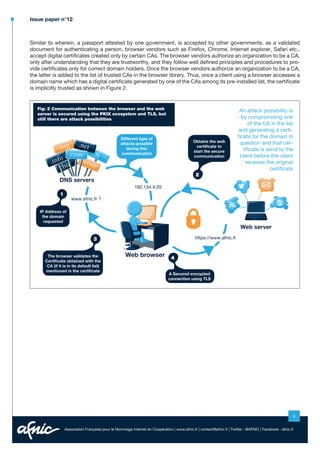
The document discusses the need for secure communication over the internet, especially when sensitive data is involved, and highlights the vulnerabilities in existing systems like x.509 public key infrastructure (PKIX). It introduces the DANE protocol, which aims to provide end-to-end security by leveraging DNS security extensions (DNSSEC) to authenticate domain names and their corresponding certificates. DANE offers a solution to the risks posed by compromised Certificate Authorities and enhances the overall security of internet communications.