Podman is an open source tool for managing OCI containers and container images. It allows users to find, run, build, share and deploy applications using containers. Some key points about Podman include:
- It is daemonless, secure, and designed for Linux containers.
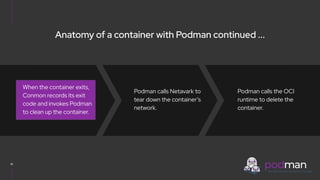
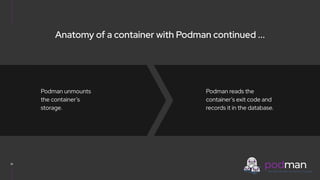
- Podman manages the entire container lifecycle from creation to deletion. It handles mounting, networking, and the container runtime.
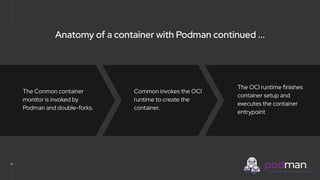
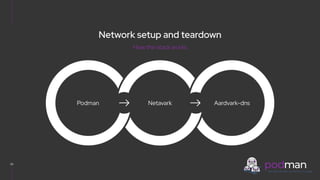
- When running a container, Podman generates an OCI specification, pulls the image if needed, configures networking using Netavark, and uses Conmon to monitor the container process.
- Podman 4 introduced a new network stack based on Netavark and Aardvark-dns