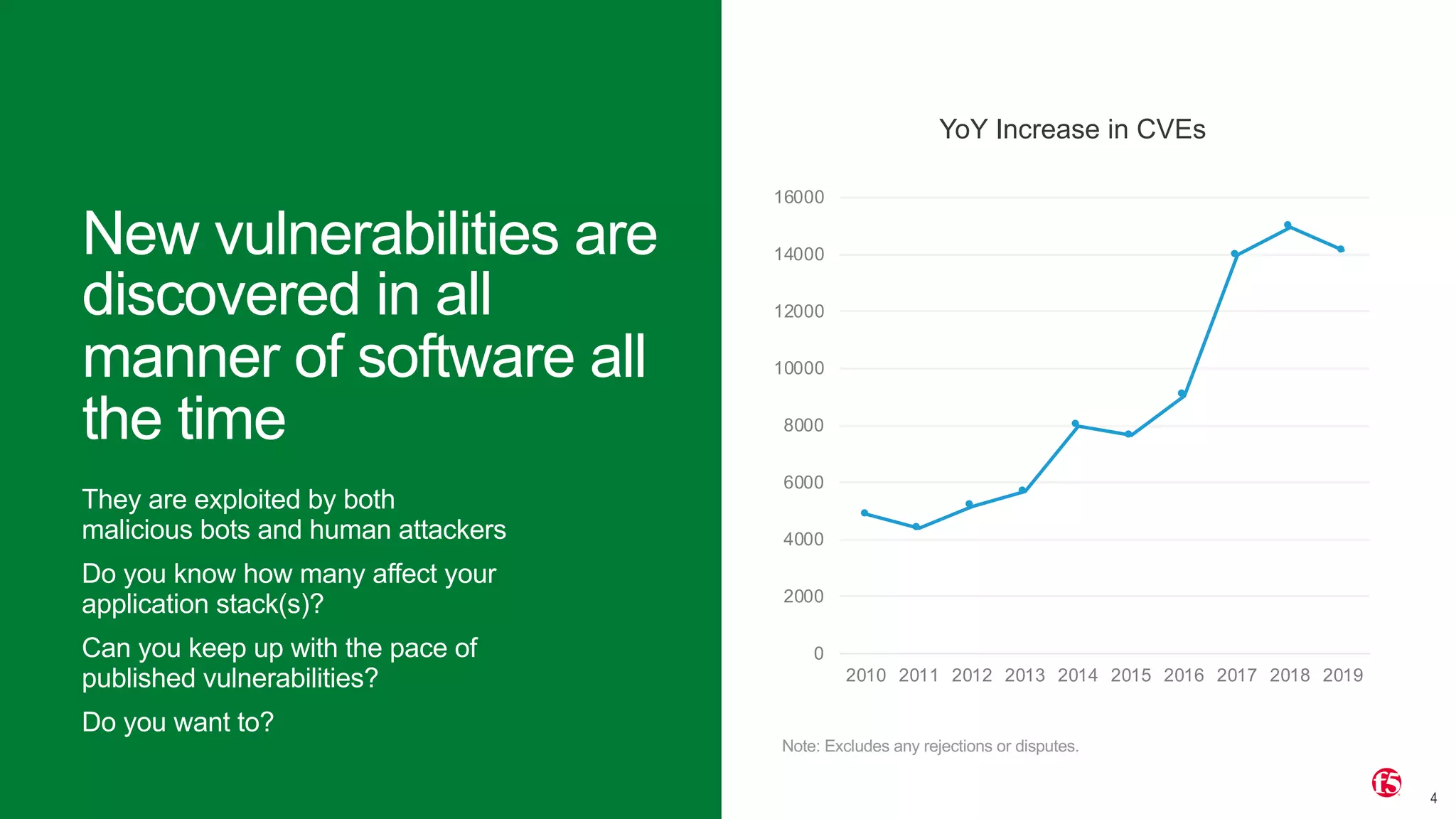
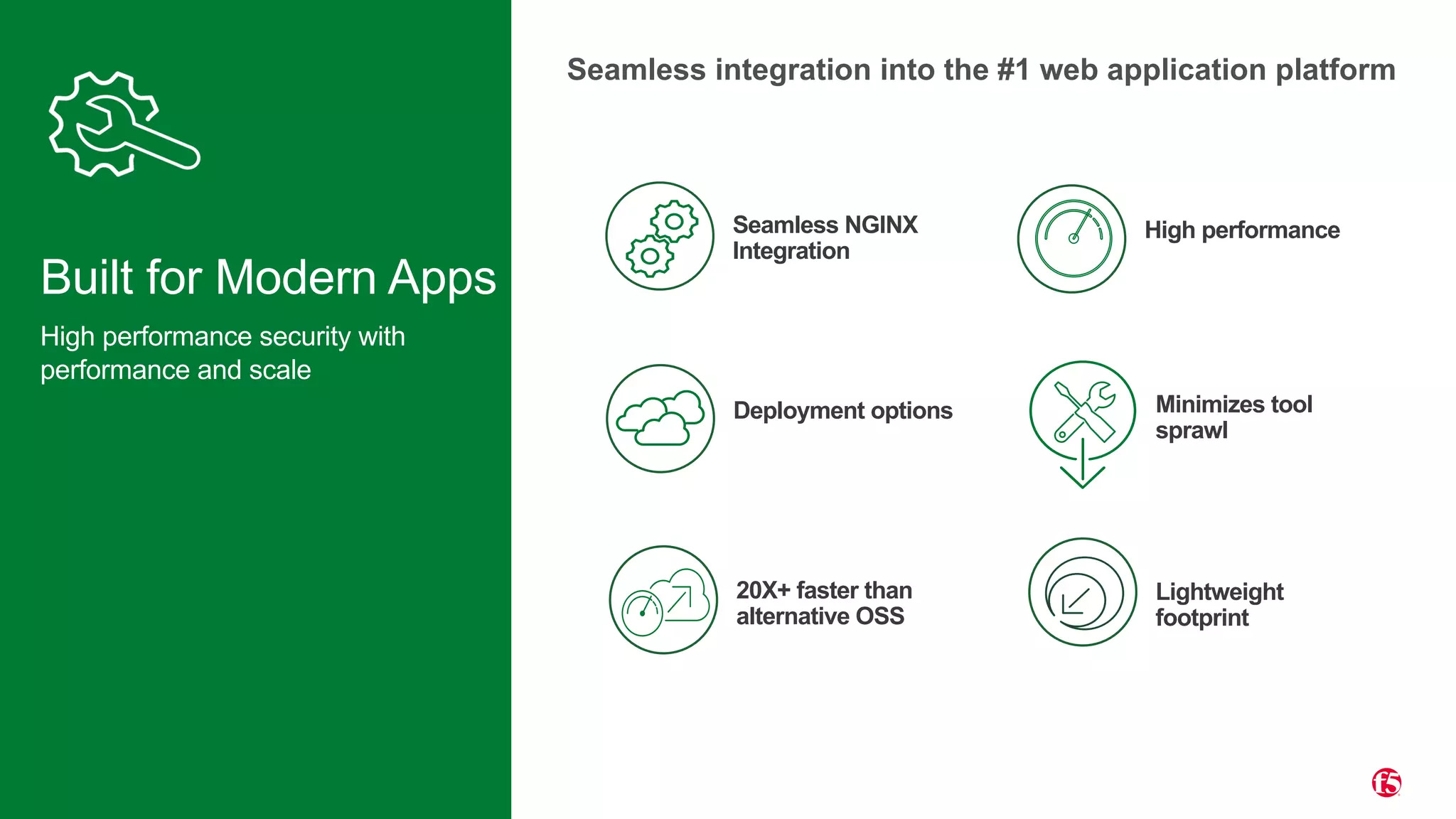
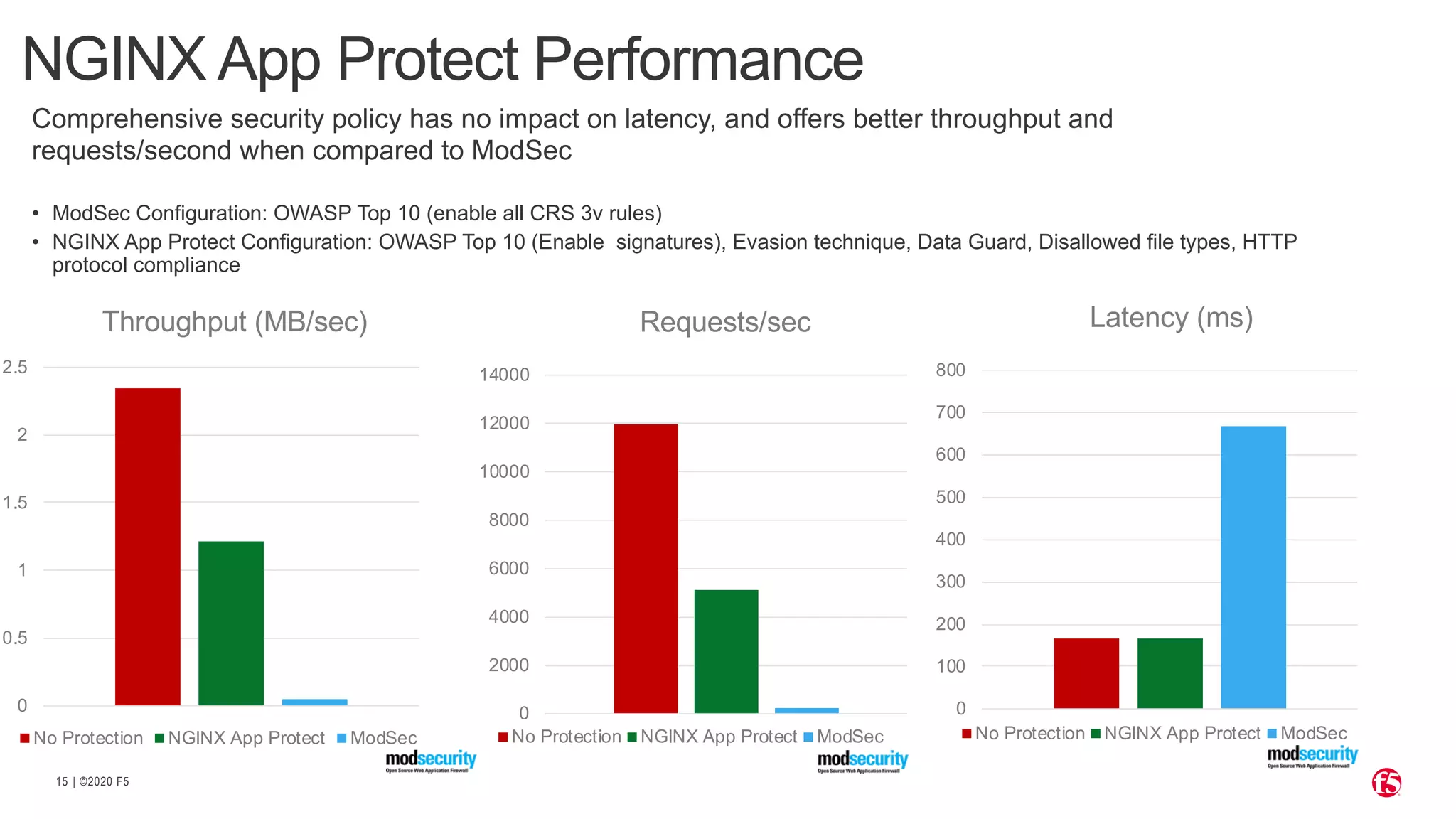
The document discusses the challenges of securing applications in a multi-cloud environment, highlighting the prevalence of software vulnerabilities and common attack vectors. It emphasizes the need for integrating security controls into the development pipeline to protect modern applications effectively. F5's NGINX App Protect solution is presented as a high-performance web application firewall that enhances security while maintaining optimal application performance.


![| ©2020 F518
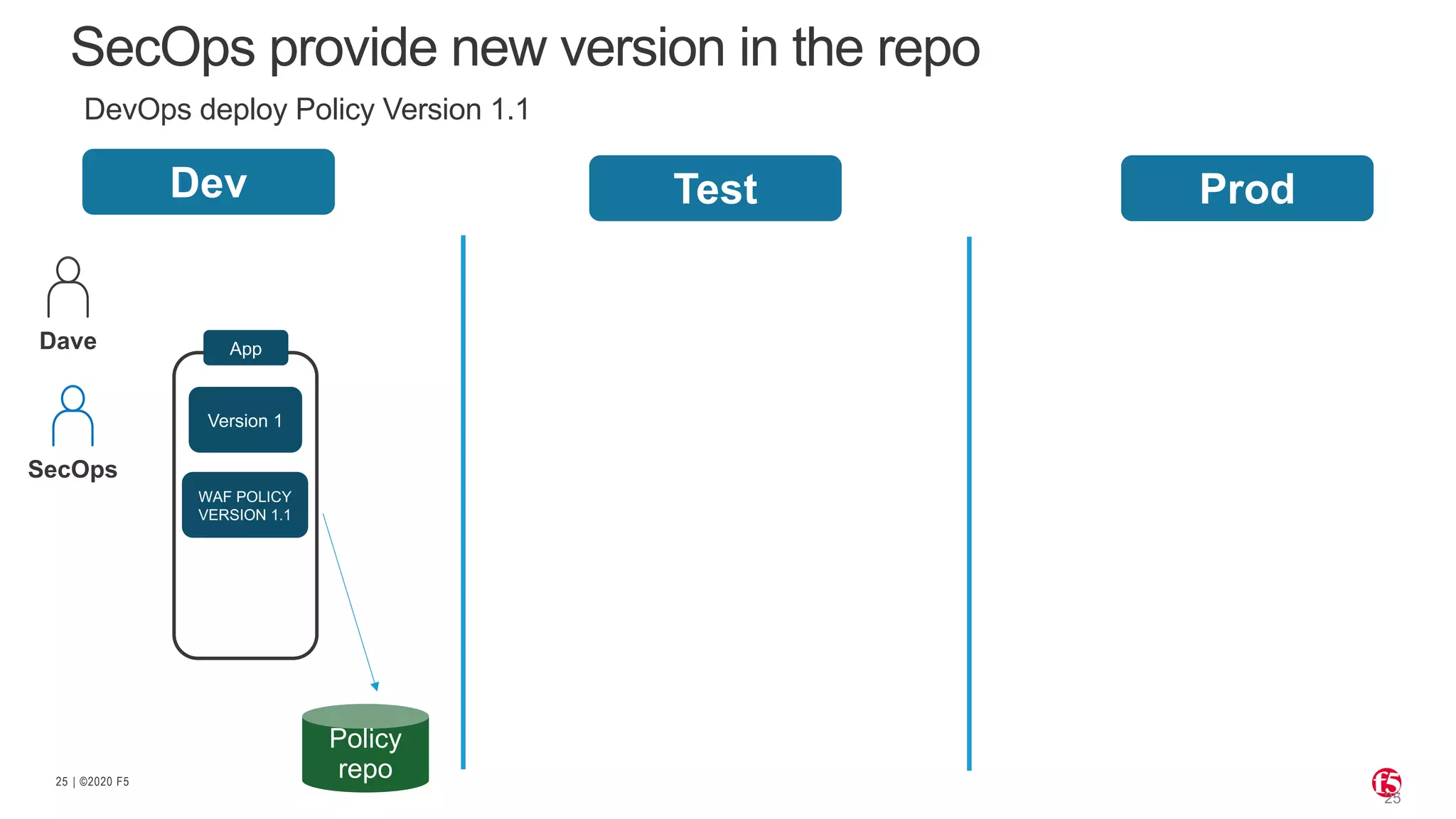
Declarative Policy Helps CI/CD Motion
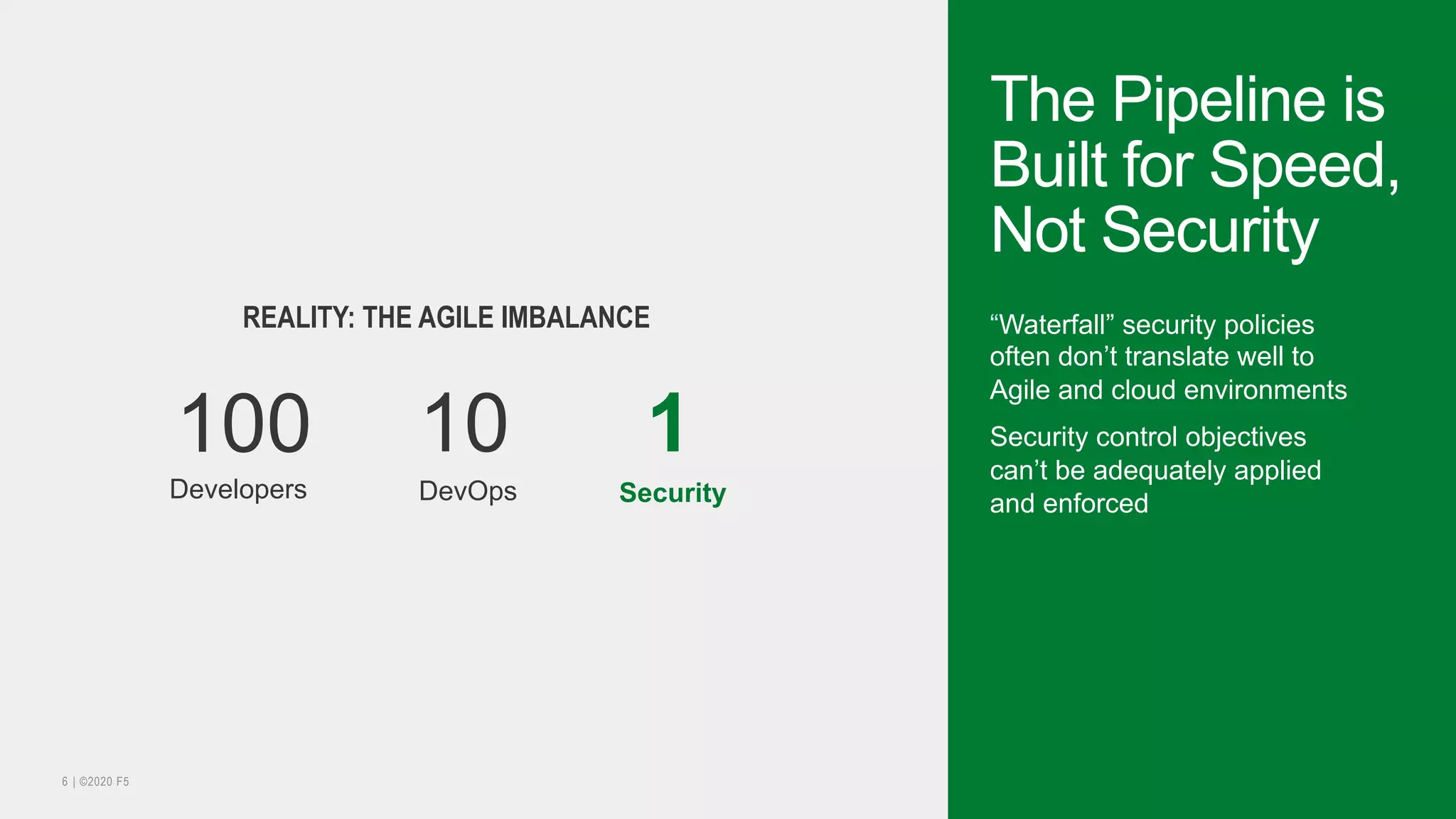
INFRASTRUCTURE AND SECURITY AS CODE
Source Code Repository CI/CD Pipeline Tool IT Automation
Application code/config for App X
security policy/config for App X
Pipeline for build/test/deploy of App X
Ansible playbook for deployment
of App X with its app services
Owned by SecOps Operated by DevOps
{"policy": {
"name":"AppPolicy01",
"description":"AppV1.1 - DEMO ",
"template":{ "name":"POLICY_TEMPLATE_RAPID_DEPLOYMENT" },
"enforcementMode":"blocking",
"server-technologies":[
{"serverTechnologyName":"MySQL“ } ],
"signature-settings":{"signatureStaging": false},
}](https://image.slidesharecdn.com/decouvreznginxappprotect-200622212456/75/Decouvrez-NGINX-AppProtect-18-2048.jpg)
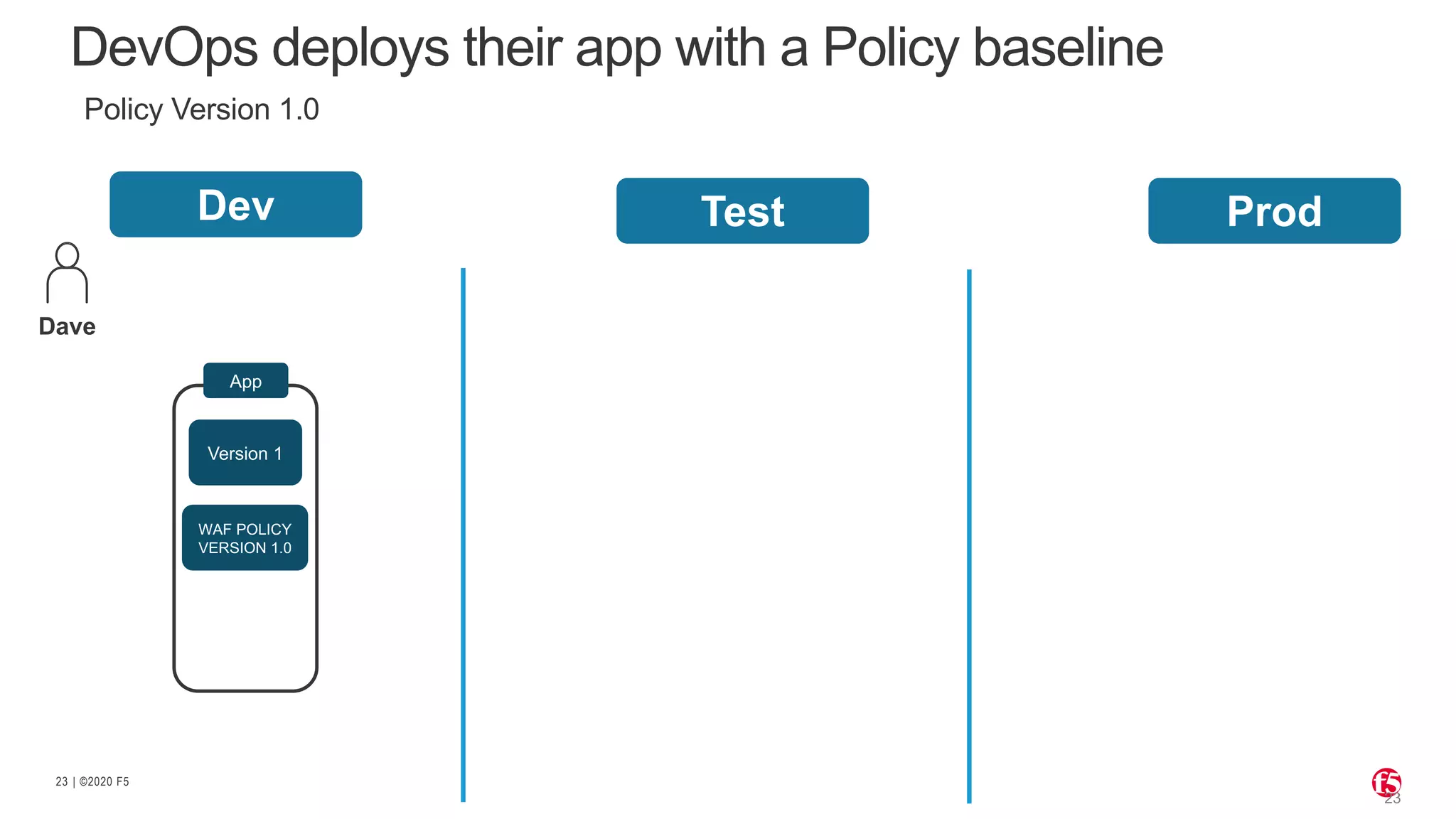
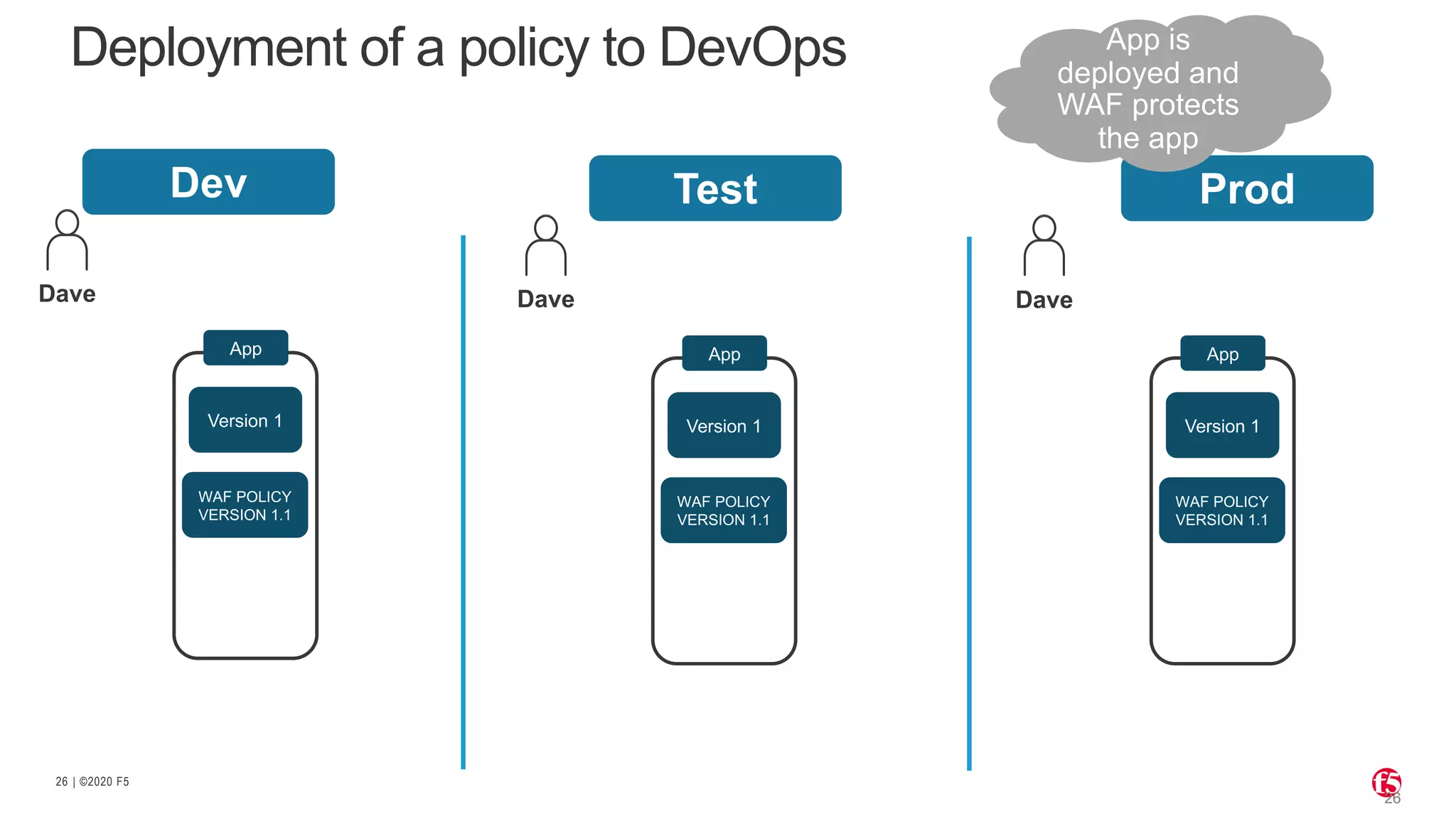
![| ©2020 F524
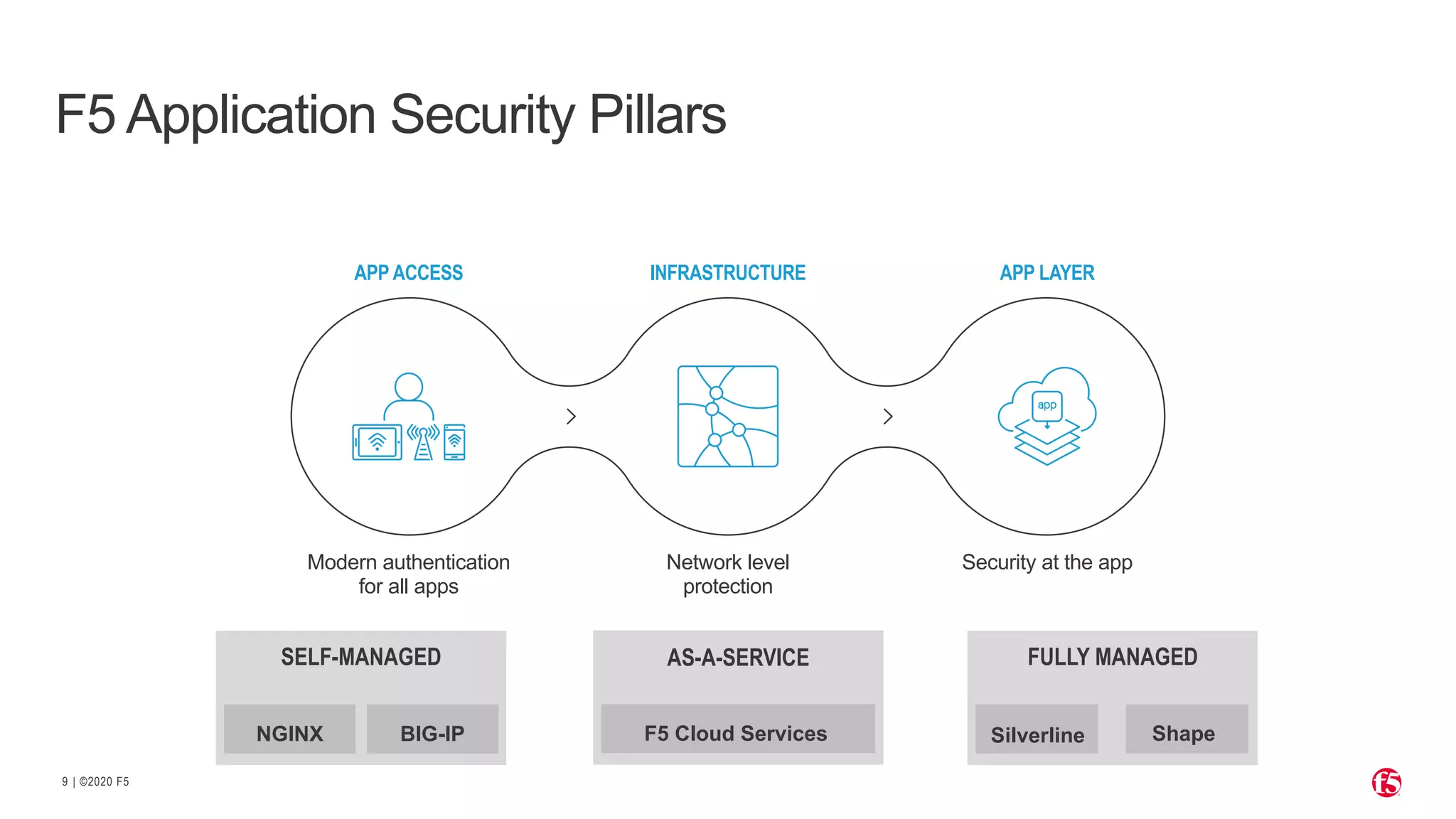
CD
[ Developer ]
Version
control
CI server
Repo
(Docker HUB)
CD server
Build
DEV
env
security
services
Deploy dev
container
Functional
testing
WAF
BLOCKED
security testing](https://image.slidesharecdn.com/decouvreznginxappprotect-200622212456/75/Decouvrez-NGINX-AppProtect-24-2048.jpg)