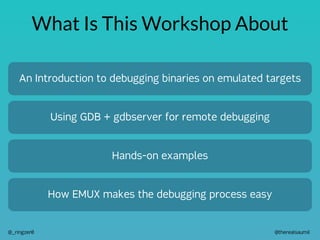
The document outlines a workshop led by Saumil Shah on debugging binaries using the emux IoT emulation framework. It covers concepts like remote debugging, the functions of a debugger, and utilizes tools like gdb and gef, with practical exercises involving an emulated target binary and attack scripts. Additional resources, including codes and documentation links, are provided for participants to enhance their learning experience.









![@therealsaumil
@_ringzer0
A few GDB/GEF commands
RECONNAISSANCE
vmmap [GEF] Display the process' memory layout
info target Information about the target being debugged (ELF binary)
info sharedlibrary Shared Libraries that are loaded with the binary
info functions List of functions that belong to the target binary
PROCESS EXECUTION
break Set a breakpoint
continue Resume process execution
rbreak Set multiple breakpoints using regular expressions
stepi / nexti Step Into / Next Instruction
CPU AND MEMORY
context [GEF] Better view of registers, stack, code, call stack, etc.
x Examine memory (many variations)
hexdump [GEF] When you want characters and bytes side by side
backtrace Display the call stack
info frame Inspect stack frames
disassemble Disassemble code
printf Formatted printing
LUXURIES
set logging Enable / Disable logging and redirect log output to a file
commands Execute multiple commands in sequence every time a breakpoint is reached](https://image.slidesharecdn.com/debugging-with-emux-back2workshops-2022-220708073557-d000f020/85/Debugging-with-EMUX-RIngzer0-BACK2WORKSHOPS-11-320.jpg)


![@therealsaumil
@_ringzer0
Start EMUX
./run-emux-docker
:
:
[+] Setting up forwarded ports 20080:80,20443:443,28080:8080,24433:4433,9999:9999
[+] mapping port 20080 -> 192.168.100.2:80
[+] mapping port 20443 -> 192.168.100.2:443
[+] mapping port 28080 -> 192.168.100.2:8080
[+] mapping port 24433 -> 192.168.100.2:4433
[+] mapping port 9999 -> 192.168.100.2:9999
___ __ __ _ __ __
/ __| / | | | / / by Saumil Shah | The Exploit Laboratory
| __| |/| | |_| ) ( @therealsaumil | emux.exploitlab.net
___|_| |_____/_/_
[EMUX-DOCKER !] ~$
1. Start the EMUX Docker Container](https://image.slidesharecdn.com/debugging-with-emux-back2workshops-2022-220708073557-d000f020/85/Debugging-with-EMUX-RIngzer0-BACK2WORKSHOPS-14-320.jpg)
![@therealsaumil
@_ringzer0
Launch the target
2. Run launcher and boot into Damn Vulnerable ARM Router
[EMUX-DOCKER !] ~$ launcher](https://image.slidesharecdn.com/debugging-with-emux-back2workshops-2022-220708073557-d000f020/85/Debugging-with-EMUX-RIngzer0-BACK2WORKSHOPS-15-320.jpg)
![@therealsaumil
@_ringzer0
Start Userspace
./emux-docker-shell
[emux-docker !] ~$
3. Open a new terminal window and attach to emux-docker-shell
[emux-docker !] ~$ userspace
4. Run userspace](https://image.slidesharecdn.com/debugging-with-emux-back2workshops-2022-220708073557-d000f020/85/Debugging-with-EMUX-RIngzer0-BACK2WORKSHOPS-16-320.jpg)

![@therealsaumil
@_ringzer0
Start nweb (our target binary)
Entering Damn Vulnerable ARM Router CONSOLE (/bin/sh)
[+] Logging enabled
[+] EMUX Debug log - /home/r0/workspace/logs/emuxdebug.log
[+] QEMU Console log - qemuconsole.log
[+] chroot /emux/DV-ARM/rootfs-arm /.emux/emuxshell
Script started, output log file is '/home/r0/workspace/logs/emuxdebug.log'.
BusyBox v1.23.2 (2021-10-14 18:26:48 IST) built-in shell (ash)
/ # nweb 80 /www/nweb/
6. Manually start the nweb web server from the Busybox prompt
./emux-docker-shell
[emux-docker !] ~$ curl http://192.168.100.2
<h1>Ringzer0 Hackme</h1>
7. Start another emux-docker-shell and test nweb](https://image.slidesharecdn.com/debugging-with-emux-back2workshops-2022-220708073557-d000f020/85/Debugging-with-EMUX-RIngzer0-BACK2WORKSHOPS-18-320.jpg)
![@therealsaumil
@_ringzer0
Grab the attack scripts!
[emux-docker !] ~$ cd workspace
[emux-docker !] ~/workspace$ wget https://saumil.net/tmp/attack1.py
--2022-07-07 14:12:48-- https://saumil.net/tmp/attack1.py
Resolving saumil.net (saumil.net)... 208.113.163.5
Connecting to saumil.net (saumil.net)|208.113.163.5|:443... connected.
HTTP request sent, awaiting response... 200 OK
Length: 535 [text/plain]
Saving to: 'attack1.py'
attack1.py 100%[=======================>] 535 --.-KB/s in 0s
2022-07-07 14:12:50 (58.9 MB/s) - 'attack1.py' saved [535/535]
[emux-docker !] ~/workspace$ chmod +x attack1.py
8. From the emux-docker-shell grab the following attack scripts](https://image.slidesharecdn.com/debugging-with-emux-back2workshops-2022-220708073557-d000f020/85/Debugging-with-EMUX-RIngzer0-BACK2WORKSHOPS-19-320.jpg)



