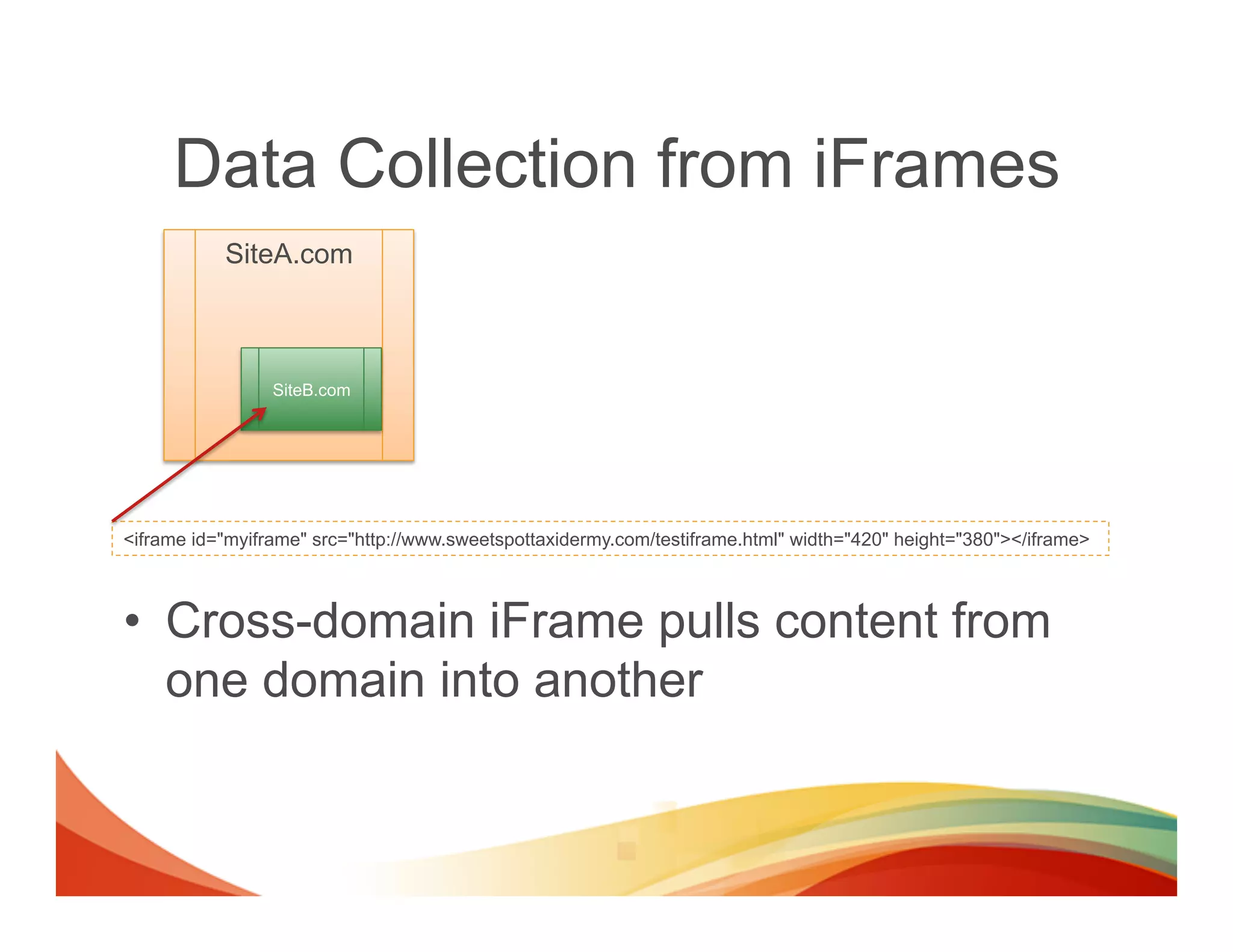
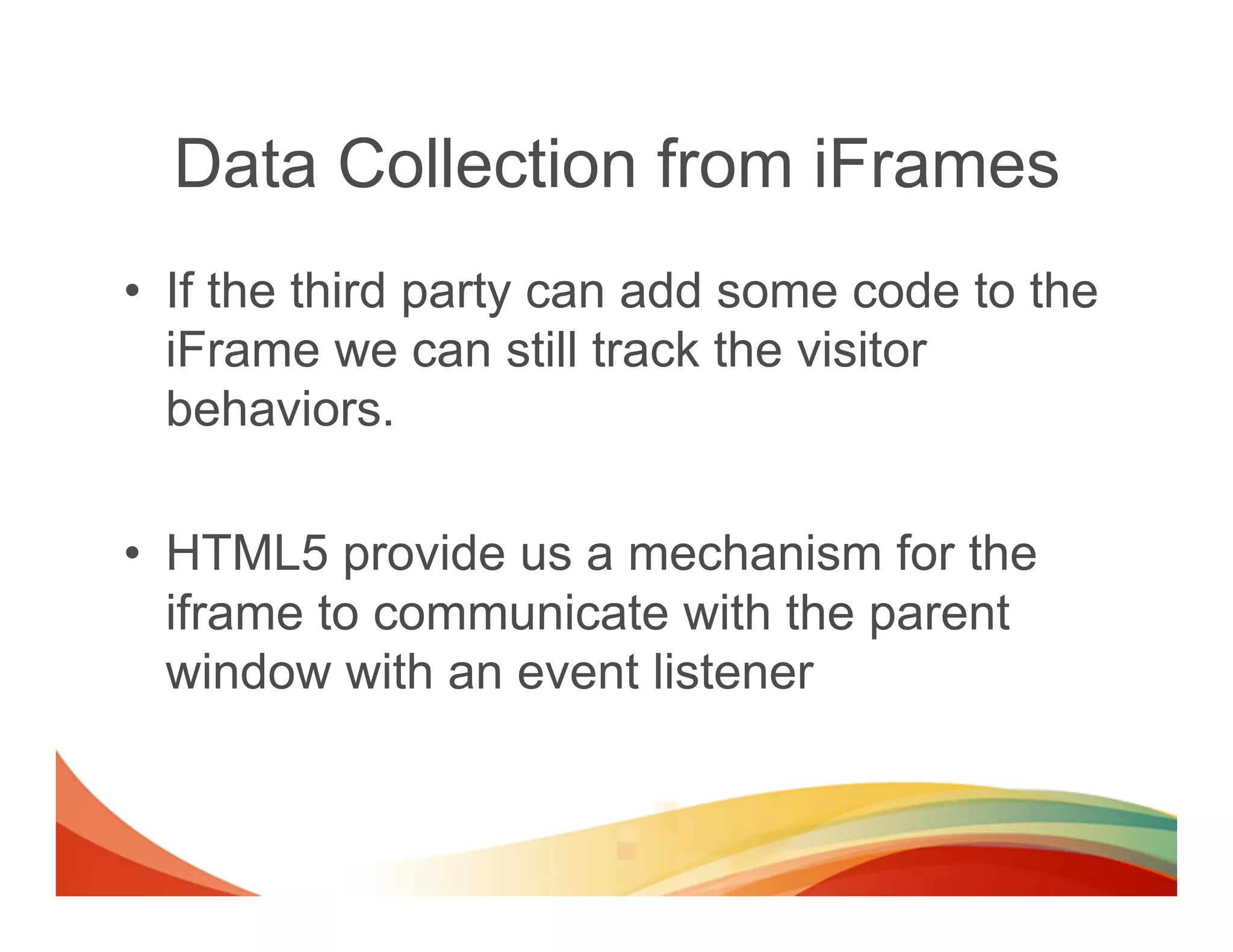
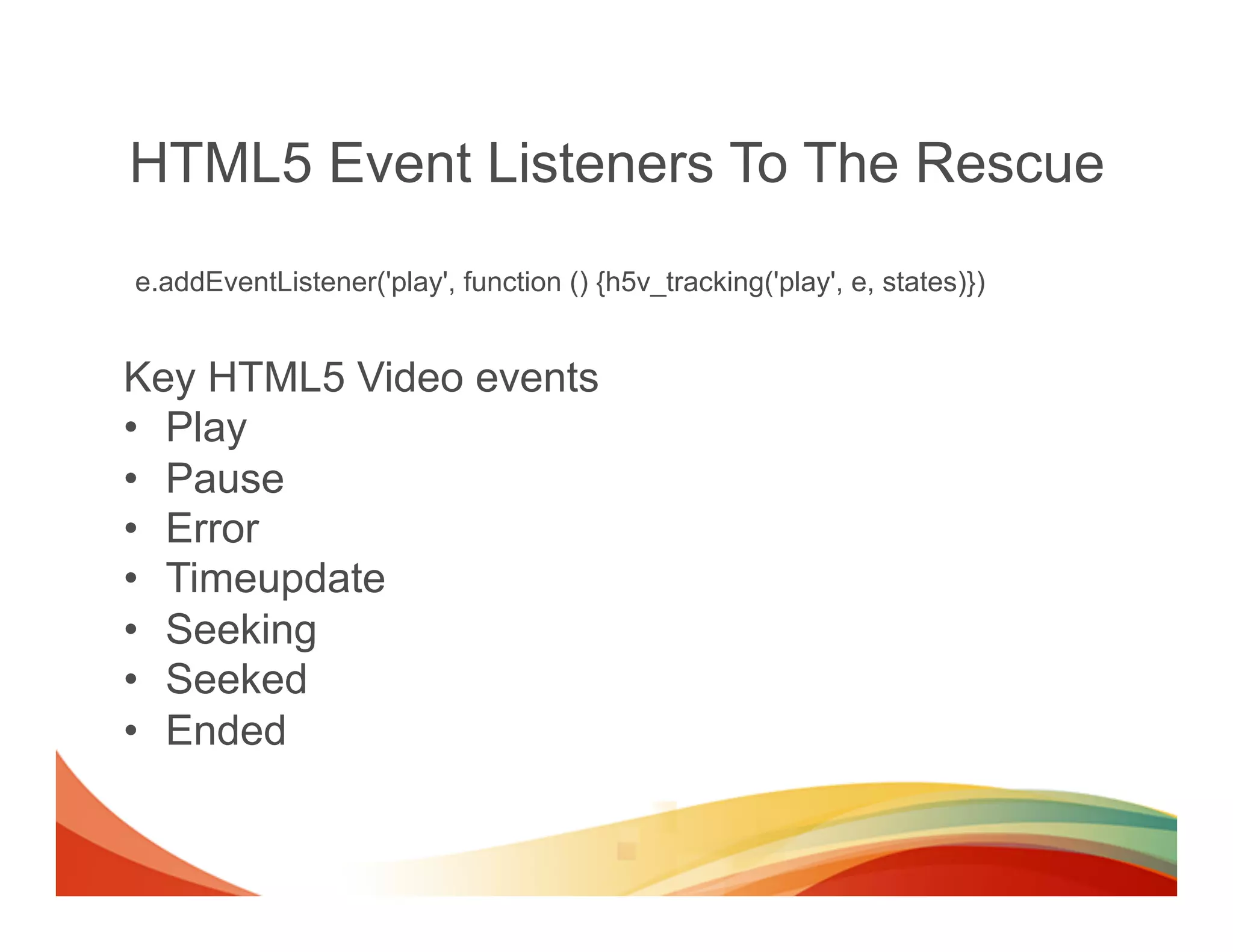
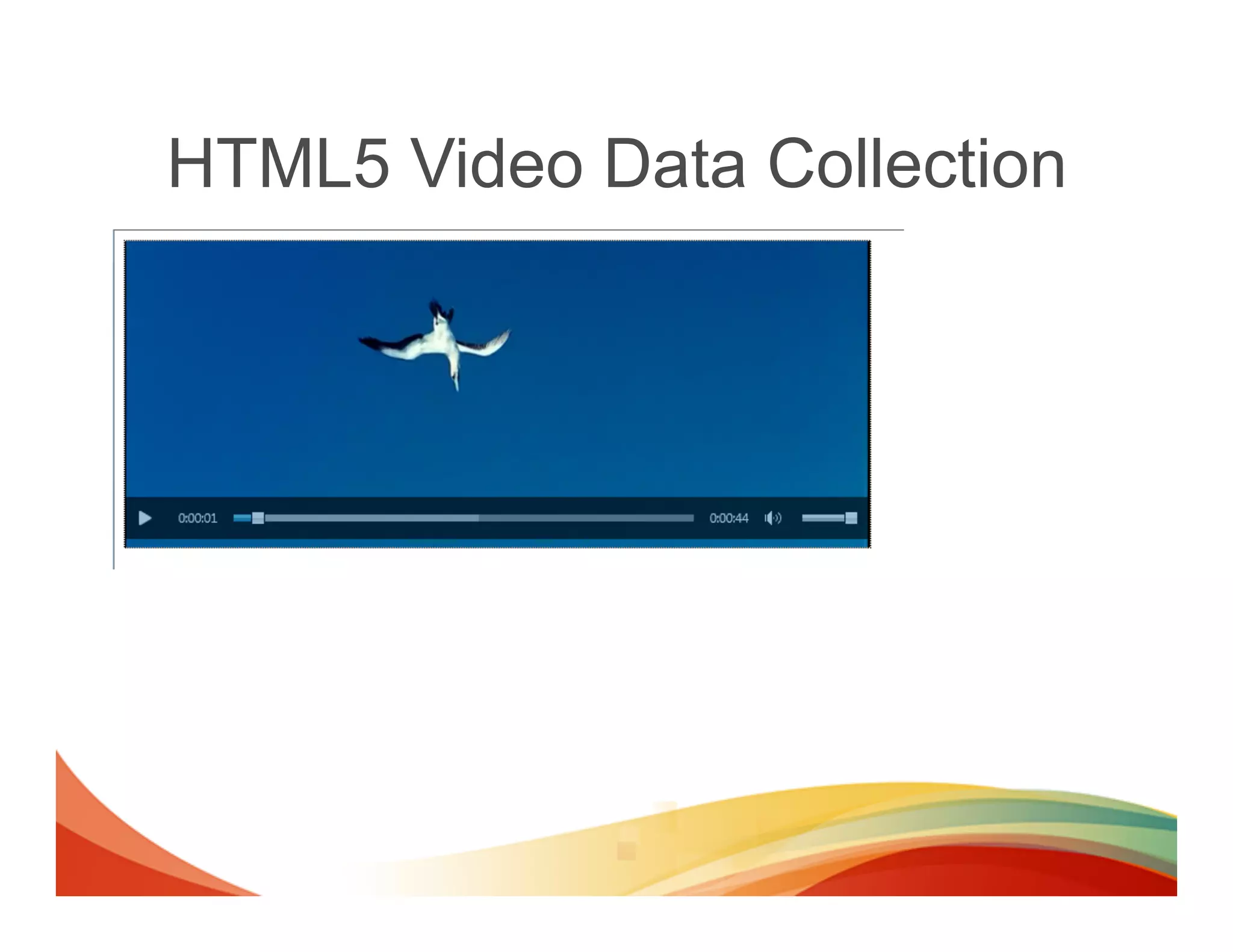
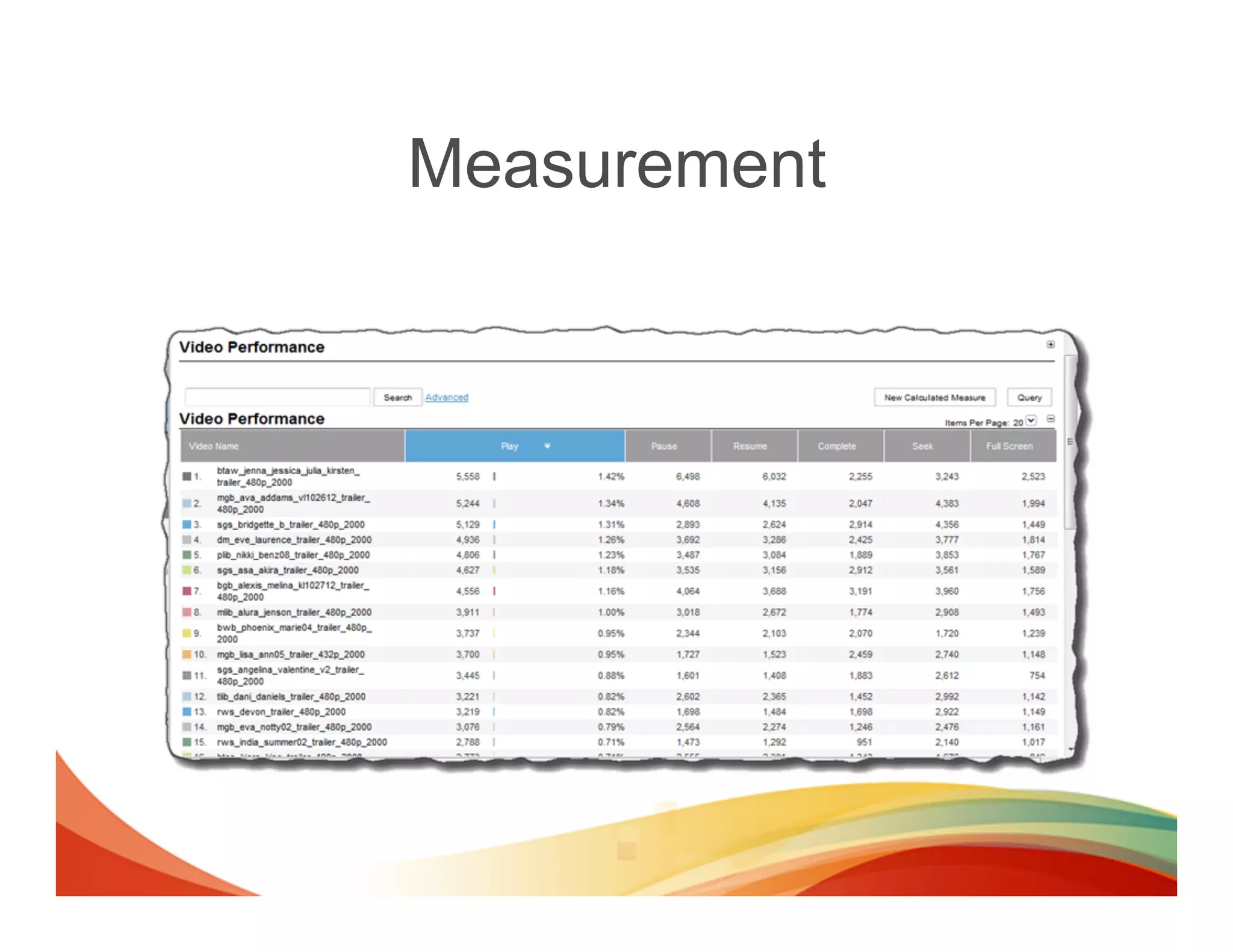
The document discusses methods for collecting multi-channel data across different domains and platforms. It describes how cross-domain tracking works using shared cookies to pass visitor IDs between sites. It also covers using iframes to collect data across domains by adding tracking code or using postMessages. Additionally, it discusses collecting event-based data using selectors and JavaScript events, and capturing video playback events with HTML5 event listeners.
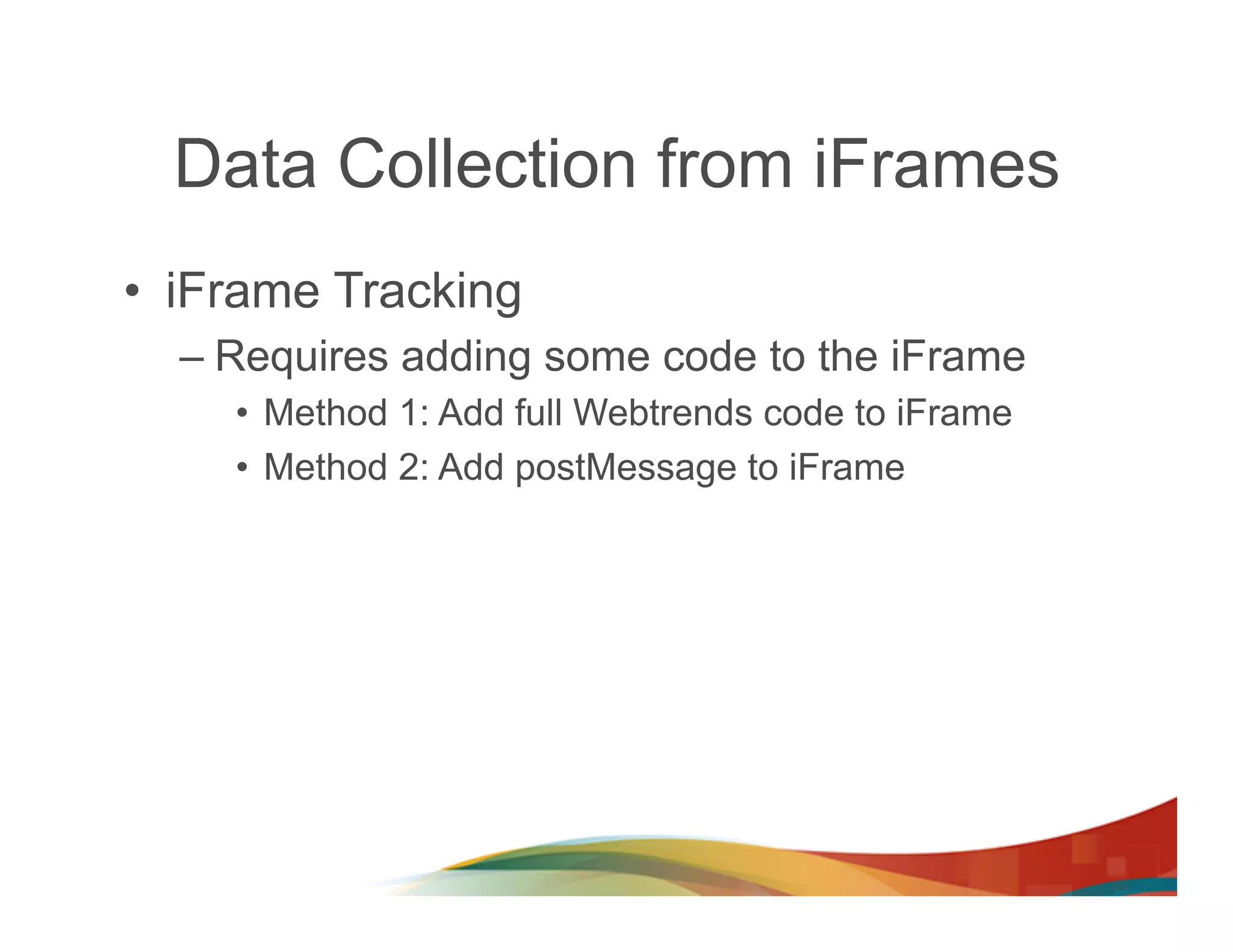
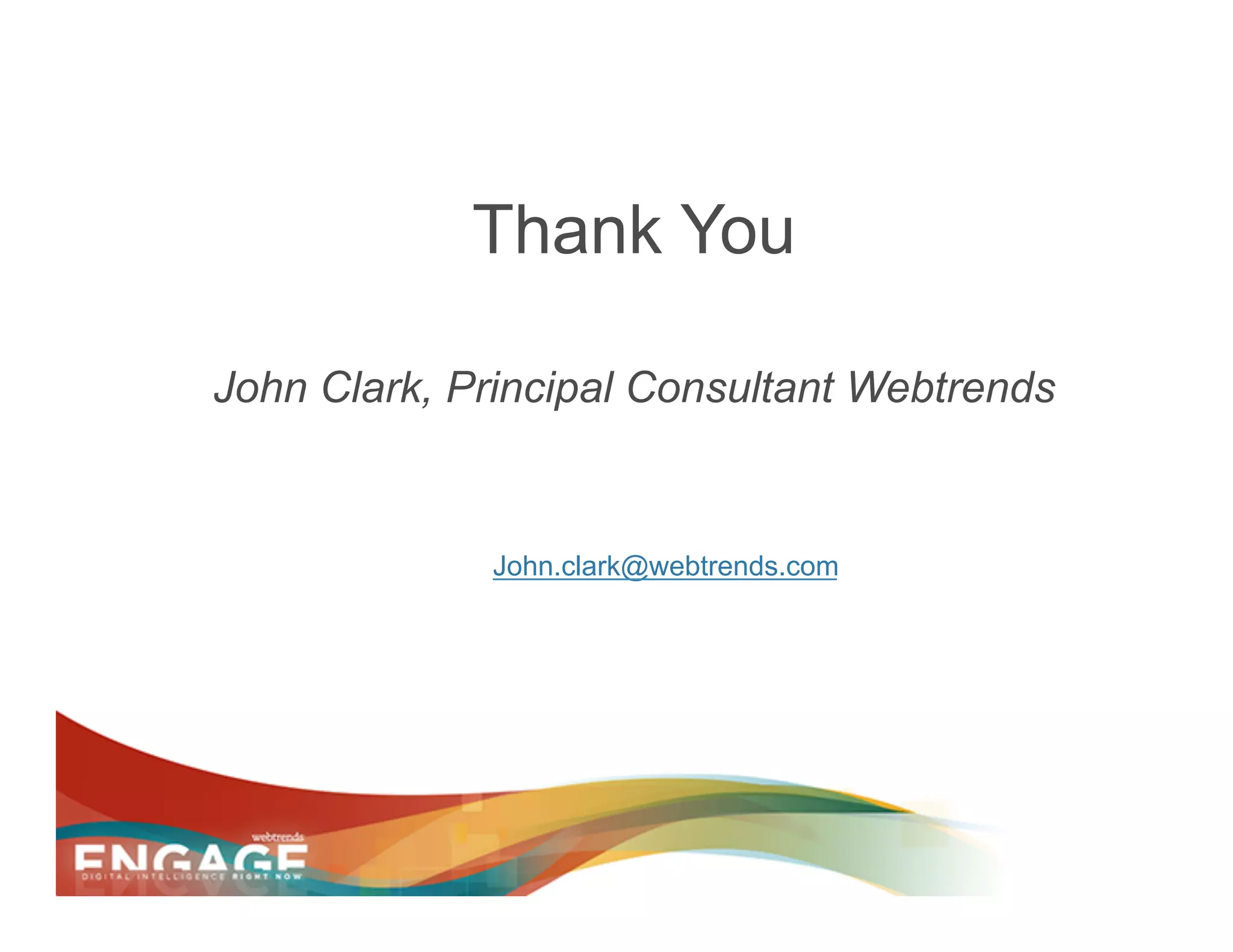
![Site B sends the tracking message to Site A
SiteA.com
<input type="Button" value="Test" name="Test"
SiteB.com onClick="dcsMultiTrack('DCS.dcssip',window.location.hostname,
'DCS.dcsuri',window.location.pathname,
'WT.ti',document.title,
'WT.event','Test Button',
'WT.dl','99')">
<script>
dcsMultiTrack = function() {
var m = Array();
// stringify the arguments
for (obj in arguments) m.push(arguments[obj]);
// send to the listner in the parent window
window.parent.postMessage([m], "*");
}
</script>
<script>
window.addEventListener("message", function(e) { Webtrends.multiTrack({argsa: e.data.split(",")}) } ,false);
</script>](https://image.slidesharecdn.com/engage-2013multi-channel-data-130205182728-phpapp02/75/Engage-2013-Multi-Channel-Data-Collection-18-2048.jpg)
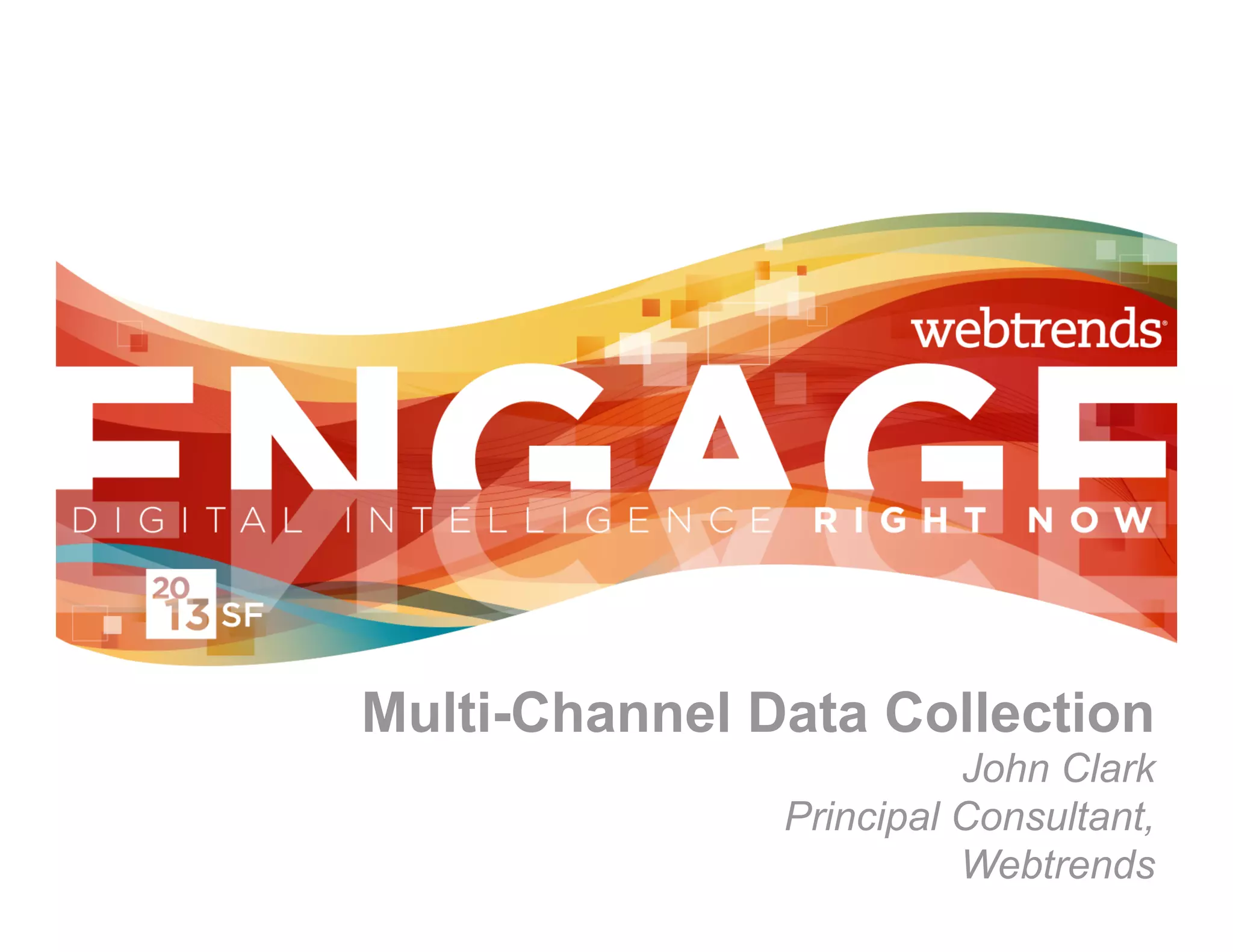
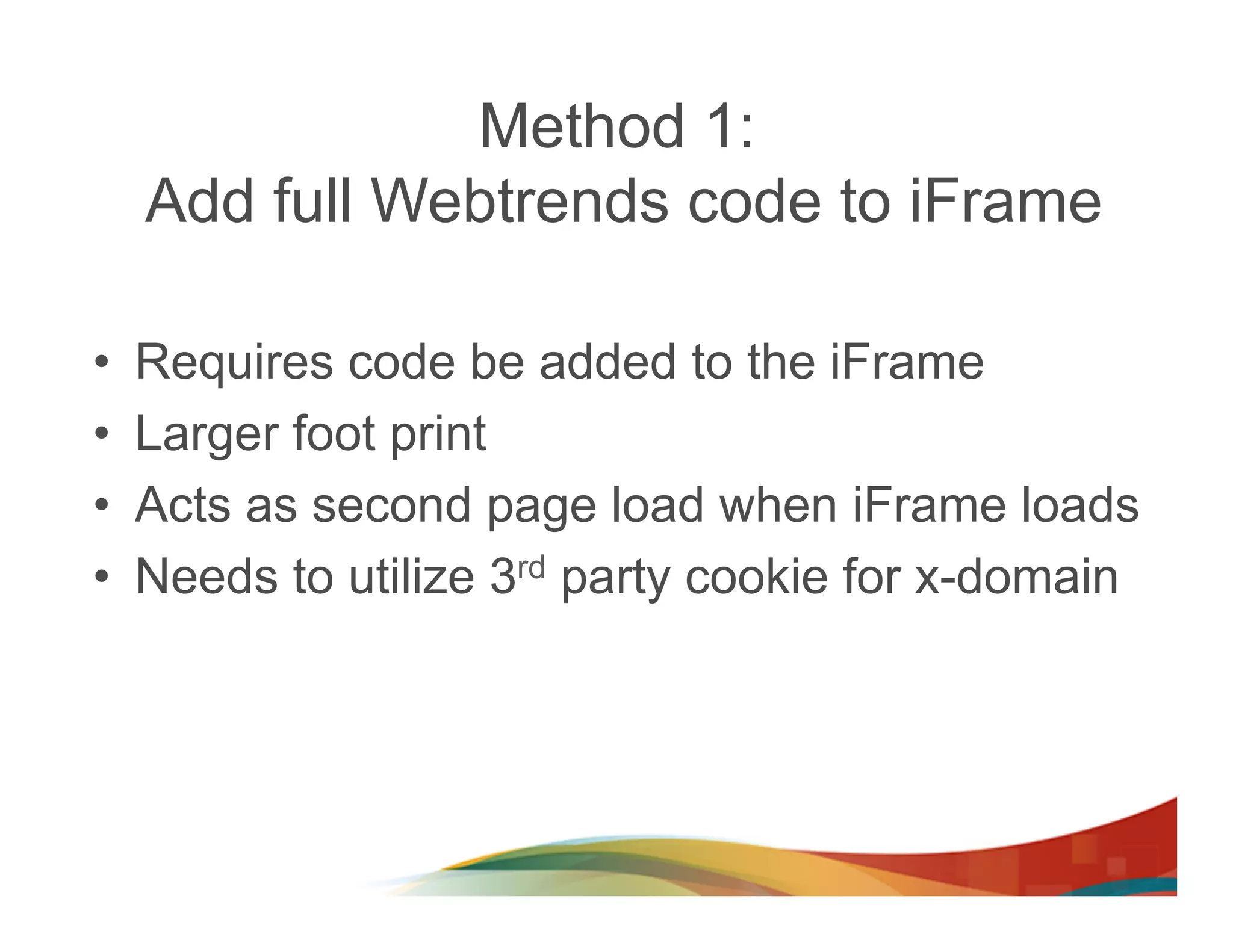
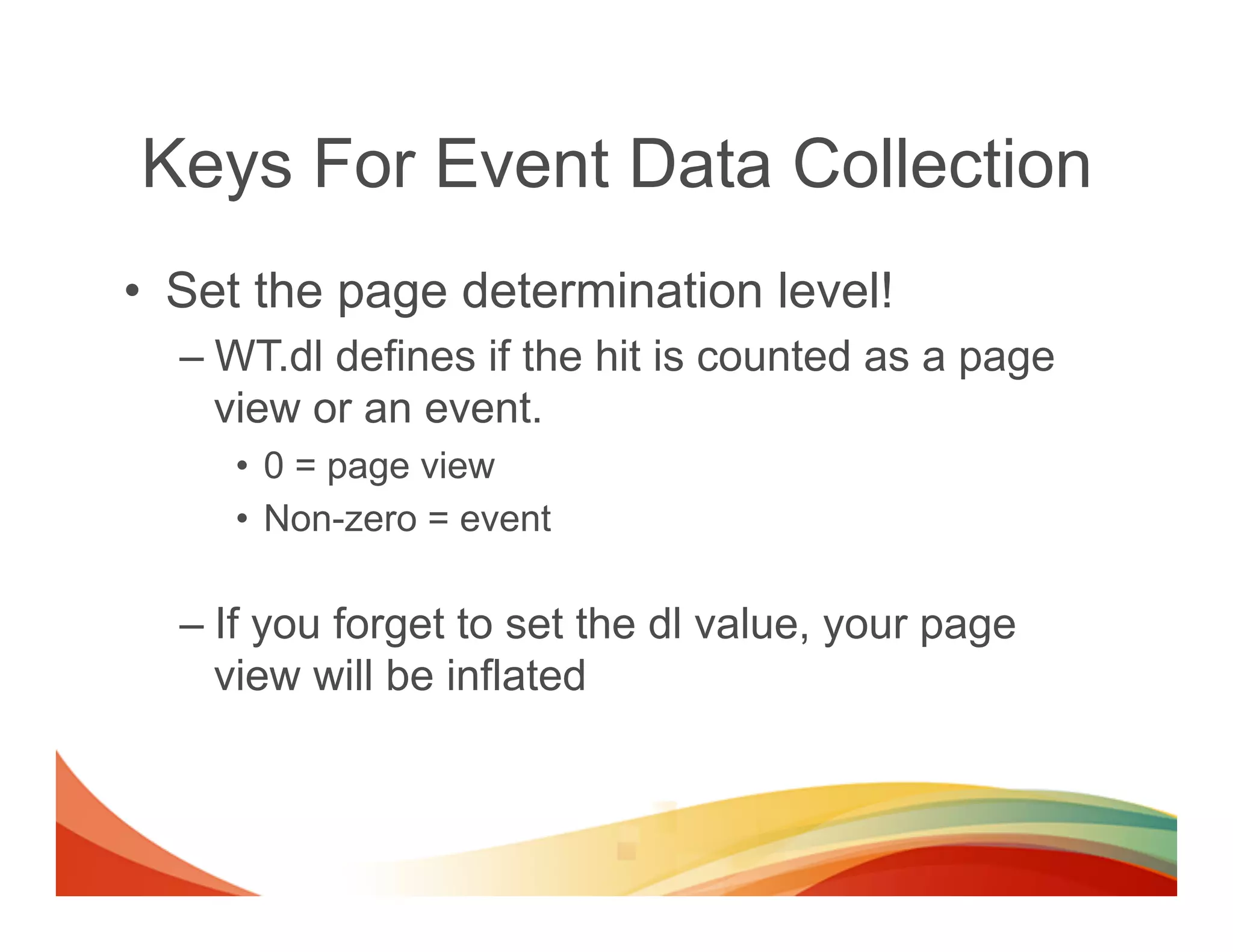
![Event Data Collection
• Collecting event based data is easy with Webtrends!
– Track when a visitor clicks a checkbox in a filter object
jQuery Selector Webtrends Selector
jQuery('.filterOption').live('click', function (evt) { dcs.addSelector(‘.filterOption'’,
transform: function (dcsObject, o) {
var e = evt.target || evt.srcElement;
var e = o[‘element’];
Webtrends.multiTrack({
element: this, o.argsa.push ("DCS.dcssip", window.location.hostname,
argsa: ["DCS.dcssip", window.location.hostname, "DCS.dcsuri", window.location.pathname,
"DCS.dcsuri", window.location.pathname, "WT.ti", document.title,
"WT.ti", document.title, "WT.dl", "31",
"WT.dl", "31", "WT.e_nam", jQuery(e).text(),
"WT.e_nam", jQuery(e).text(), "WT.e_typ", 'filter',
"WT.e_typ", 'filter', "WT.e_state", ", e.checked?’true’:’false’);
"WT.e_state", e.checked?’true’:’false’] }
}) });
});
• Using this technique you can track almost any page event on any
object. (hoverovers, focus, clicks, tap, swipe, …)](https://image.slidesharecdn.com/engage-2013multi-channel-data-130205182728-phpapp02/75/Engage-2013-Multi-Channel-Data-Collection-23-2048.jpg)
![No Clear Standards - Yet
[…]
standard metrics
have yet to be
established. One-
third said their clients
considered unique viewers
to be the best way to
measure audience. Another
one-quarter said it was
target impressions.
[…]
Source: http://www.emarketer.com/Articles/Print.aspx?R=1009195](https://image.slidesharecdn.com/engage-2013multi-channel-data-130205182728-phpapp02/75/Engage-2013-Multi-Channel-Data-Collection-33-2048.jpg)