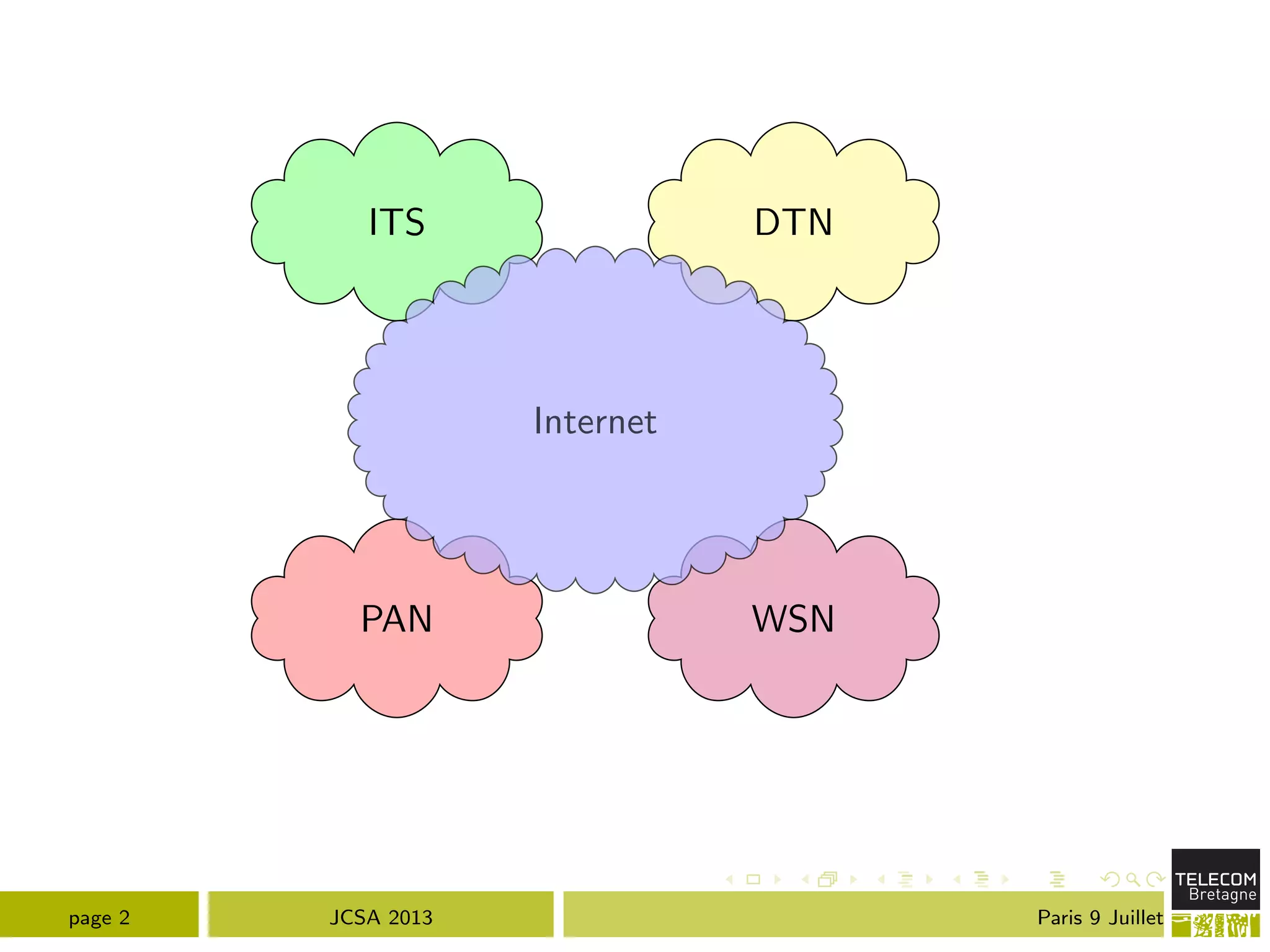
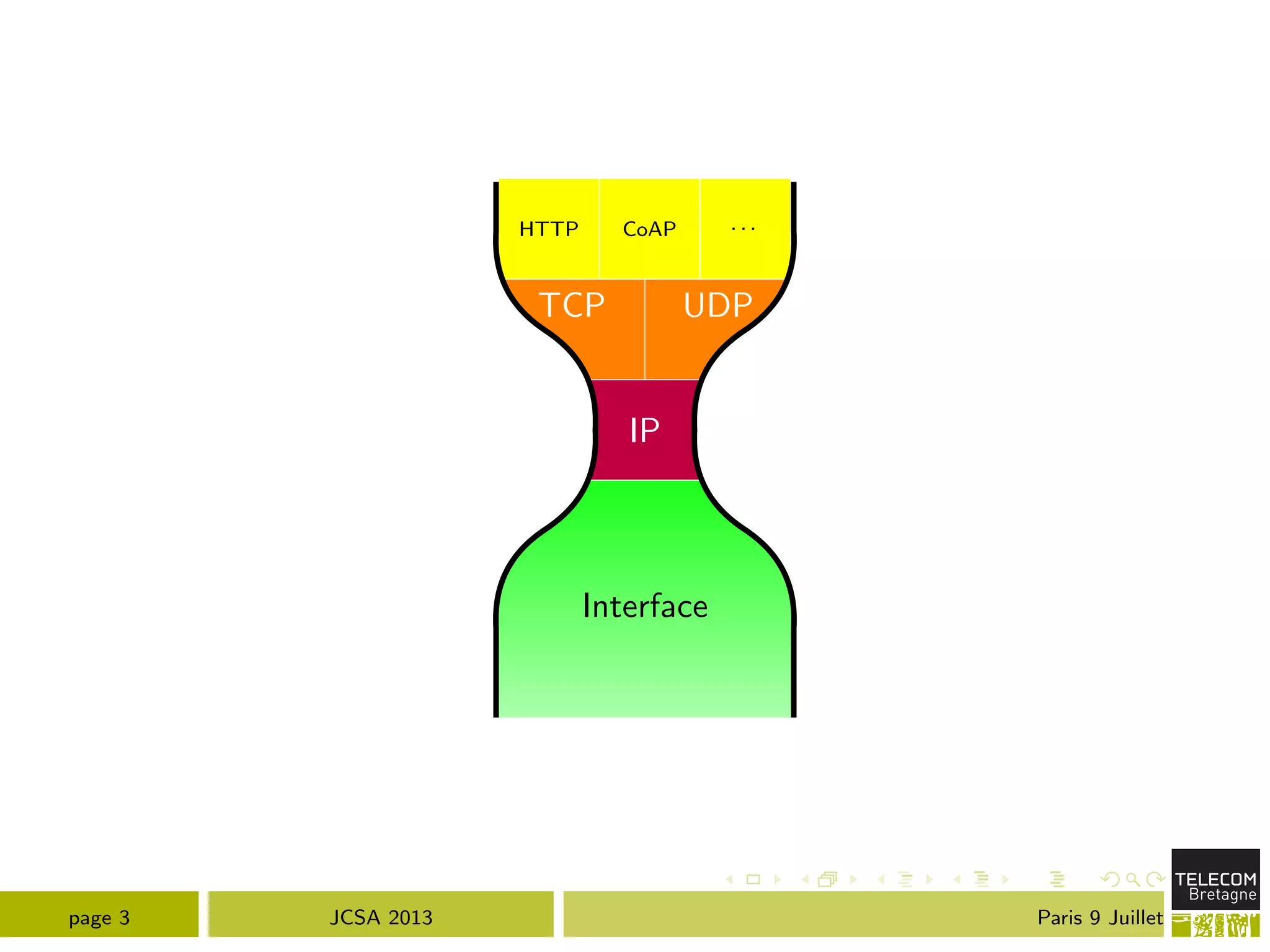
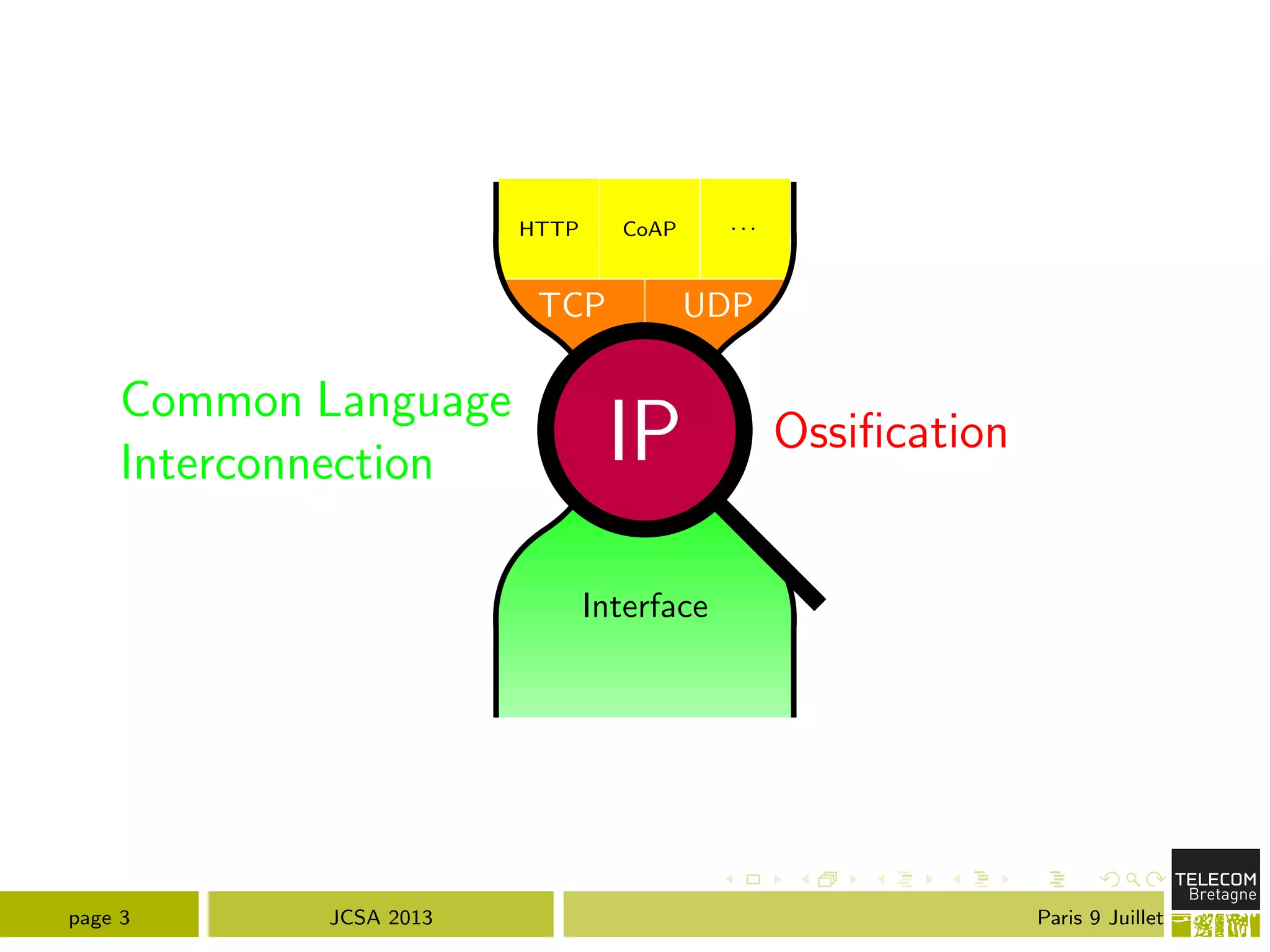
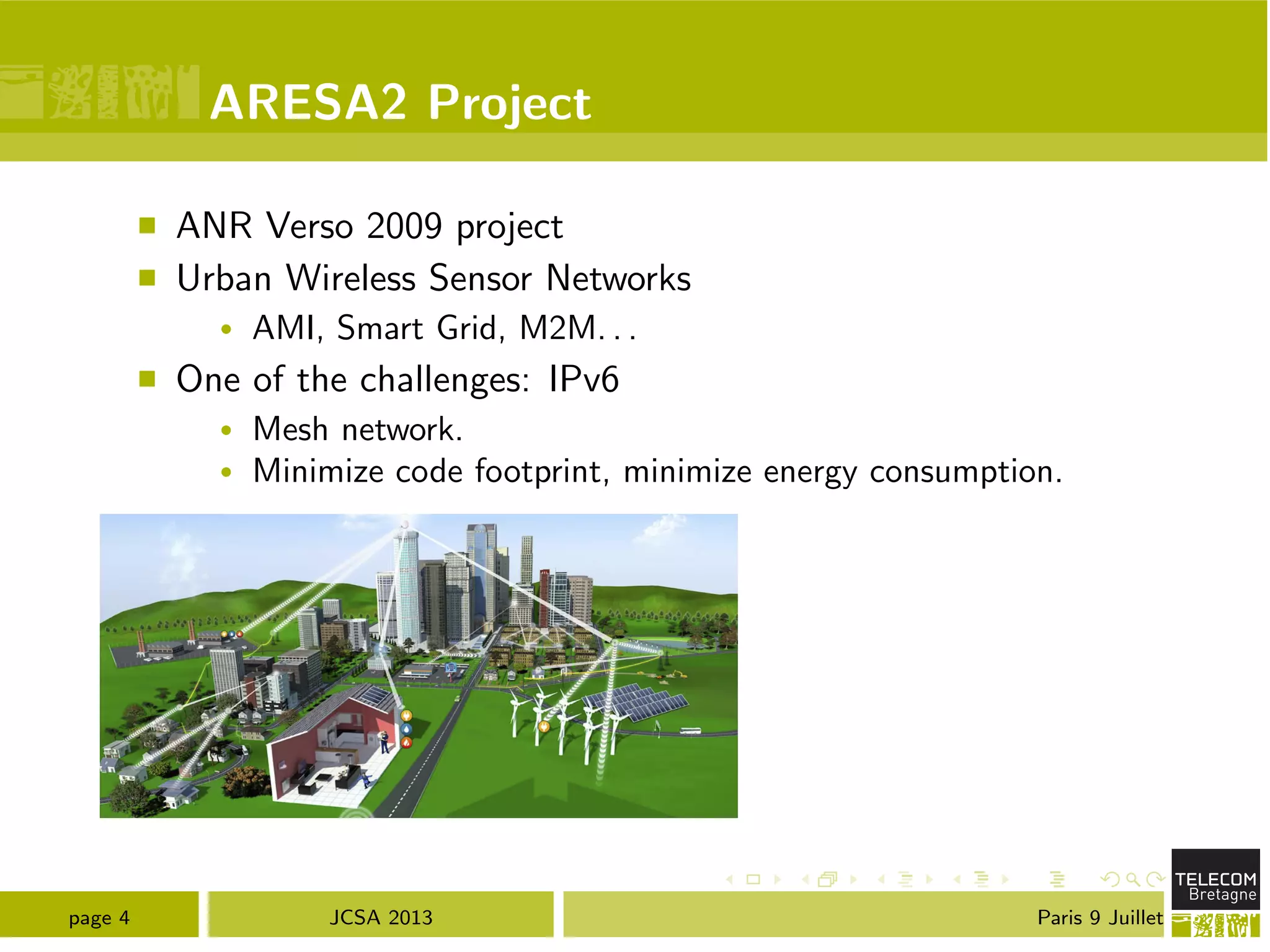
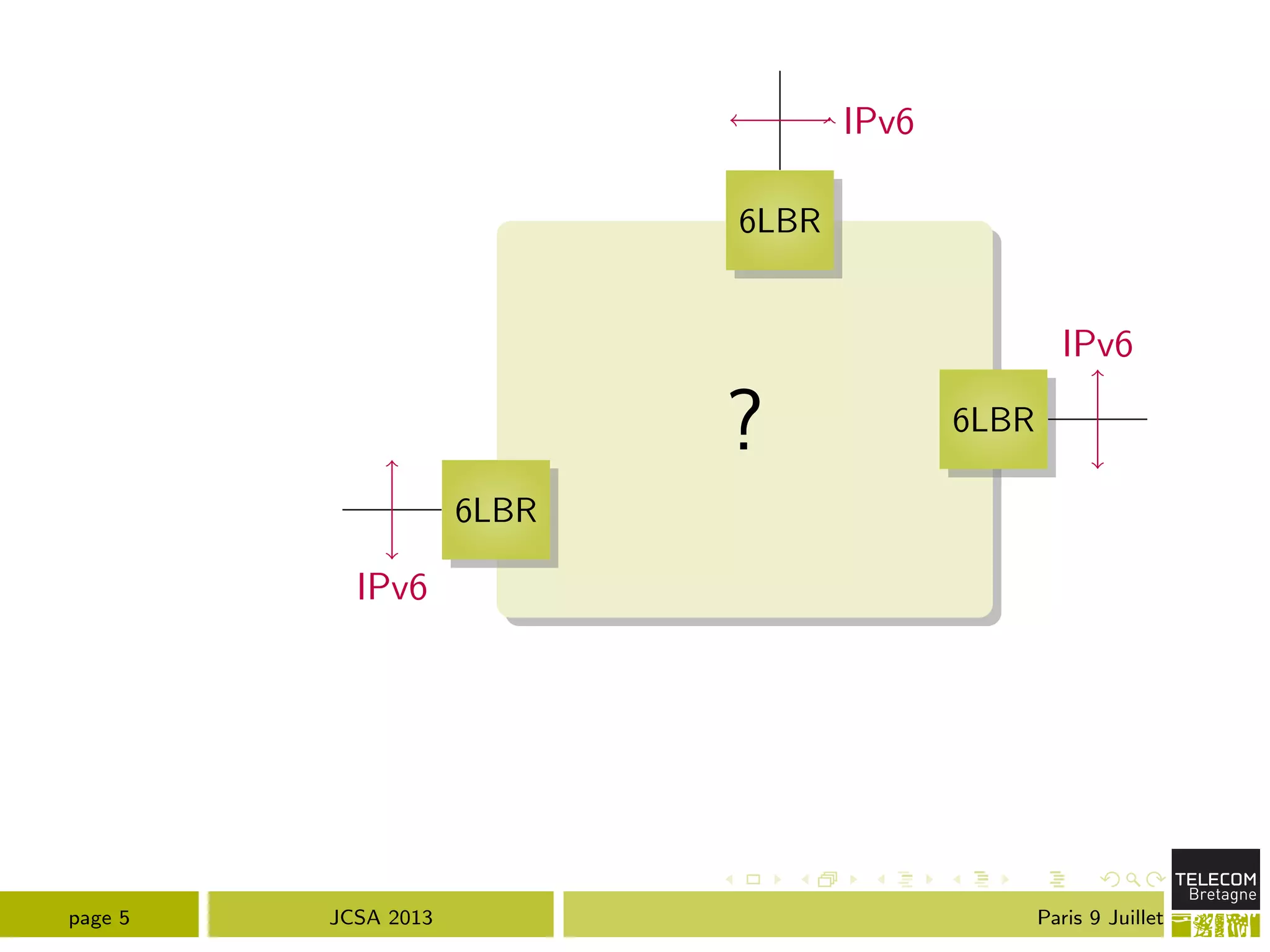
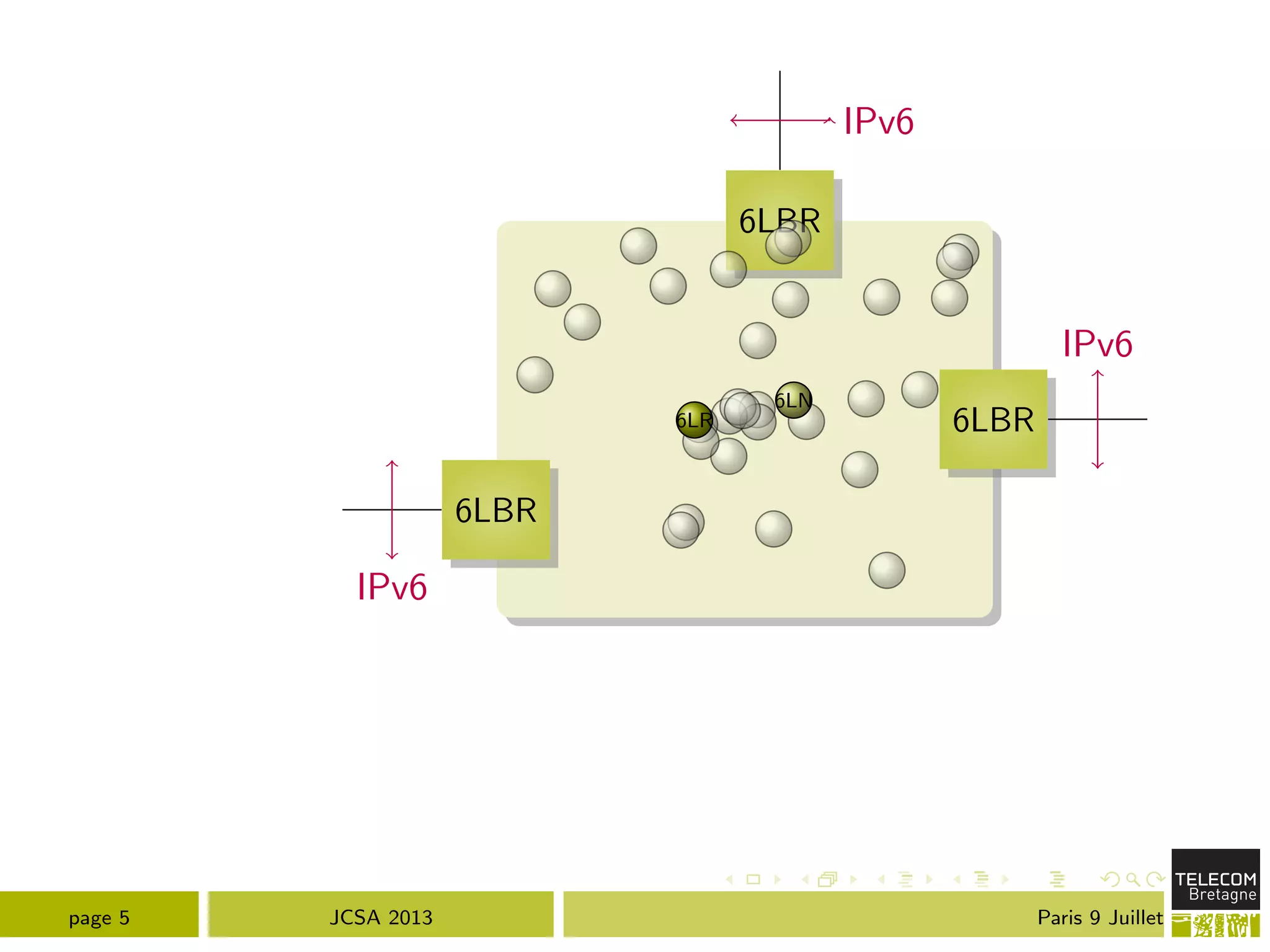
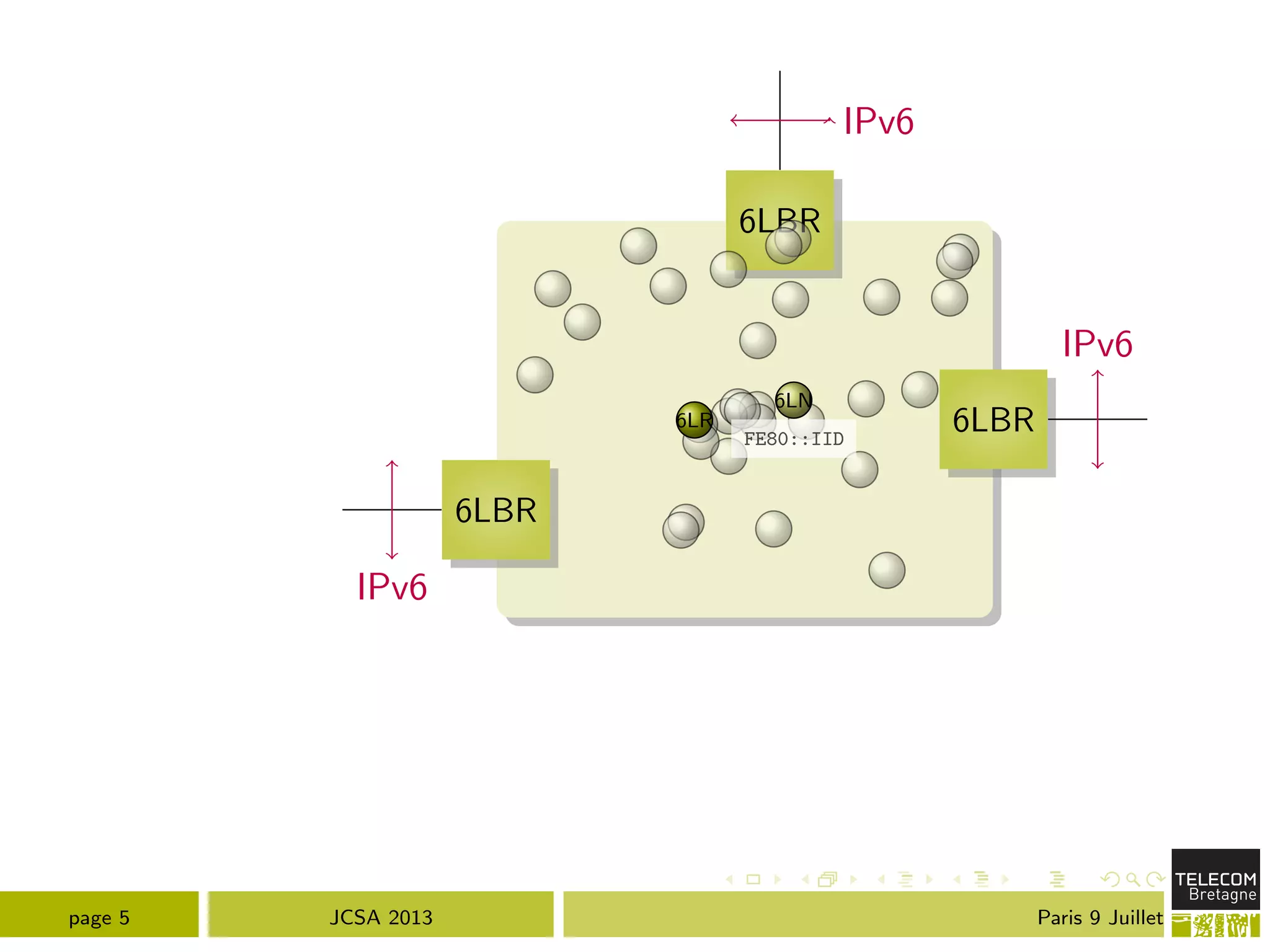
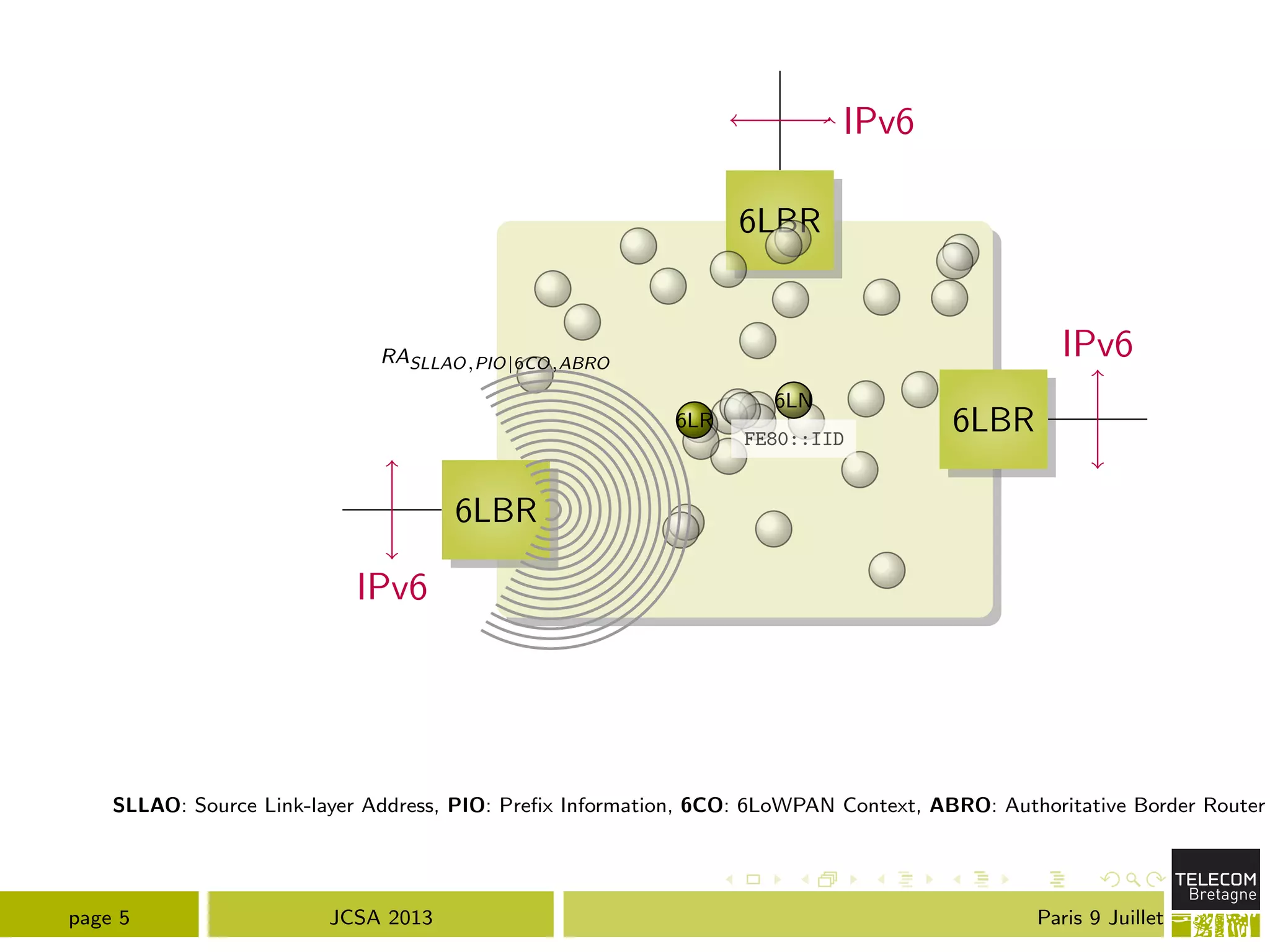
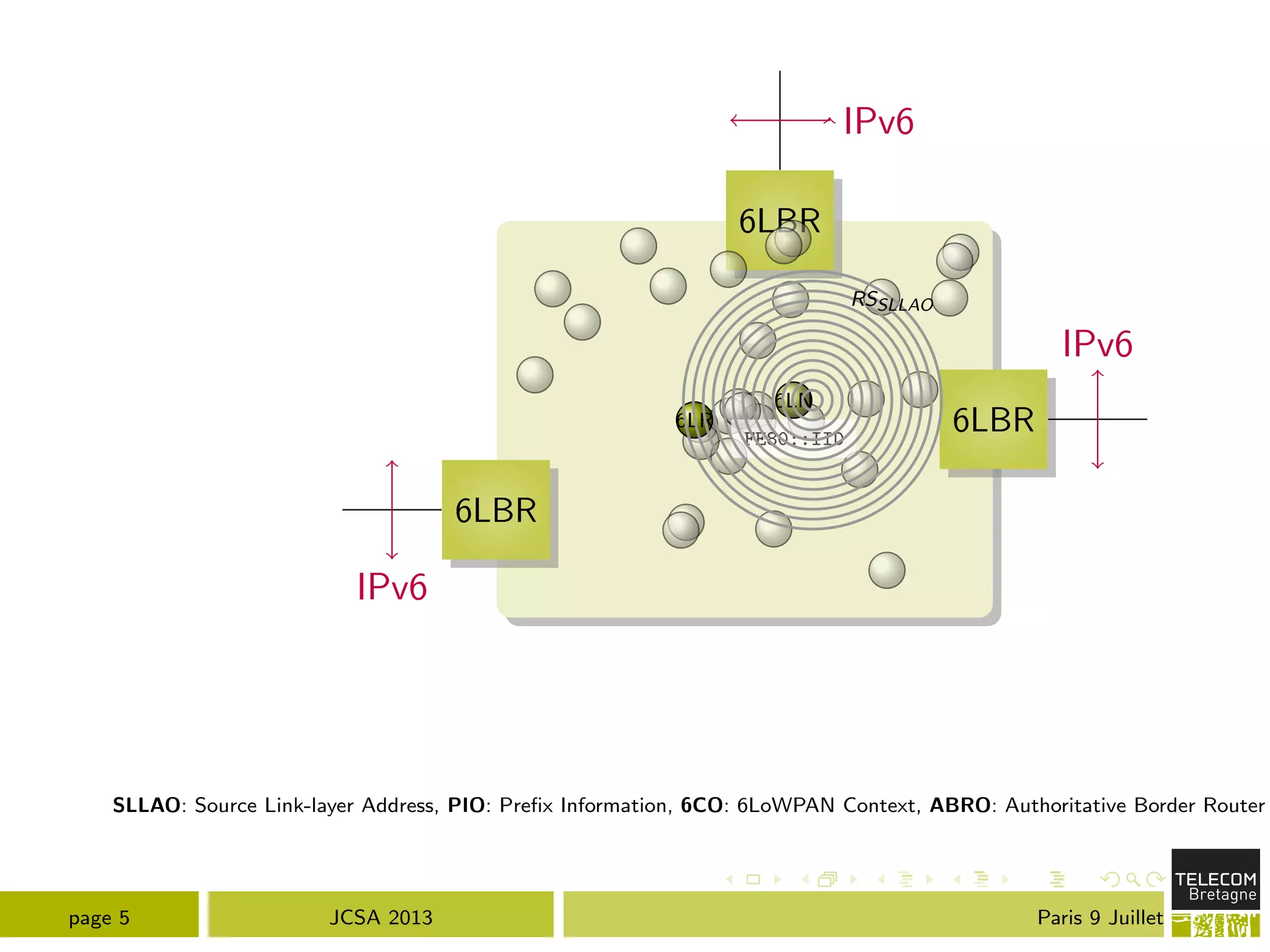
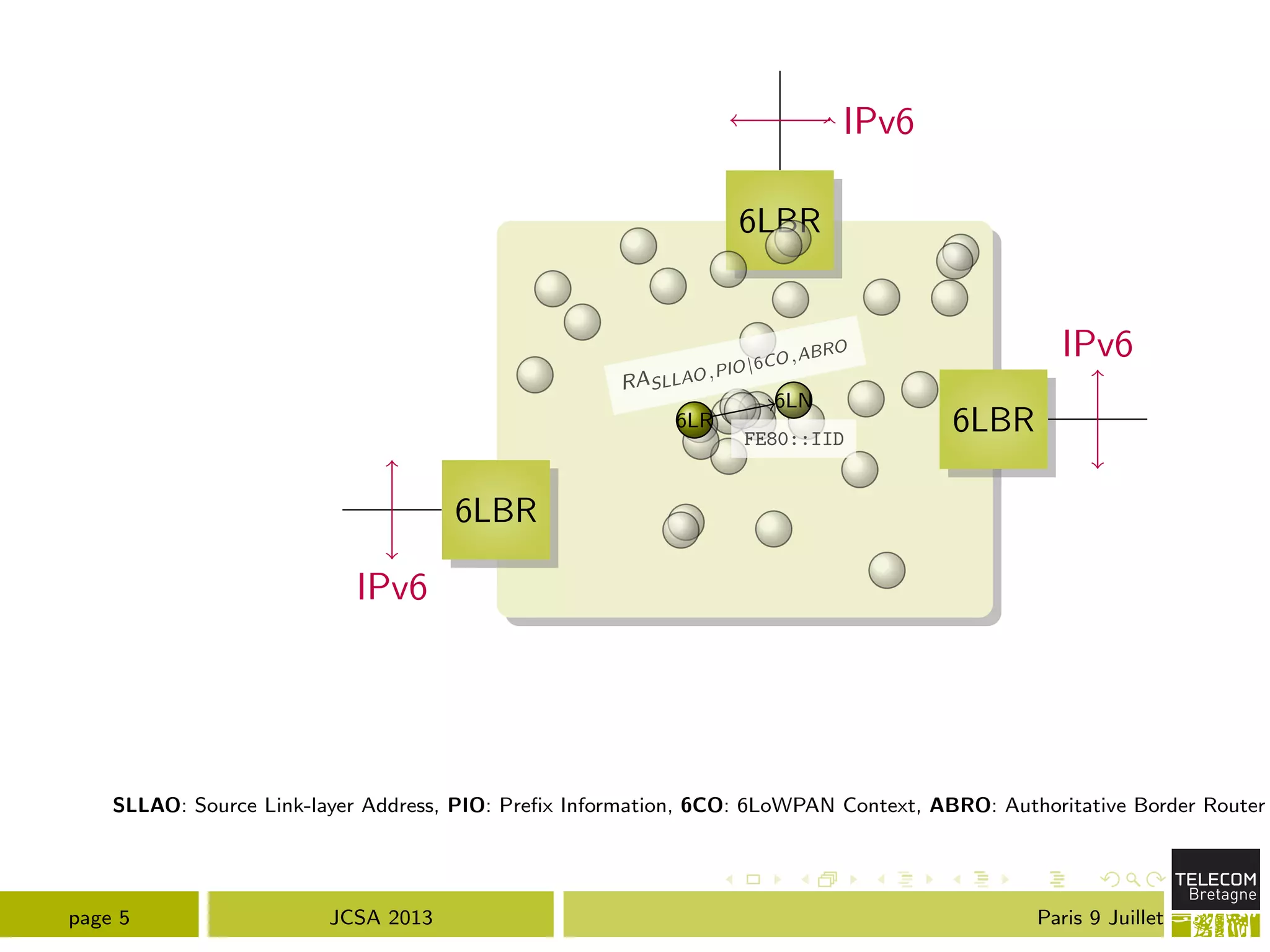
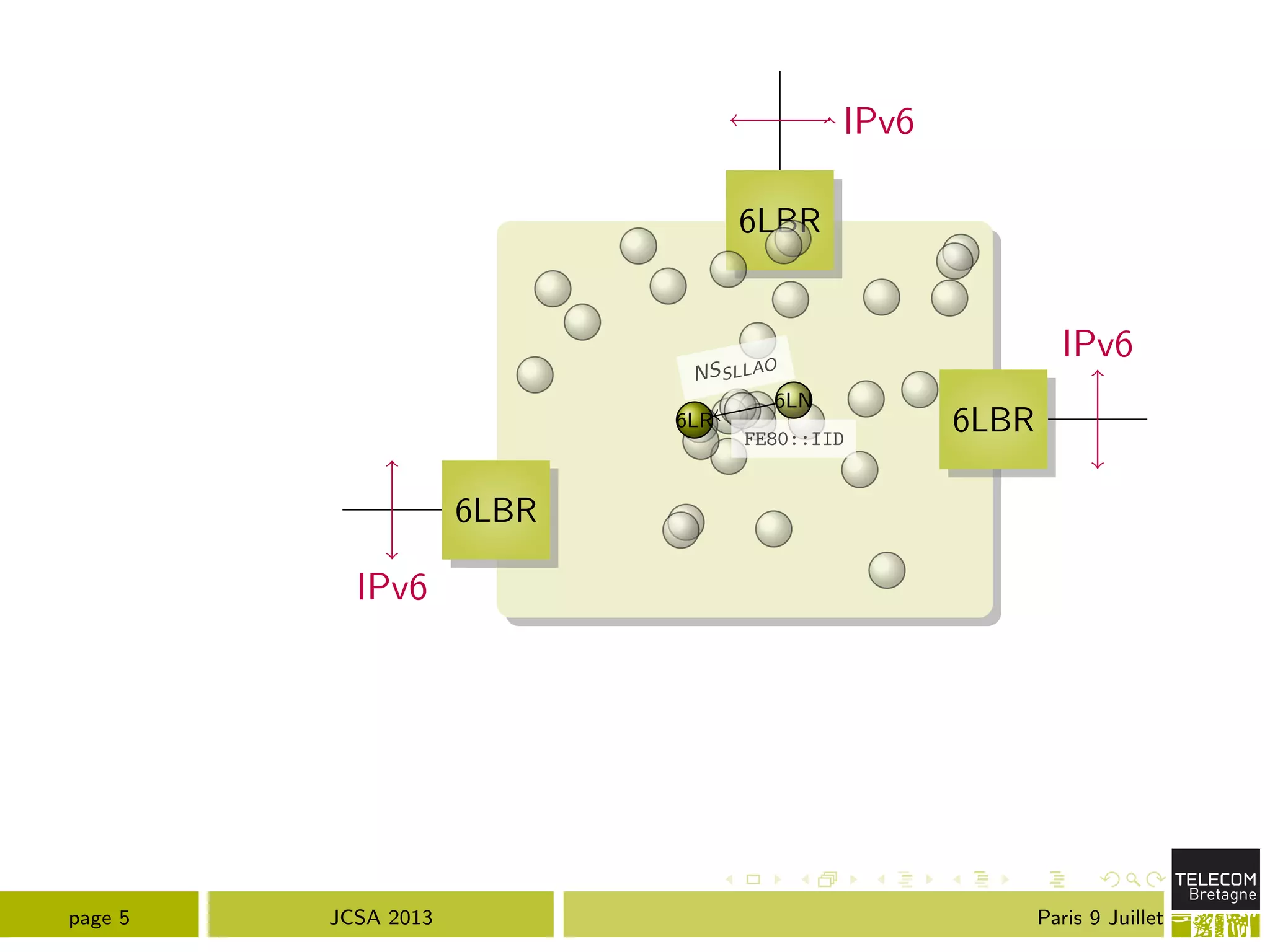
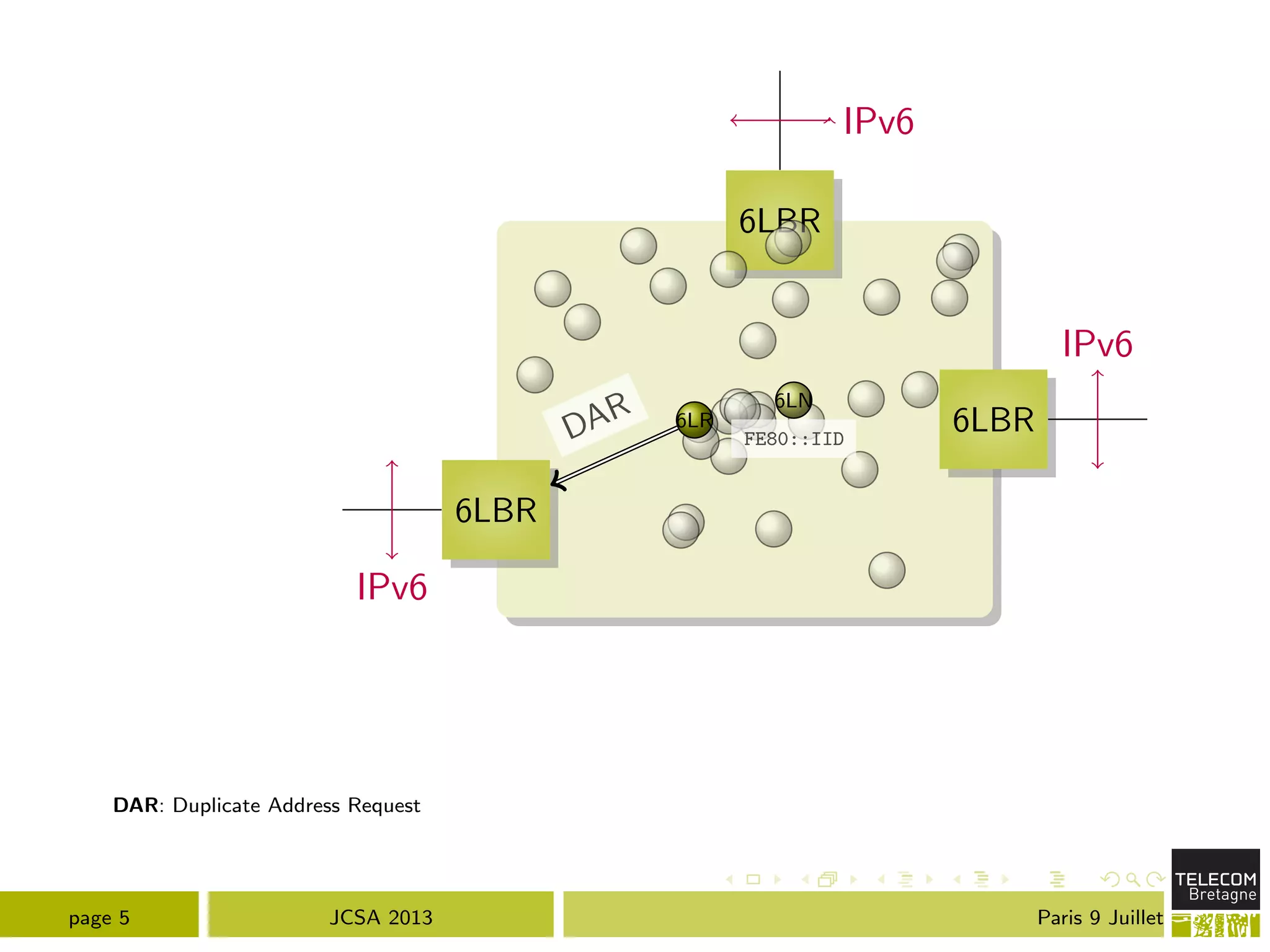
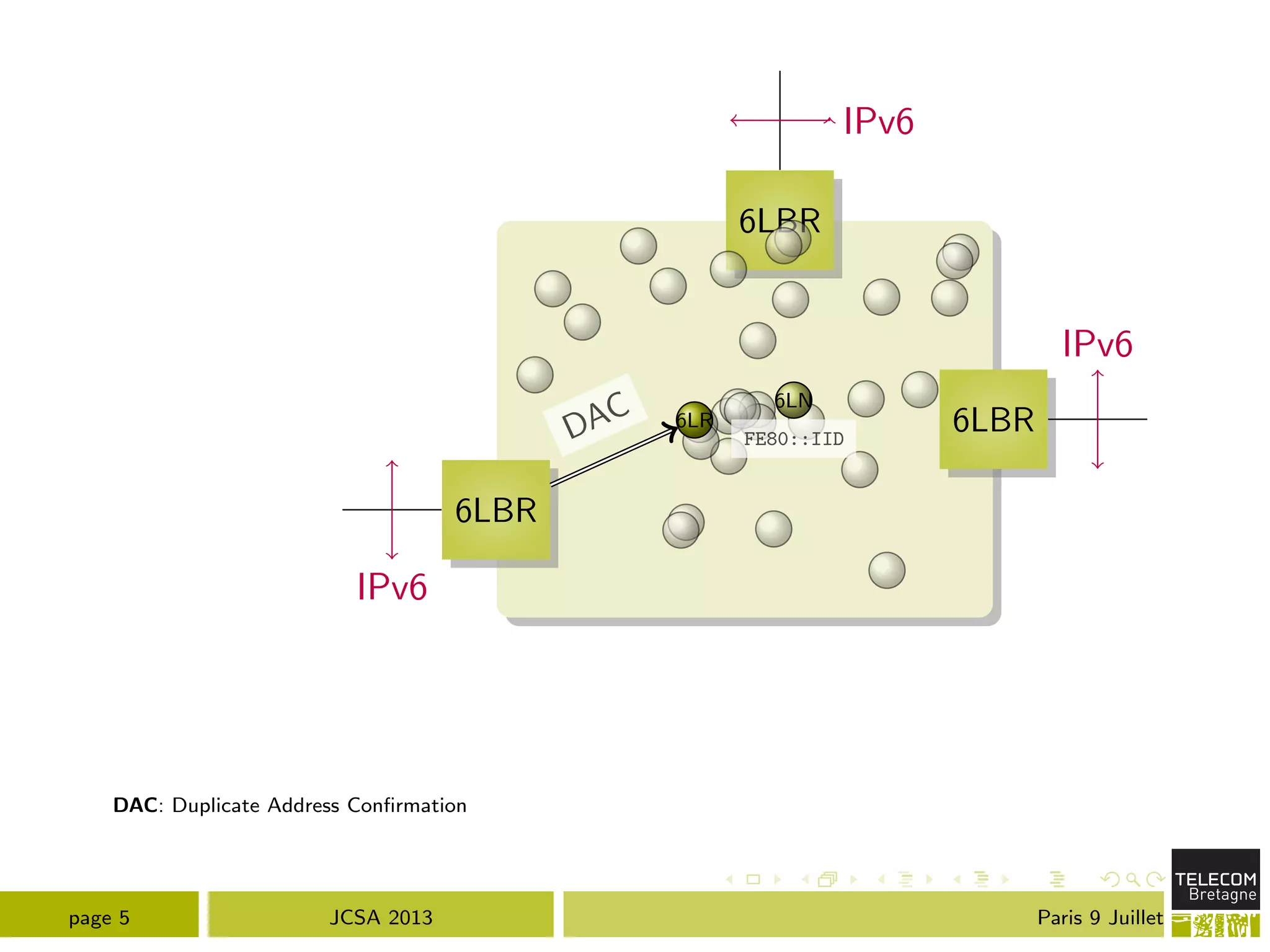
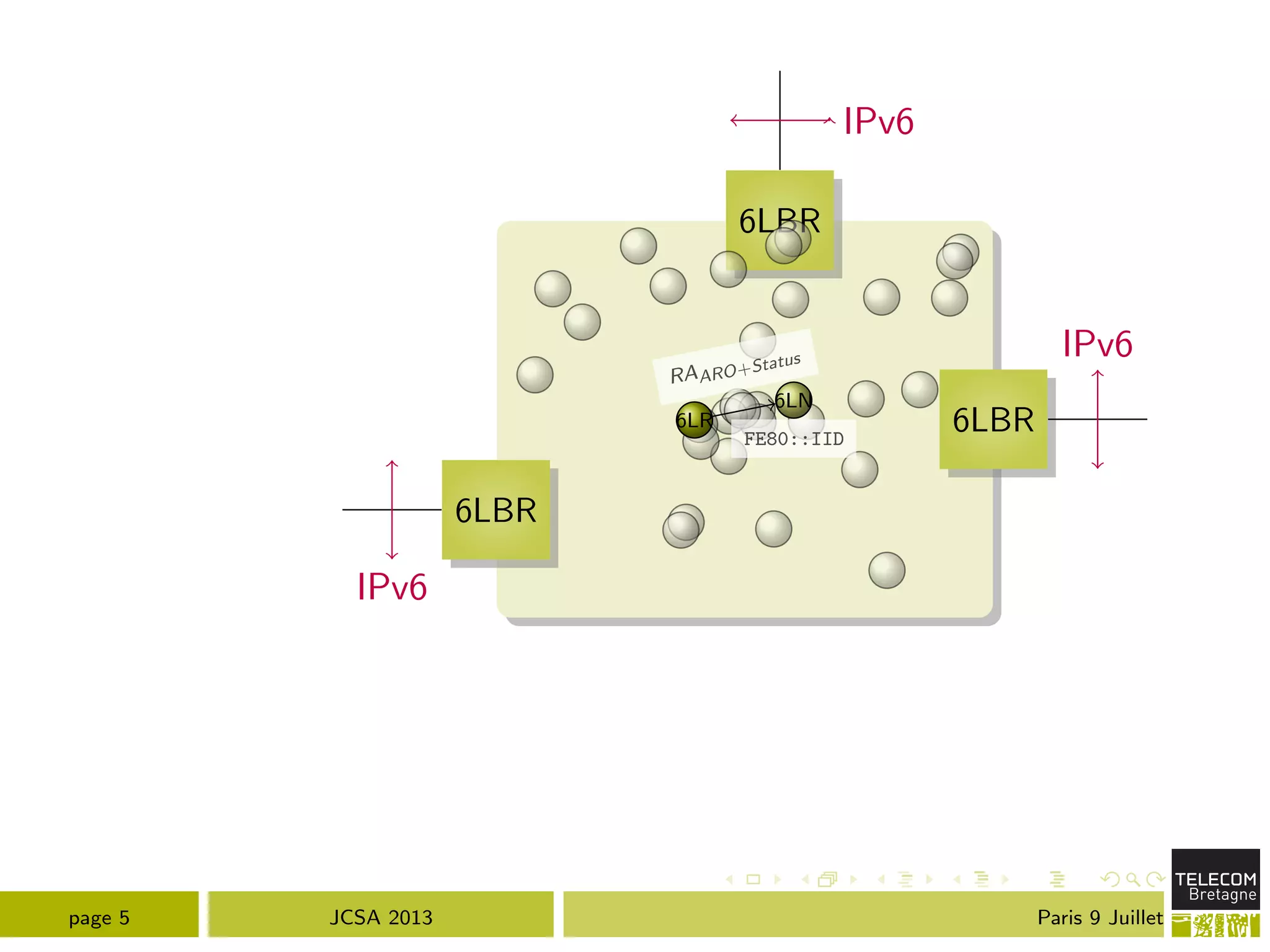
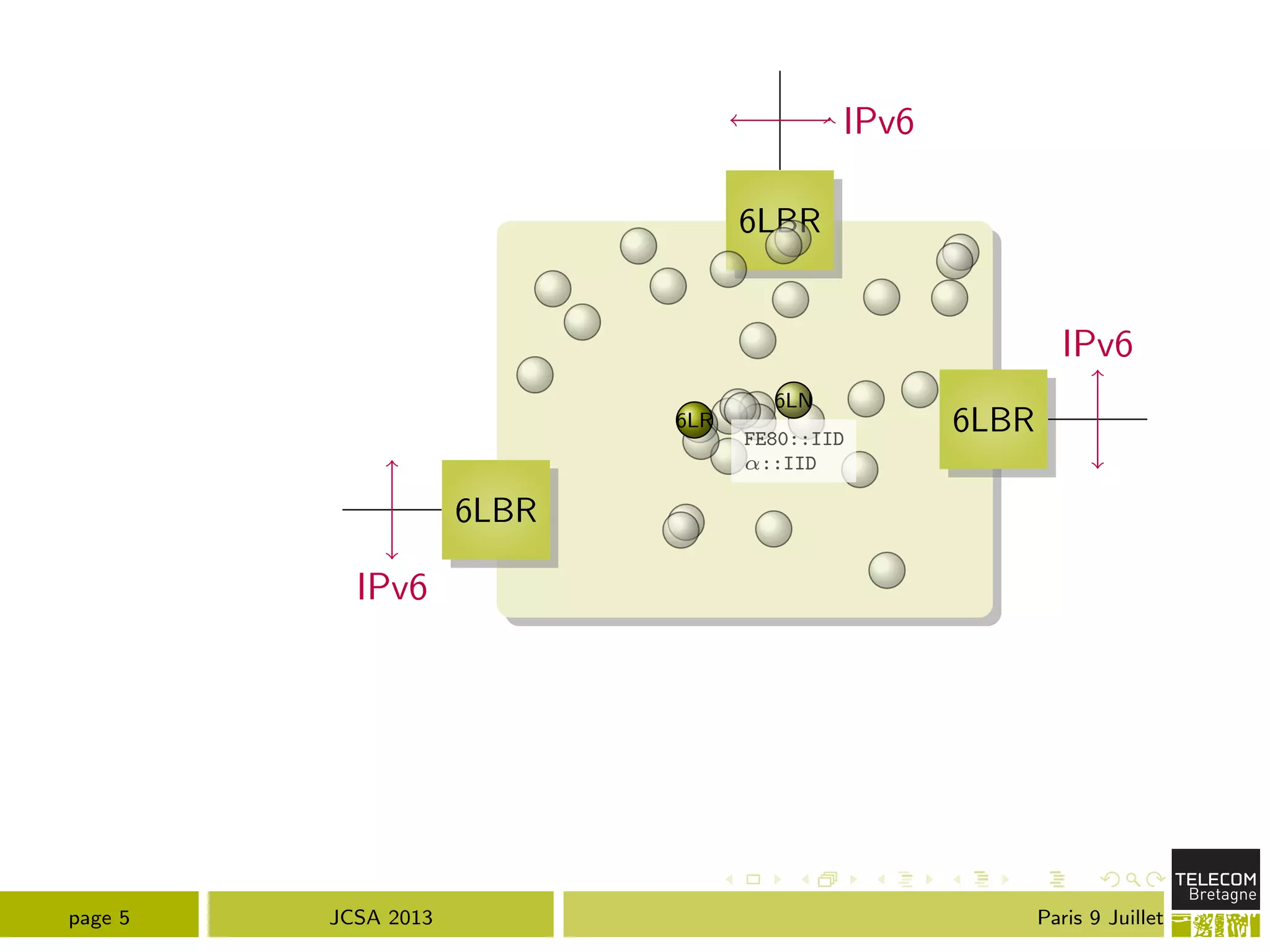
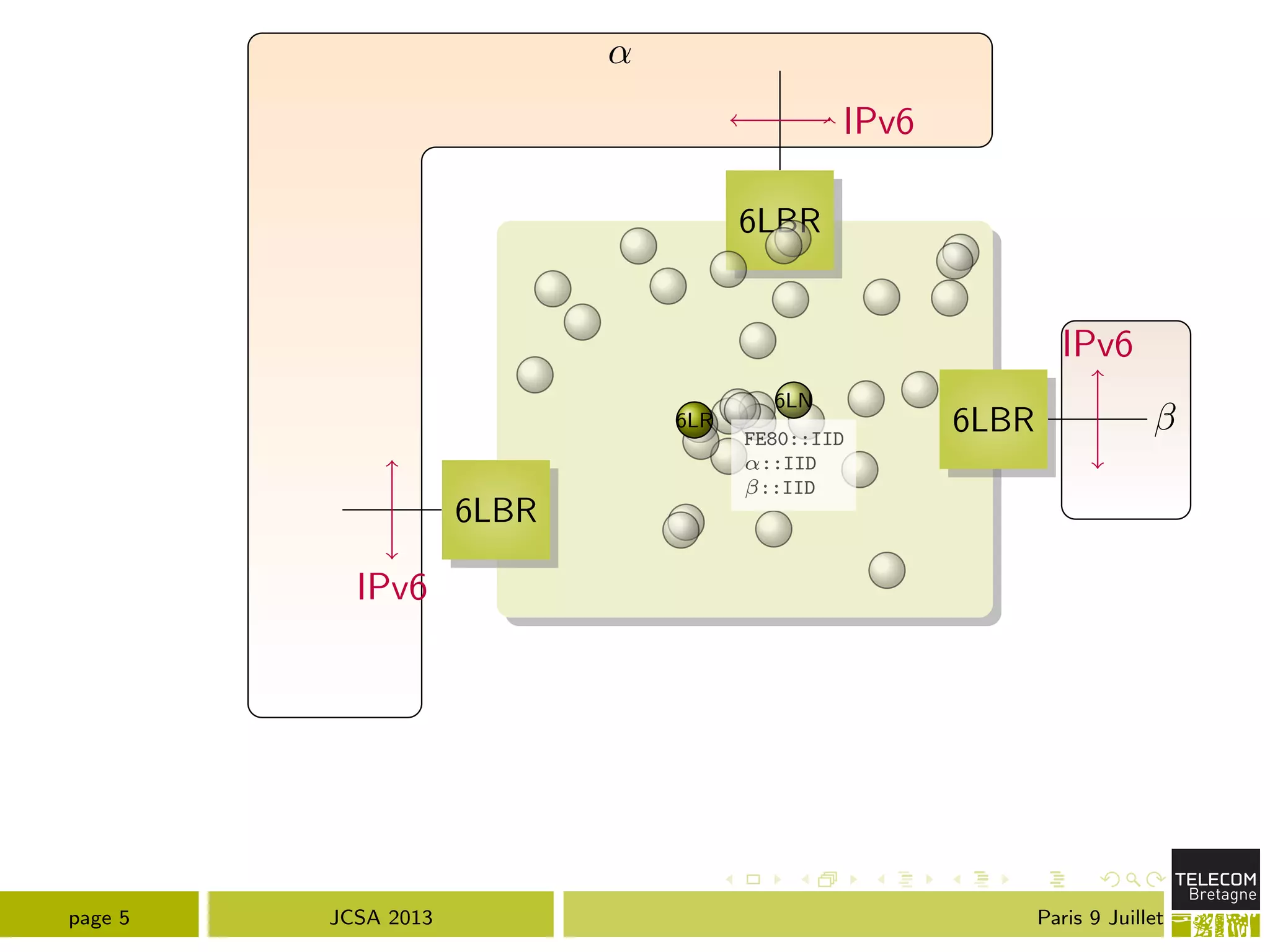
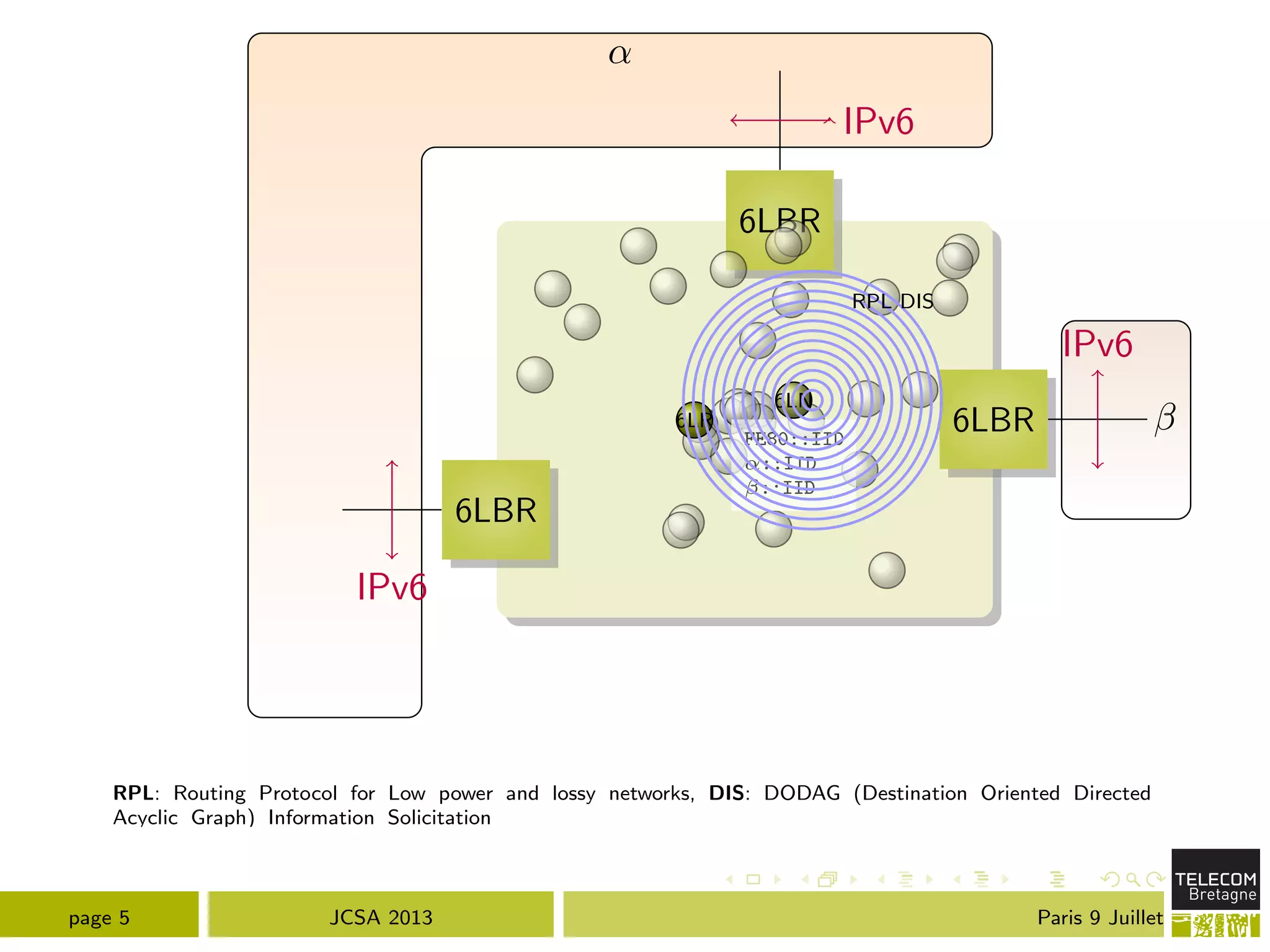
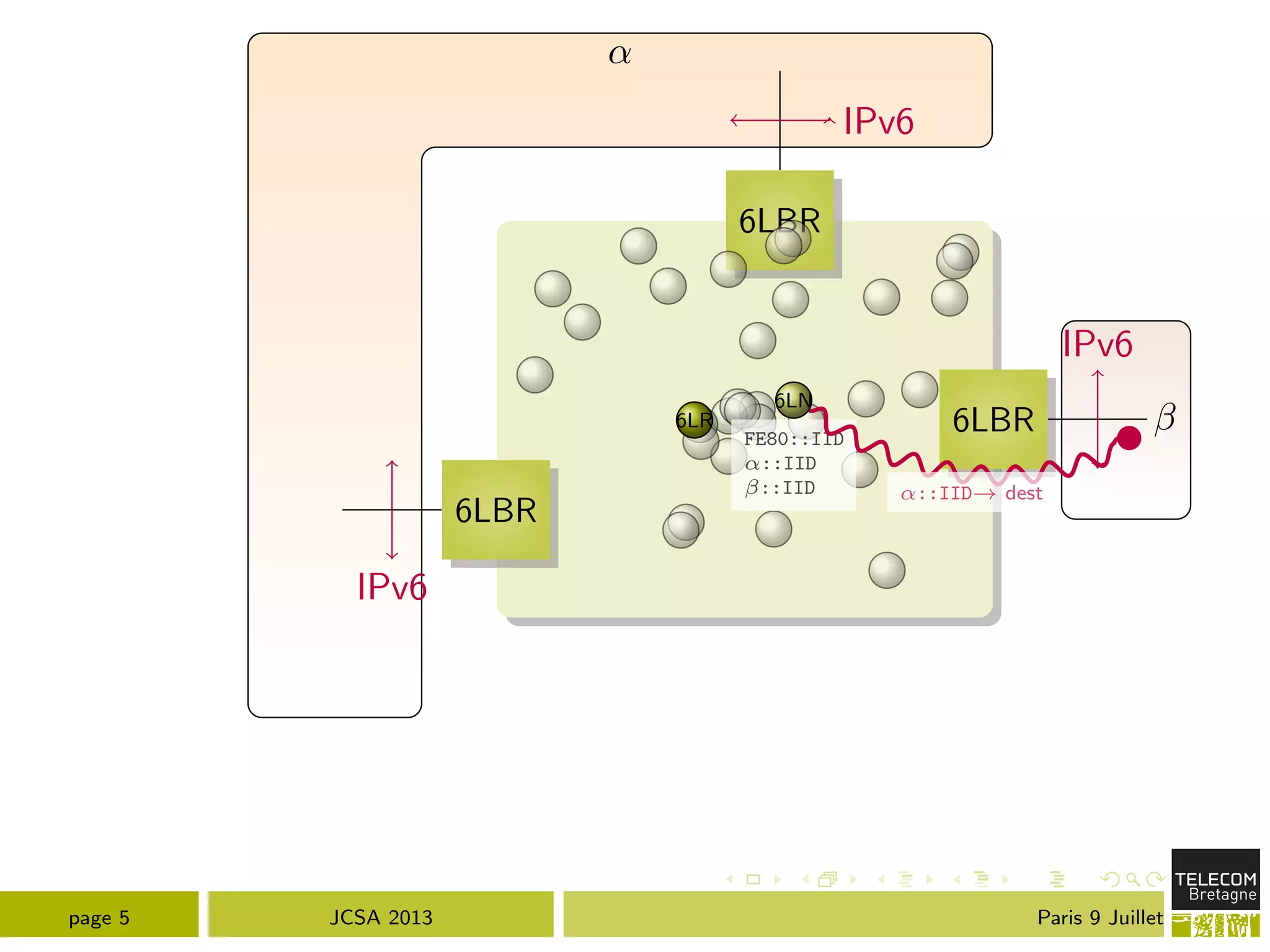
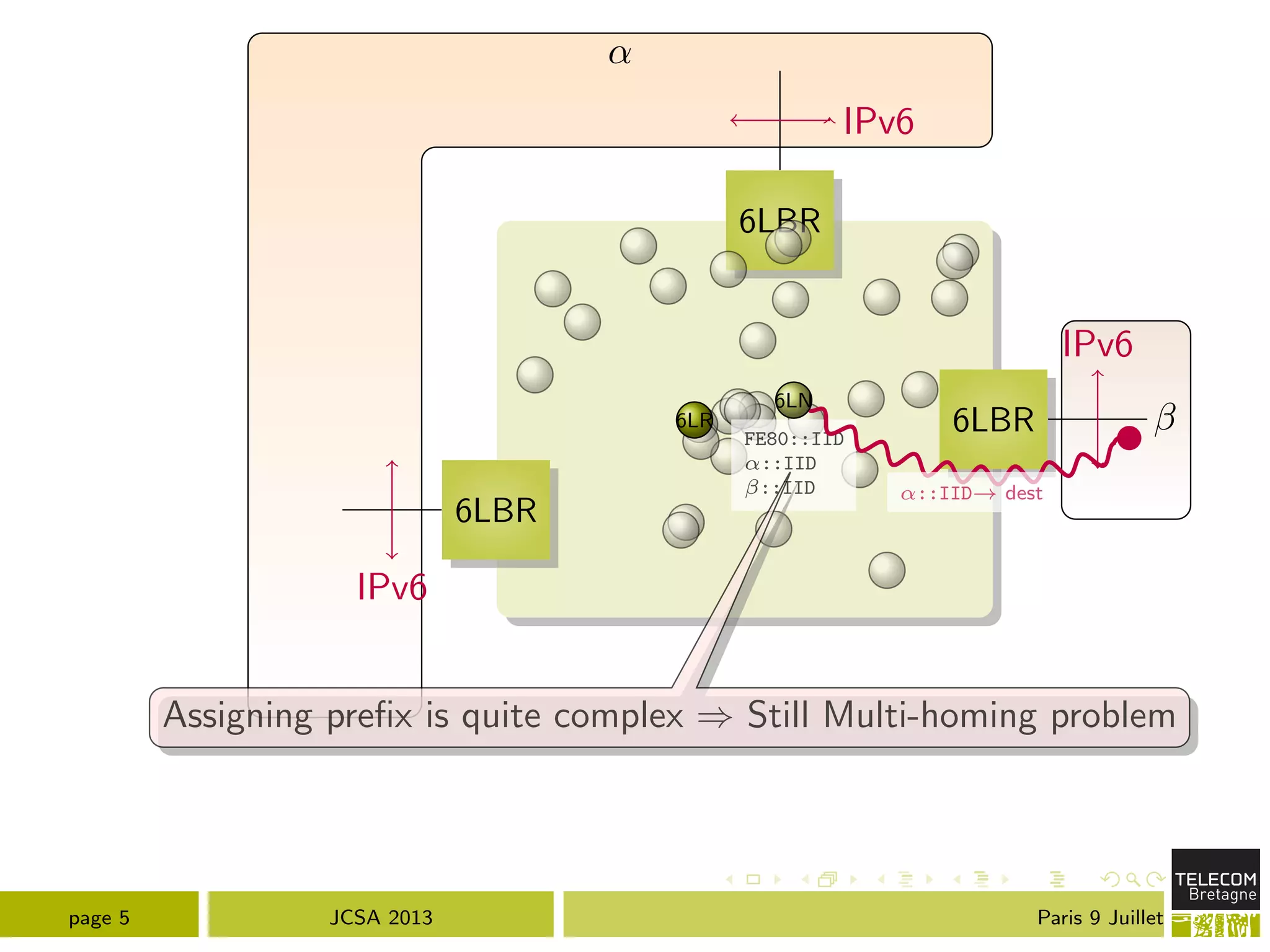
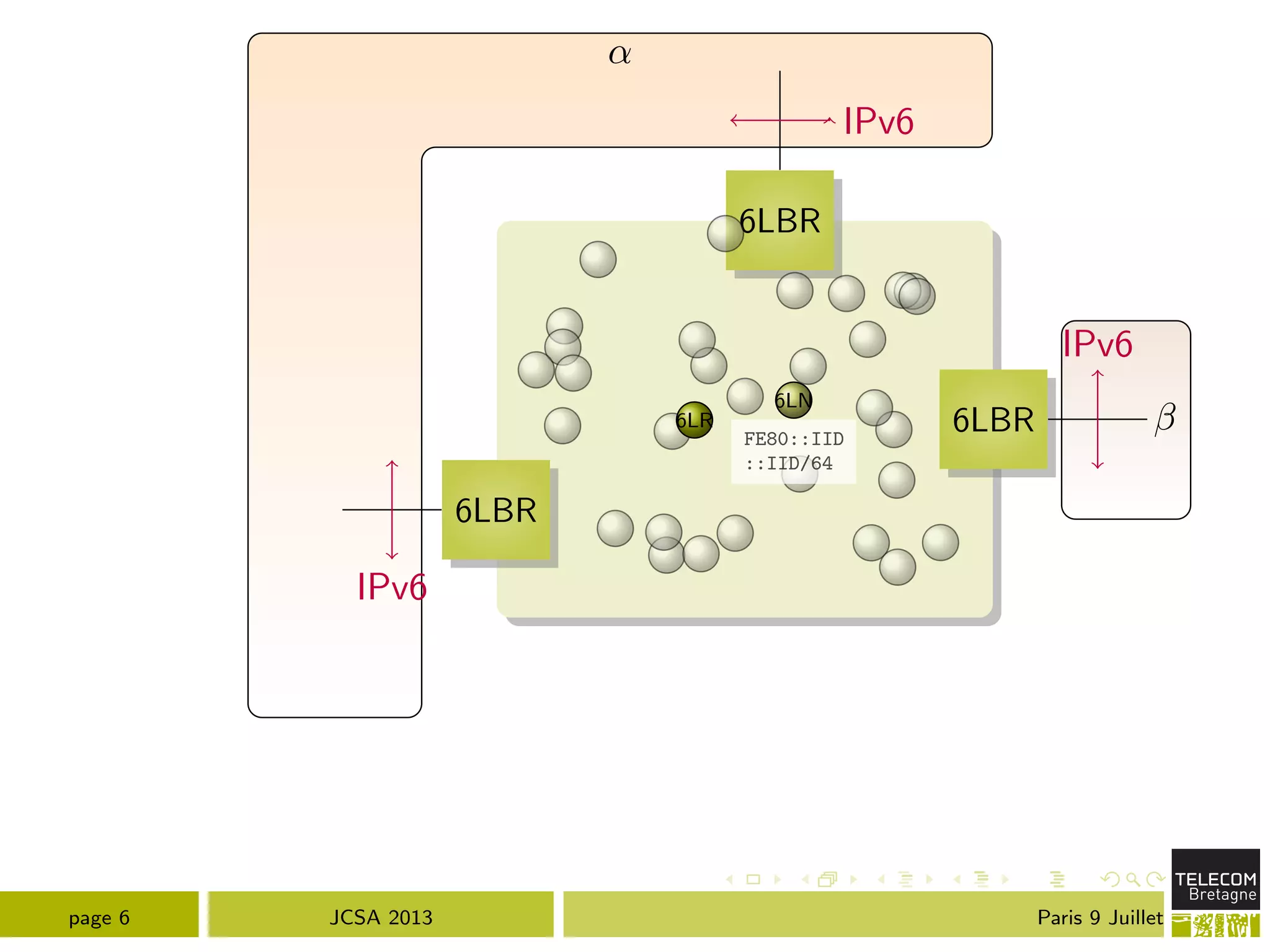
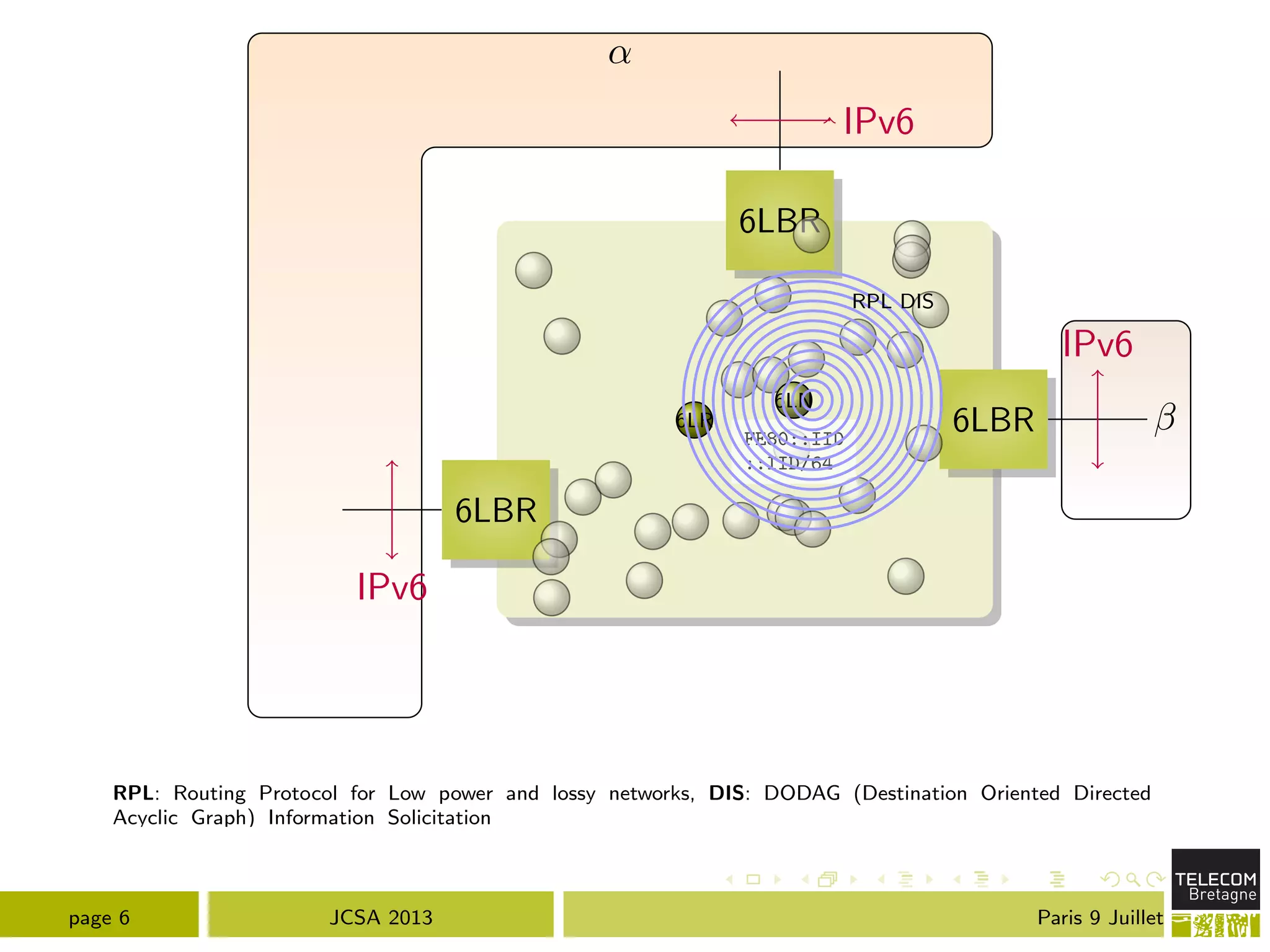
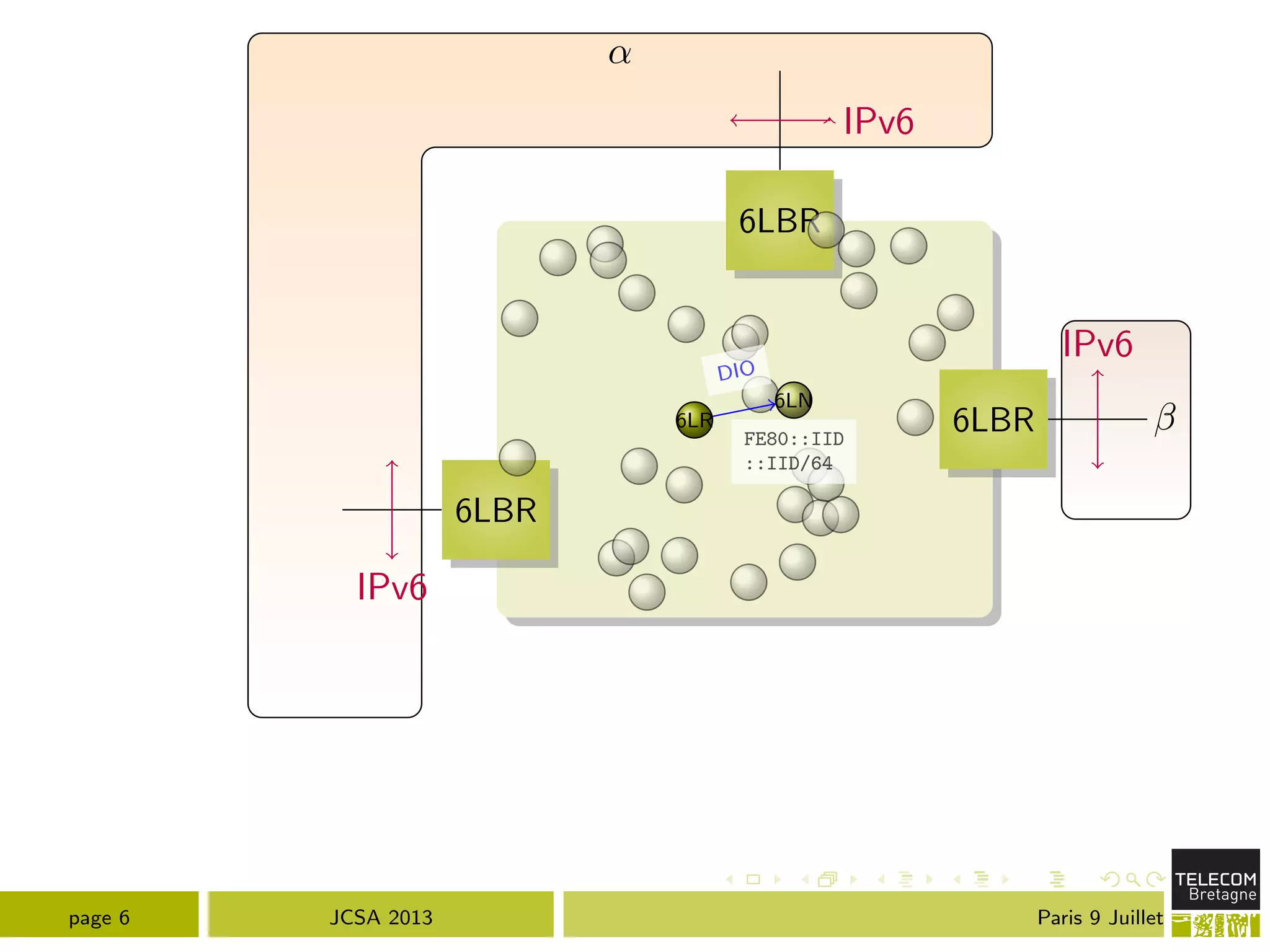
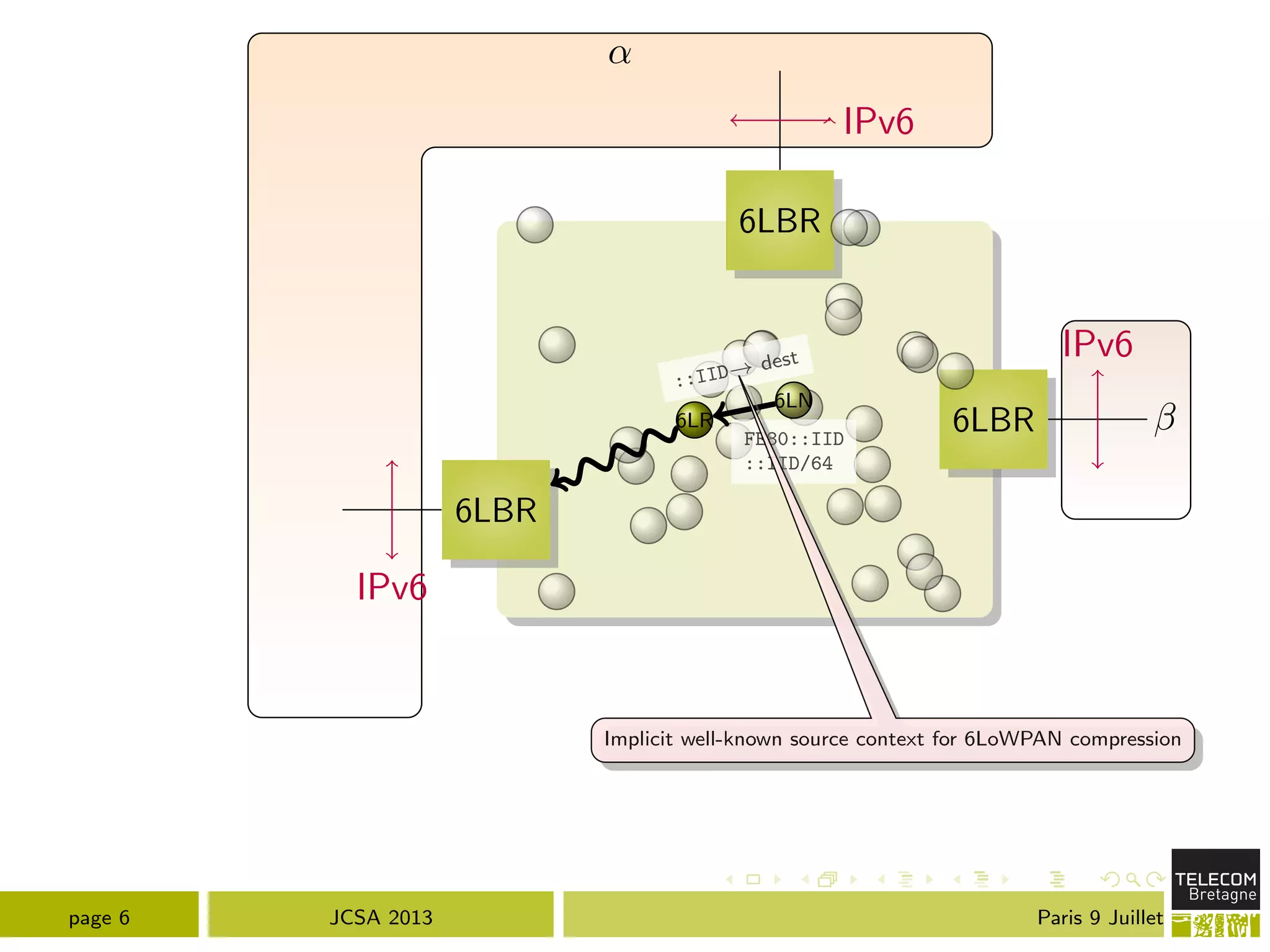
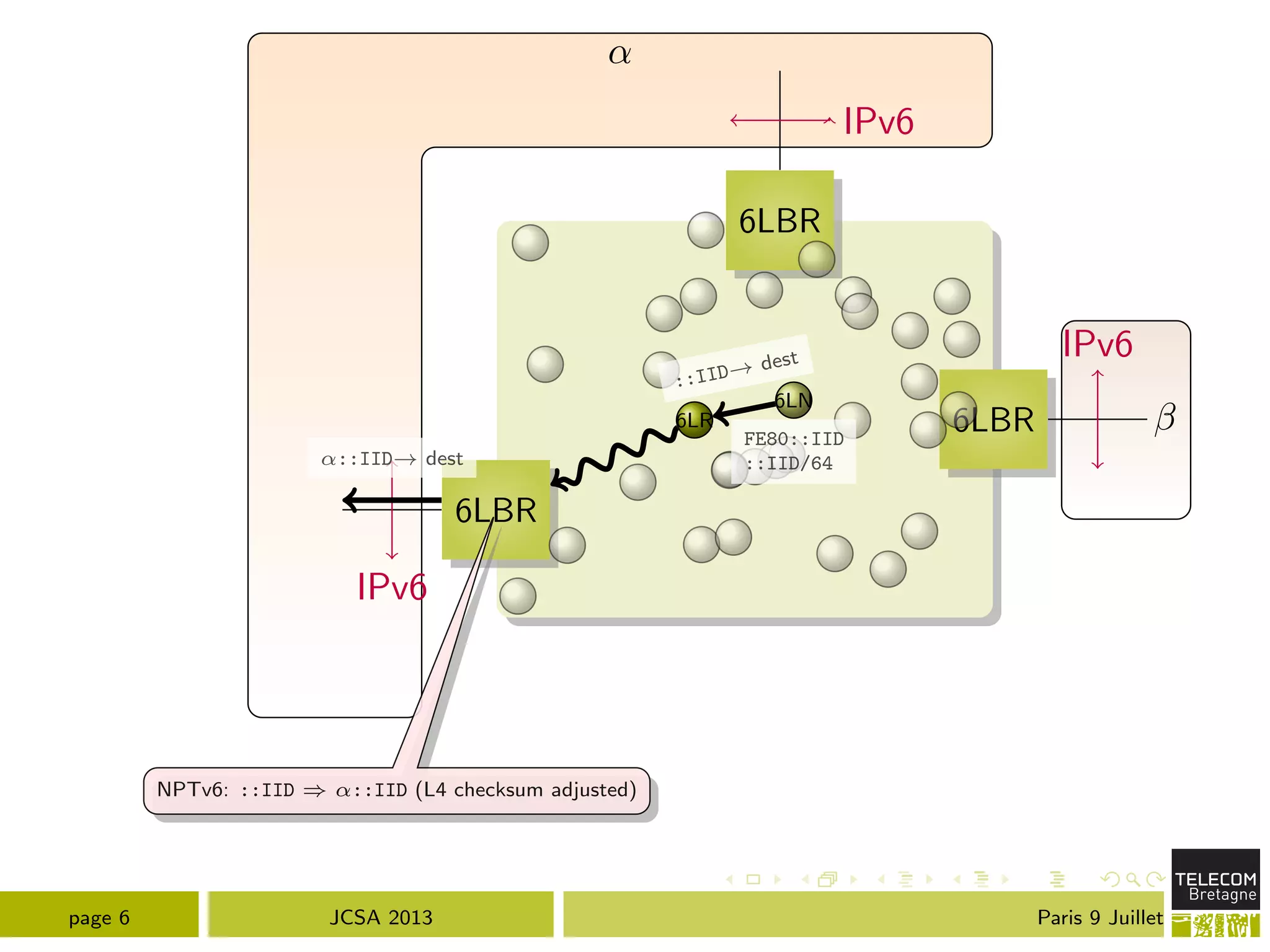
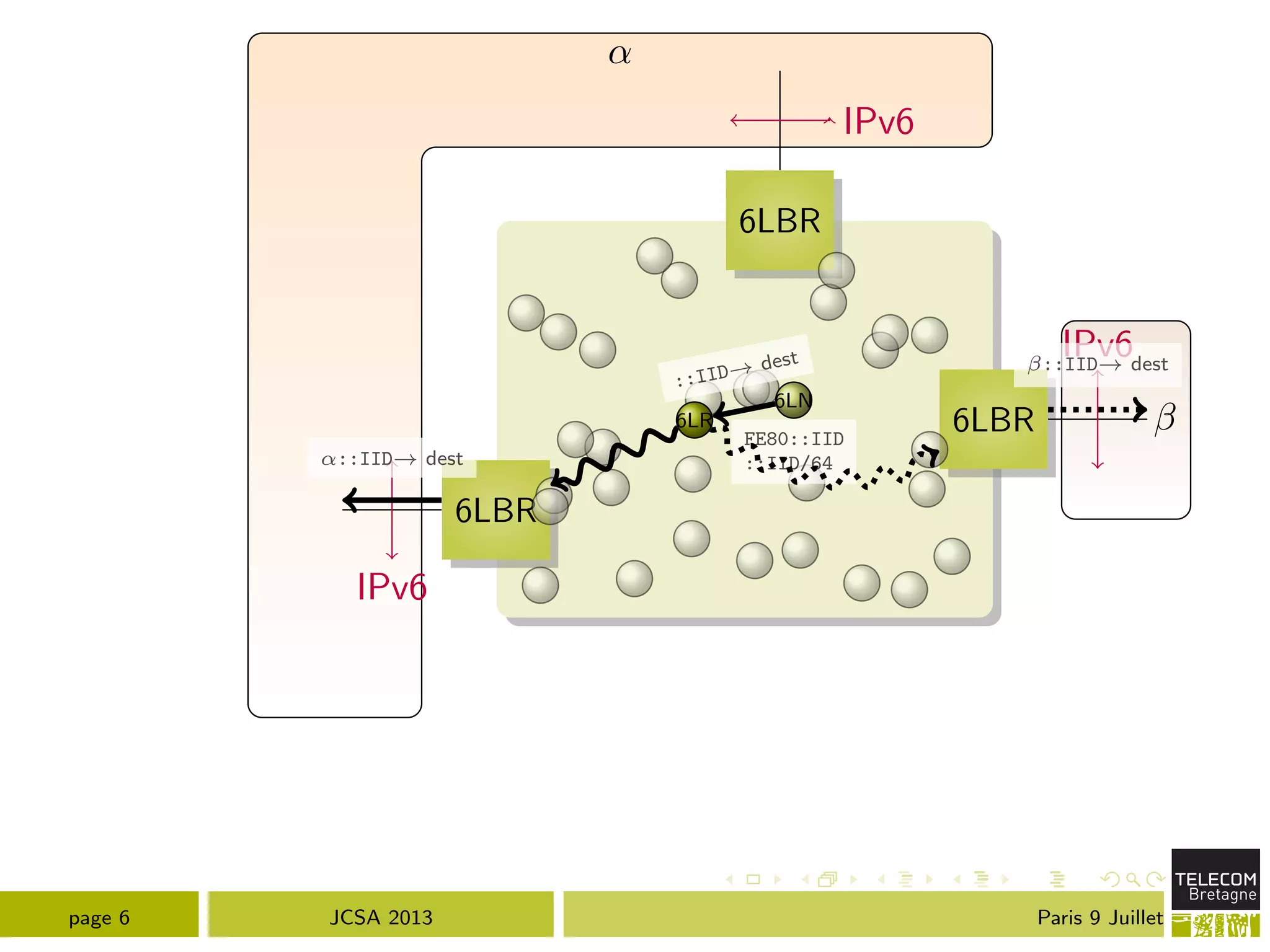
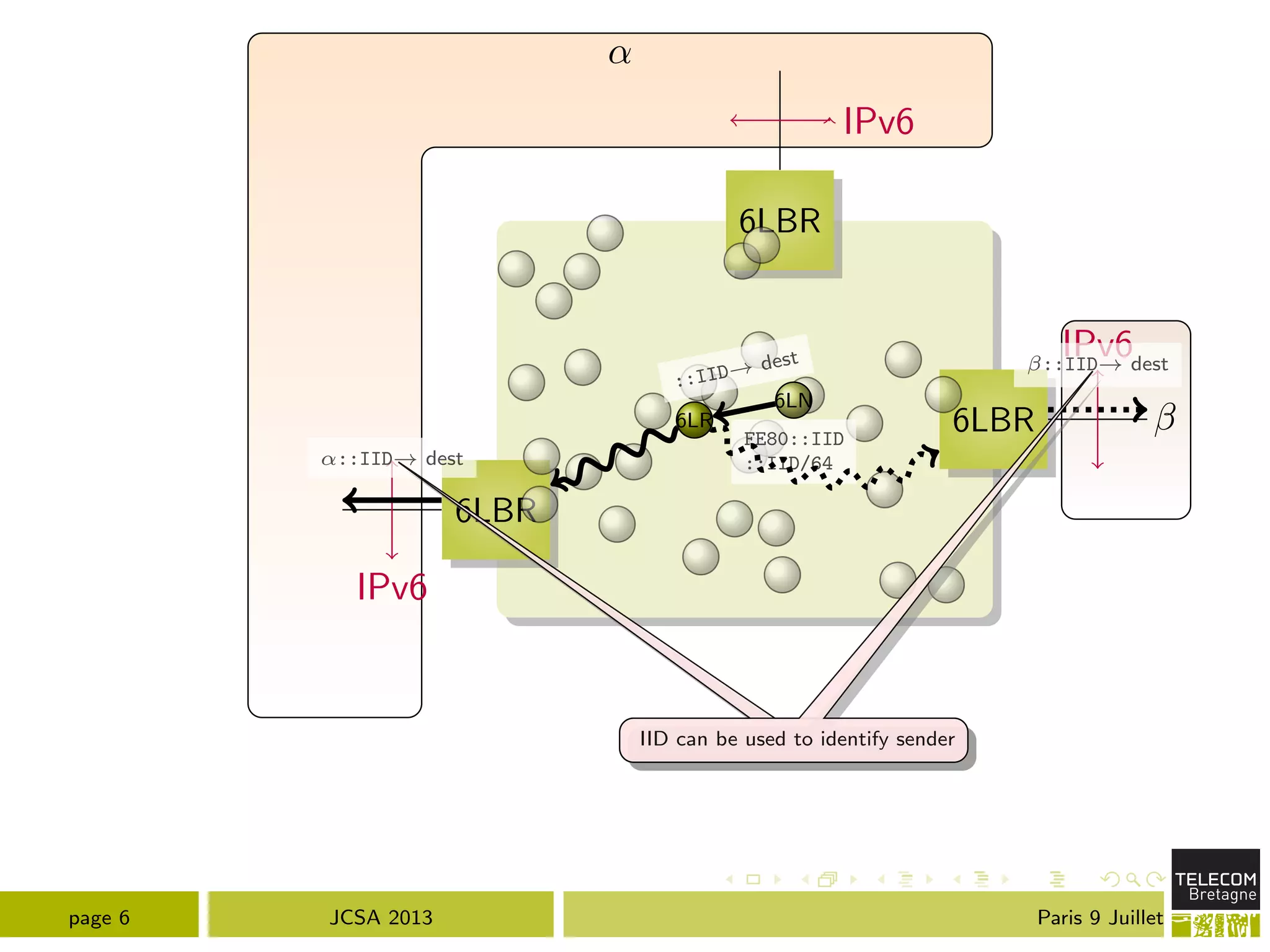
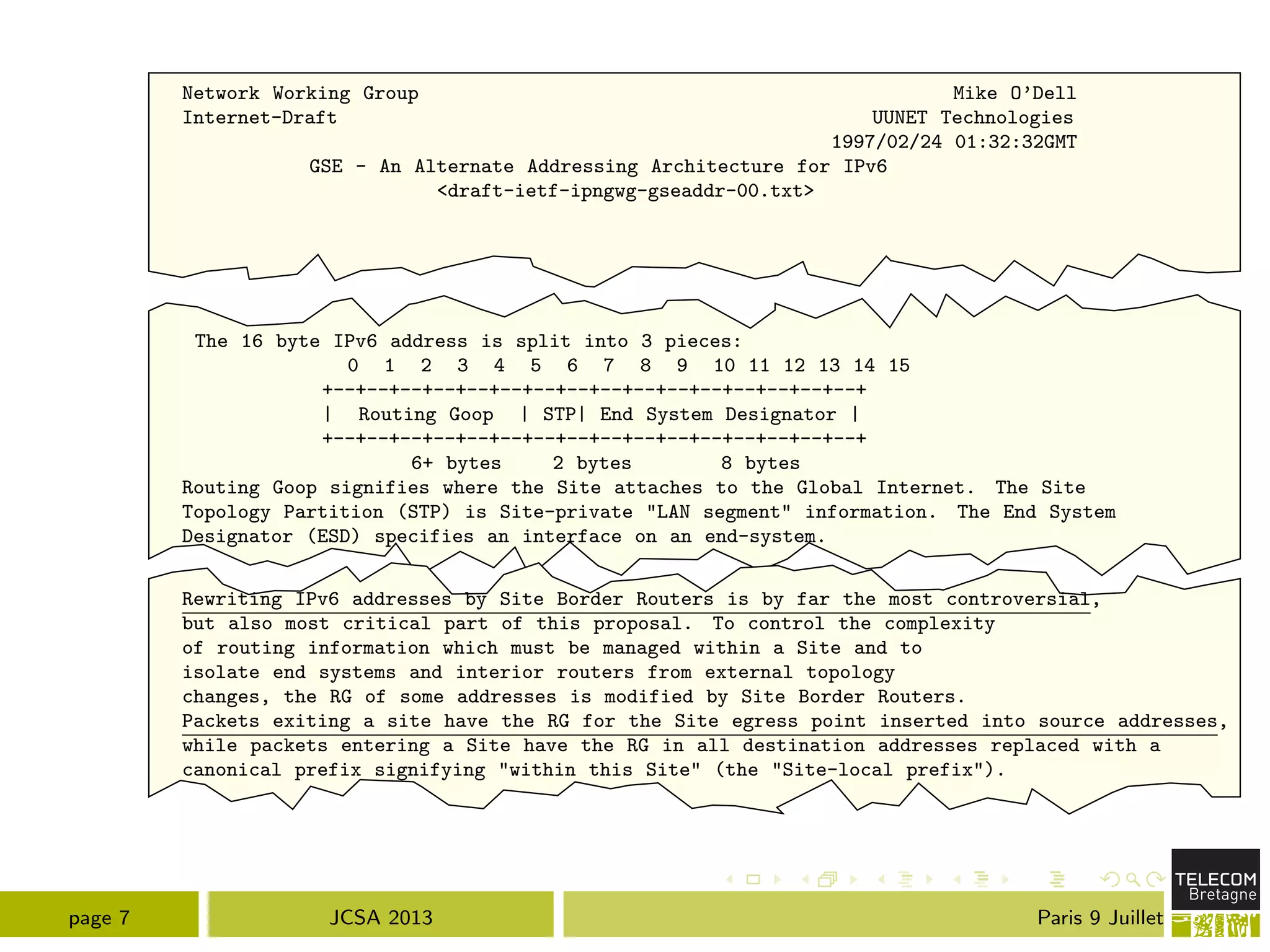
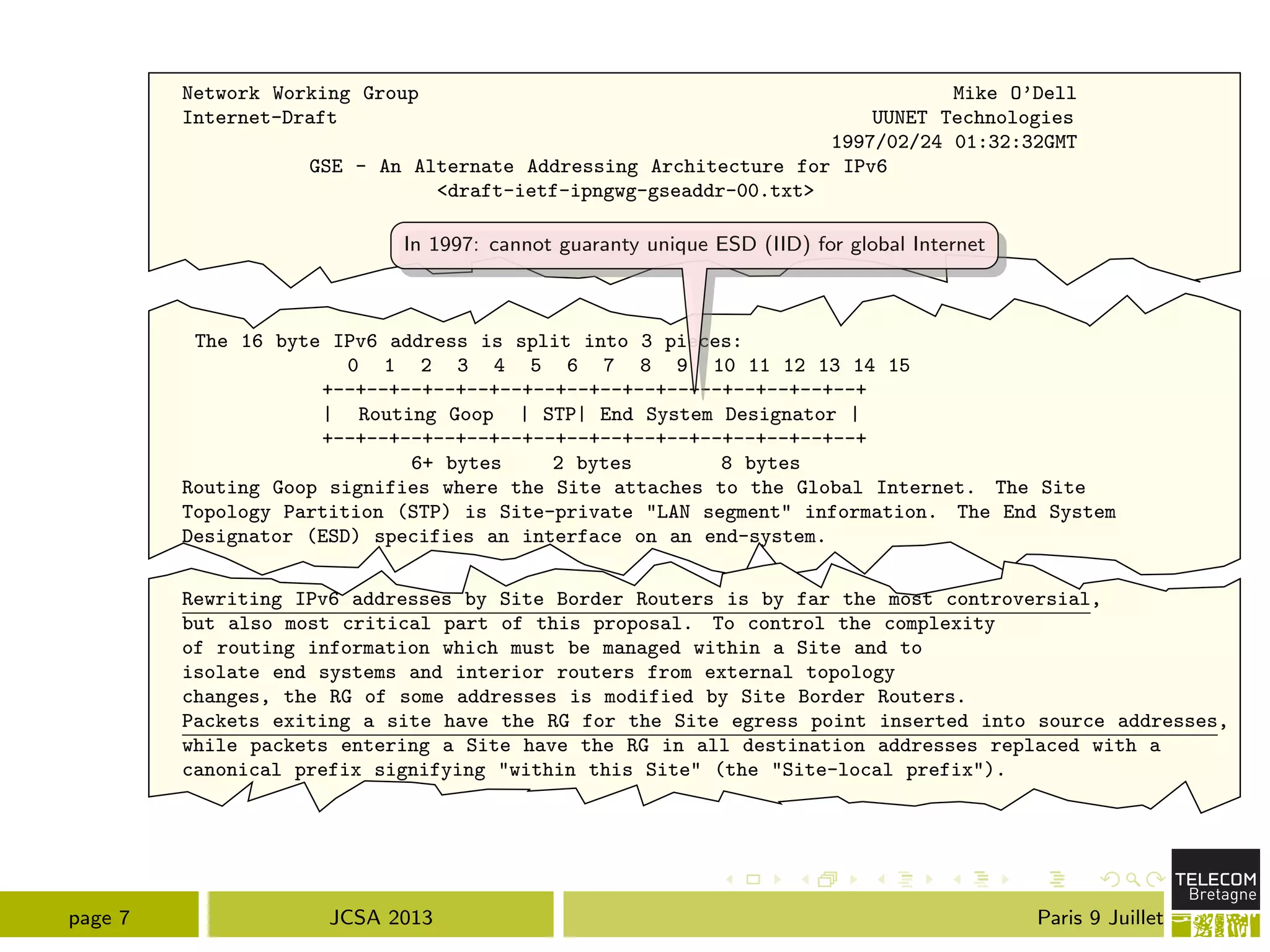
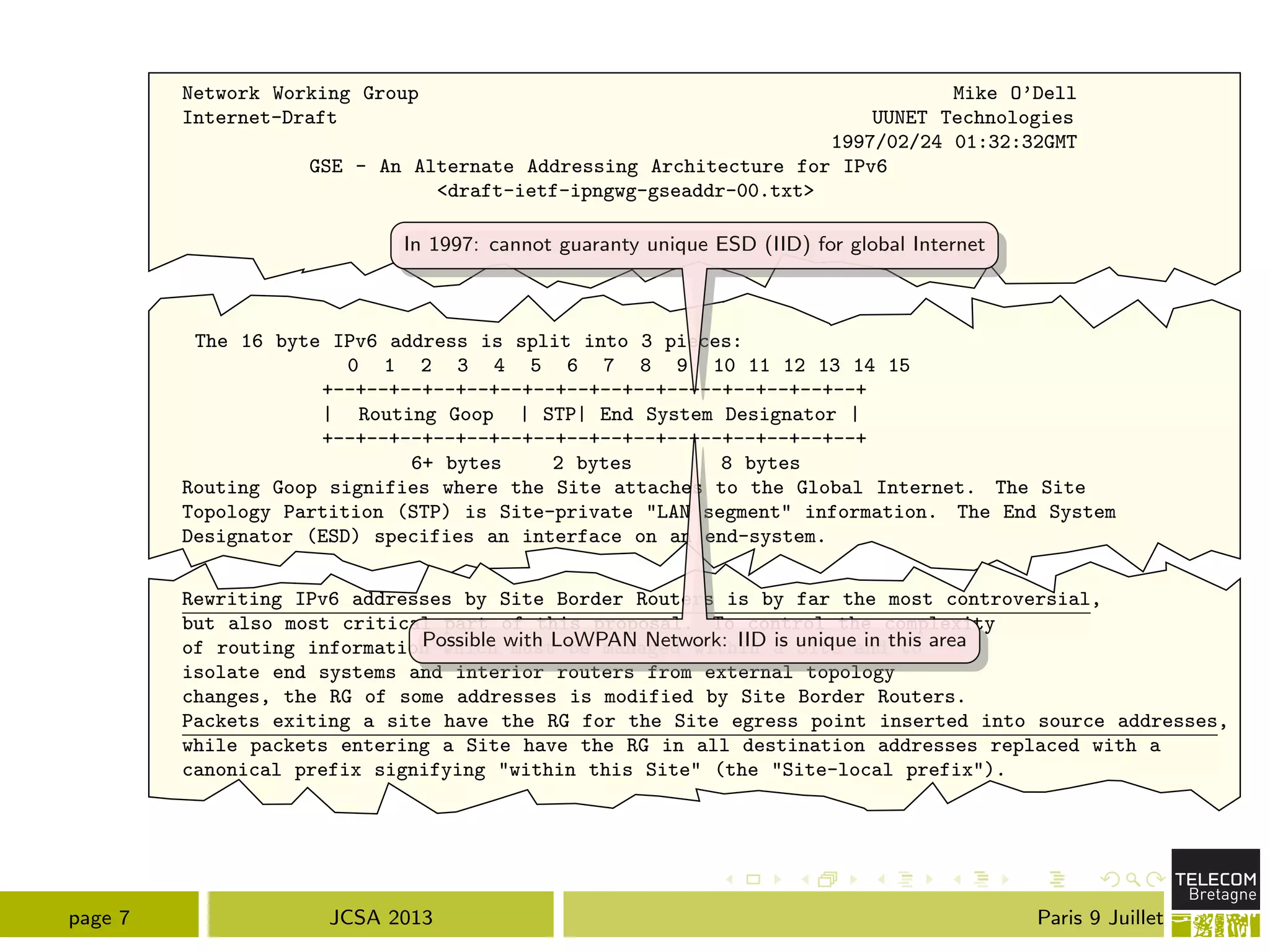
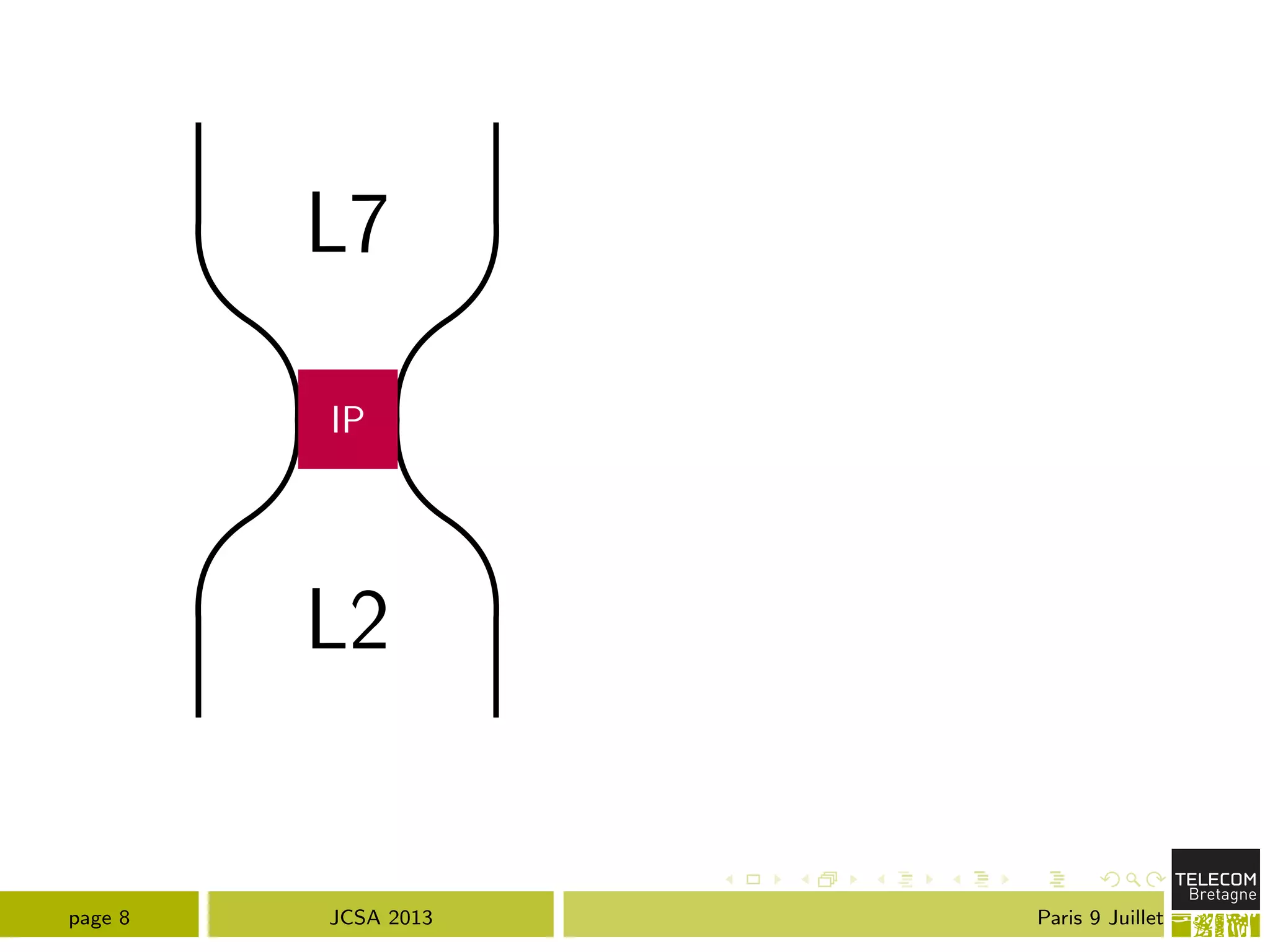
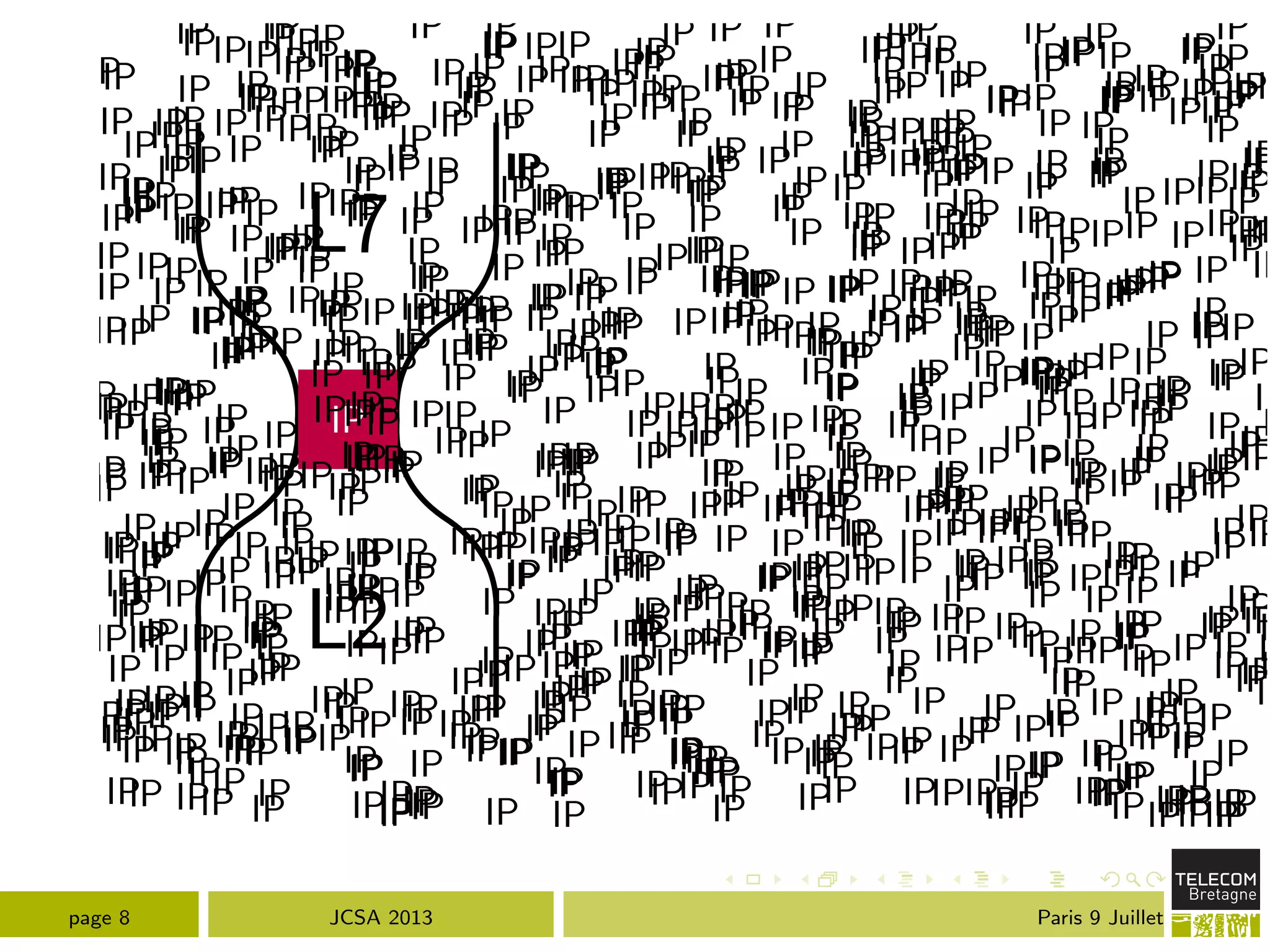
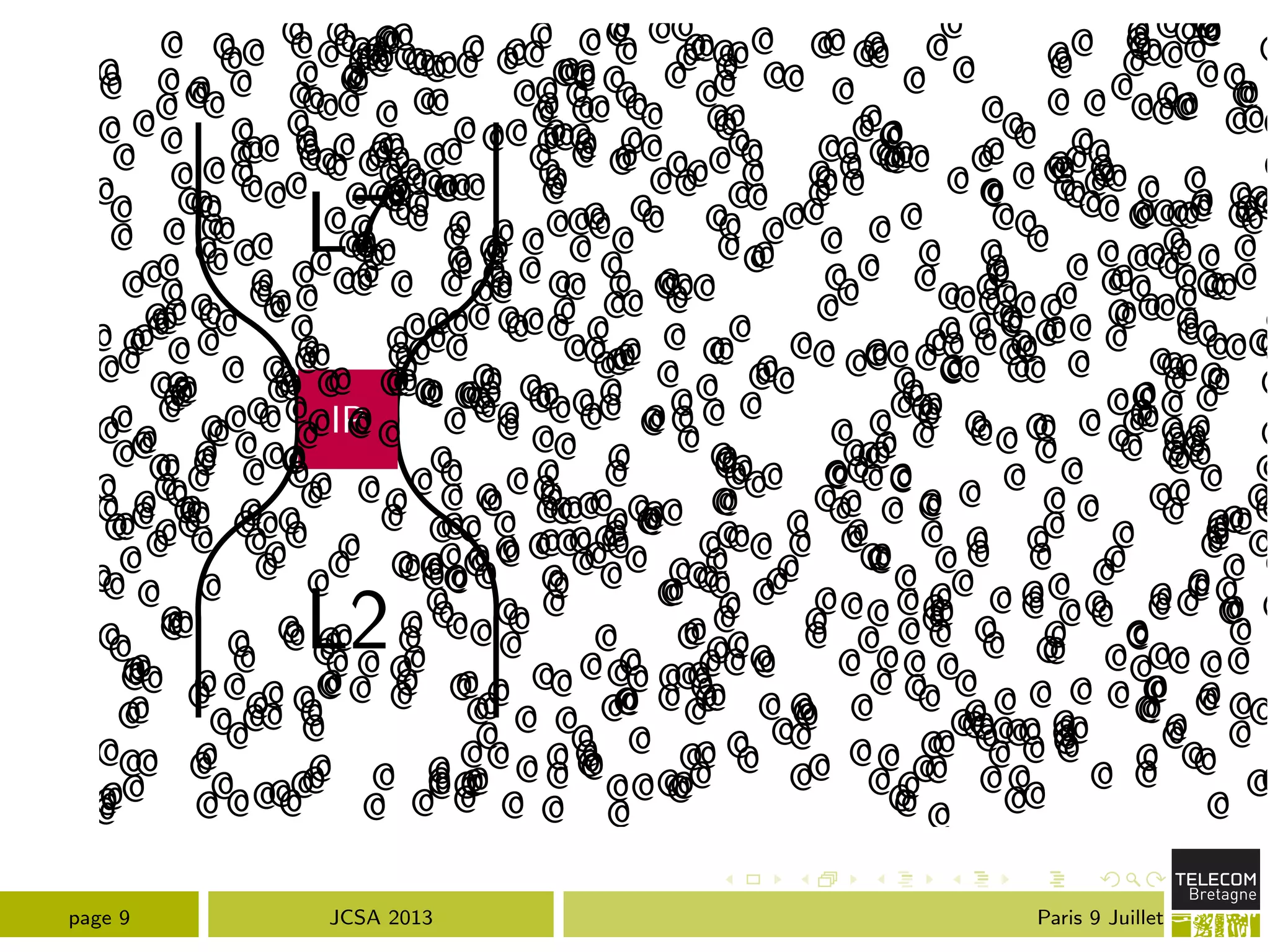
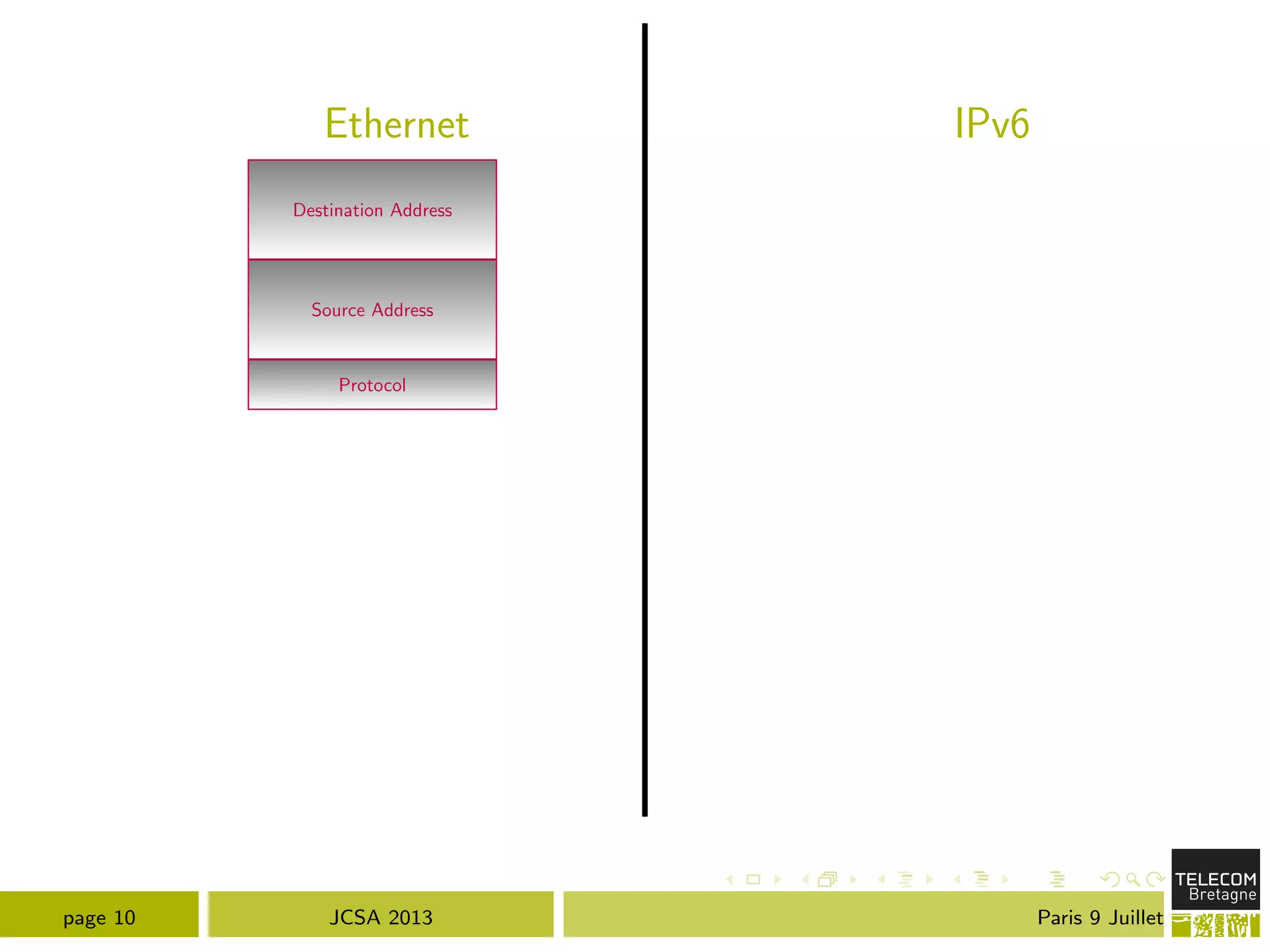
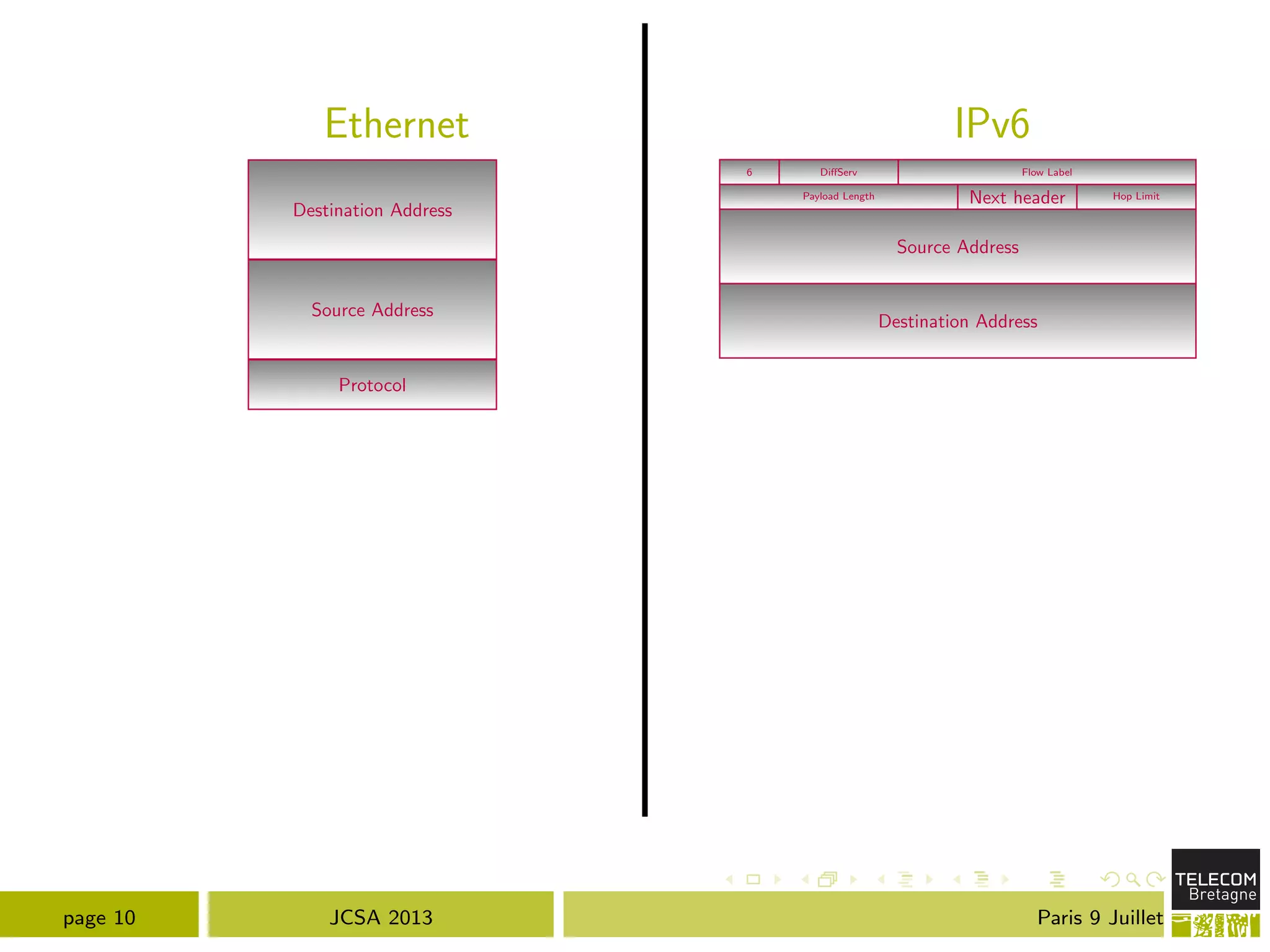
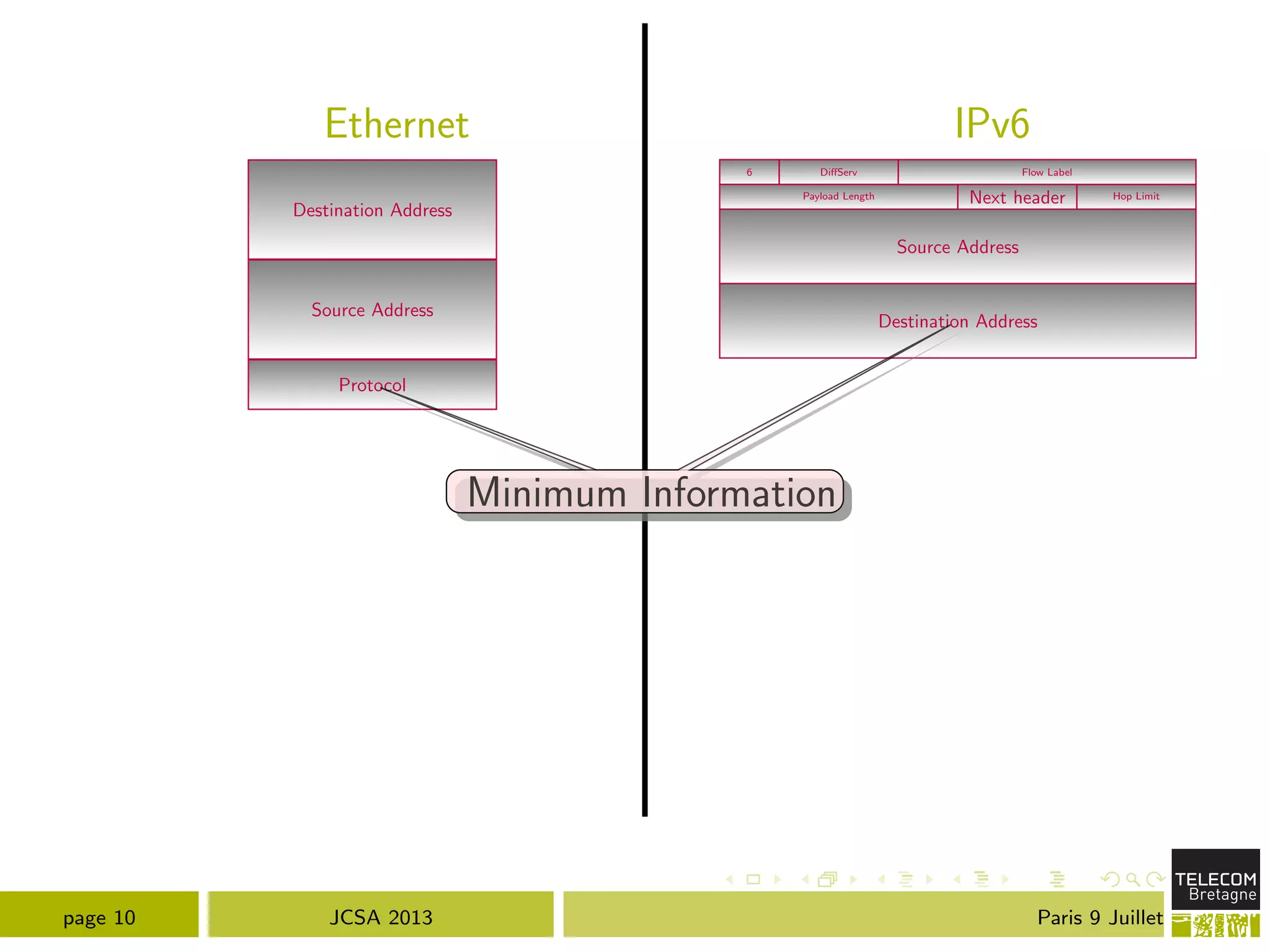
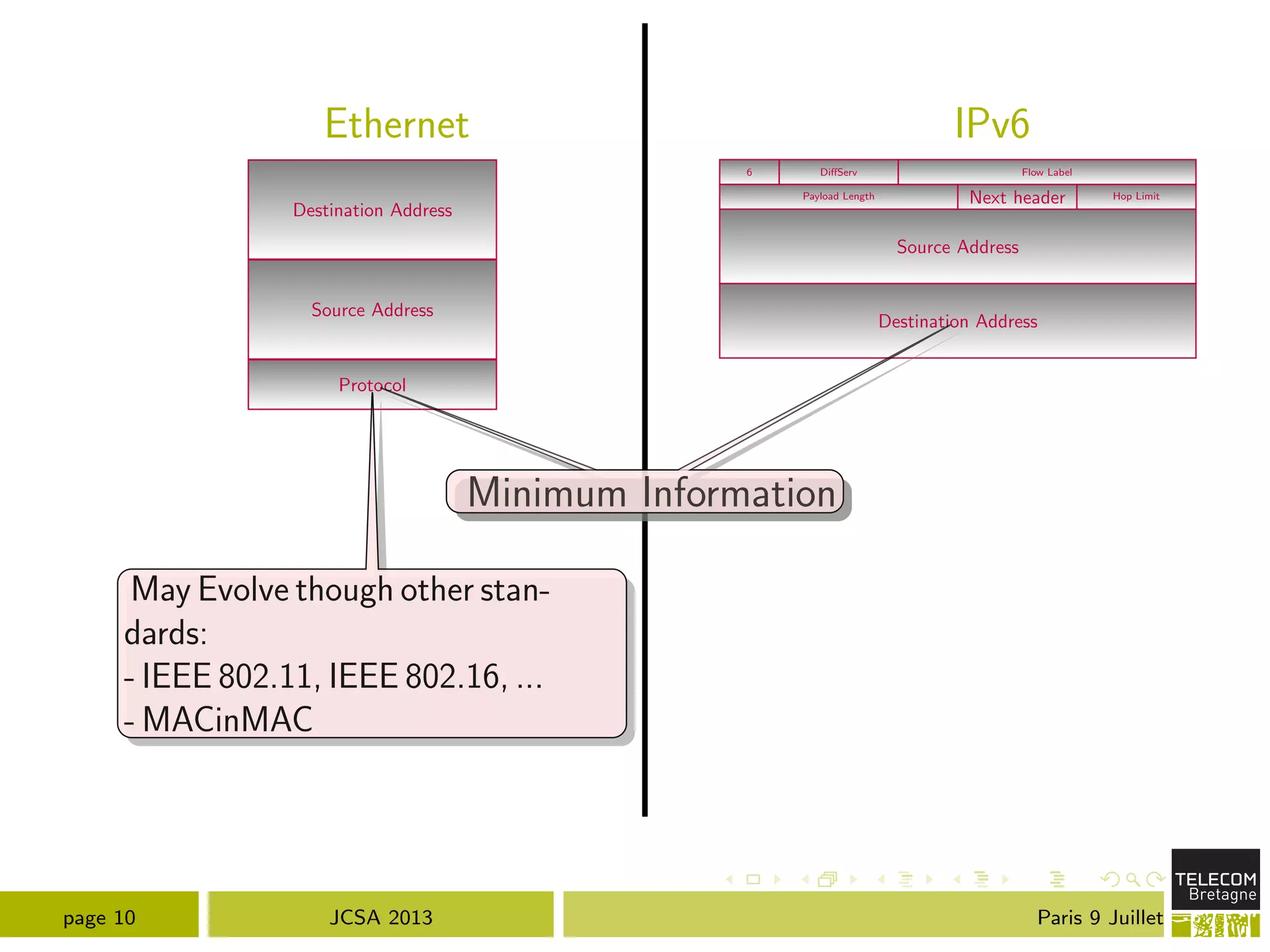
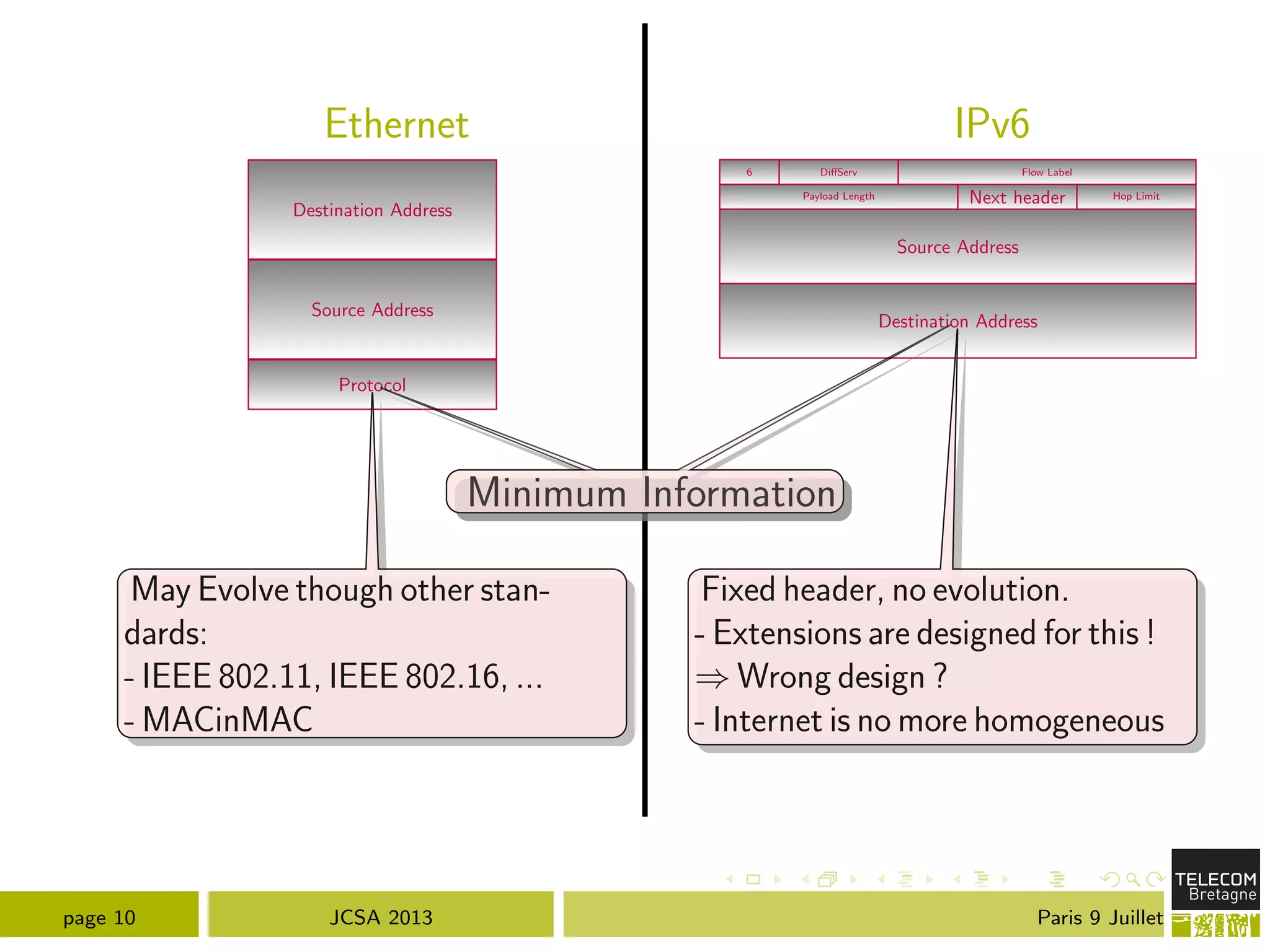
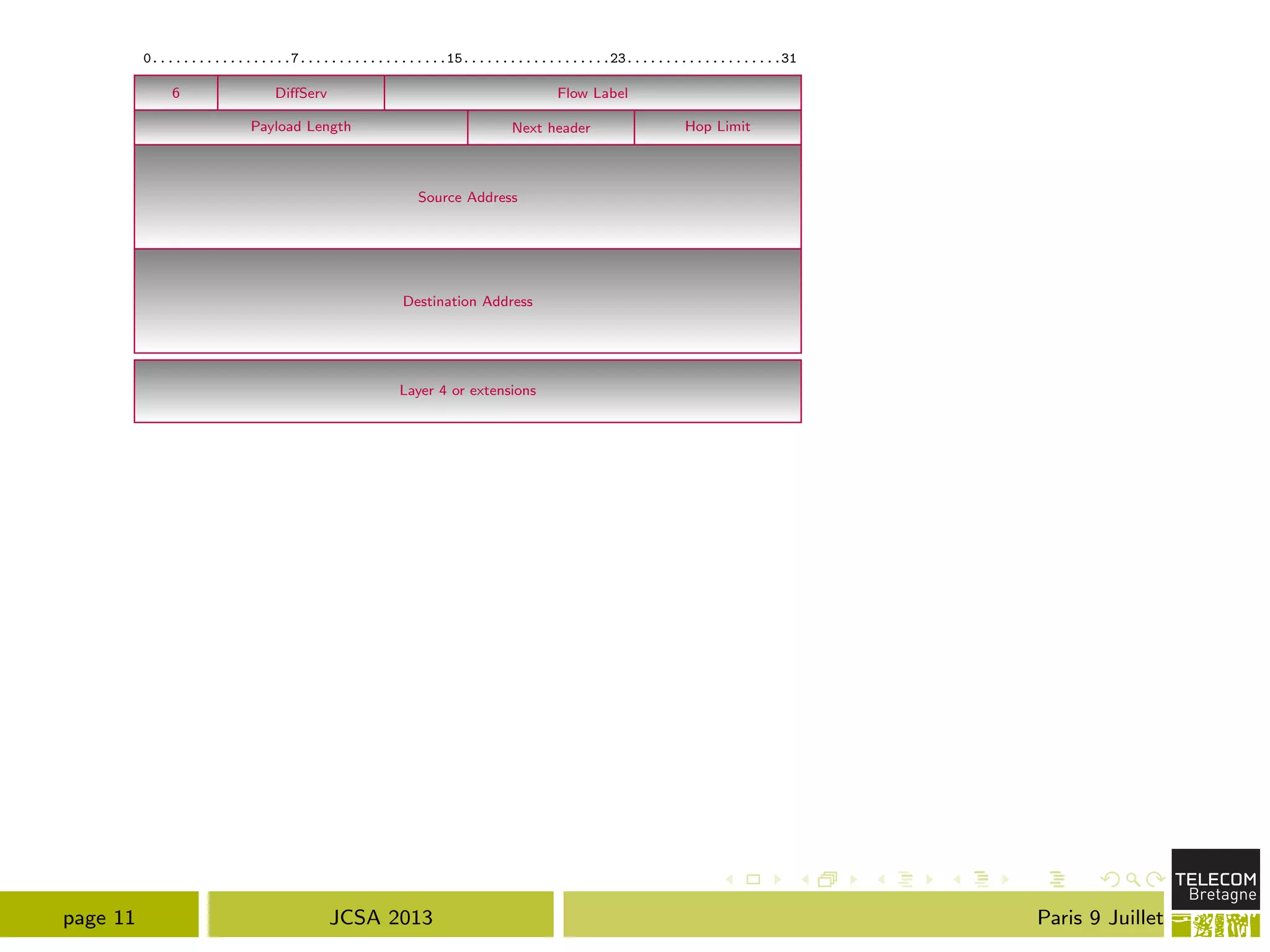
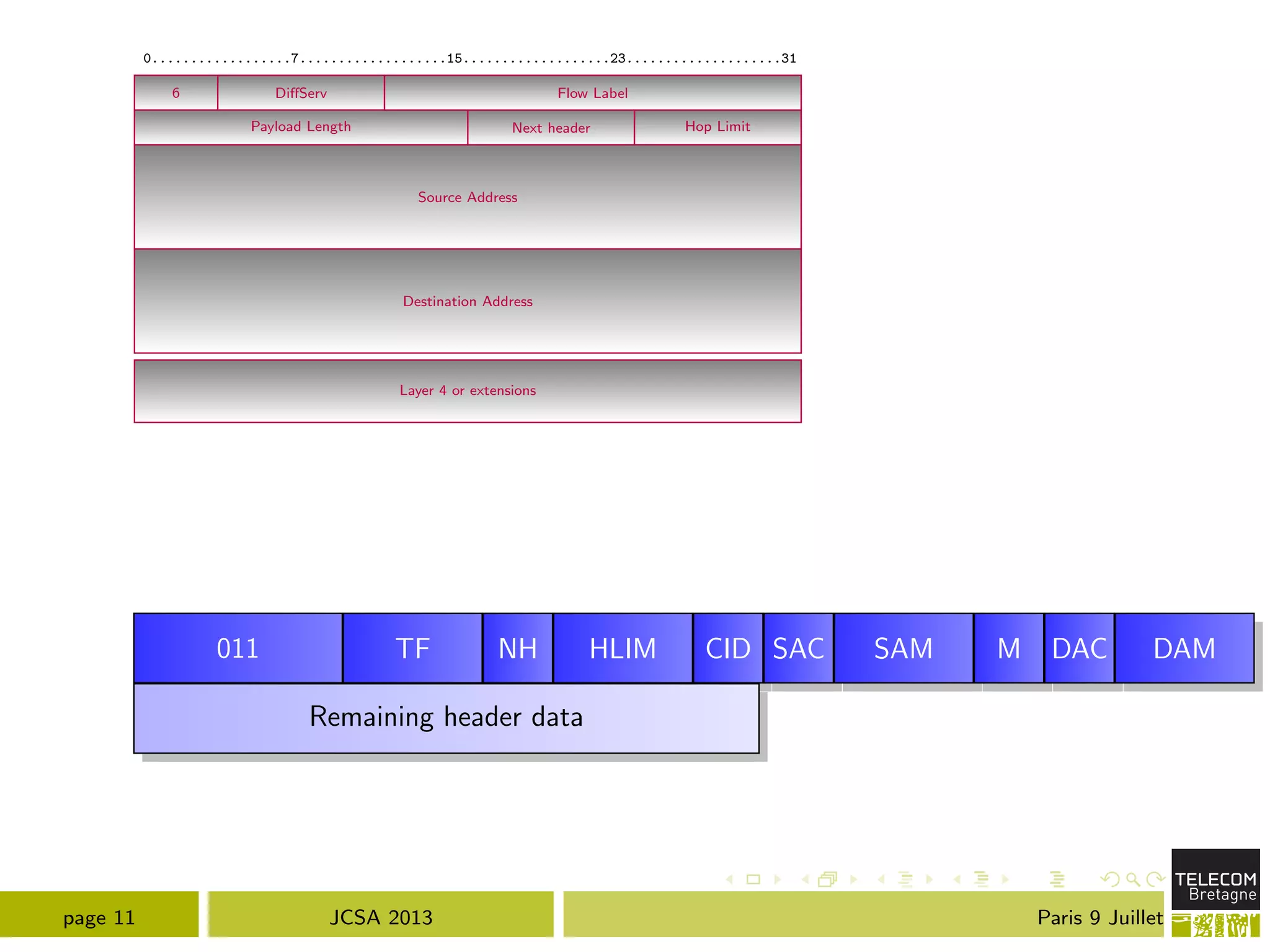
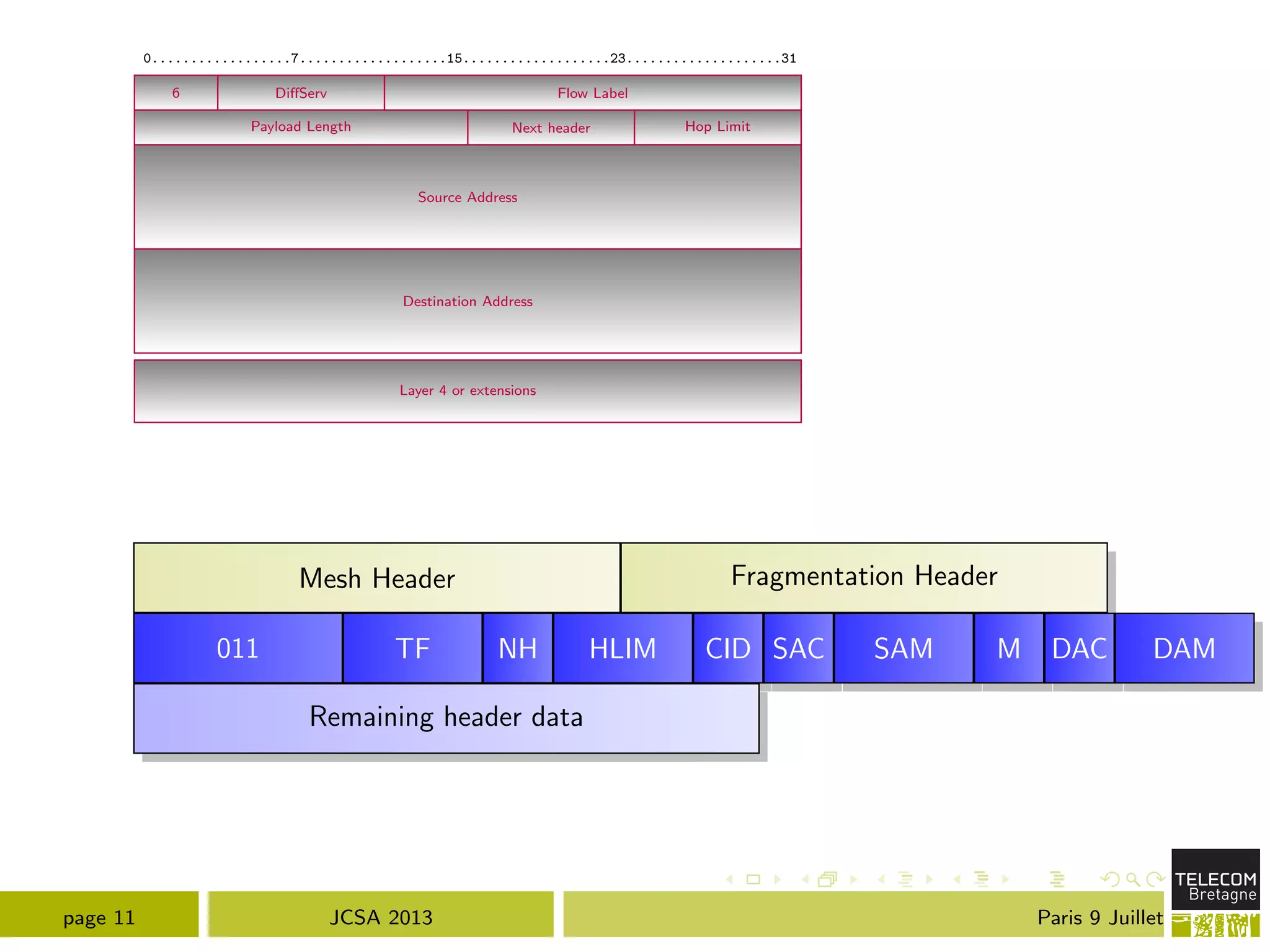
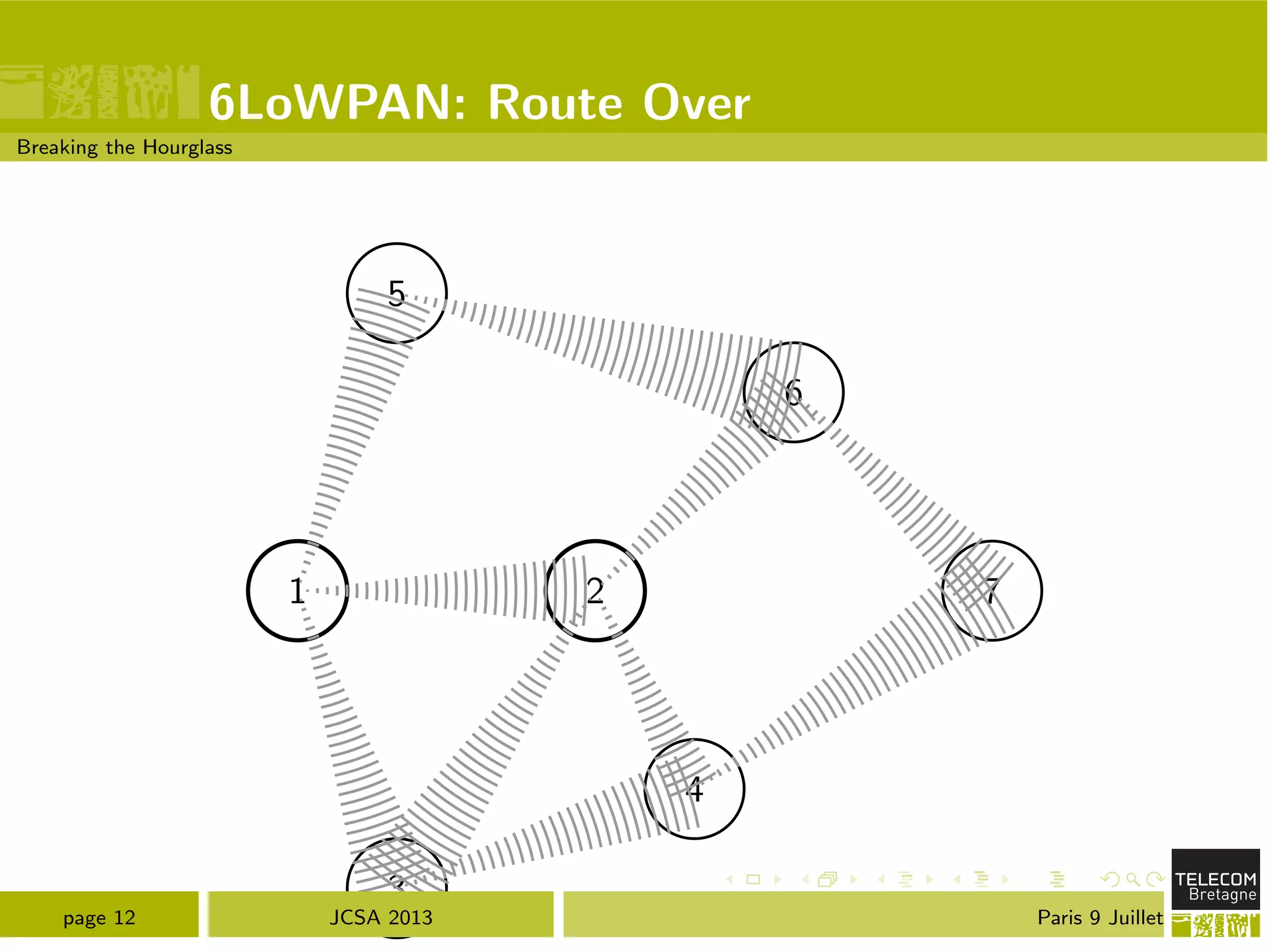
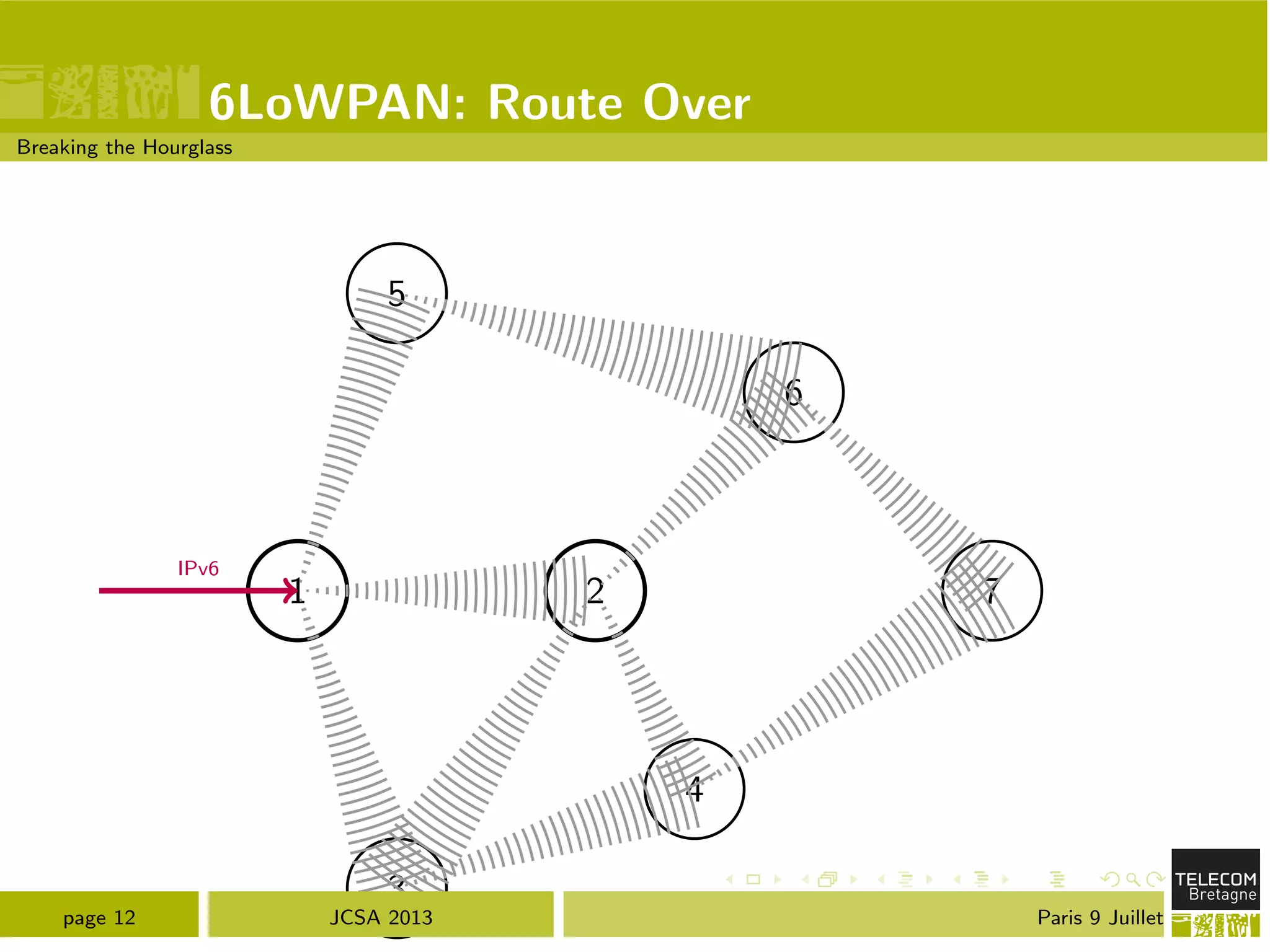
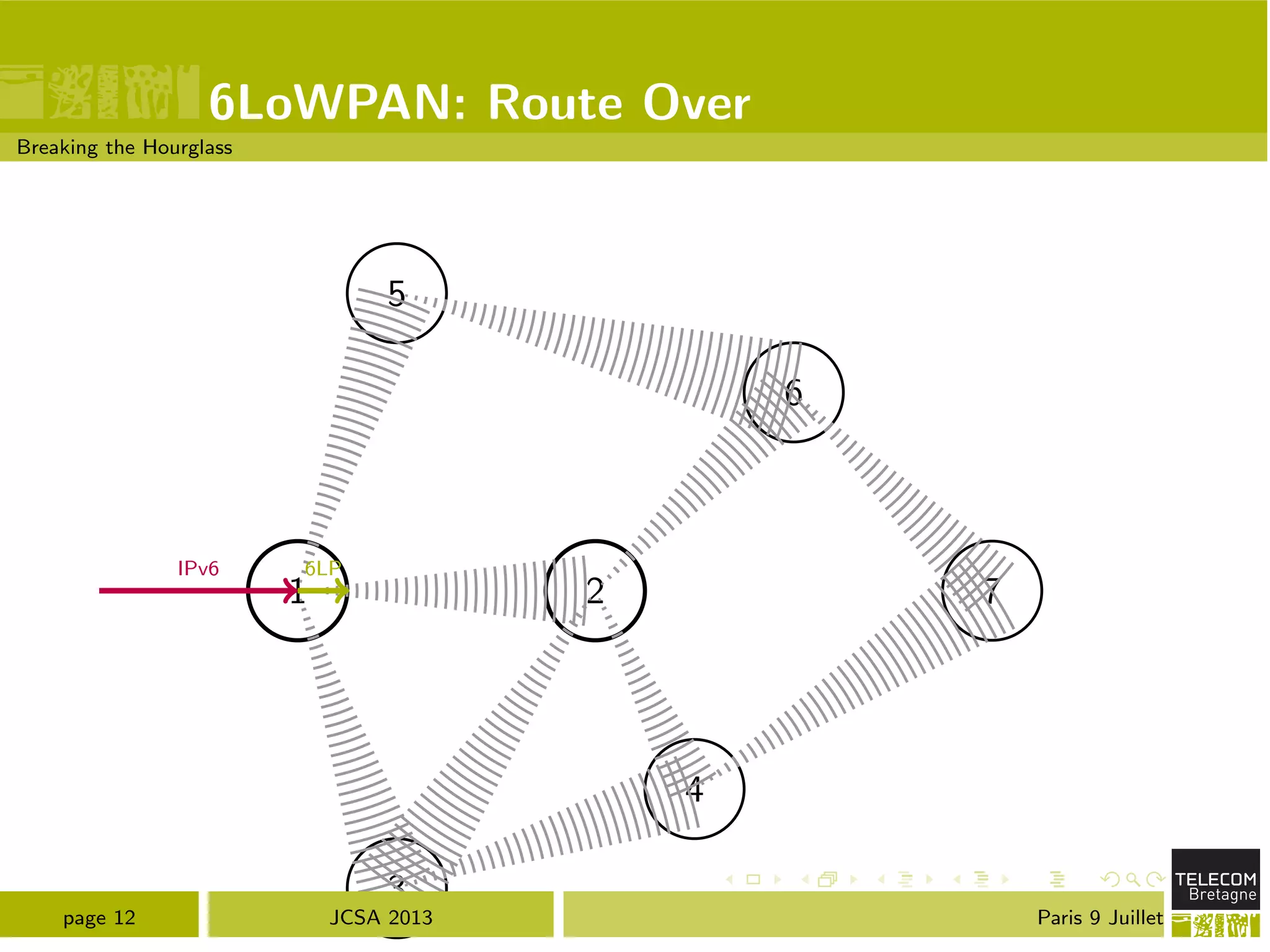
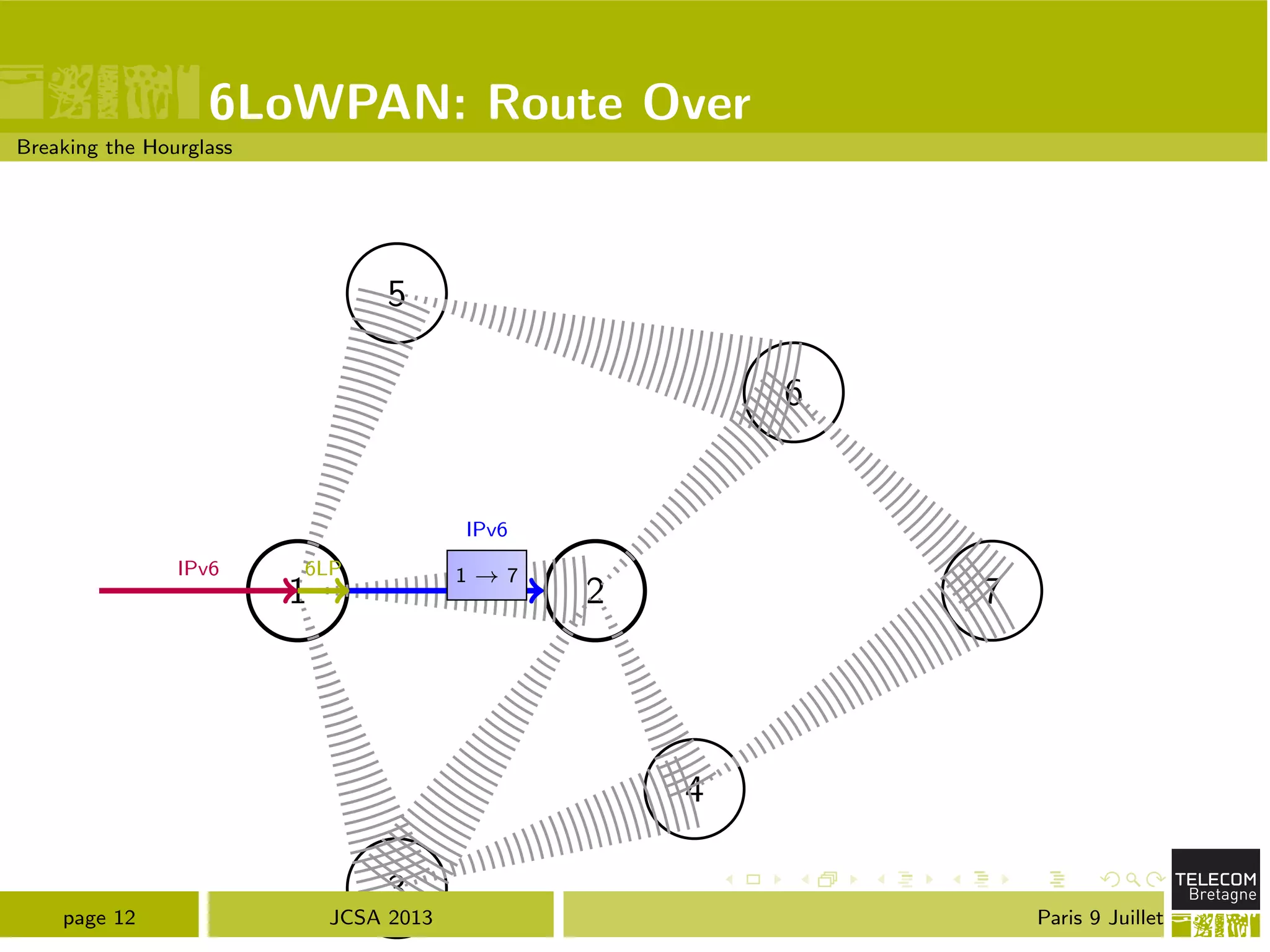
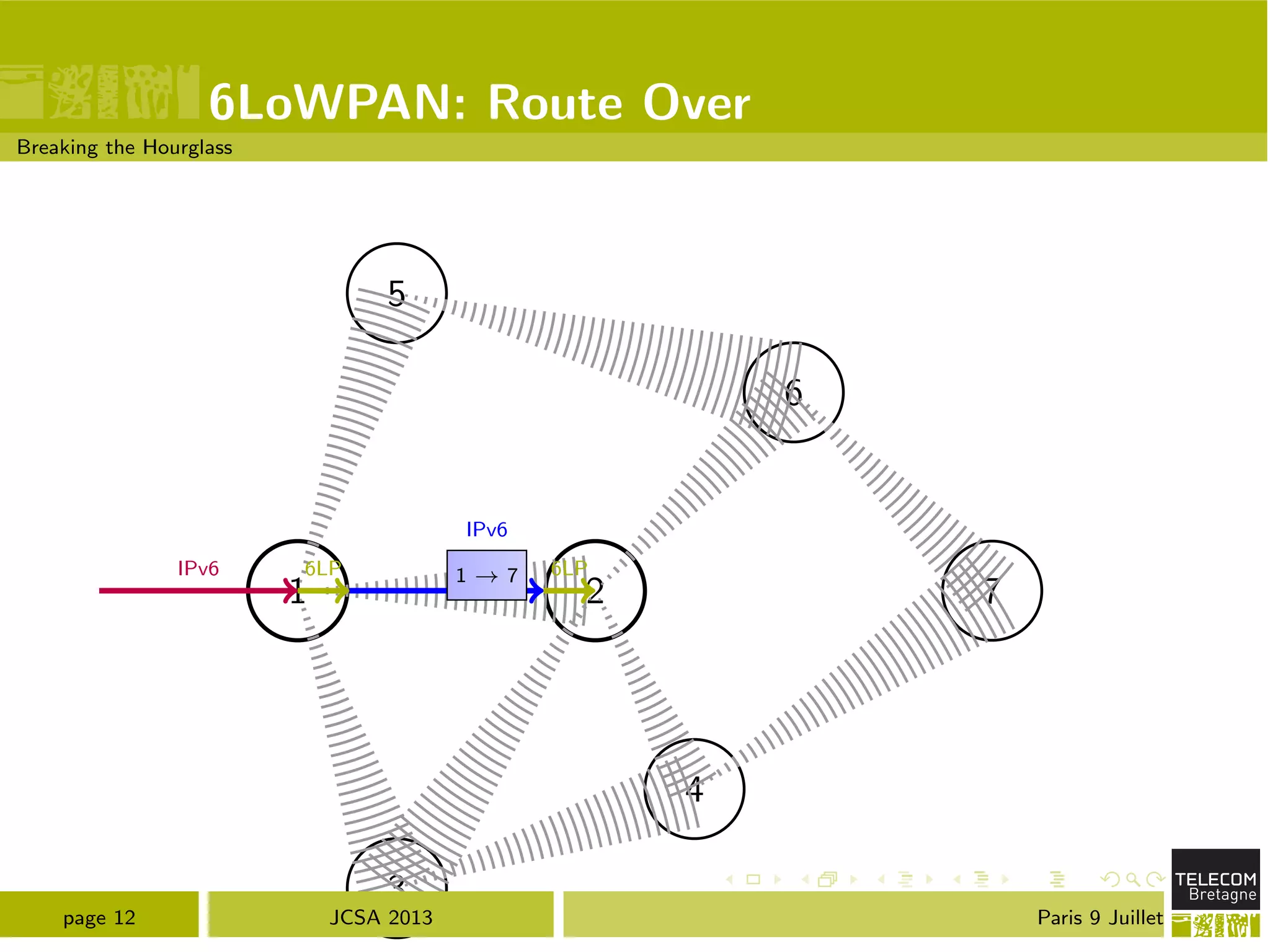
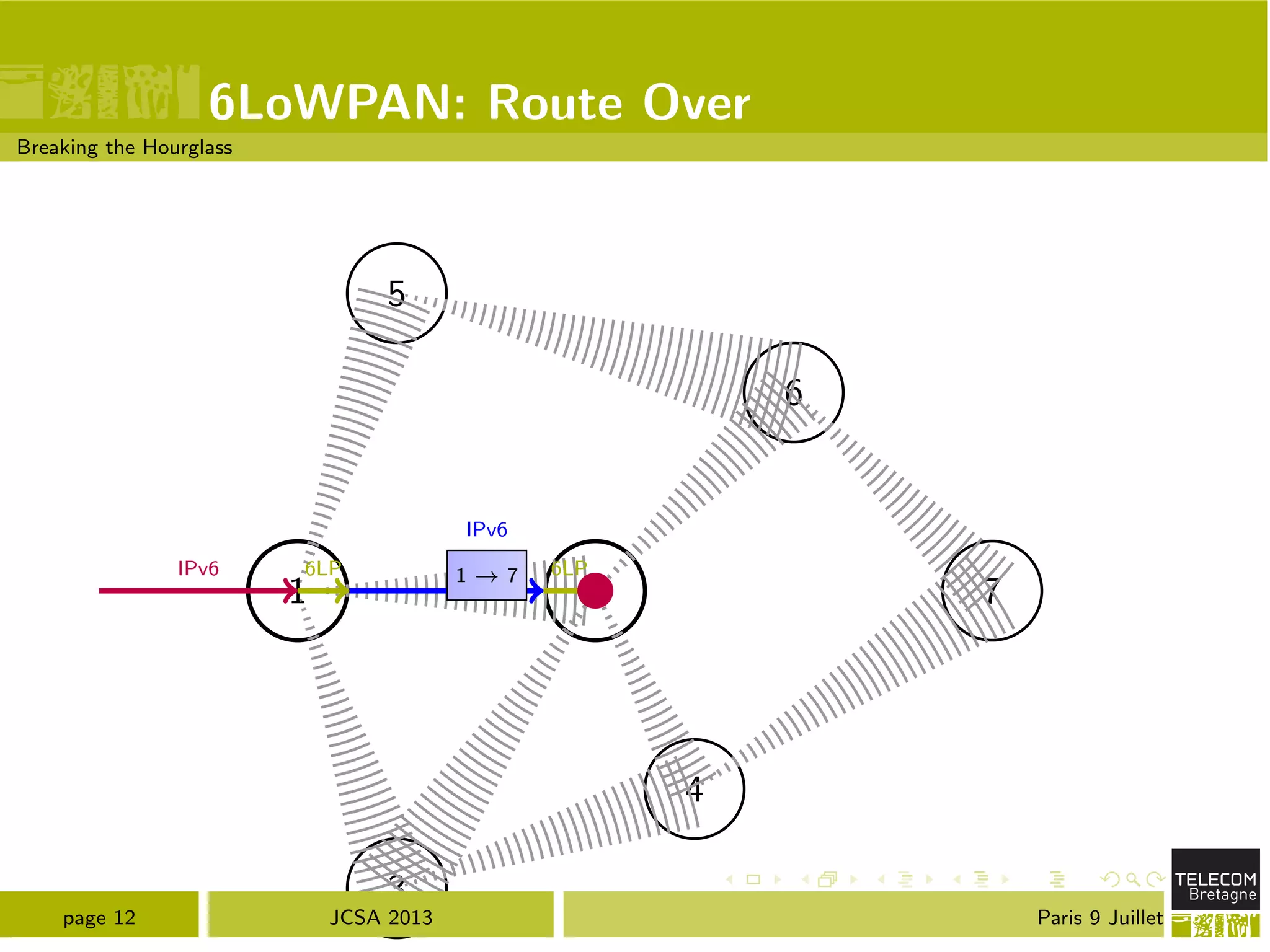
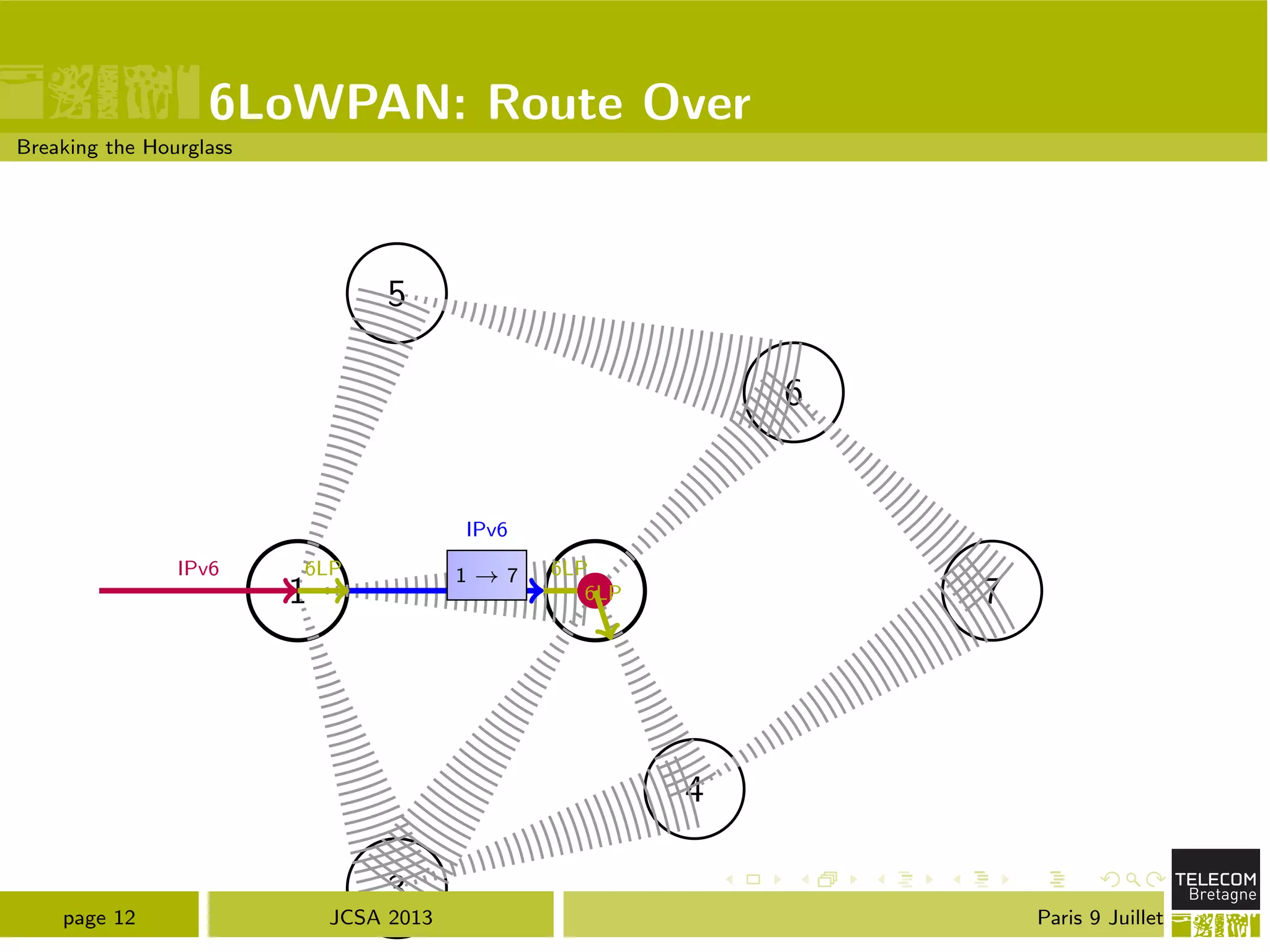
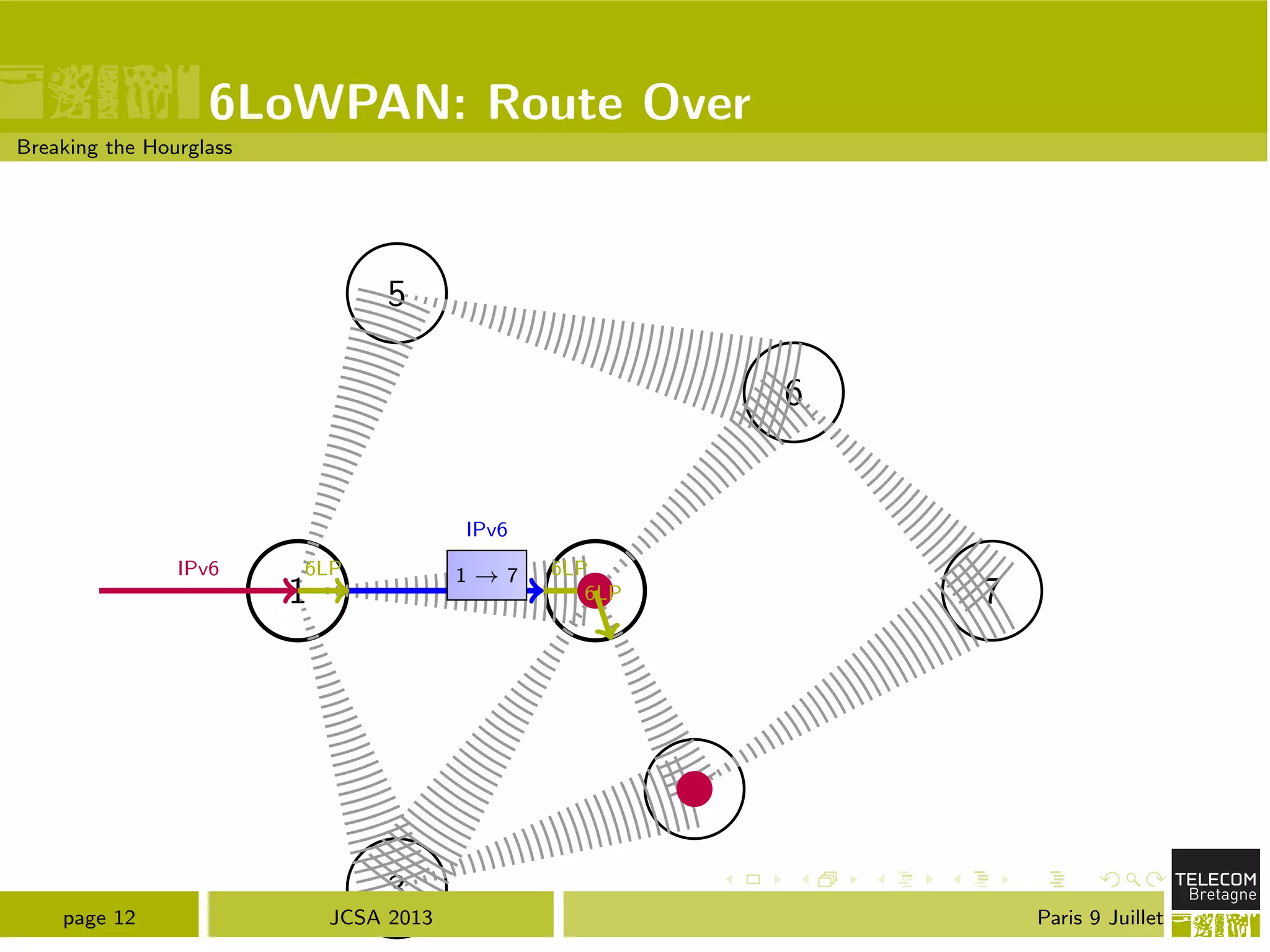
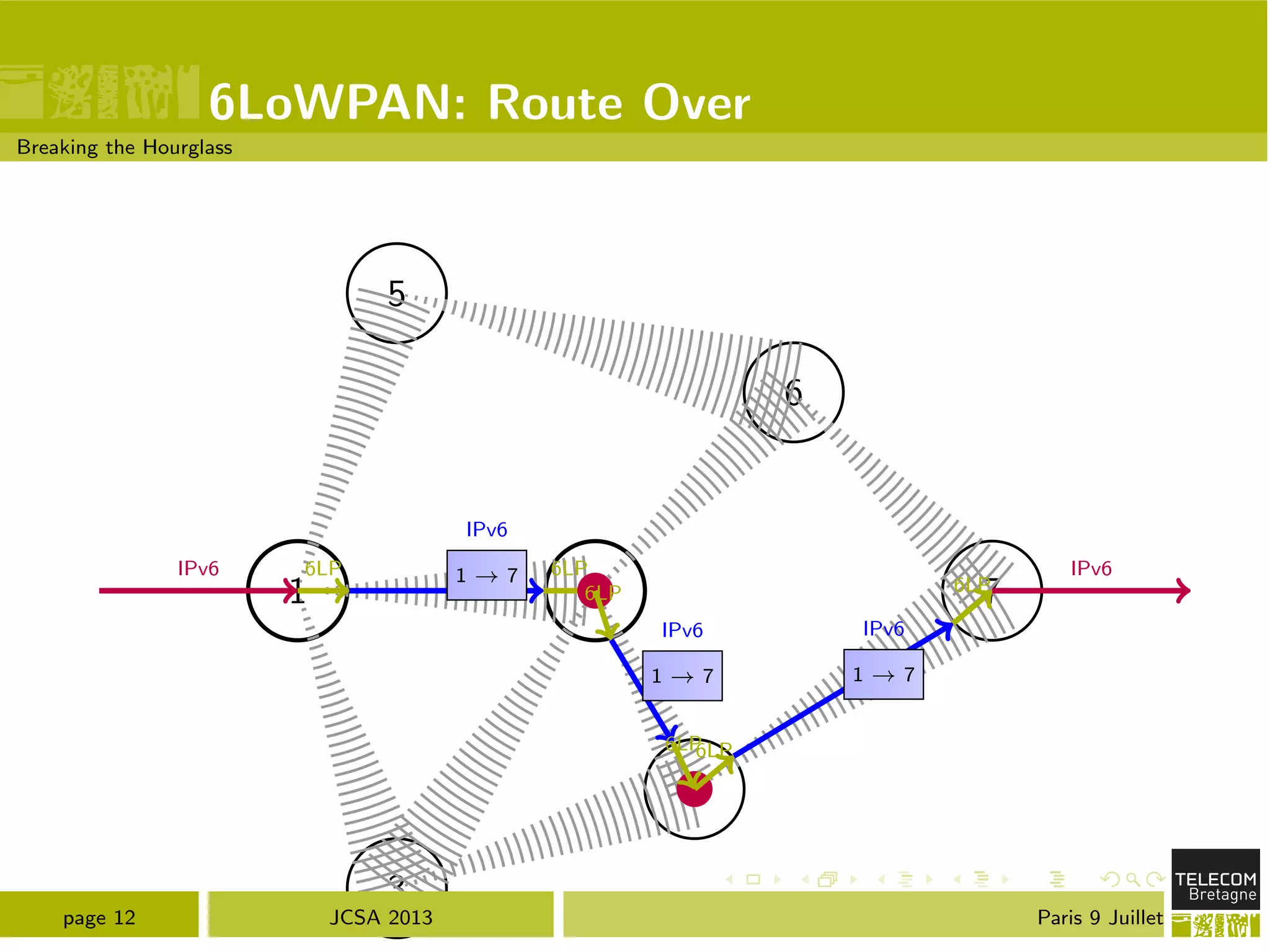
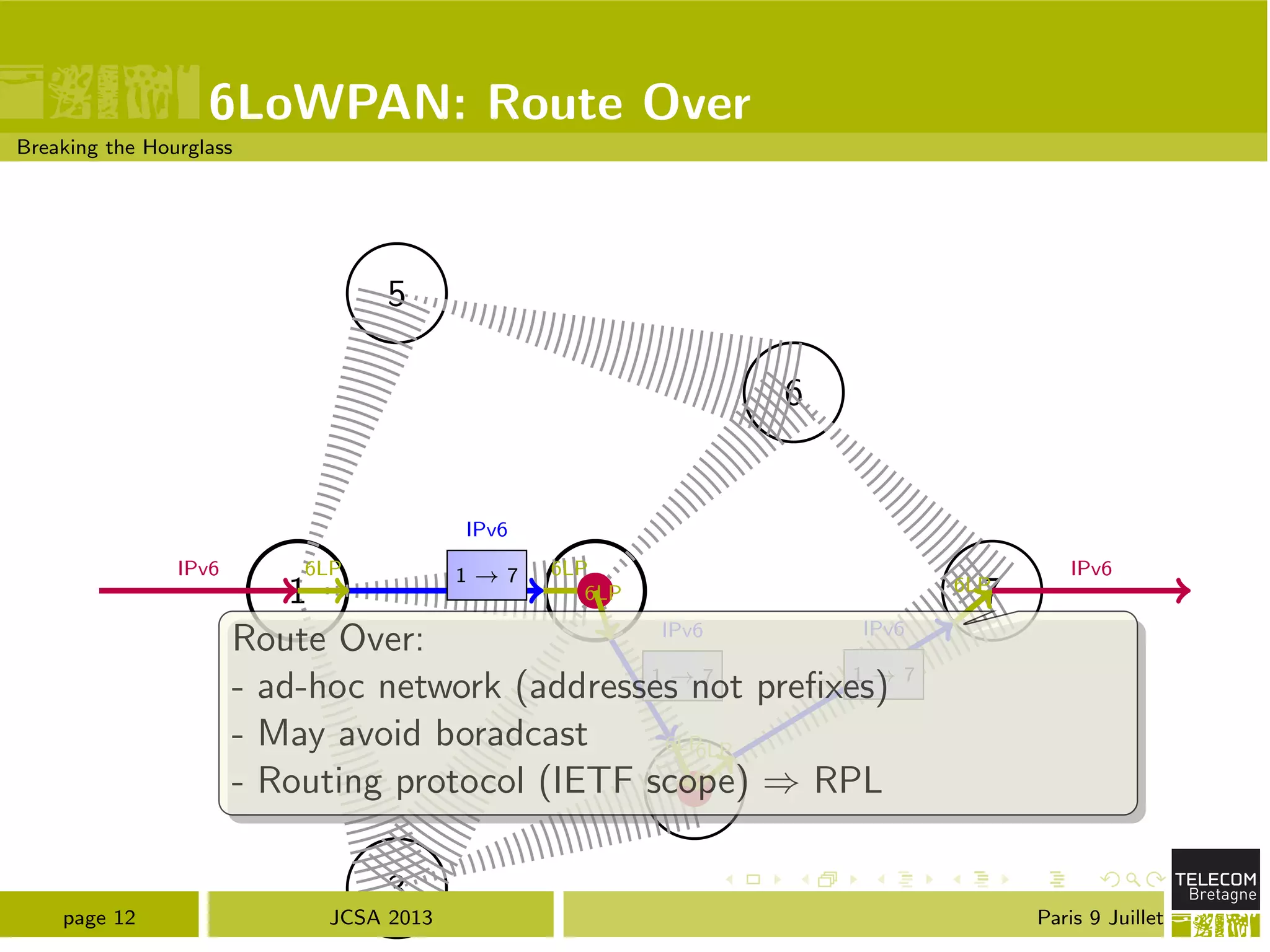
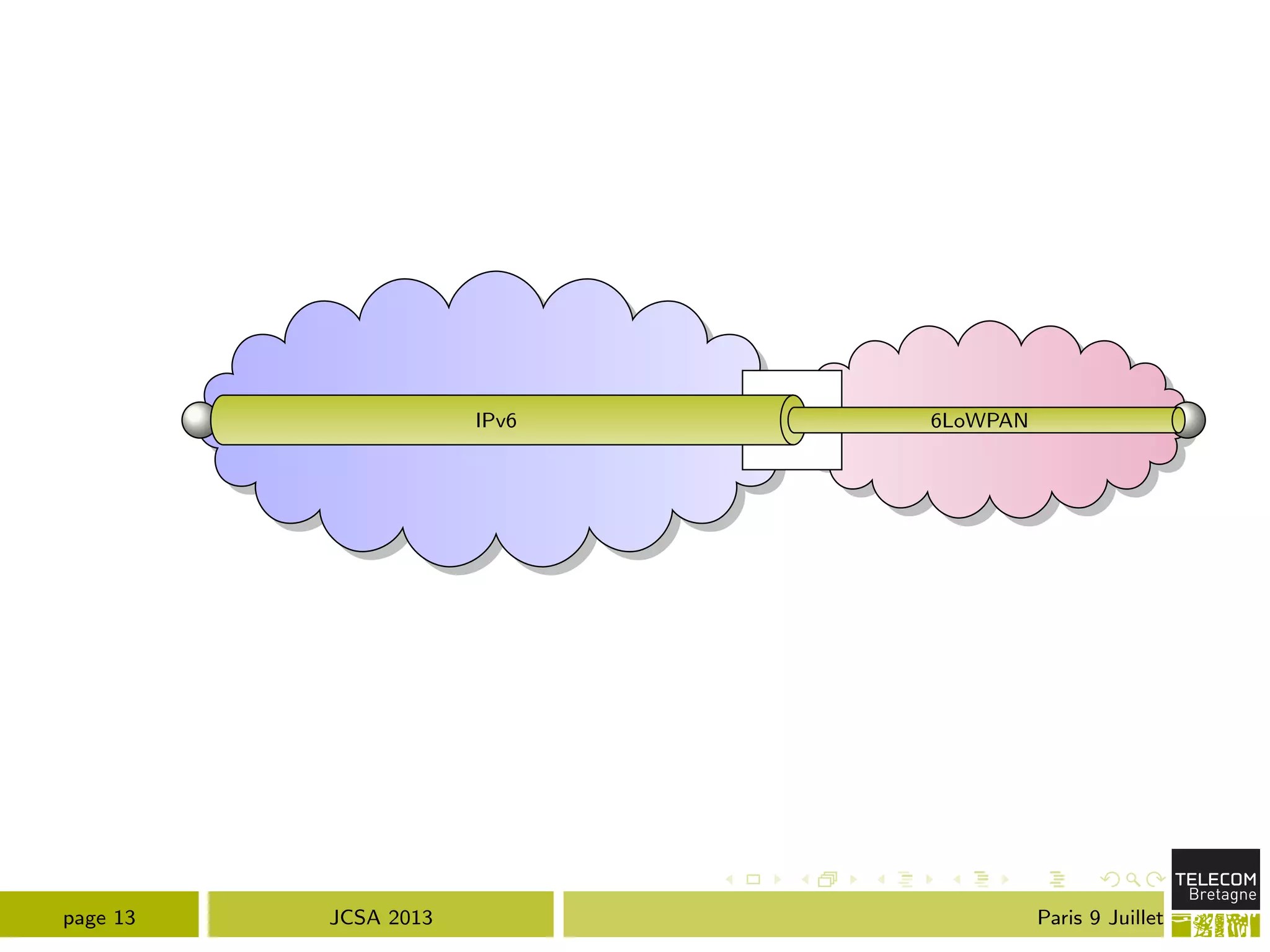
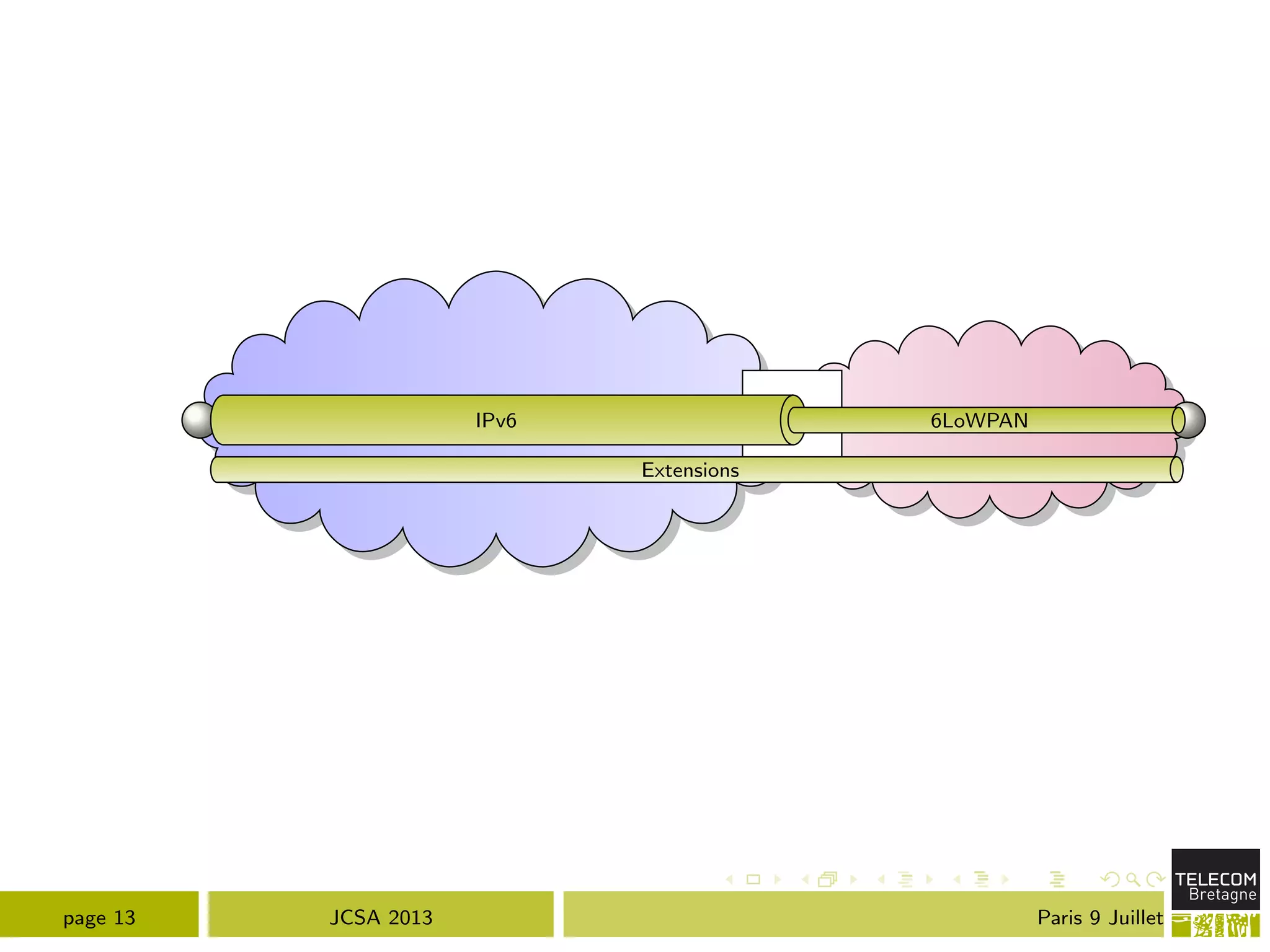
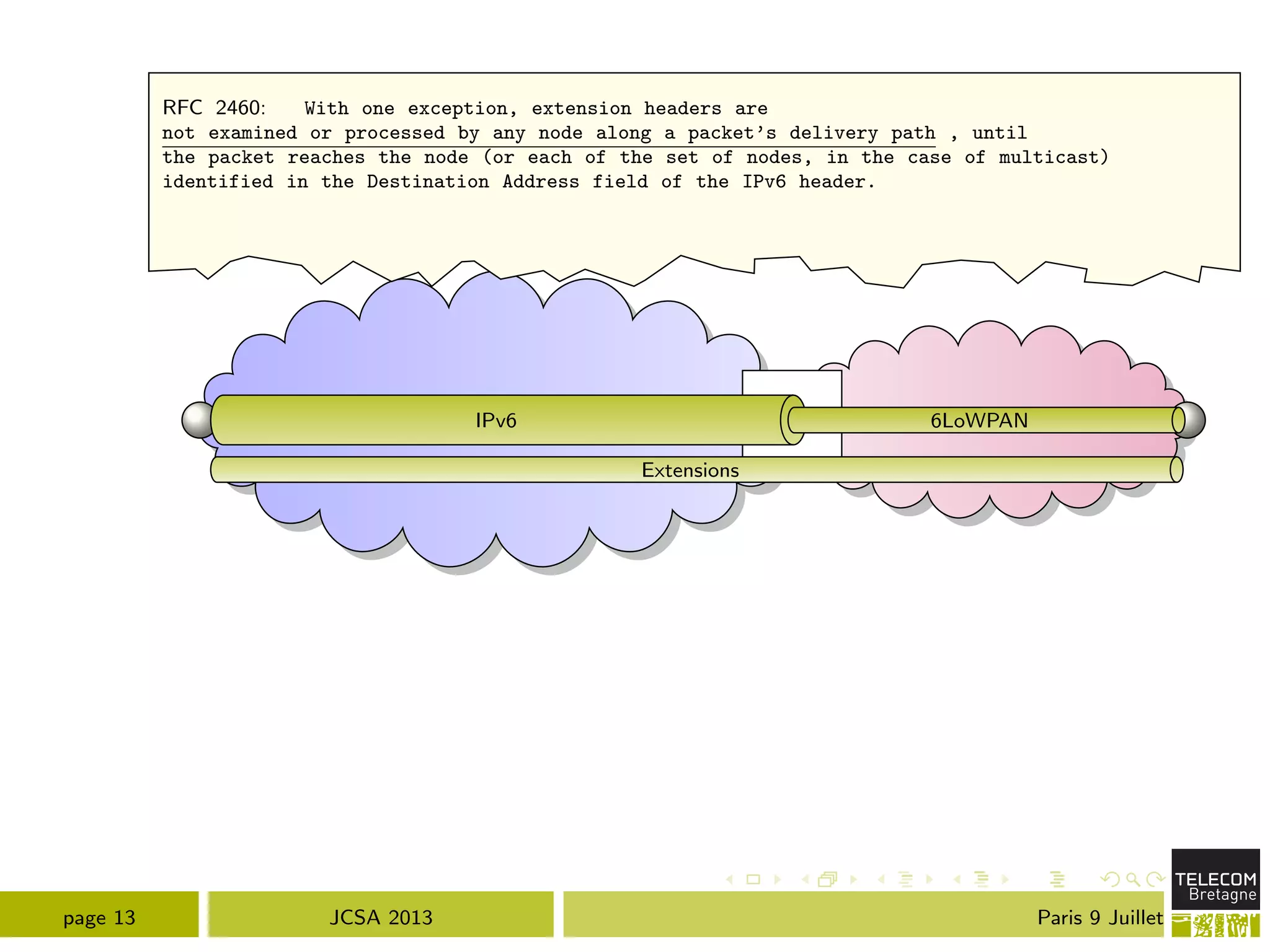
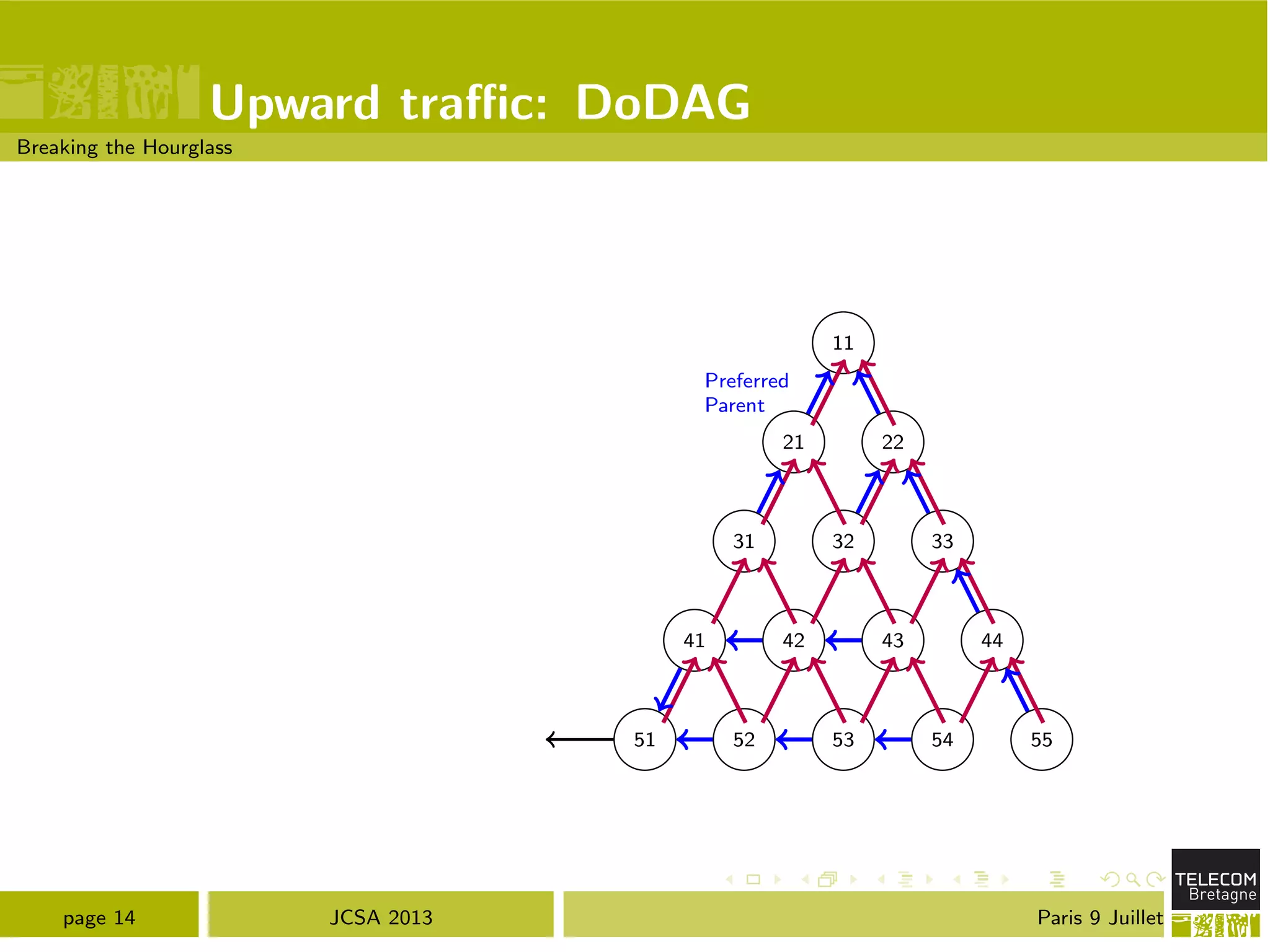
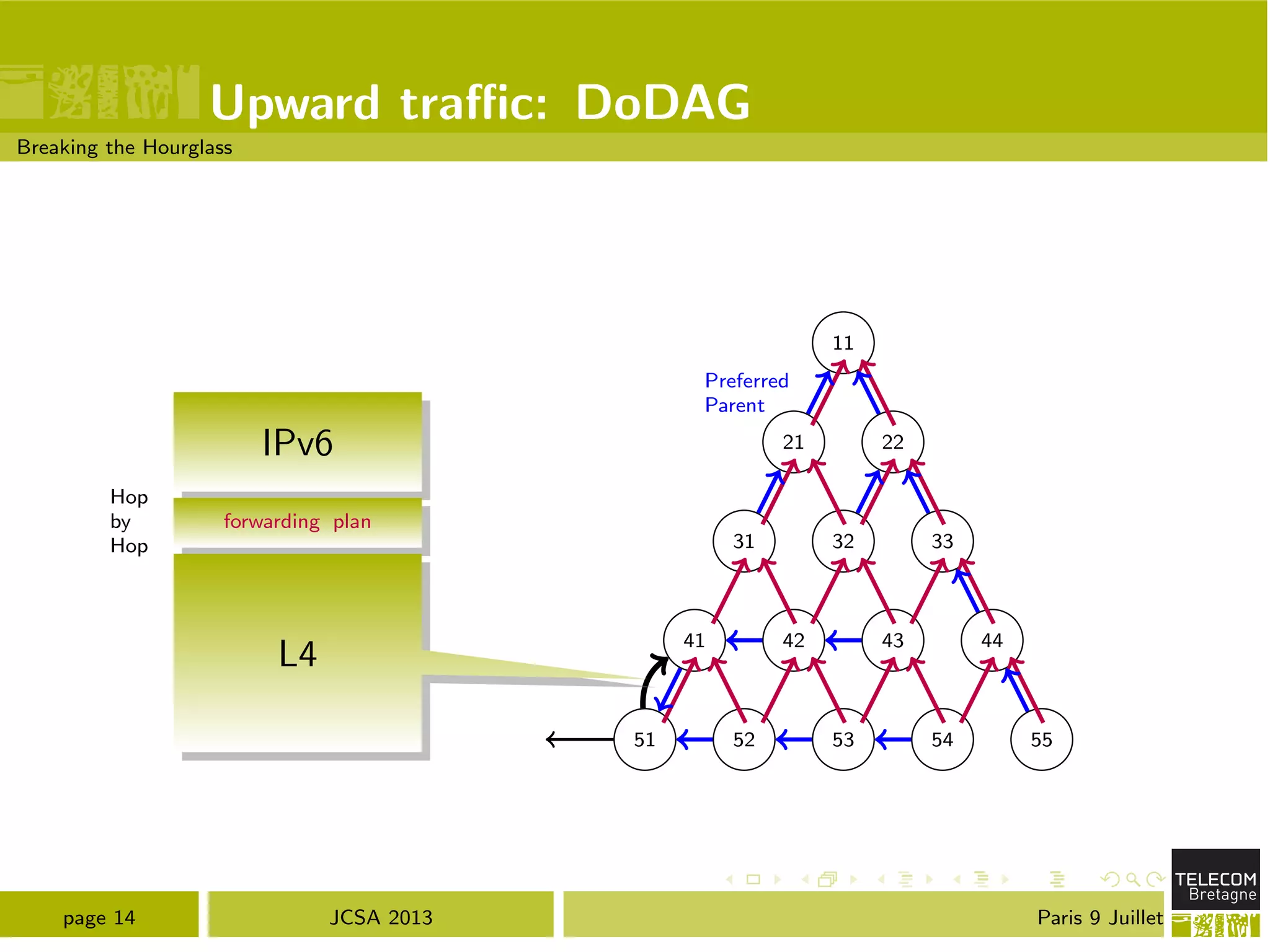
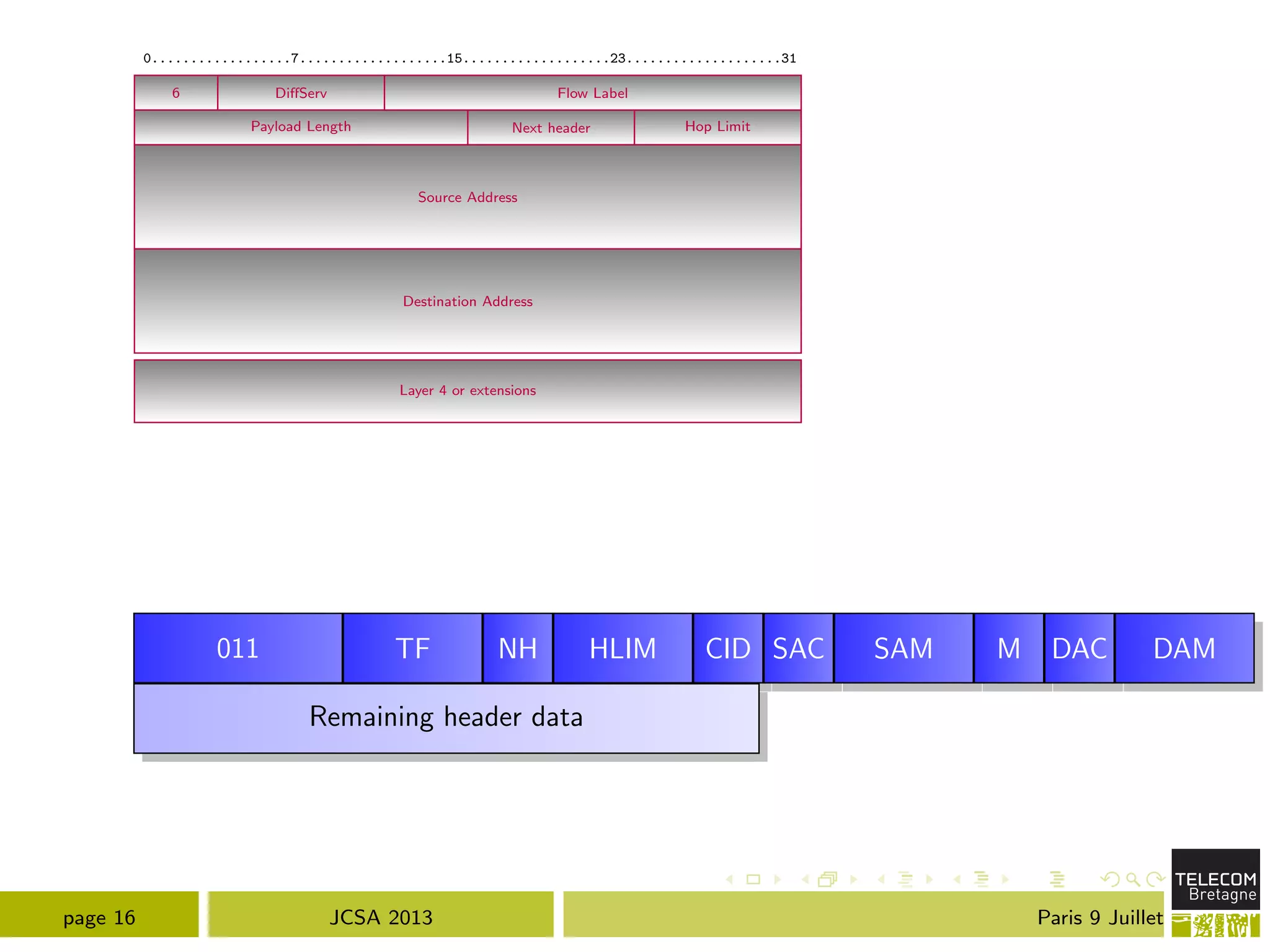
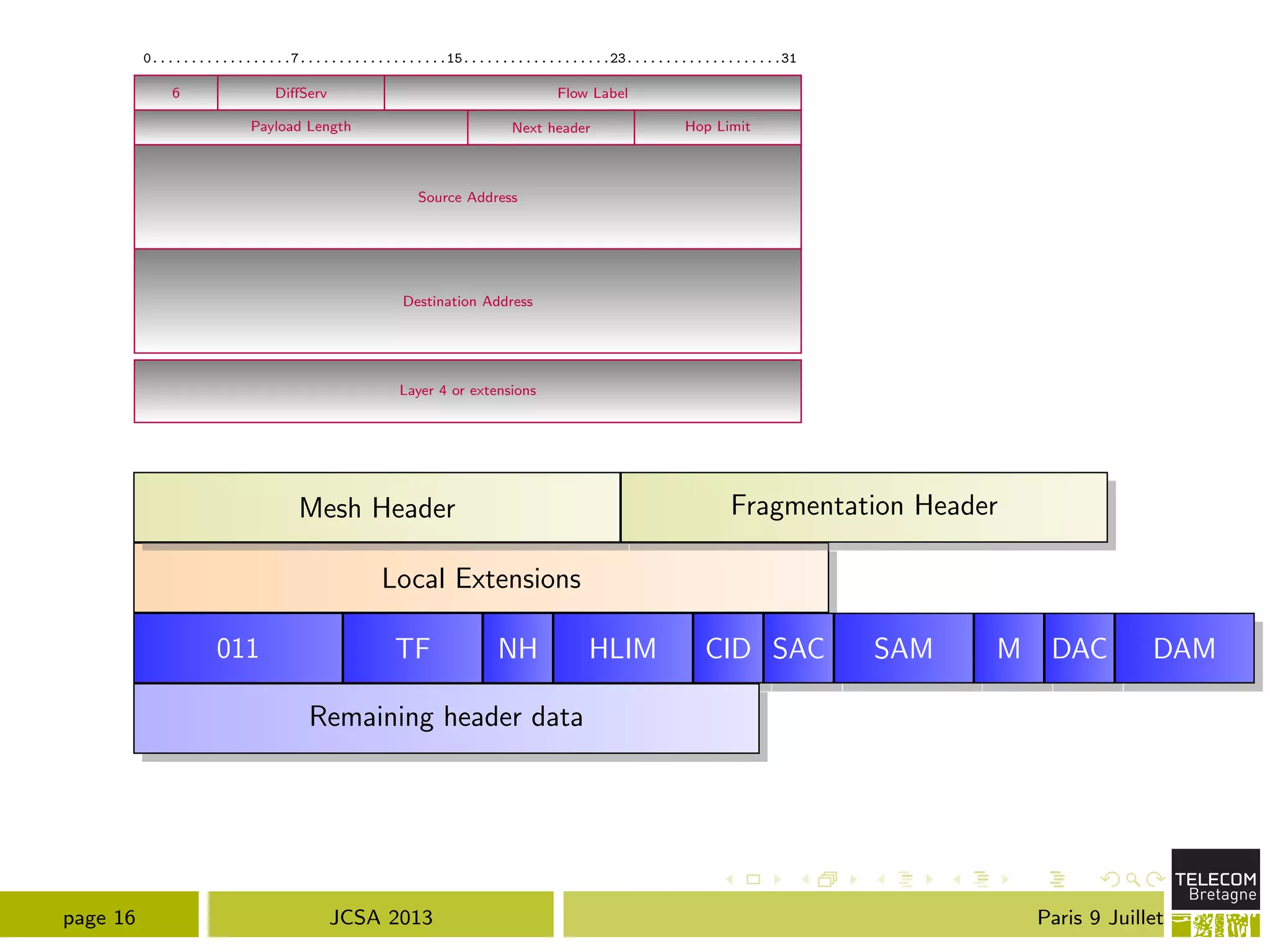
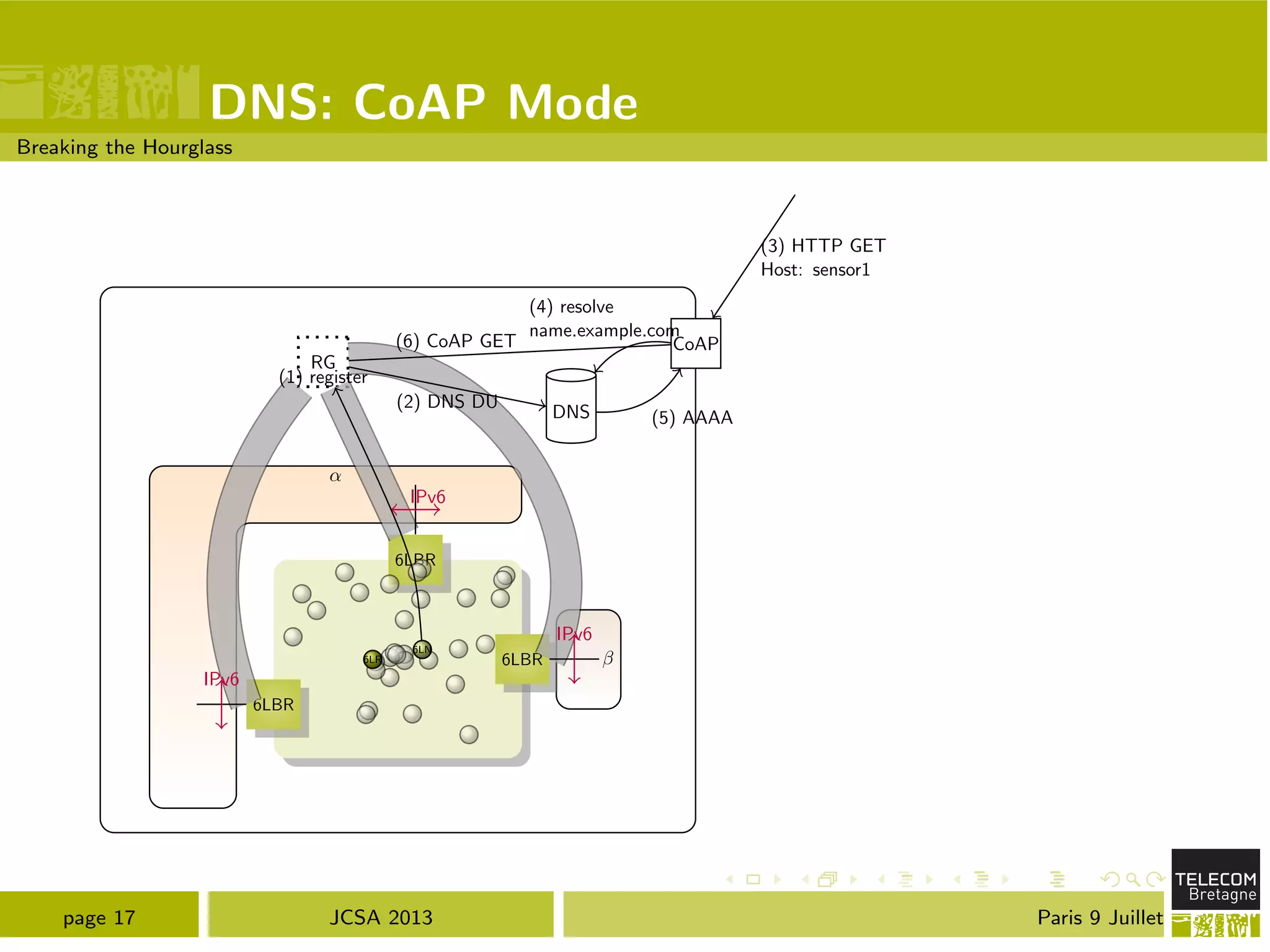
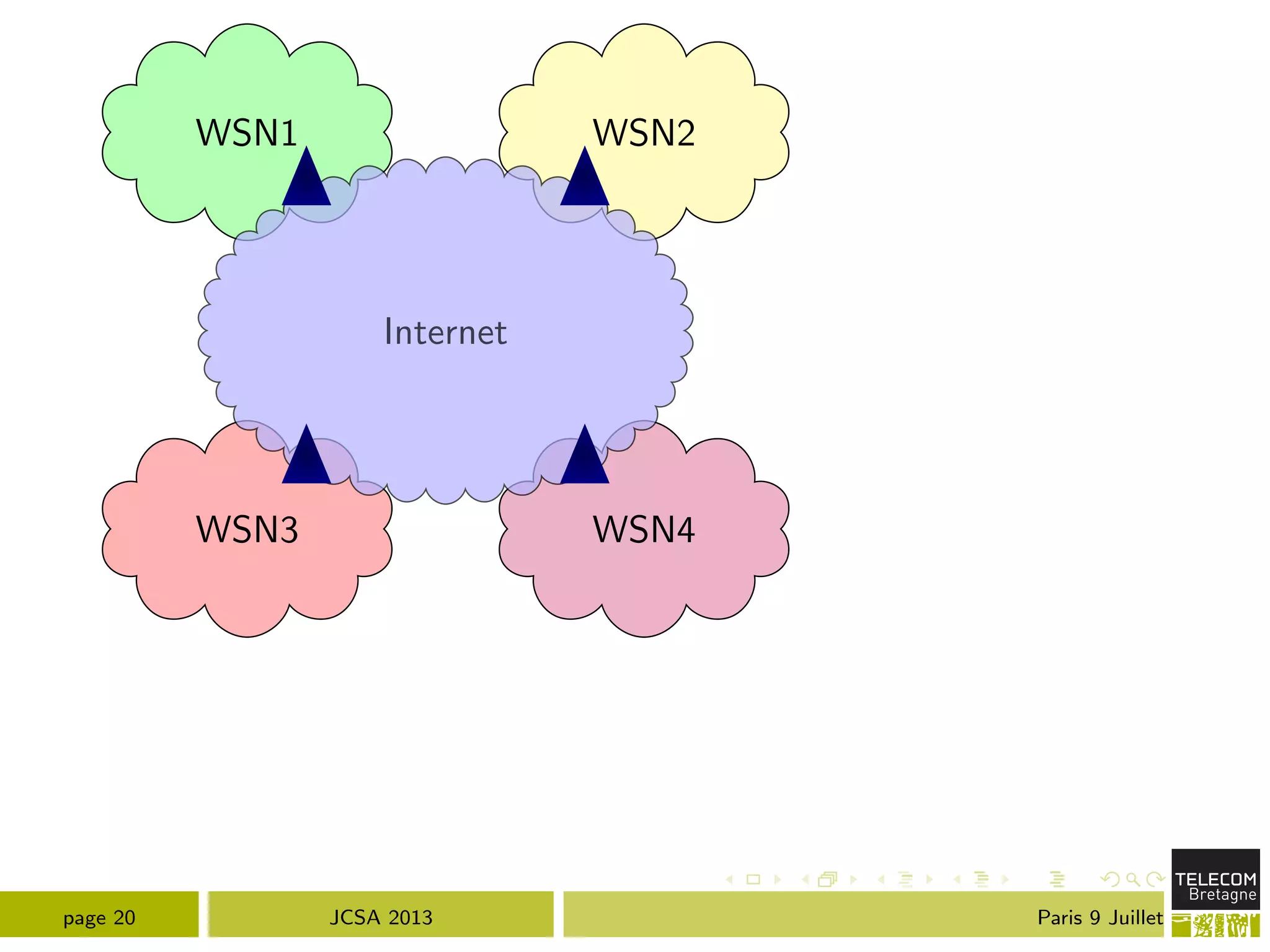
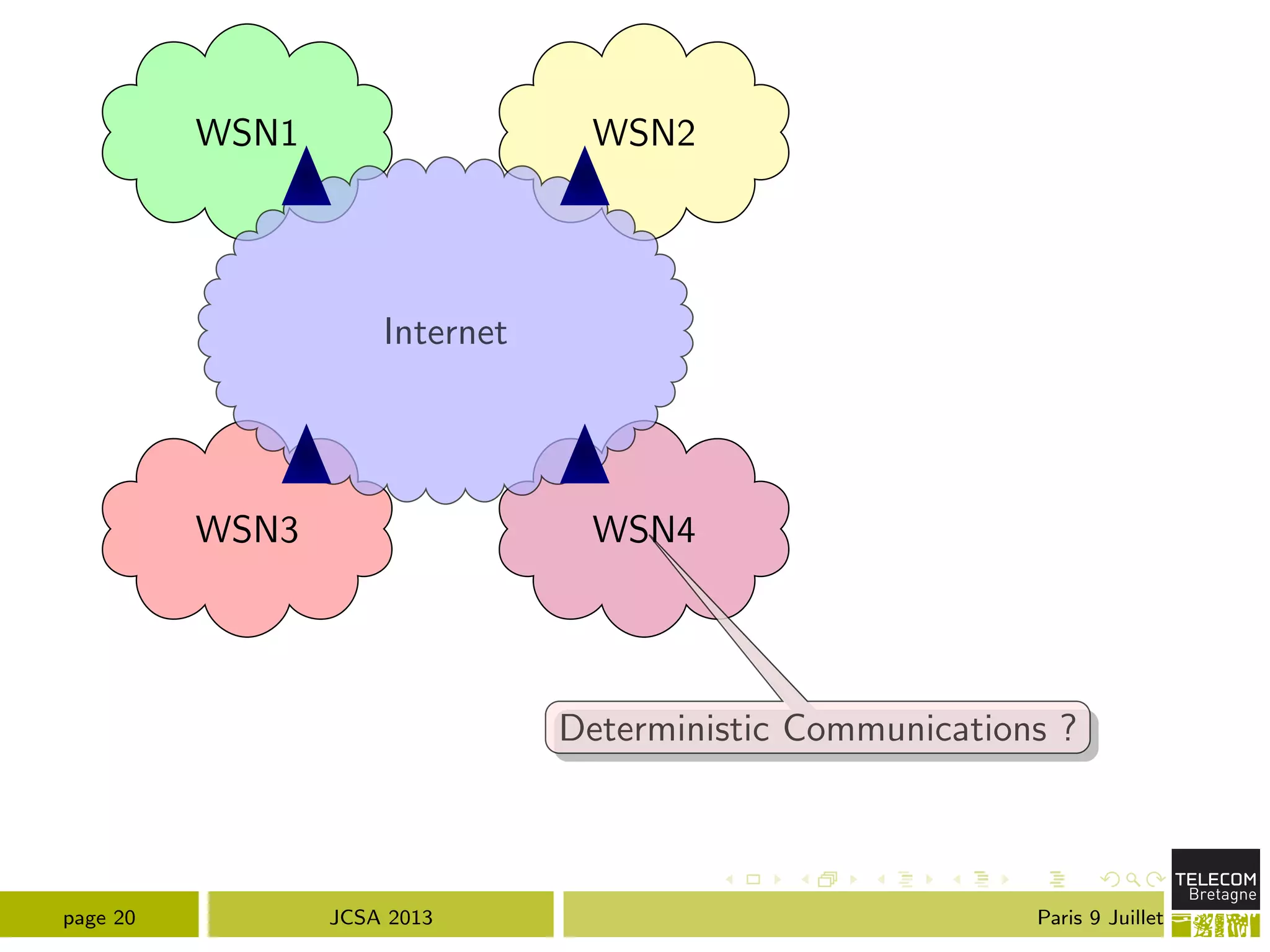
The document discusses various aspects of IPv6 addressing architecture, particularly focusing on the GSE (Global Site Endpoint) proposal that allows for complex site topology management. It delves into the structure of IPv6 addresses and the modifications required for routing information to adapt to internal and external network changes. Additionally, the text touches on the challenges of unique identifier management for end systems within the broader context of low-power and lossy networks.