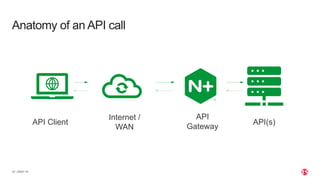
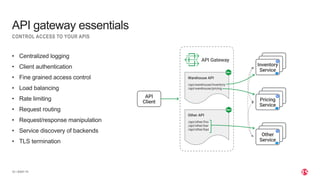
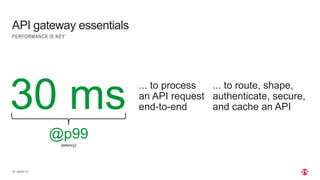
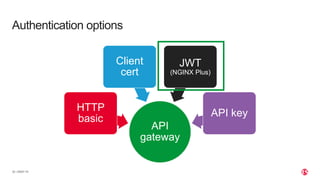
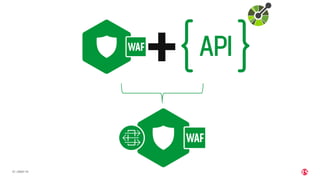
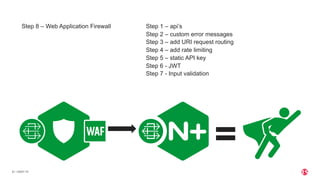
The document discusses the deployment and security of an API gateway using NGINX, outlining the essential components and benefits of APIs and API gateways. It emphasizes the importance of performance, security features such as authentication and traffic control, and the increasing adoption of APIs in digital ecosystems. The presentation also includes steps for implementation and additional resources for further learning.


![| ©2021 F5
11
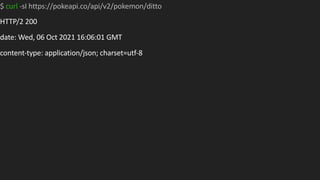
$ curl -s -X GET https://pokeapi.co/api/v2/pokemon/ditto | jq '.types'
[
{
"slot": 1,
"type": {
"name": "normal",
"url": "https://pokeapi.co/api/v2/type/1/"
}
}
]](https://image.slidesharecdn.com/deployandsecureyourapigatewaywithnginx-211117213850/85/Deploy-and-Secure-Your-API-Gateway-with-NGINX-From-Zero-to-Hero-APCJ-8-320.jpg)