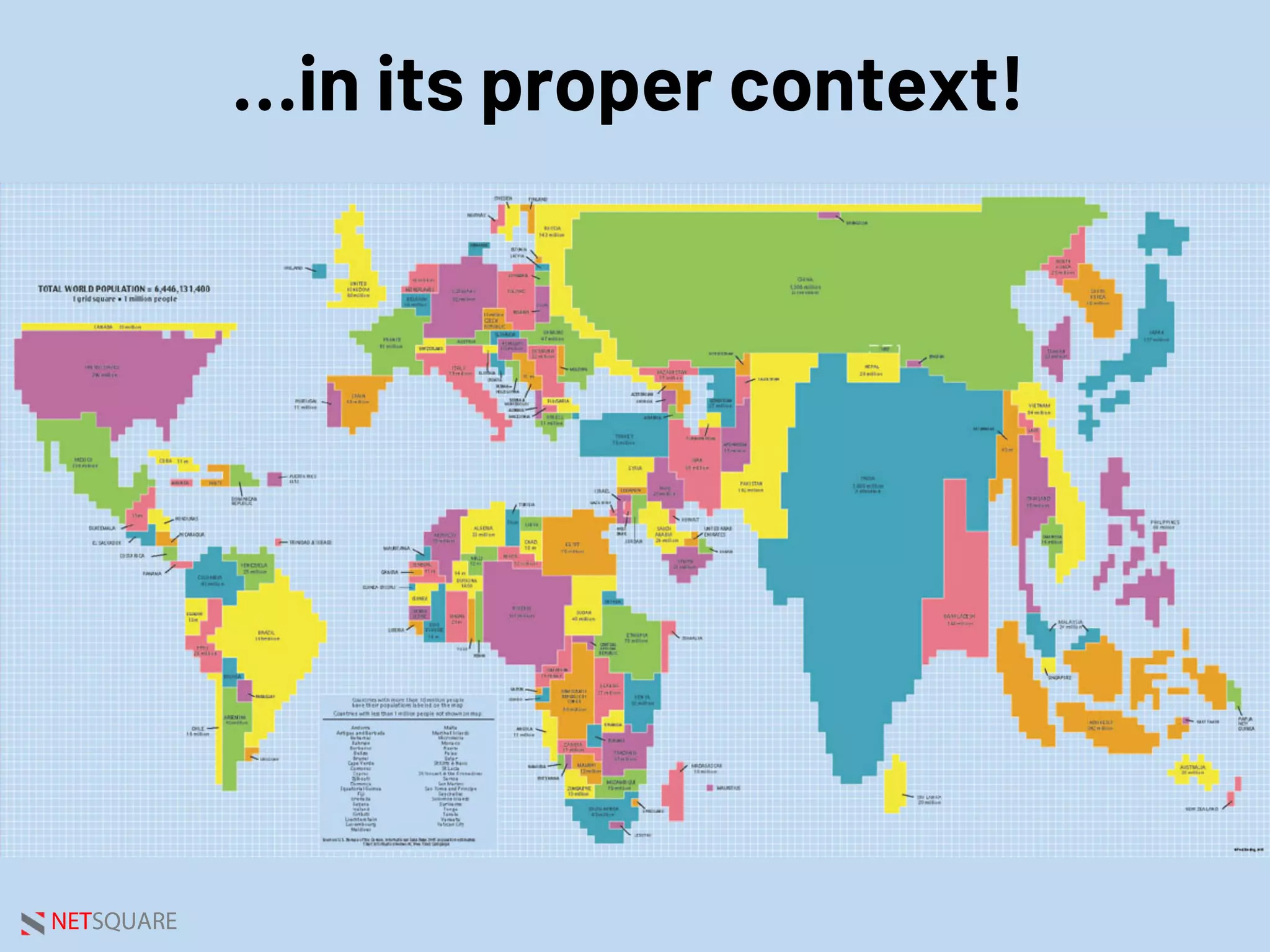
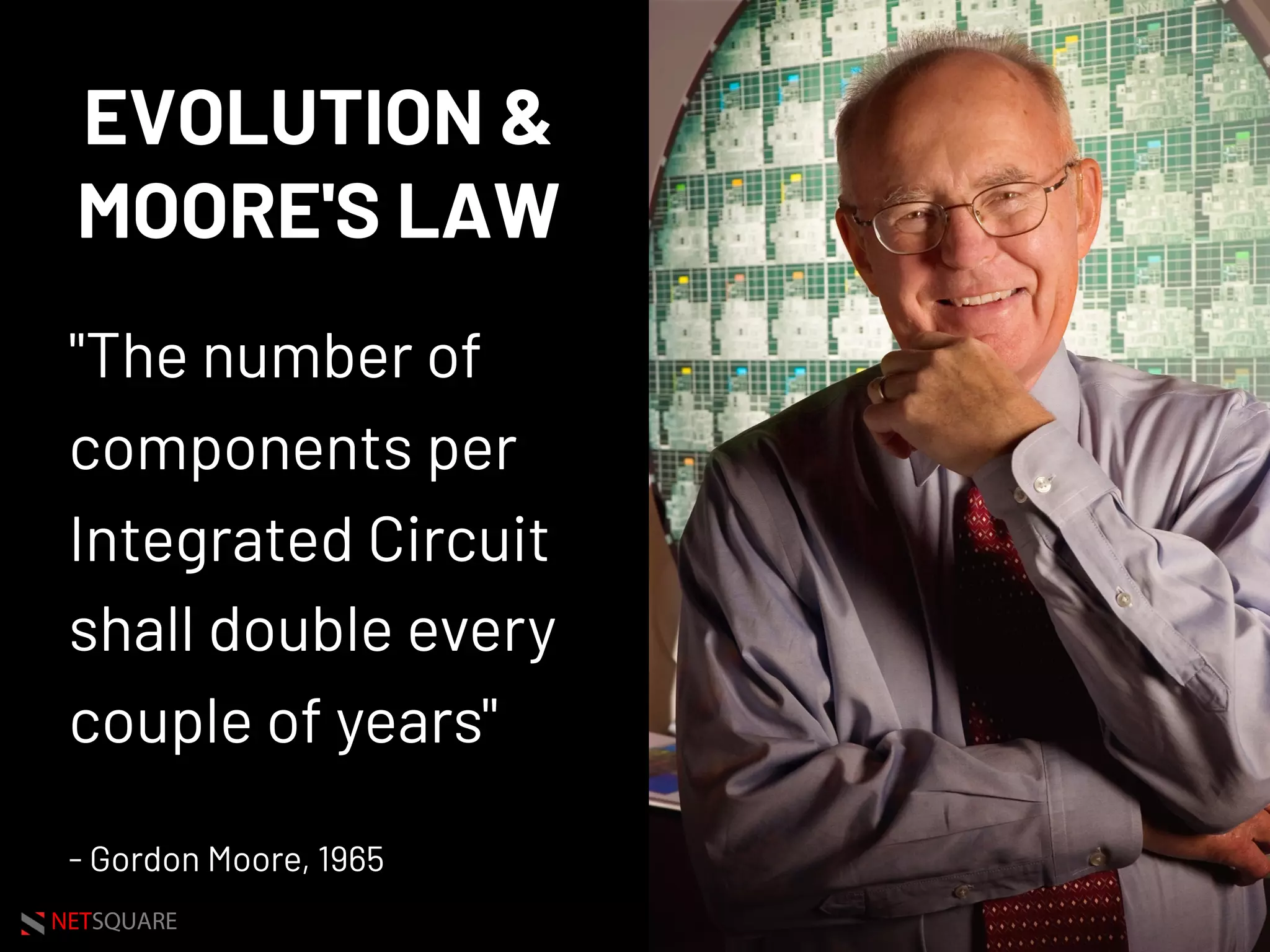
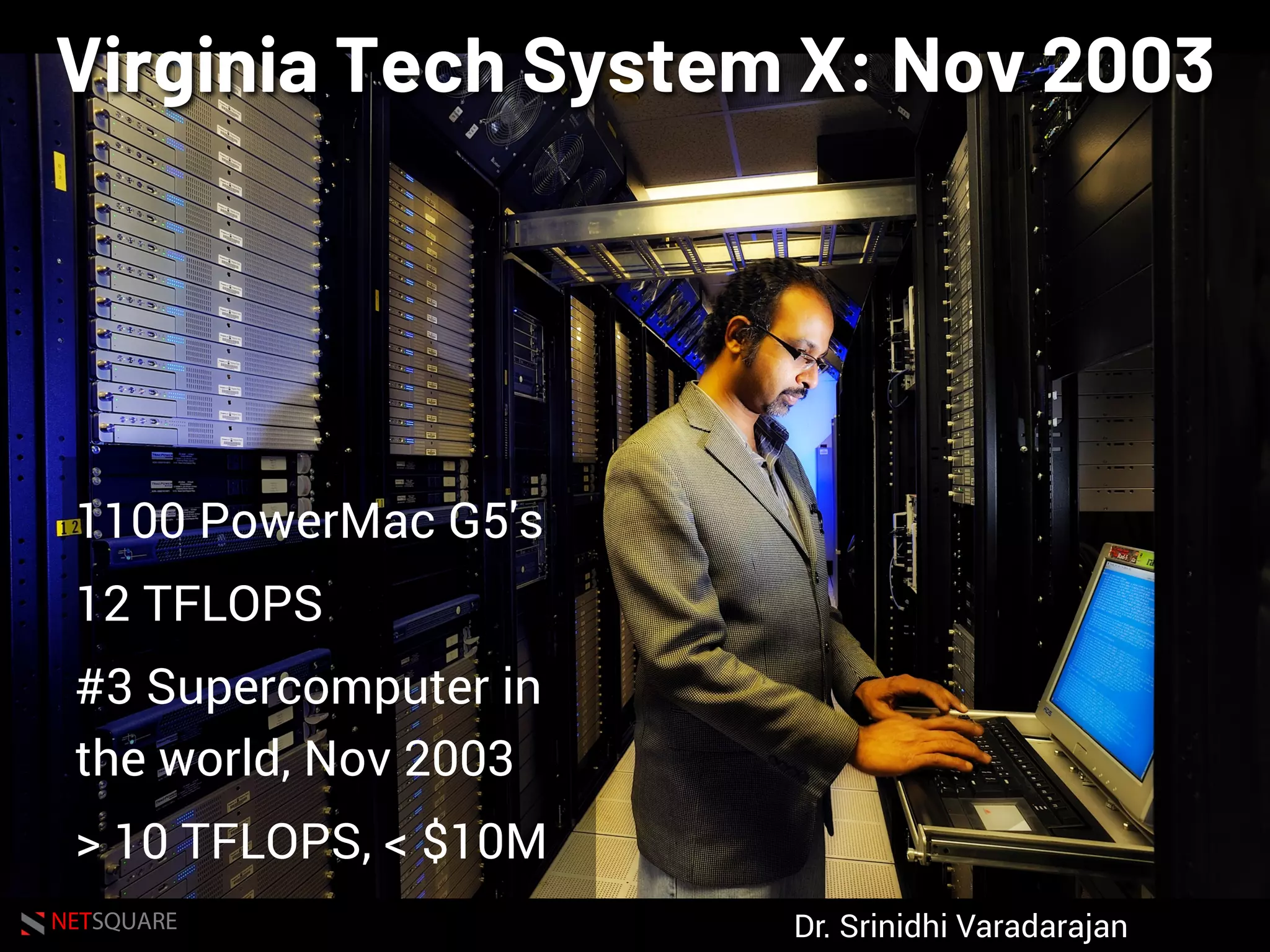
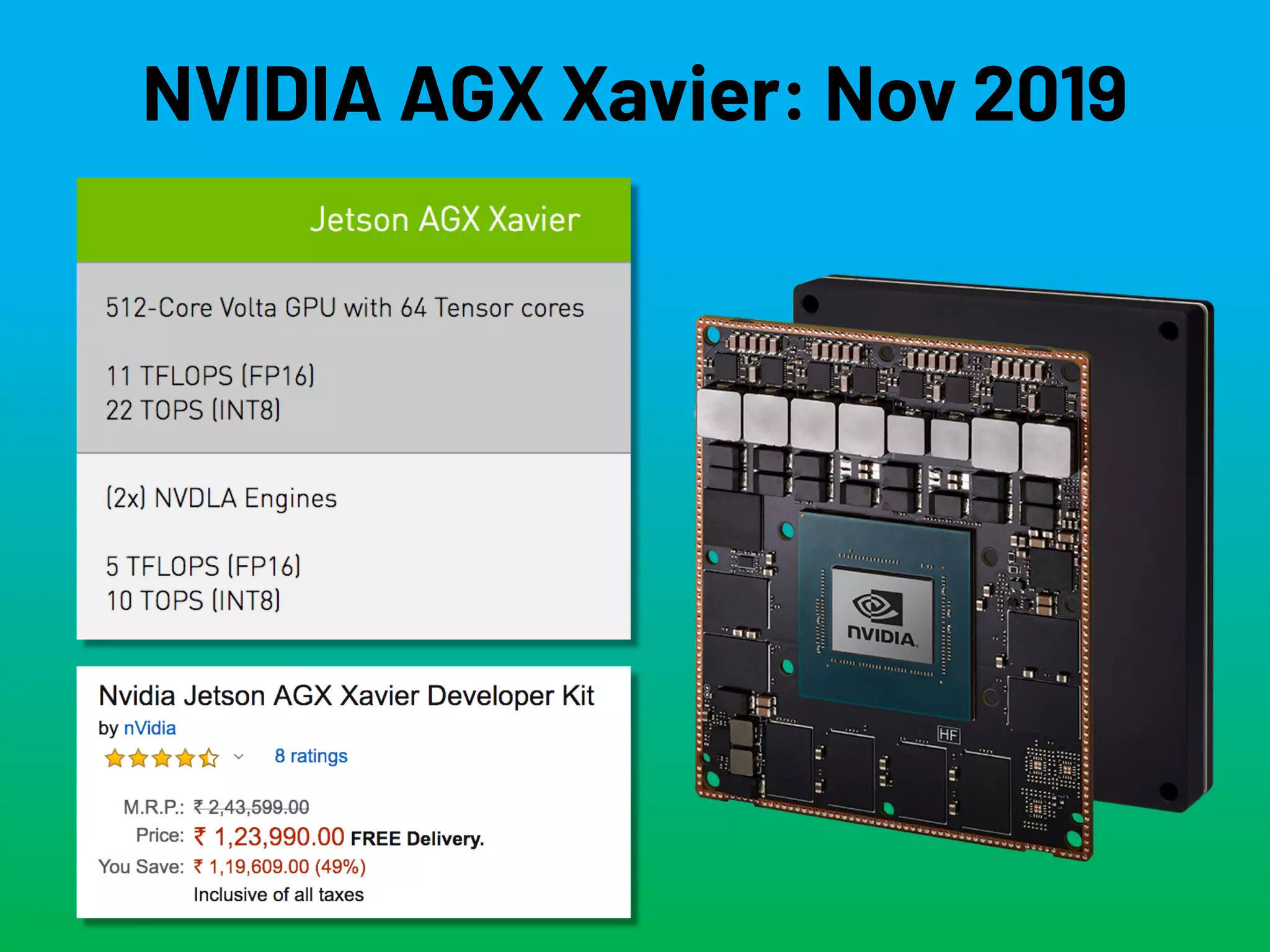
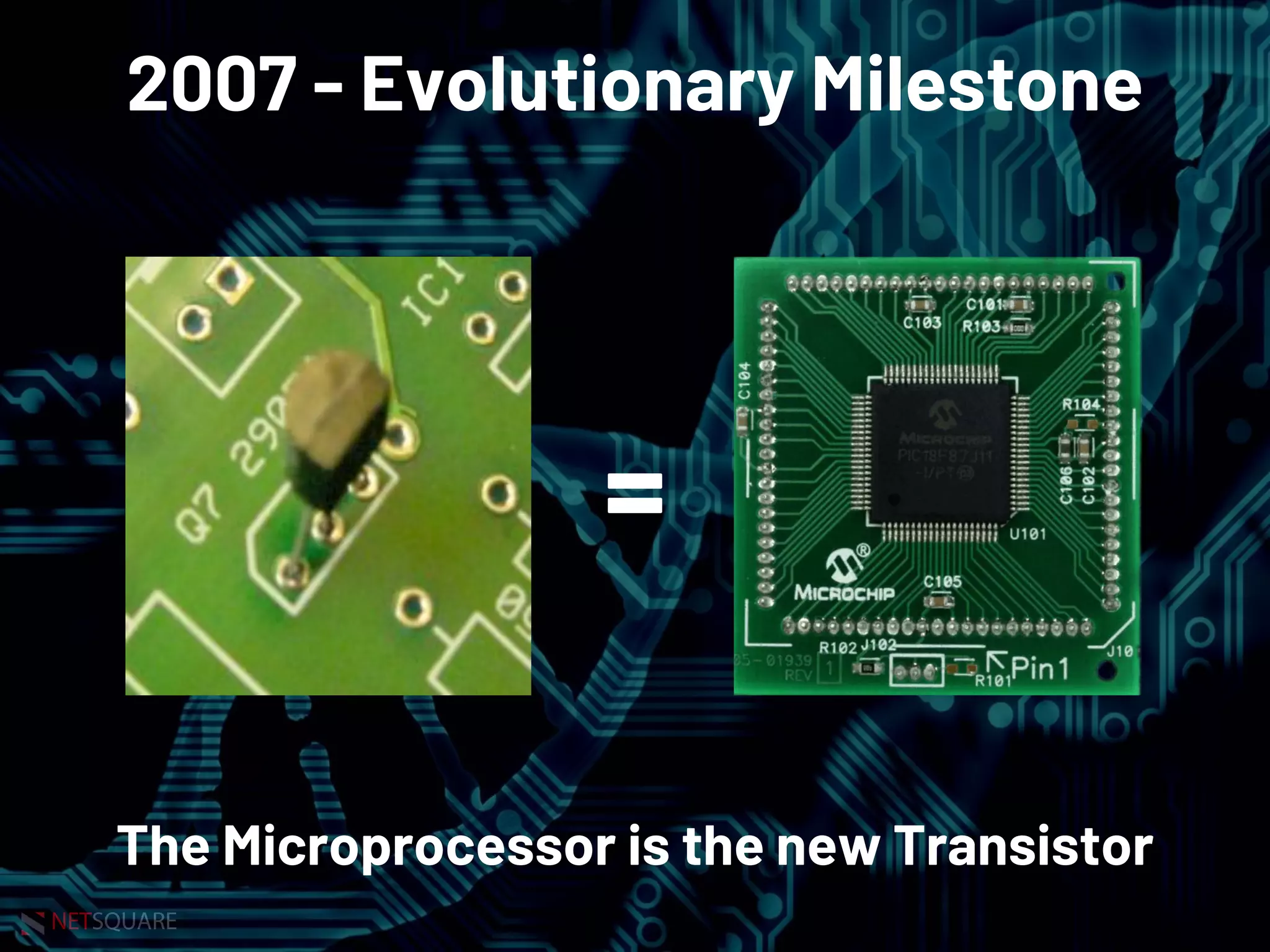
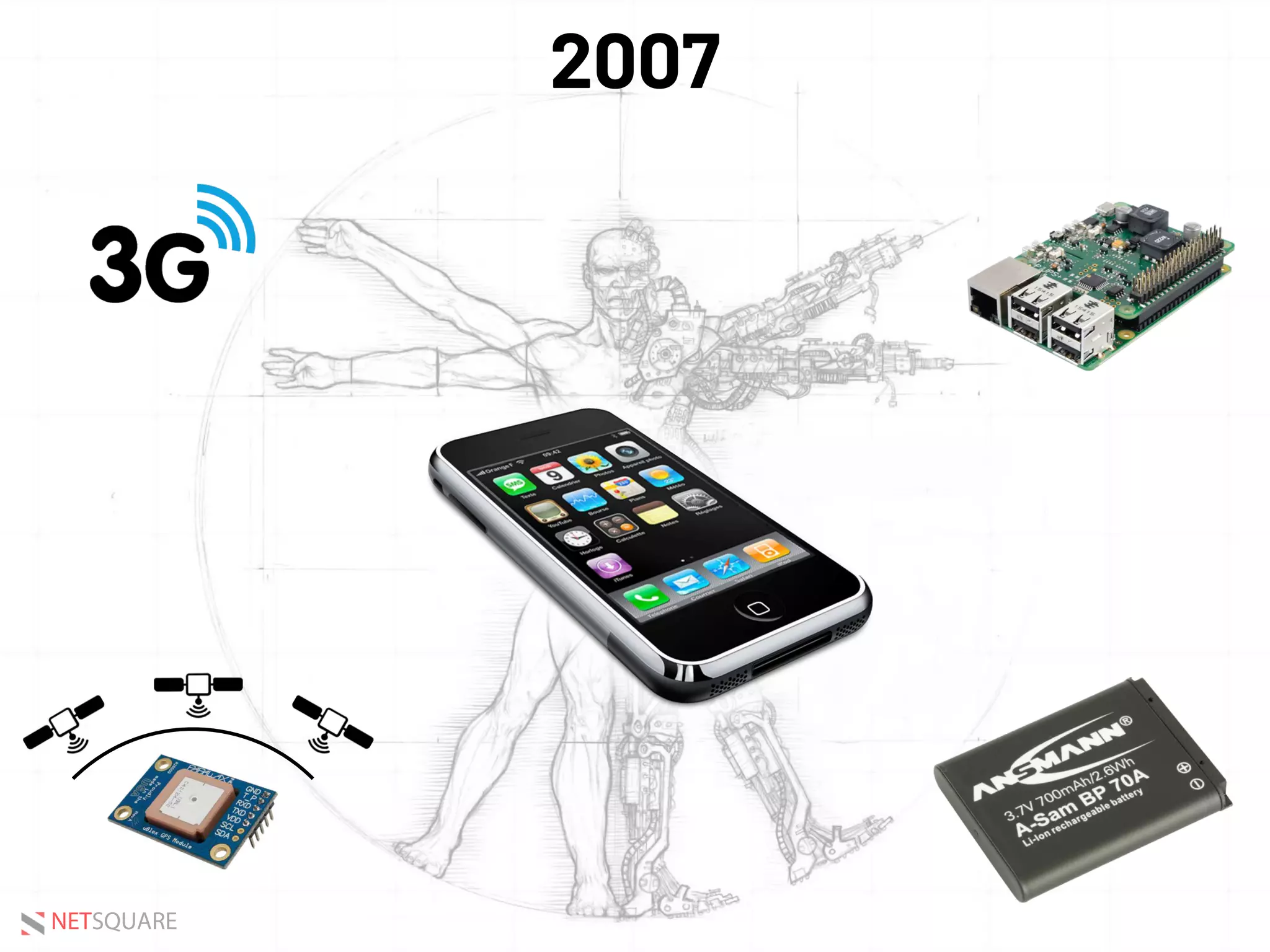
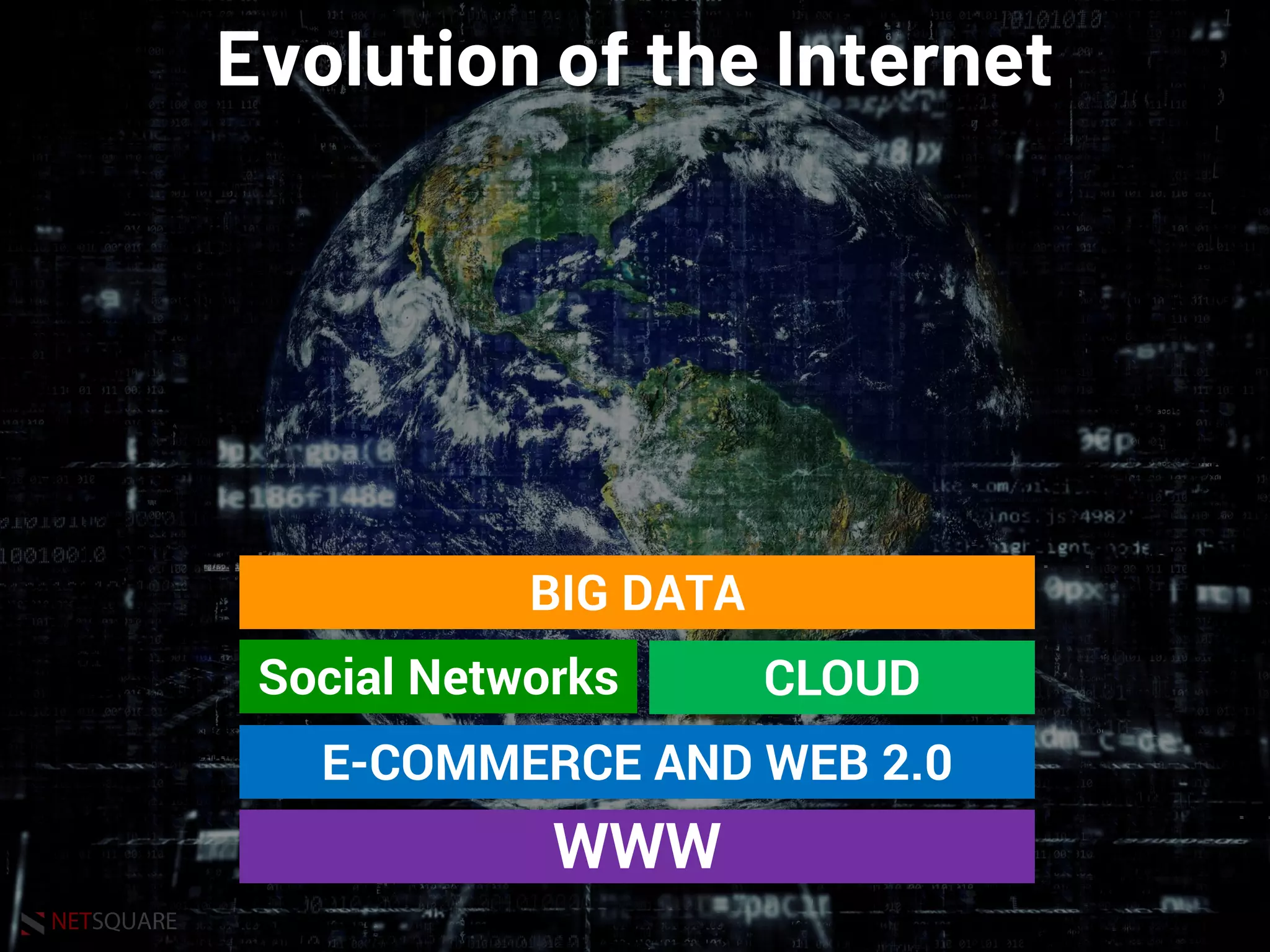
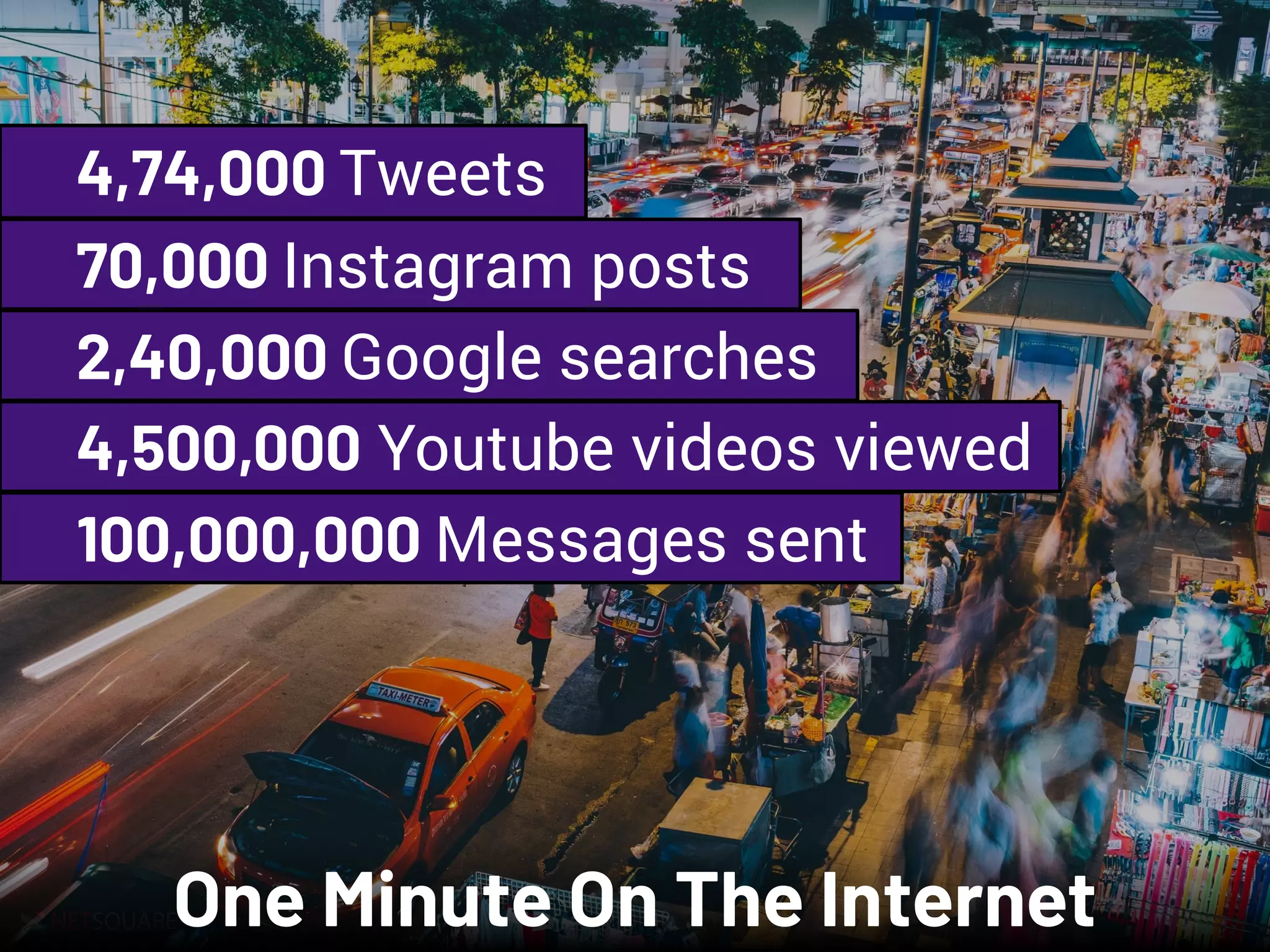
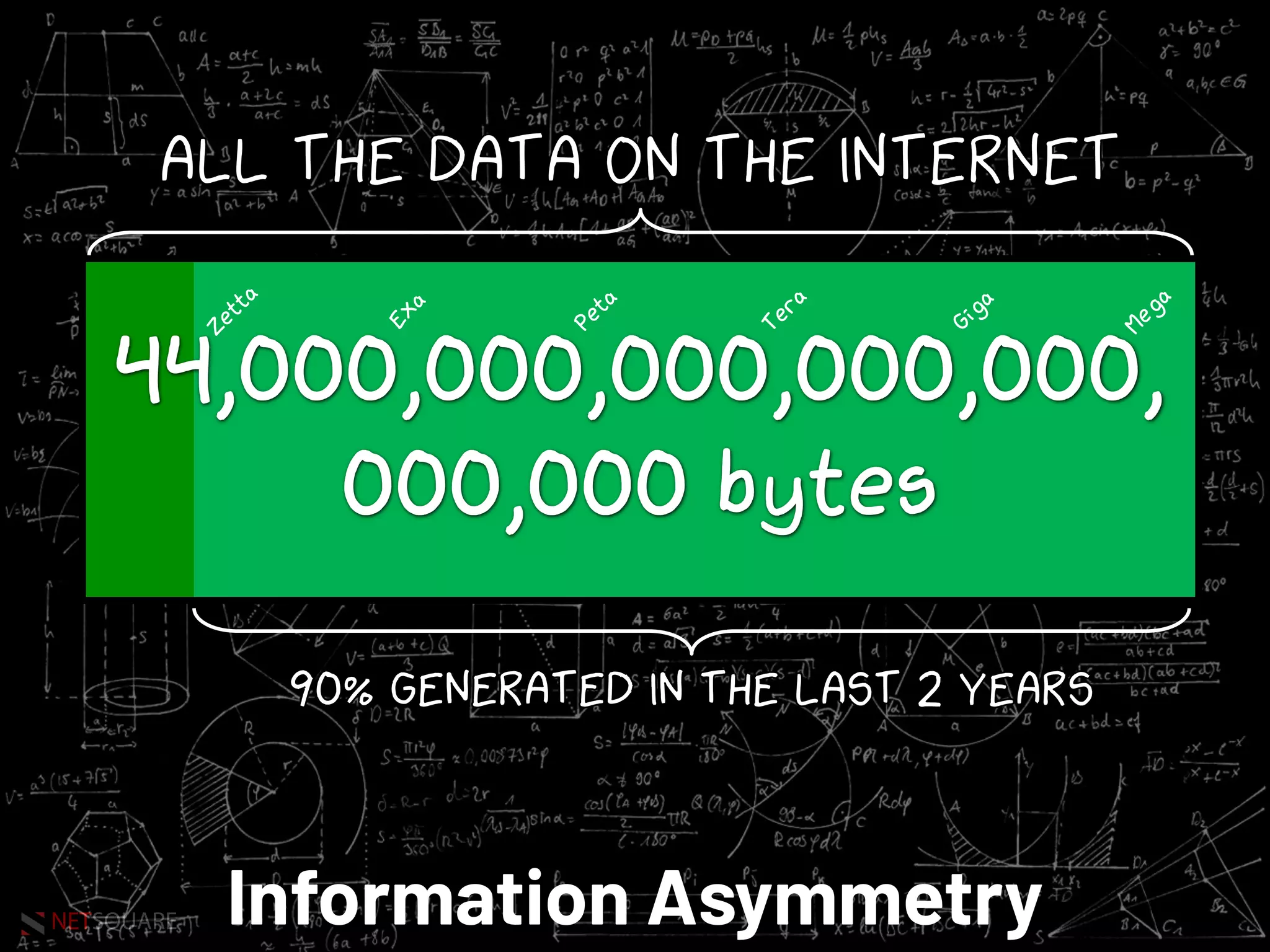
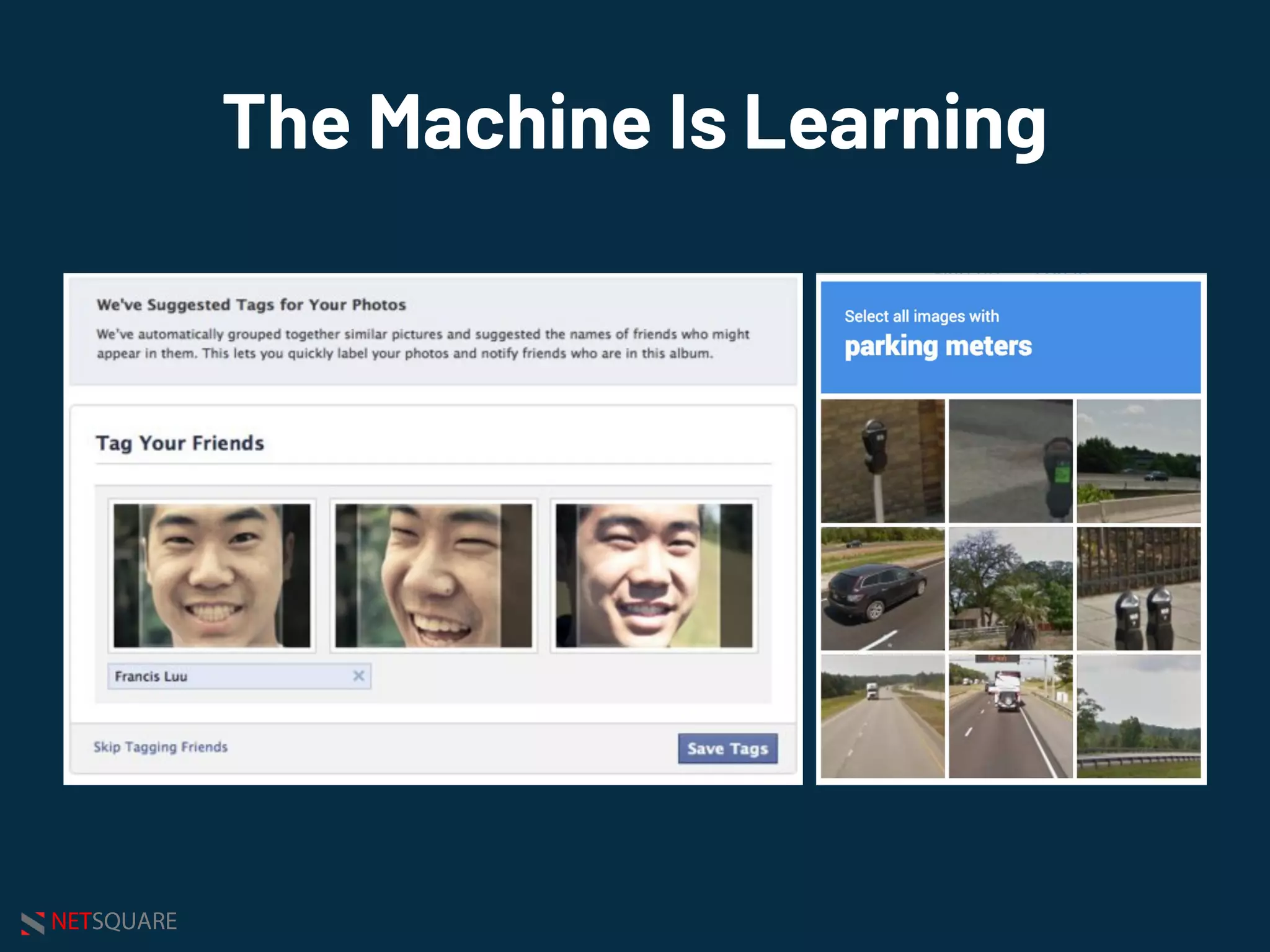
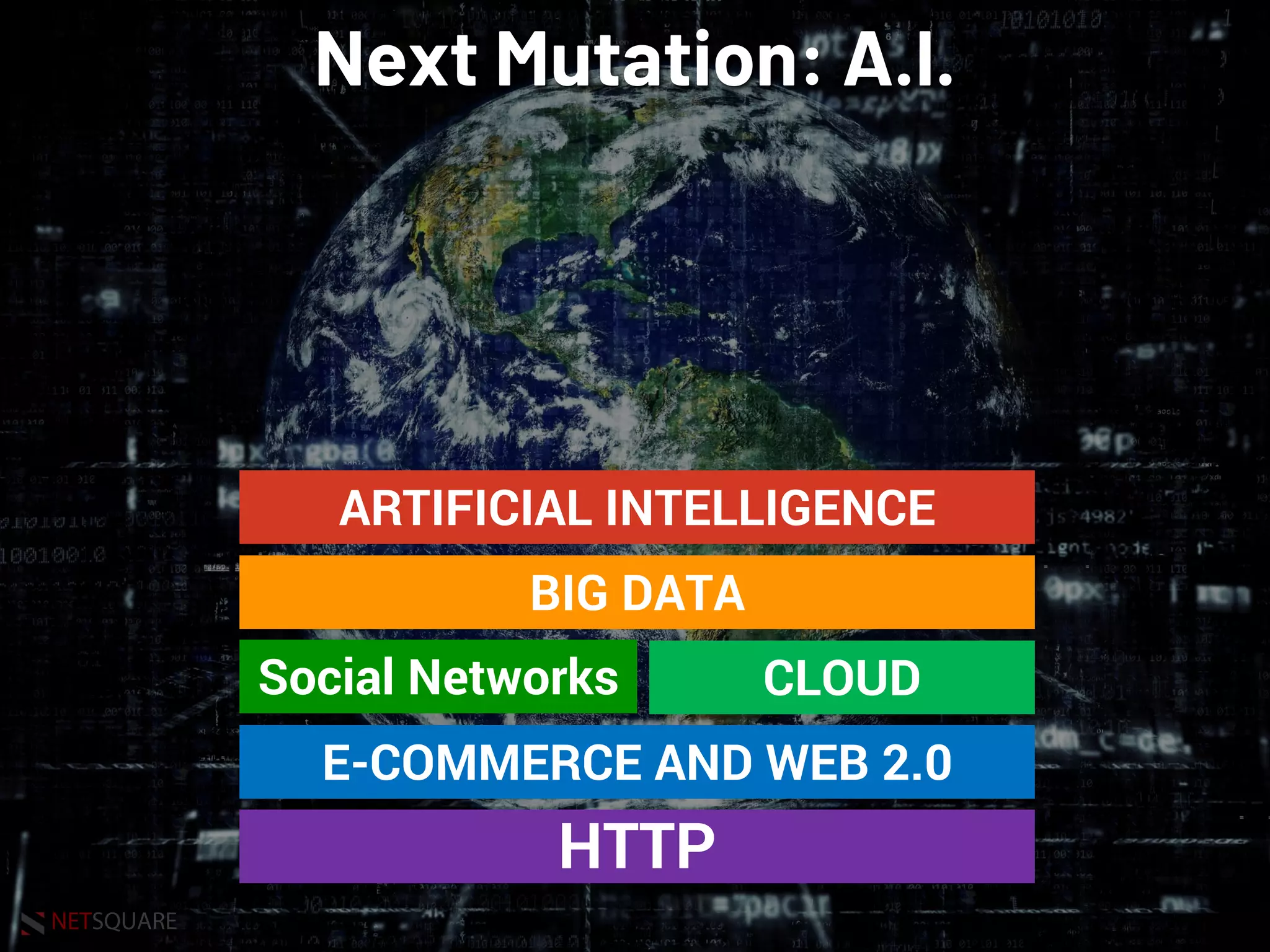
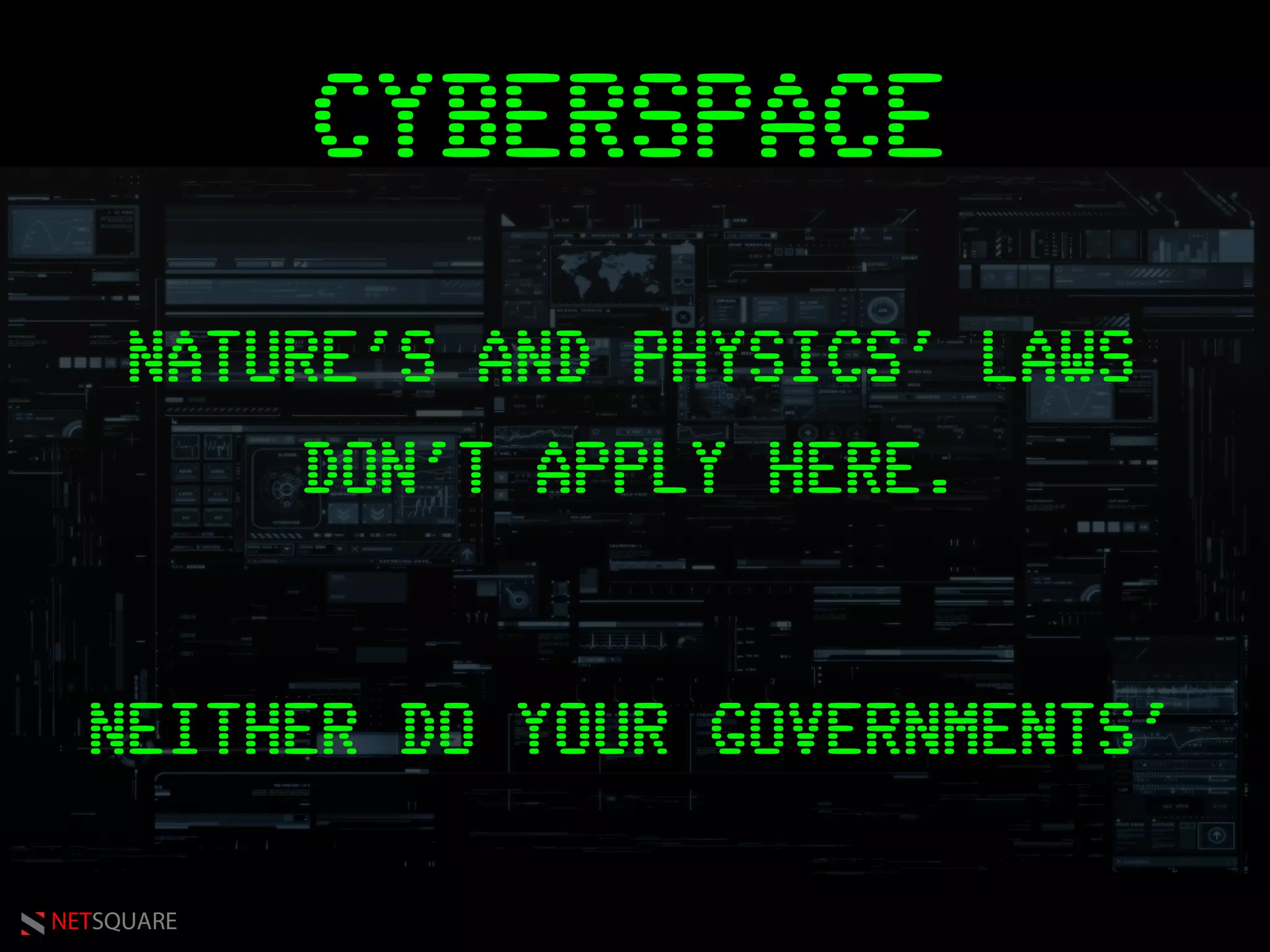
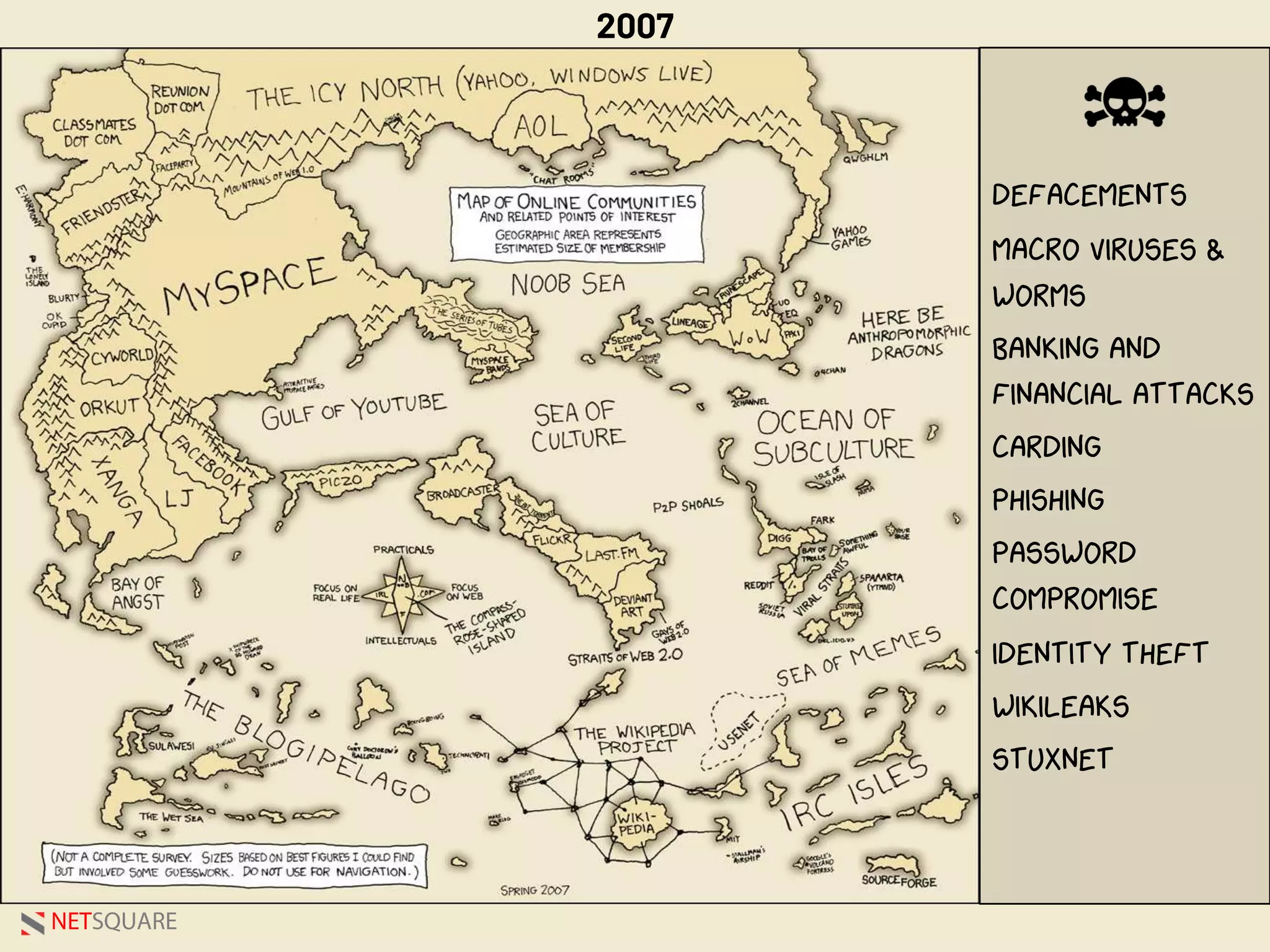
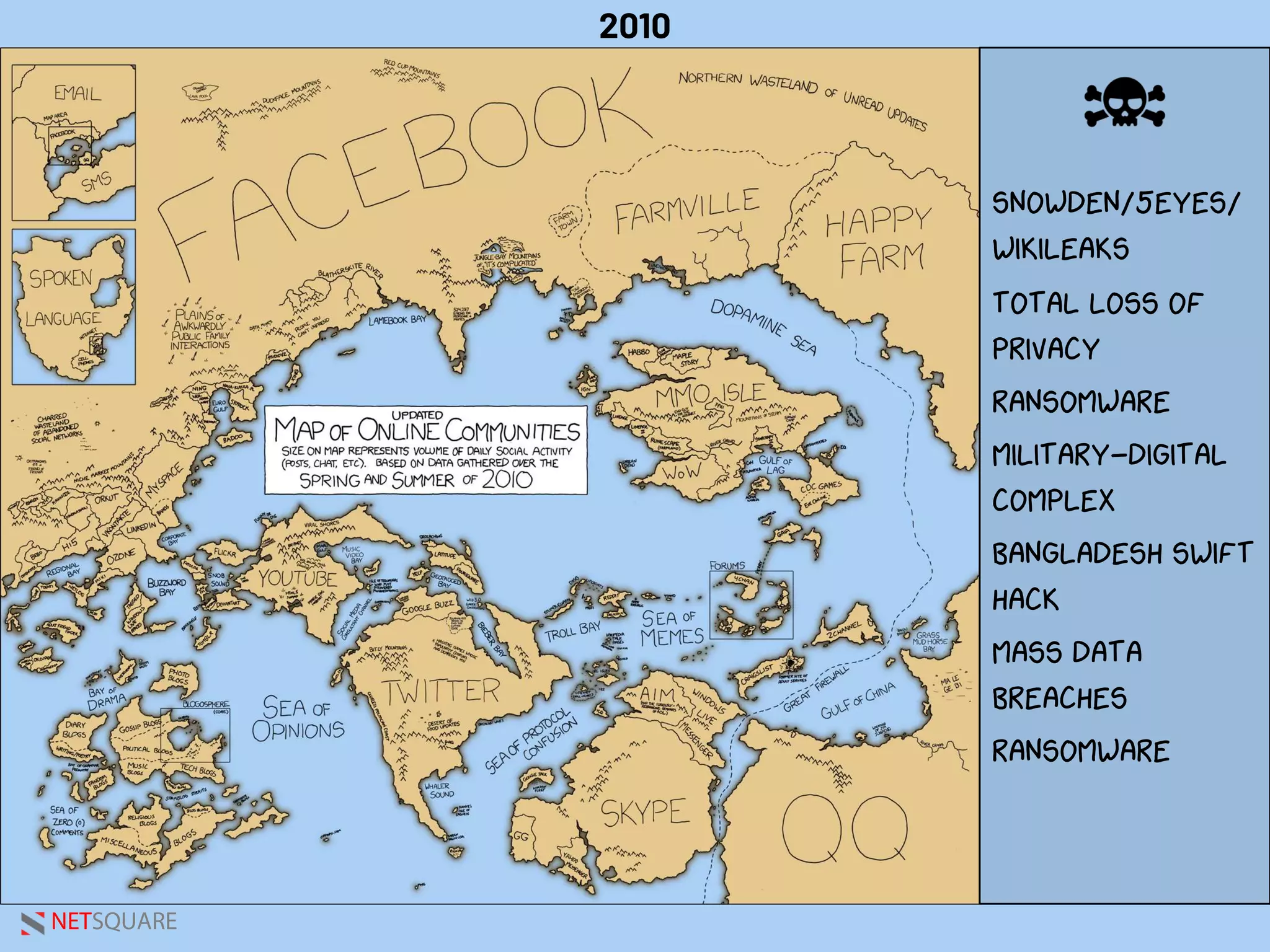
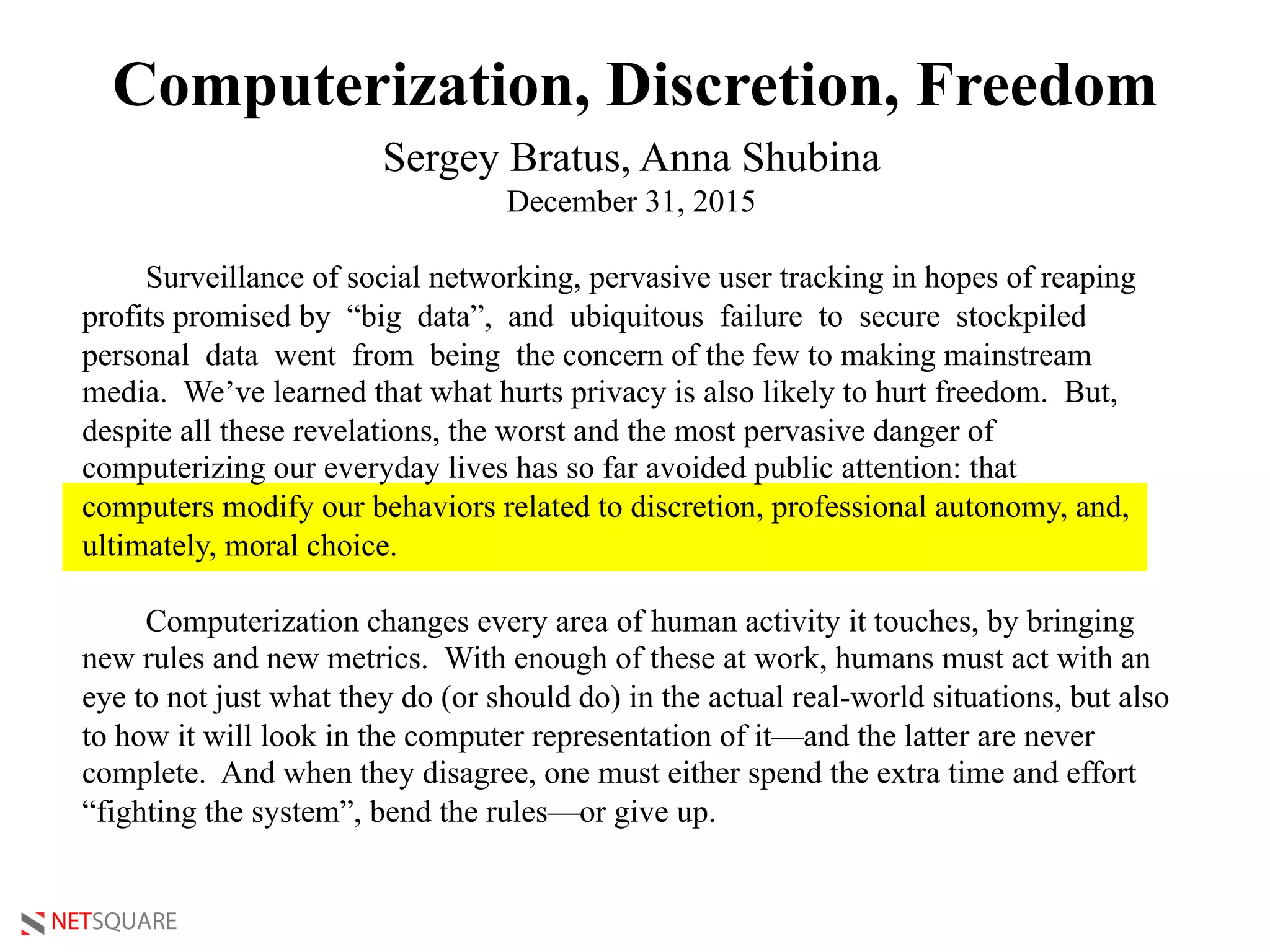
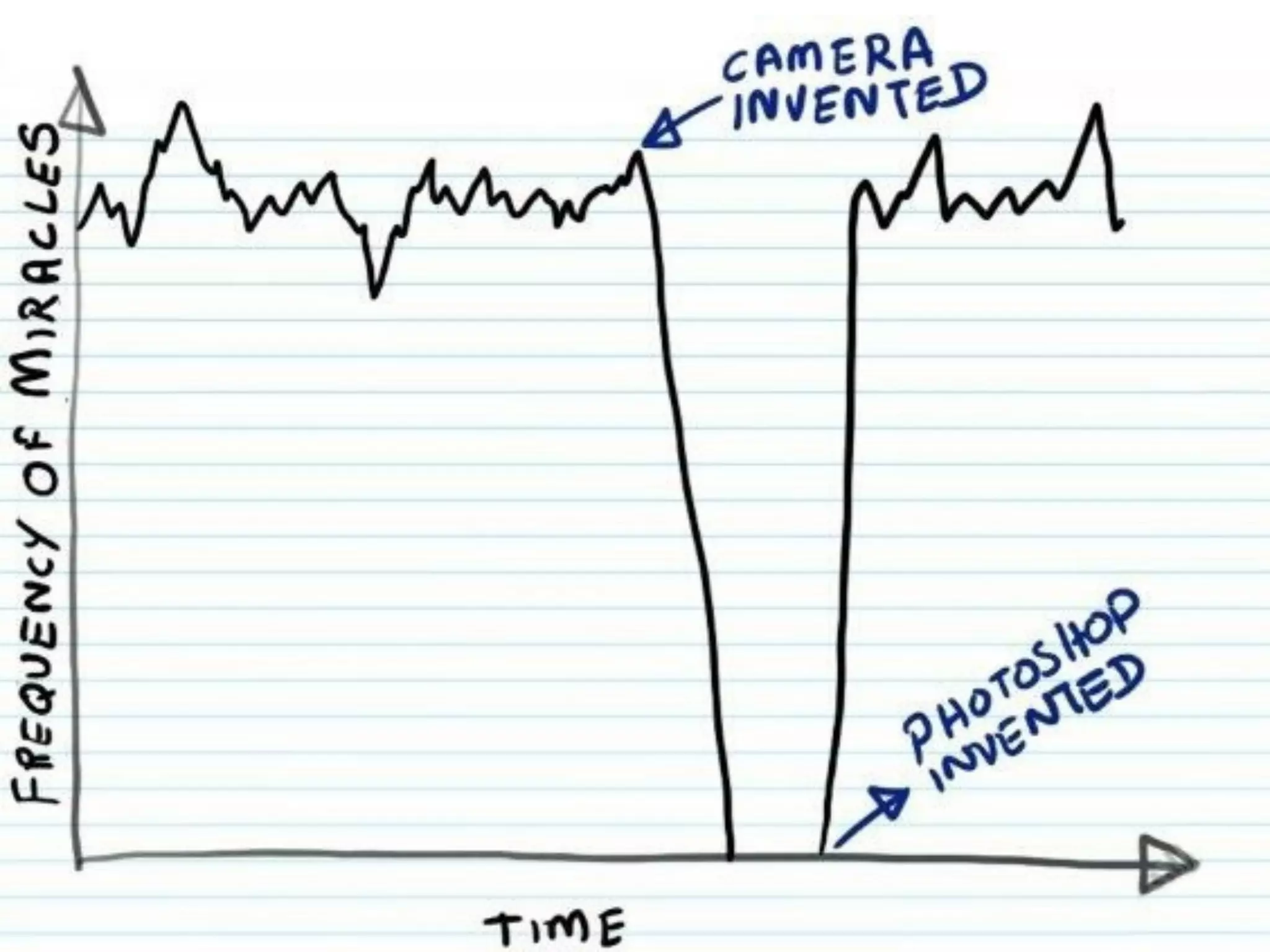
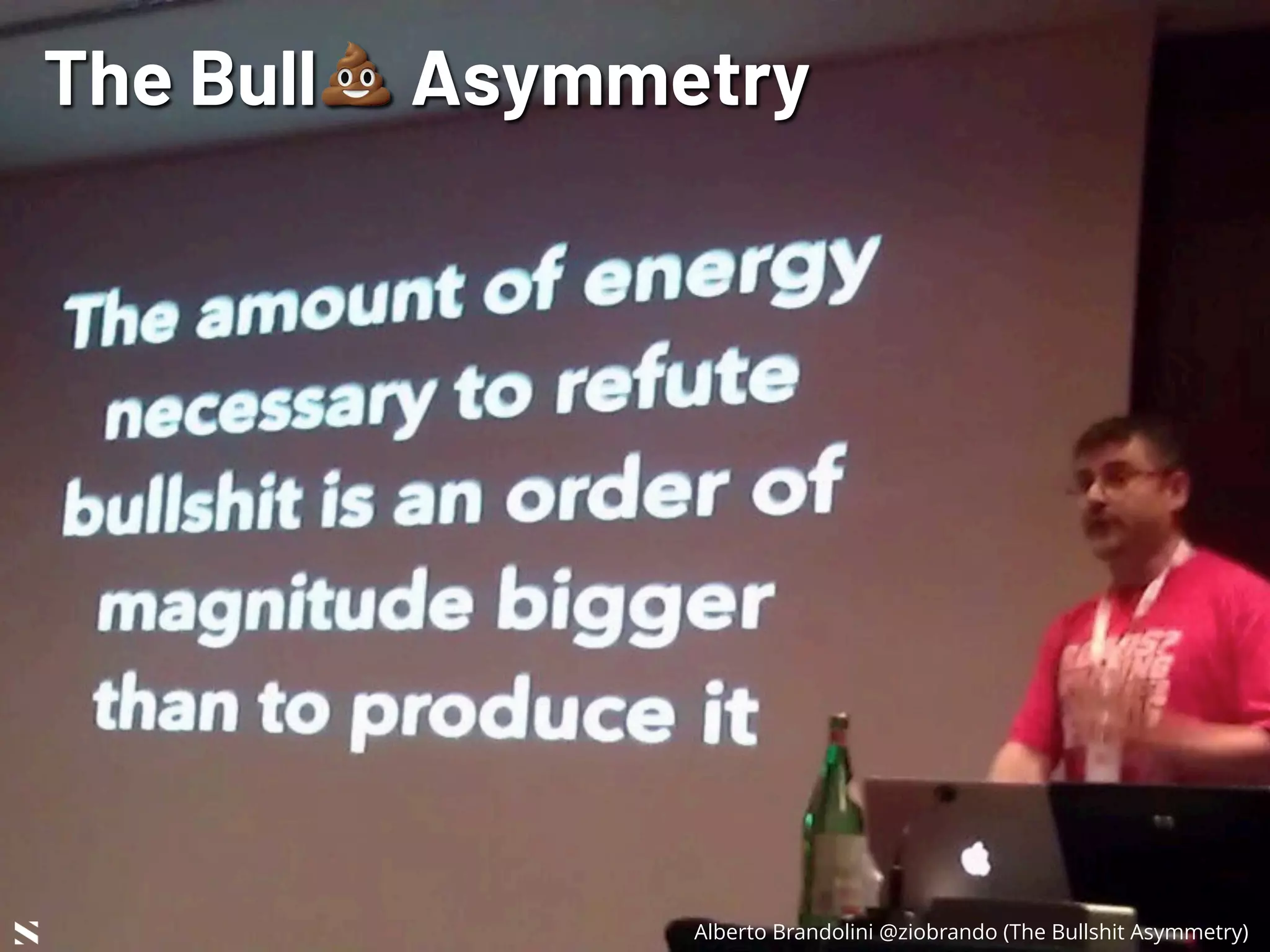
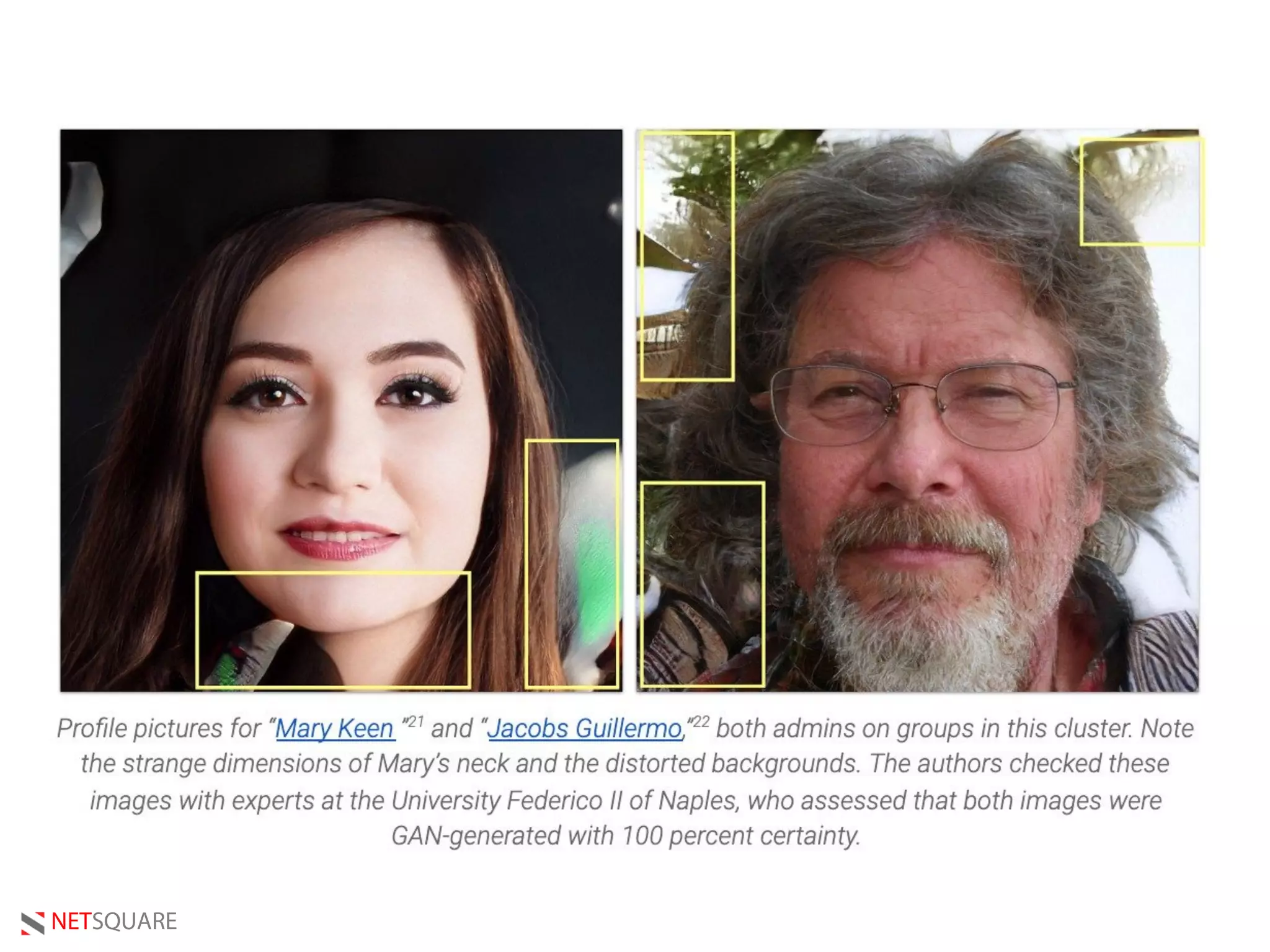
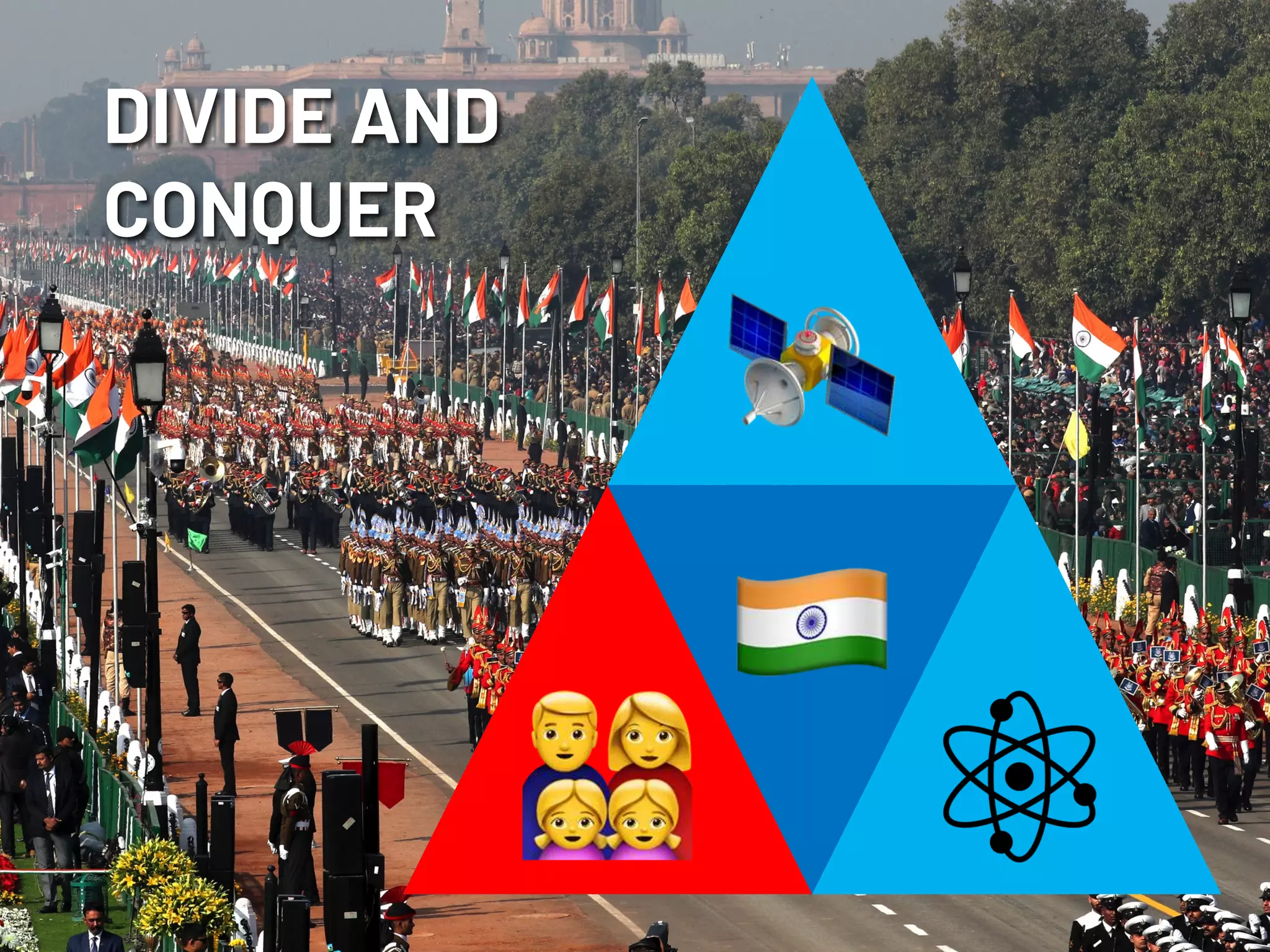
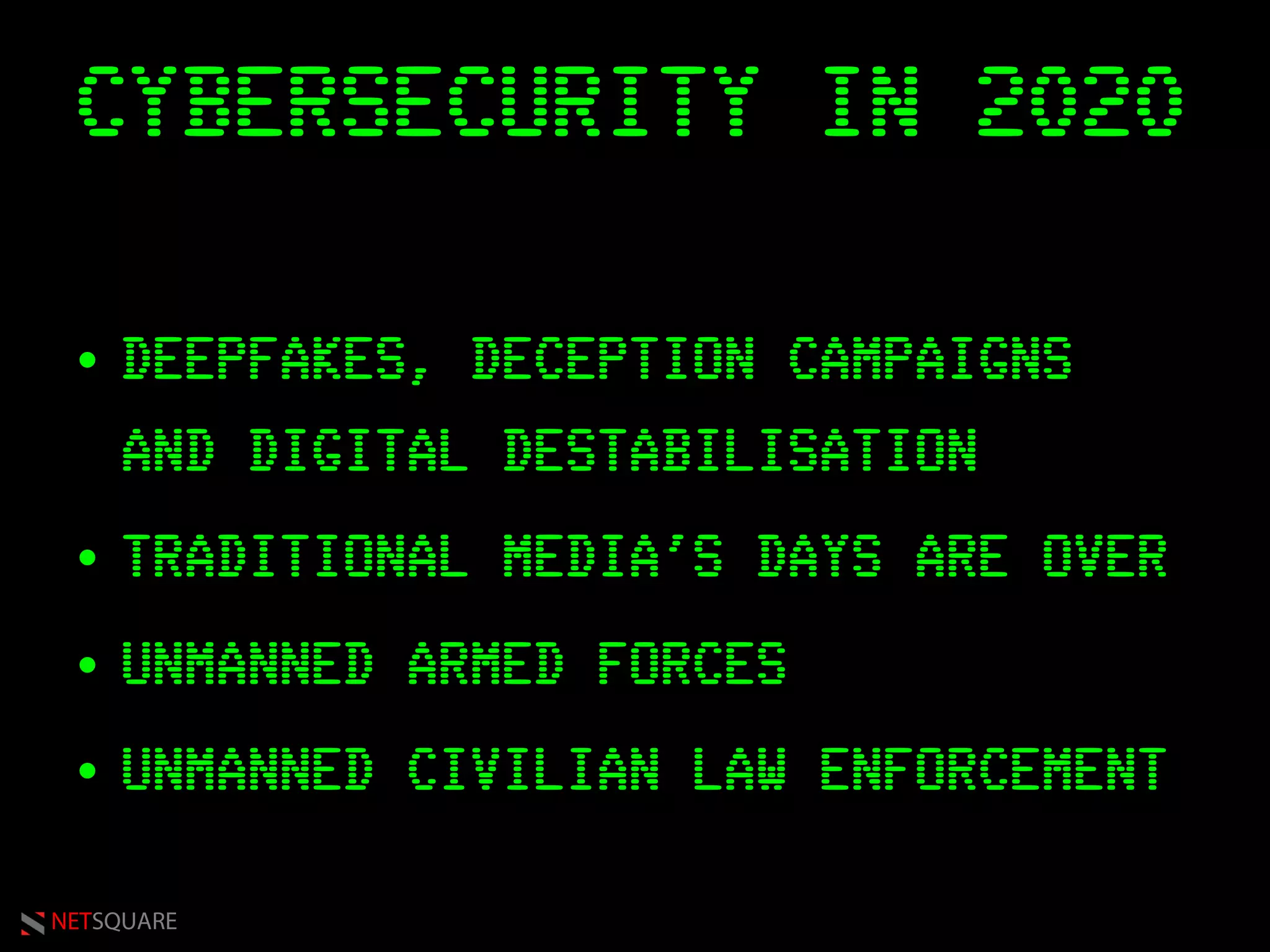
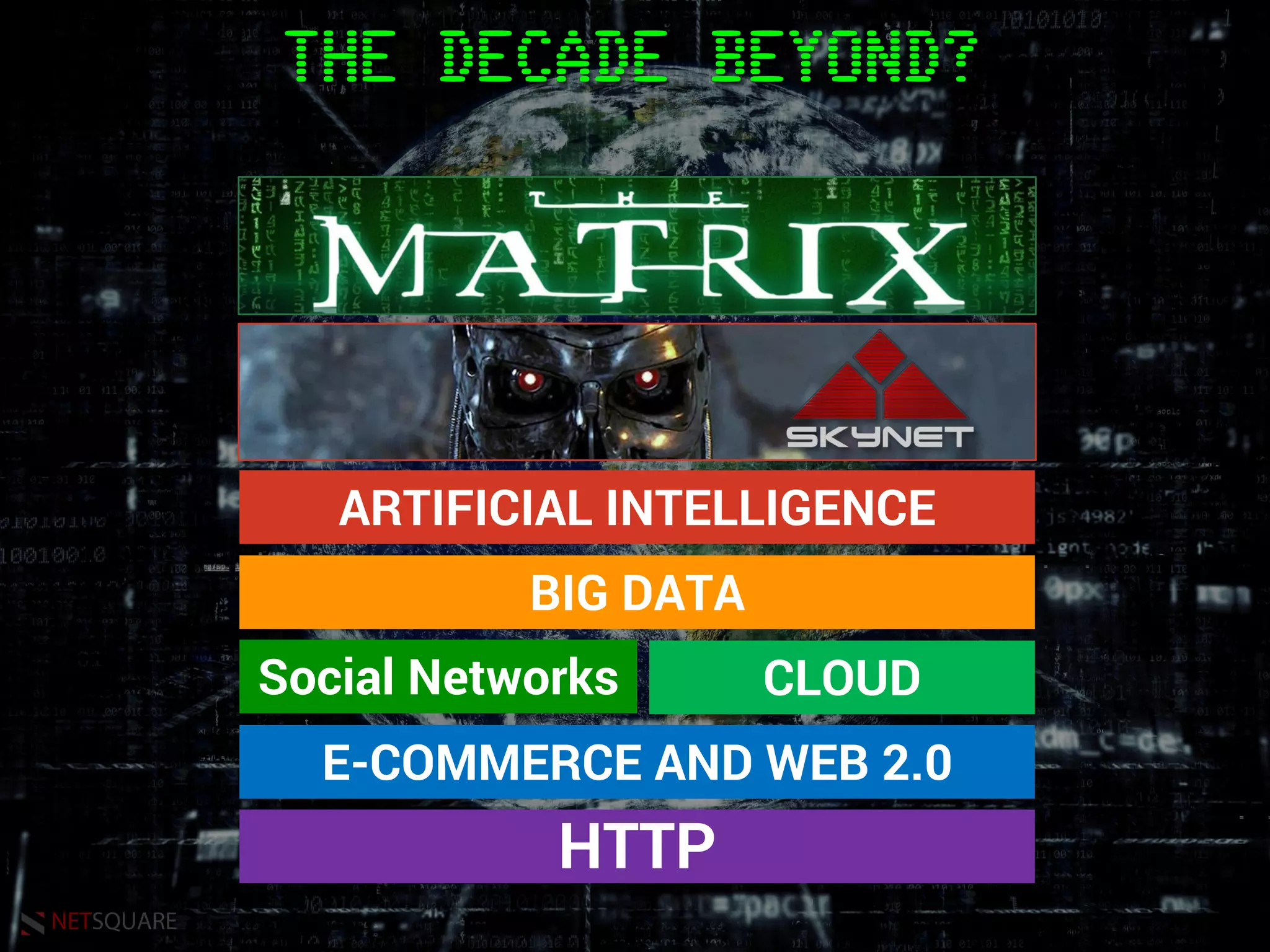
The document discusses the evolution of cyberspace, cybersecurity challenges, and India's role in this landscape over the next decade, as presented by Saumil Shah. It highlights the asymmetry between technology's rapid advancement and society's response, emphasizing issues like data privacy, manipulation of behavior, and the impact of artificial intelligence. The talk also points to the need for India to leverage its unique information overload advantage in overcoming these challenges.