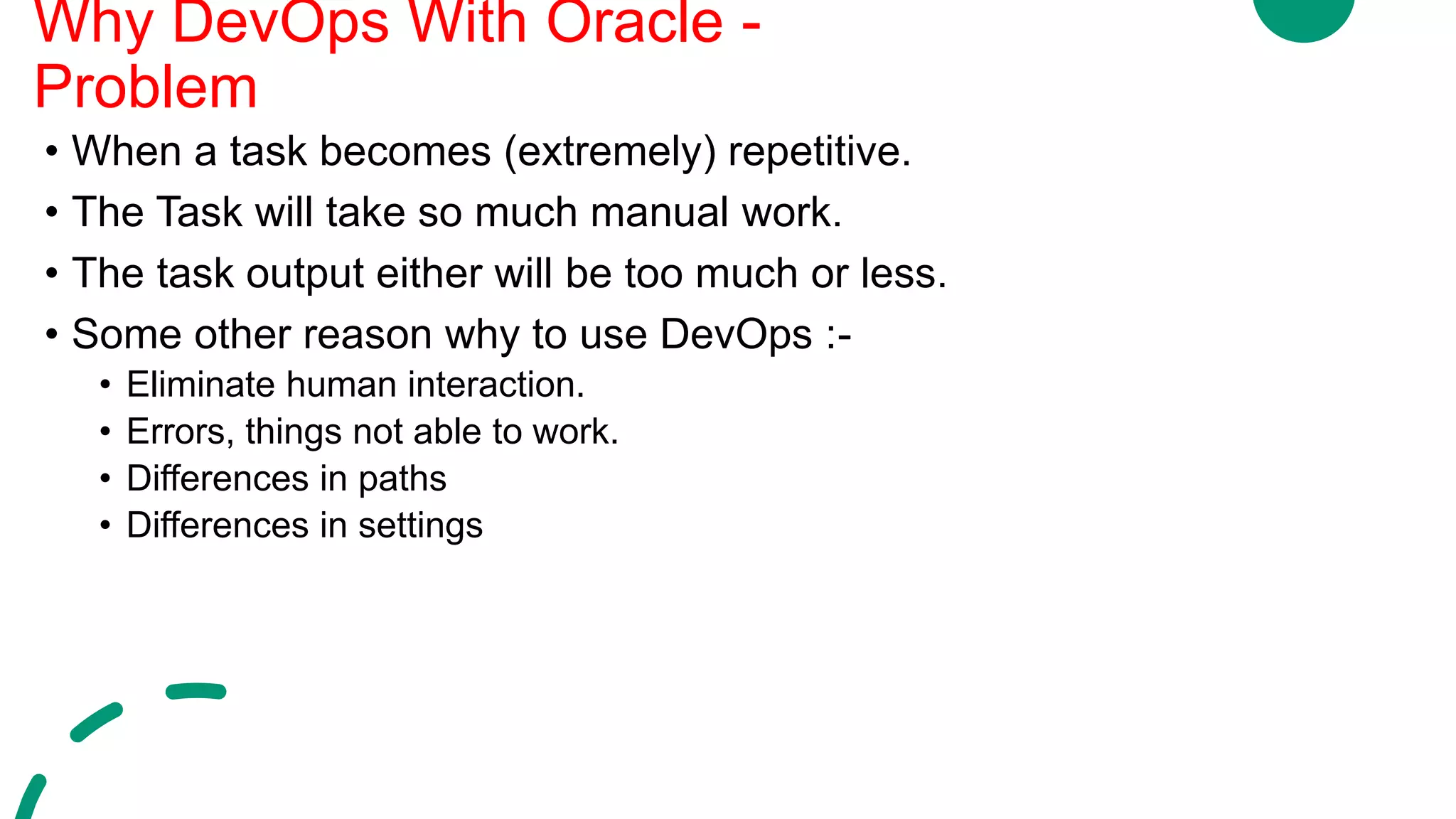
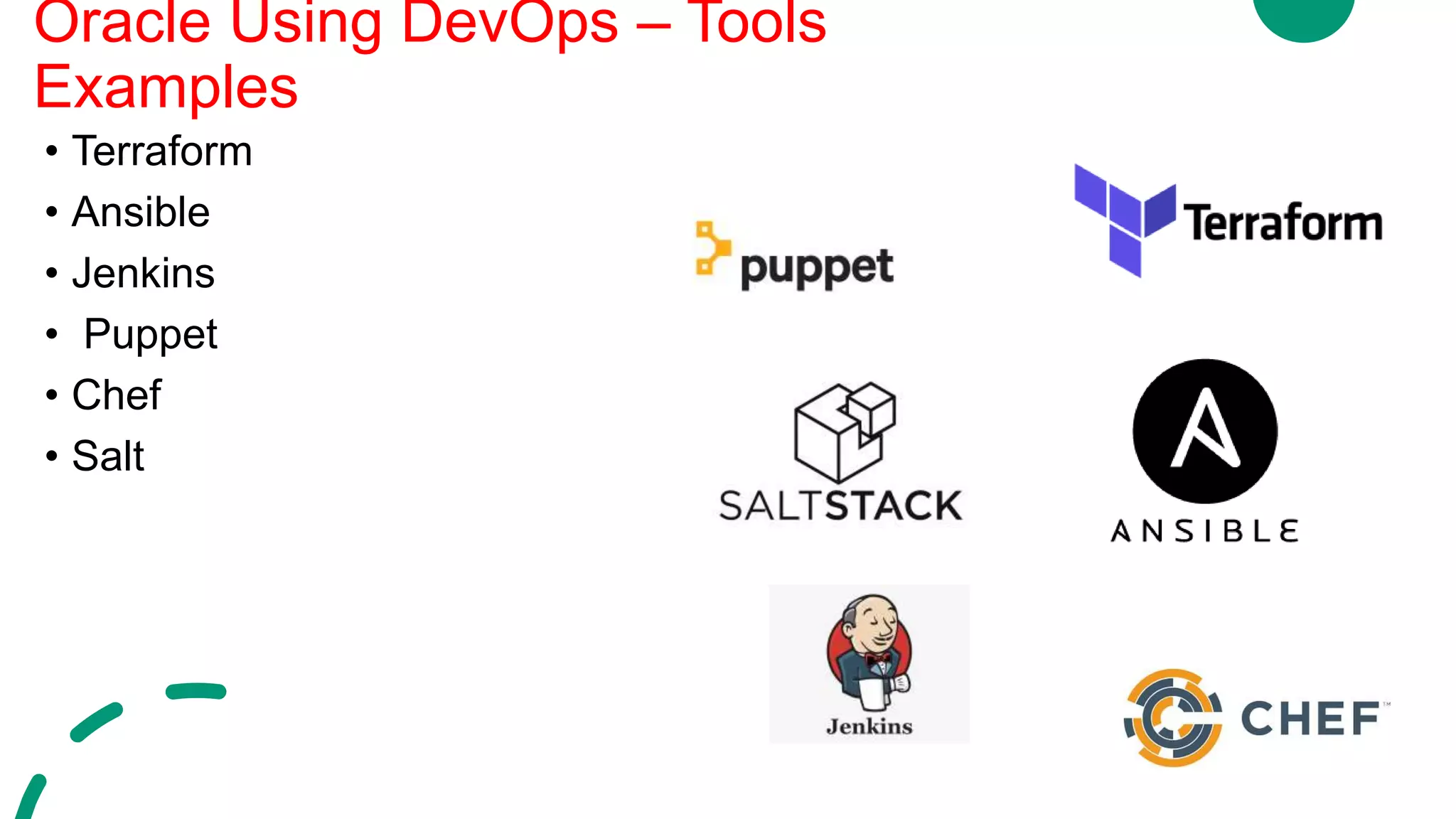
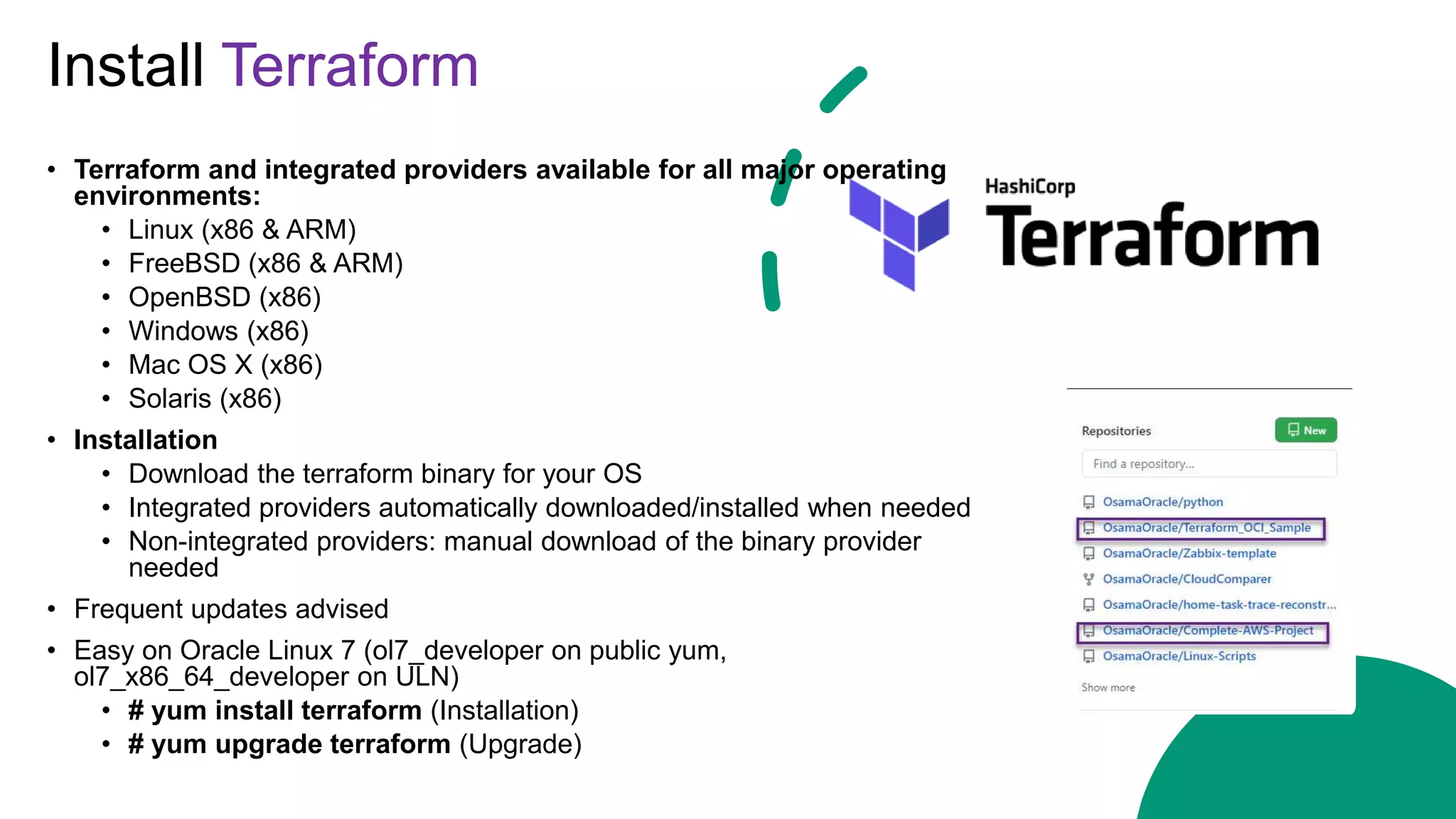
- The document discusses using DevOps practices for databases. It provides an overview of DevOps and how it relates to databases.
- It introduces the speaker, Osama Mustafa, who is a founder, CEO, author and presenter in the Oracle community.
- The agenda includes questions and answers, automation examples, and how DevOps can make a DBA's life easier. It will also explain what DevOps is, why it is used, and when it should be implemented.





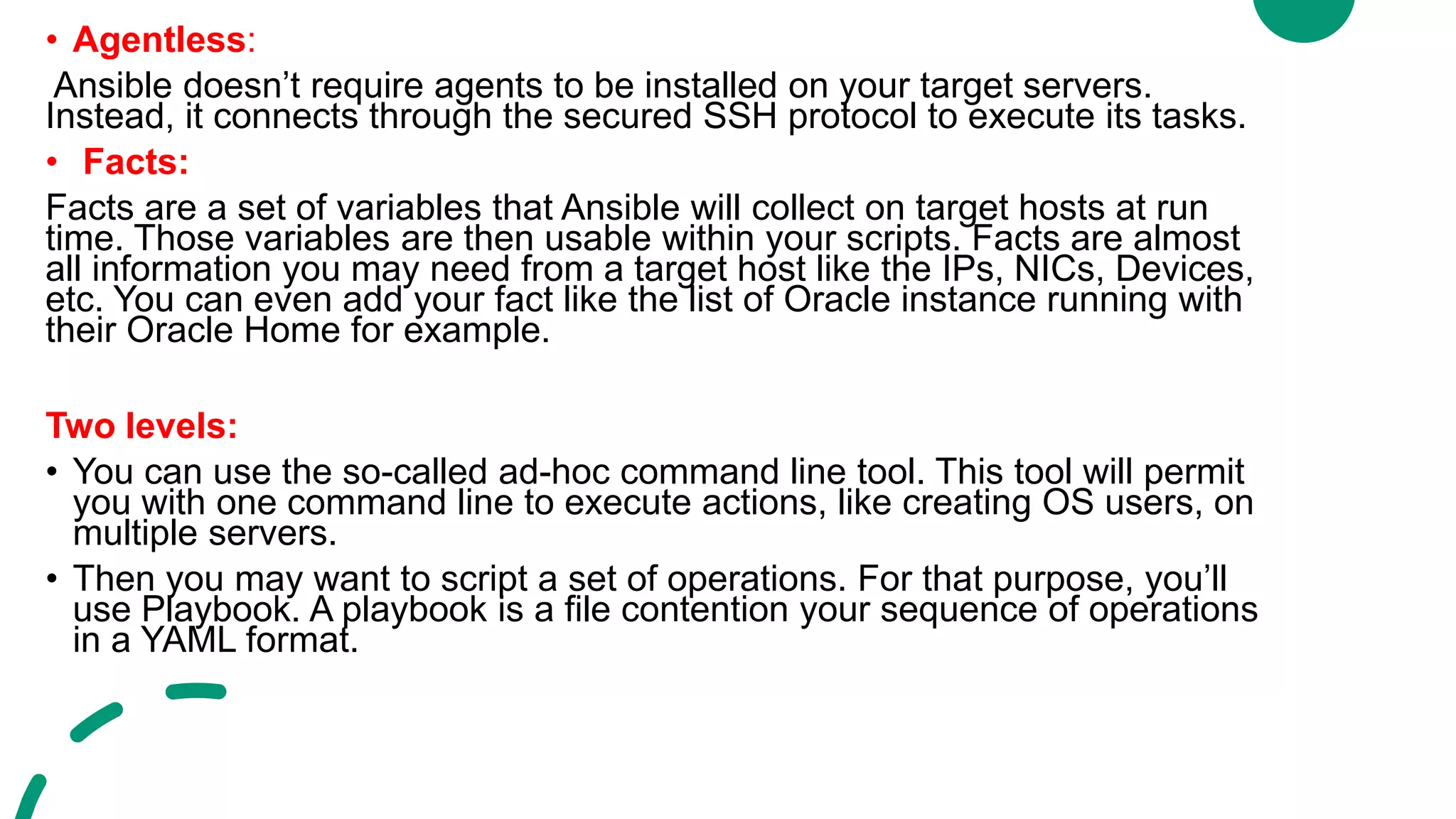
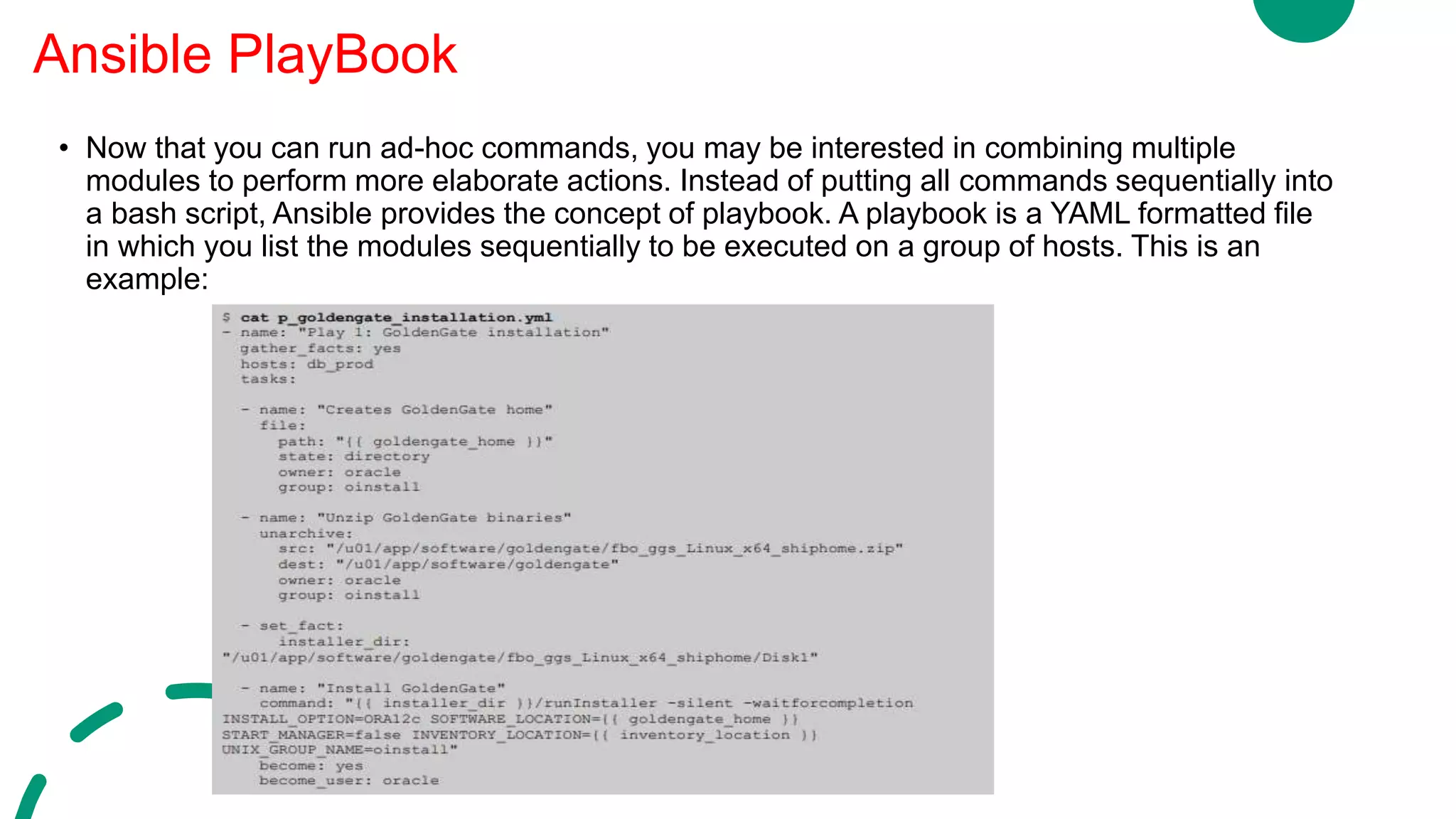
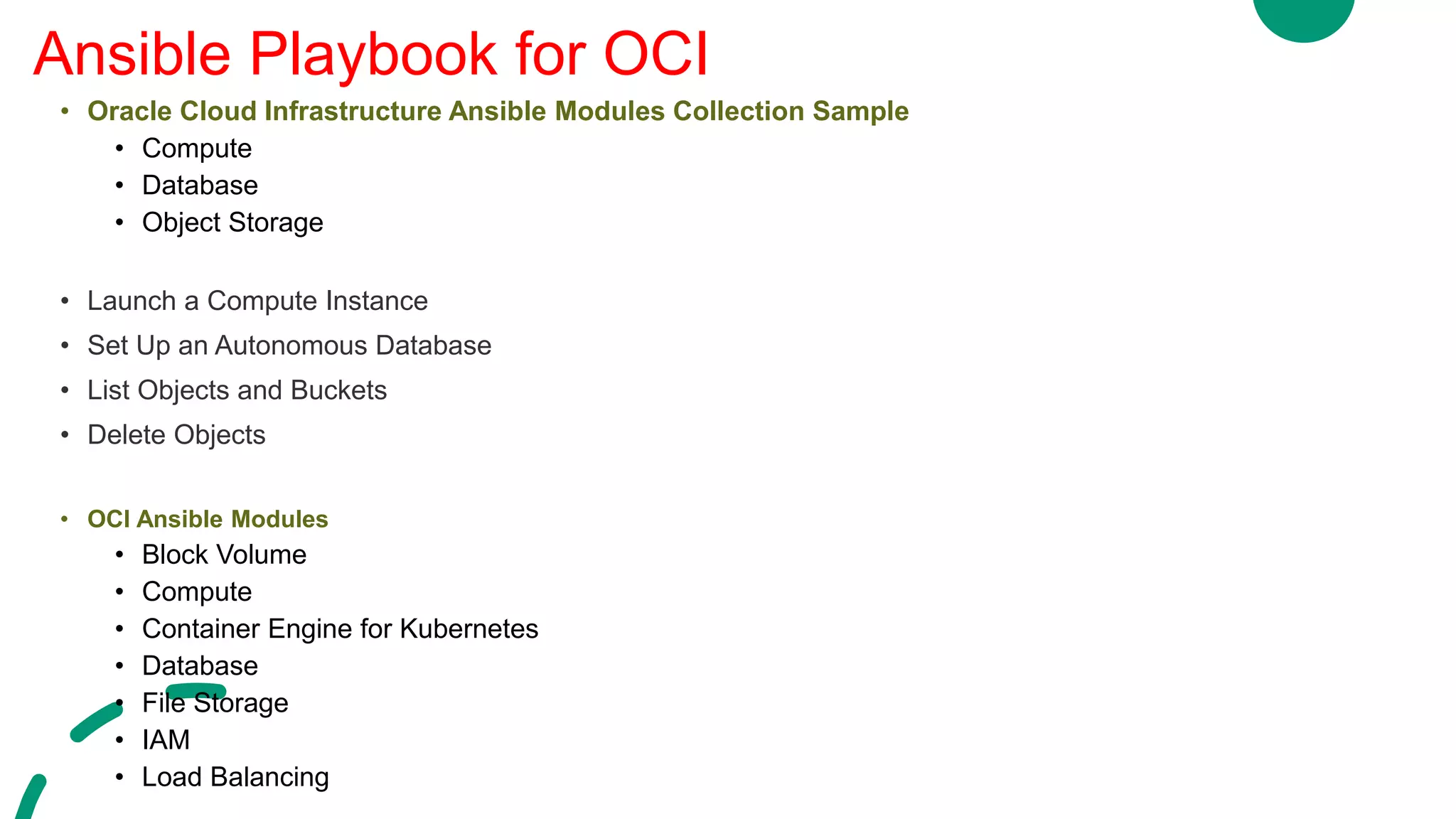
![• Automate a single task on one or more managed nodes. Ad-hoc commands are quick and easy,
but they are not reusable. So why learn about ad-hoc commands first? Ad-hoc commands
demonstrate the simplicity and power of Ansible.
• Ad-hoc commands are great for tasks you repeat rarely. For example, if you want to power off
all the machines in your lab for Christmas vacation, you could execute a quick one-liner in
Ansible without writing a playbook. An ad-hoc command looks like this:
• $ ansible [pattern] -m [module] -a "[module options]“
• Ad-hoc tasks can be used to reboot servers, copy files, manage packages and users, and much
more. You can use any Ansible module in an ad-hoc task
•
Ansible ad-Hoc command line tool
Ansible
Modules](https://image.slidesharecdn.com/devopsfordatabase-200902095137/75/DevOps-for-database-17-2048.jpg)

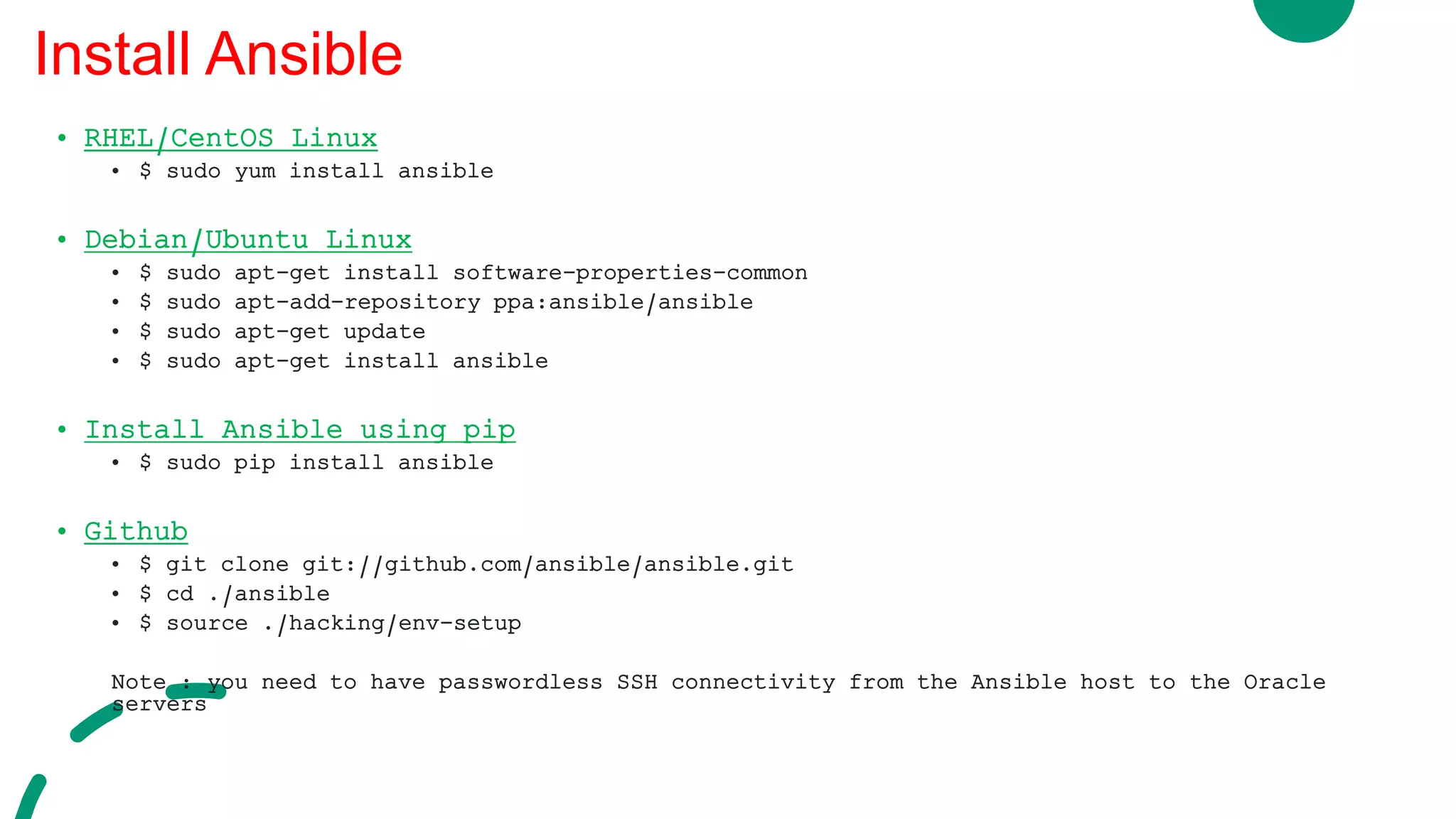
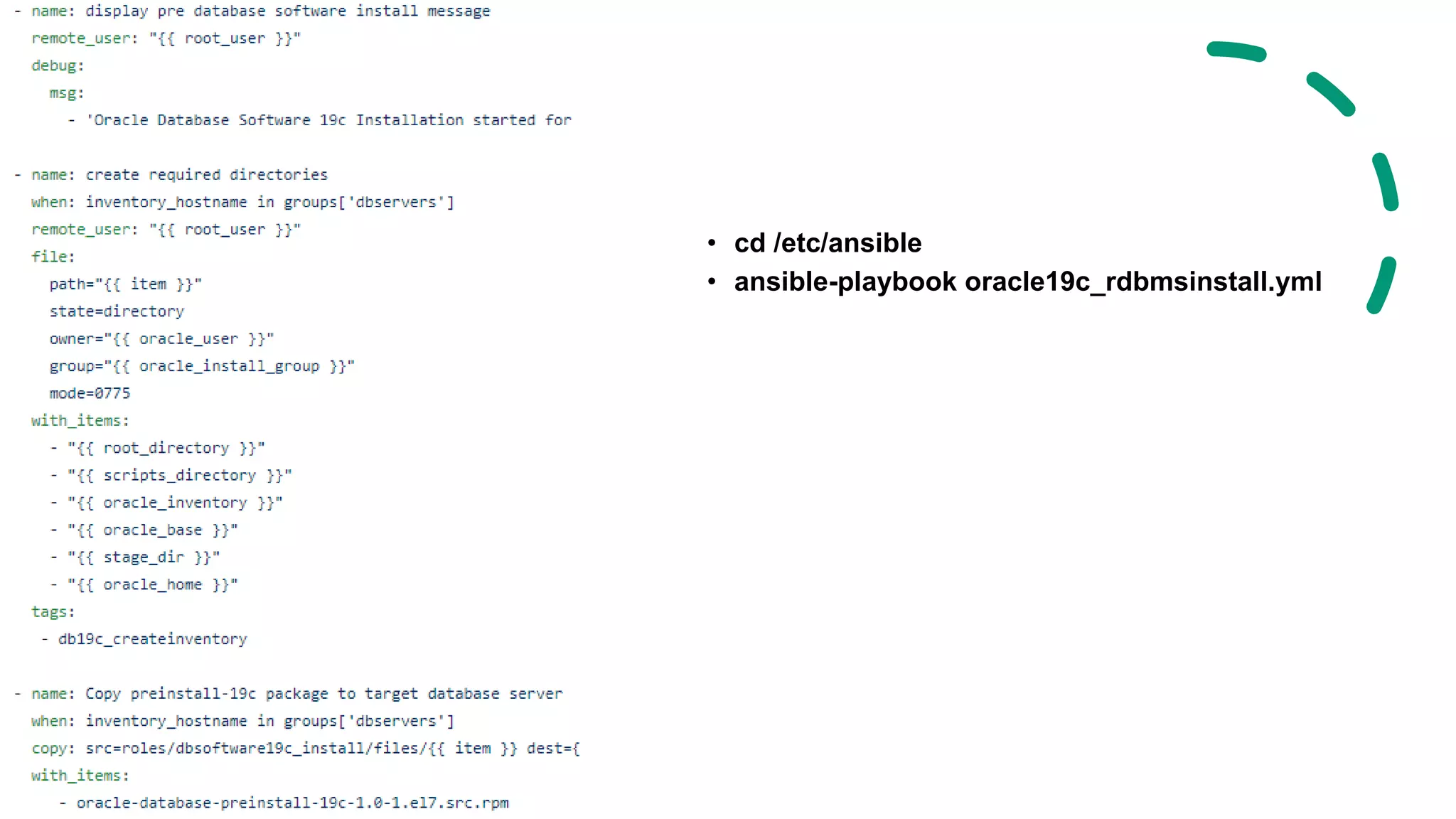
![Use Ansible to Install RDBMS 19c
Control Server
Ansible
Python
Managed Server
Server#1
Managed Server
Server#2
/etc/ansible/hosts
[Server#1]
192.168.1.1
[Server#2]
192.168.1.2
[dbservers]
192.168.1.1
192.168.1.2
oracle19c_rdbmsinstall.yml
- hosts: dbservers
user: root
roles: -
- dbsoftware19c_install](https://image.slidesharecdn.com/devopsfordatabase-200902095137/75/DevOps-for-database-20-2048.jpg)


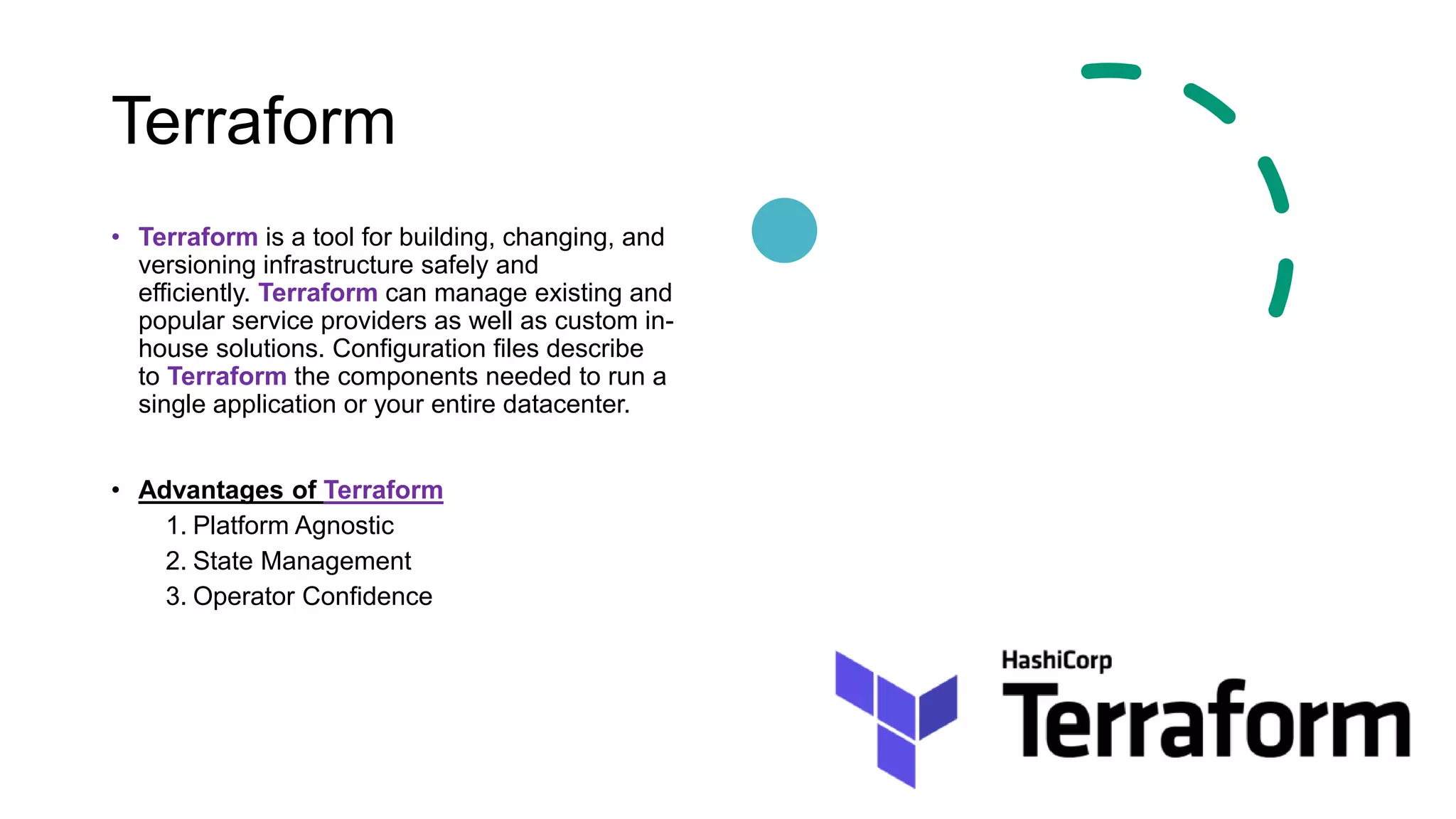
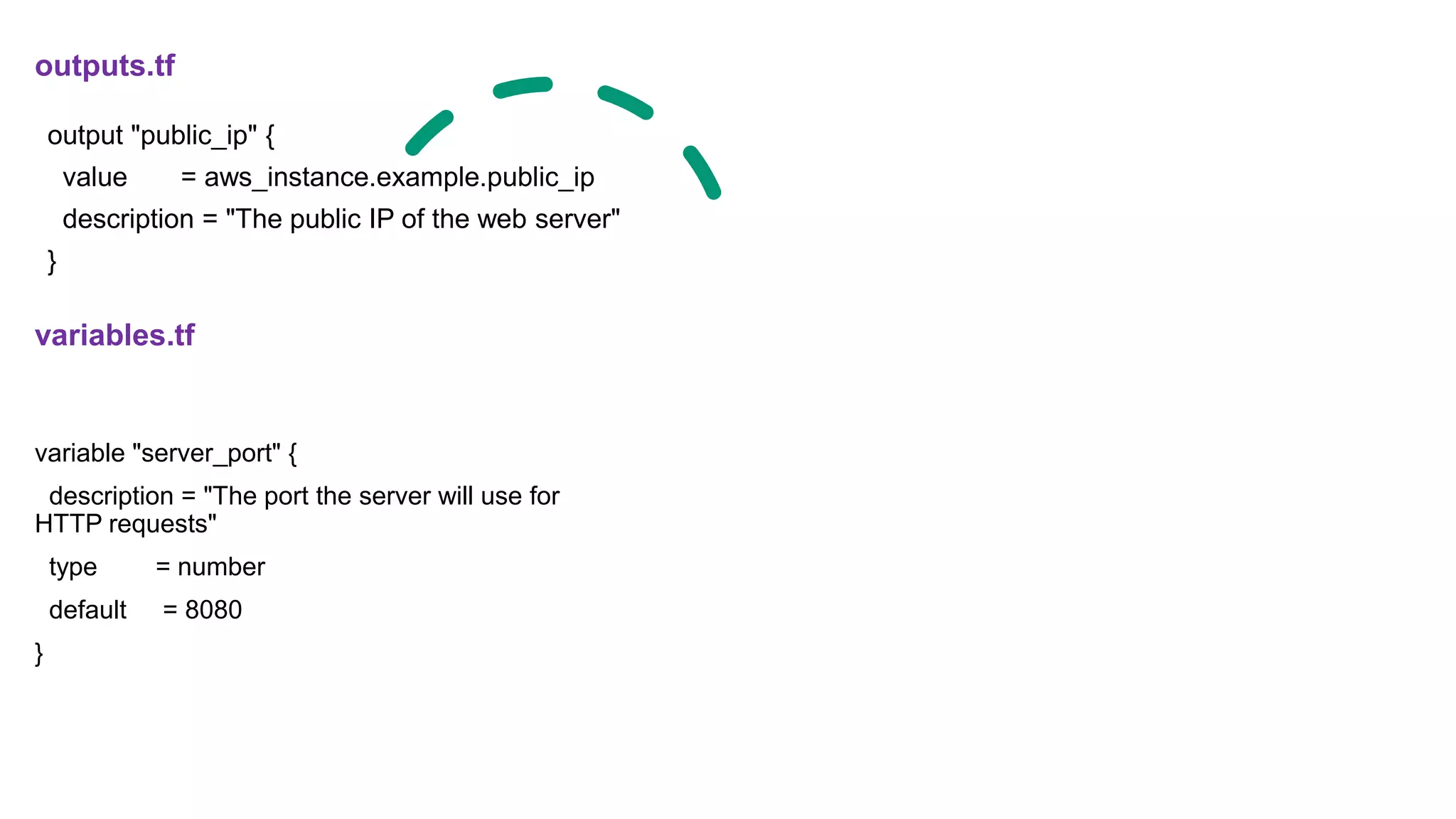
![Example – Single Web Server
main.tf terraform {
required_version = ">= 0.12"
}
# -------------------------------------------------------
# CONFIGURE OUR AWS CONNECTION
# -------------------------------------------------------
provider "aws" {
region = "us-east-2"
}
# ----------------------------
# DEPLOY A SINGLE EC2 INSTANCE
# ----------------------------
resource "aws_instance" "example" {
# Ubuntu Server 18.04 LTS (HVM), SSD Volume Type in
us-east-2
ami = "ami-0c55b159cbfafe1f0"
instance_type = "t2.micro"
vpc_security_group_ids = [aws_security_group.instance.id]
user_data = <<-EOF
#!/bin/bash
echo "Hello, World" > index.html
nohup busybox httpd -f -p "${var.server_port}" &
EOF
tags = {
Name = "terraform-example"
}
}
# ------------------------------------------------------------
# CREATE THE SECURITY GROUP THAT'S APPLIED TO THE
EC2 INSTANCE
resource "aws_security_group" "instance" {
name = "terraform-example-instance"
# Inbound HTTP from anywhere
ingress {
from_port = var.server_port
to_port = var.server_port
protocol = "tcp"
cidr_blocks = ["0.0.0.0/0"]
}
}](https://image.slidesharecdn.com/devopsfordatabase-200902095137/75/DevOps-for-database-36-2048.jpg)