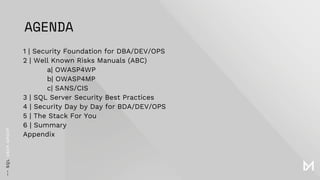
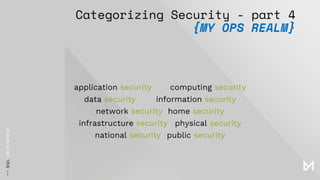
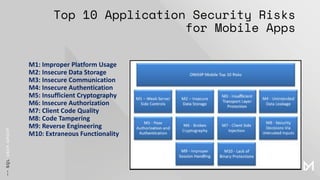
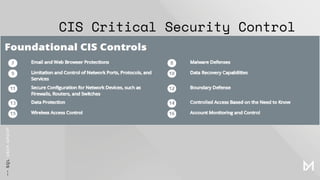
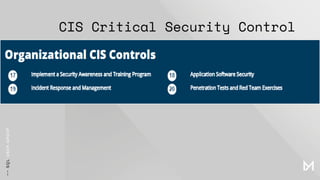
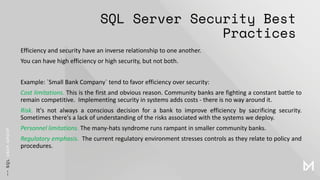
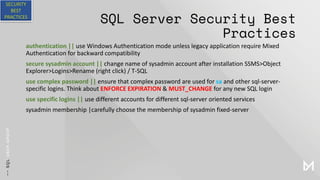
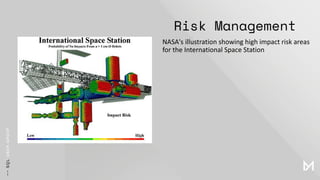
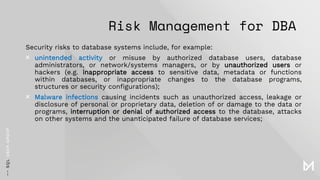
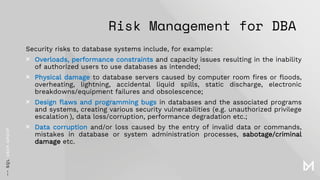
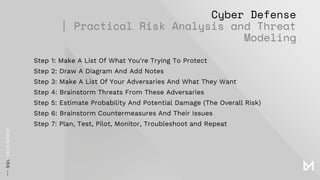
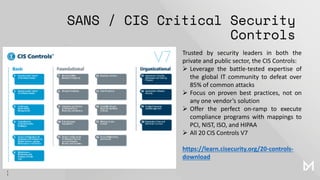
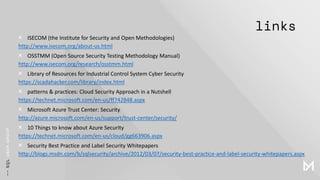
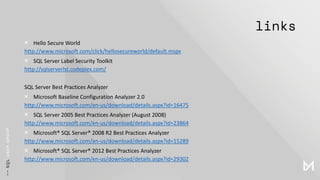
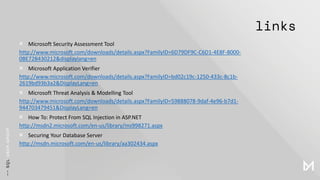
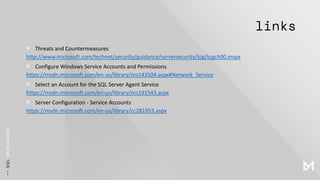
The document outlines comprehensive security practices for DBA/Dev/Ops, detailing well-known risks across various realms, including application and network security. It emphasizes the critical security controls by SANS/CIS and the top application security risks for both web and mobile applications. Additionally, it addresses SQL Server security best practices and the inherent efficiency-security trade-offs faced by organizations, particularly in community banks.