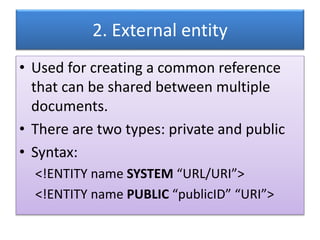
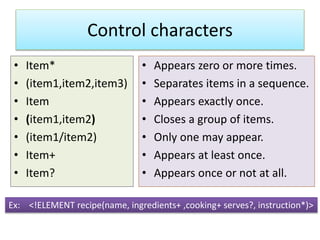
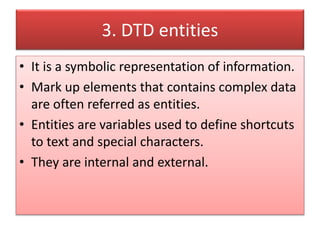
The document outlines the structure and components of XML documents, focusing on declaring elements, attributes, and entities. It details the syntax for defining elements and their attributes, including control characters for item occurrences, and distinguishes between internal and external entities. The examples provided illustrate how to implement these concepts in XML DTD (Document Type Definition).

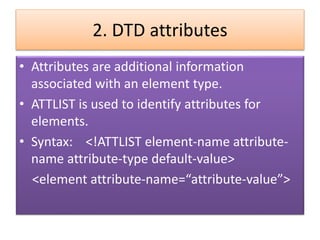
![• Ex:
<?xml version=“1.0”>
<!DOCTYPE image[
<!ELEMENT image EMPTY>
<!ATTLIST image height CDATA #REQUIRED>
<!ATTLIST image width CDATA #REQUIRED>
]>
<image height=“32” width=“32”>](https://image.slidesharecdn.com/unitvdtd-200424144428/85/DTD-elements-5-320.jpg)
![1. Internal entity
• Refers to data that an XML processor has to
parse.
• Syntax: <!ENTITY name “entity value”>
Ex:
<?xml version=“1.0”>
<!DOCTYPE letter[
<!ENTITY hbd “happy birth day”>
]>
<letter> &hbd;</letter>](https://image.slidesharecdn.com/unitvdtd-200424144428/85/DTD-elements-7-320.jpg)