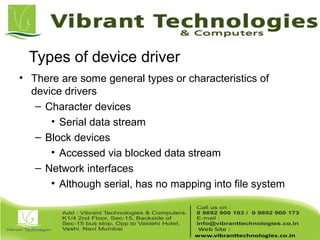
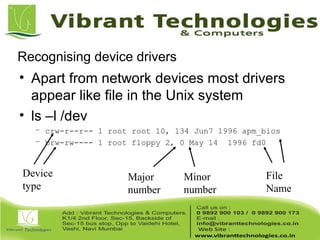
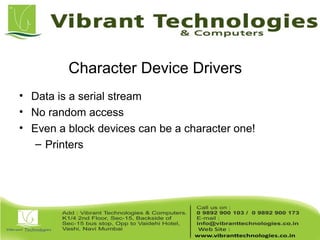
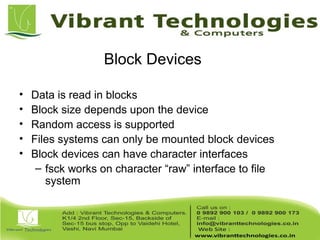
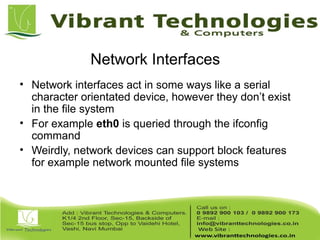
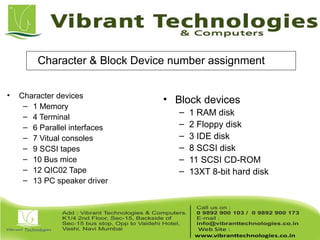
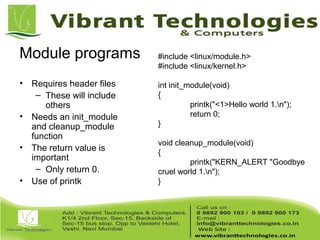
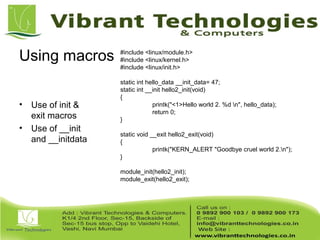
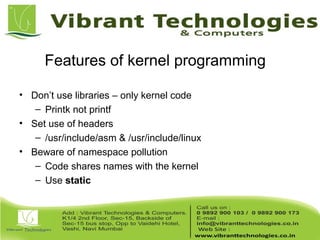
The document provides an introduction to device drivers in embedded system programming, explaining their role as software interfaces to hardware resources within the kernel. It distinguishes between different types of device drivers, such as character and block devices, and discusses the structure and features of kernel modules used for dynamic loading in the Linux operating system. Additionally, it outlines key concepts and requirements for module programming, including the necessary functions and handling of kernel processes.