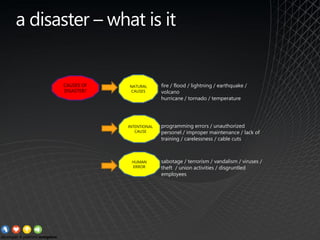
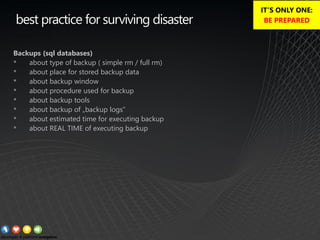
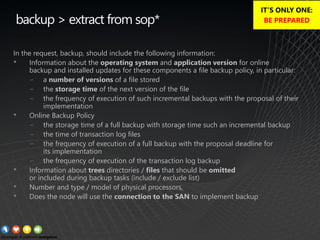
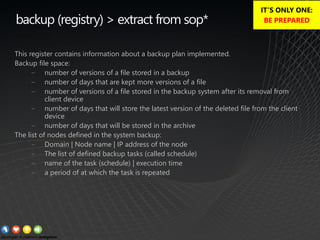
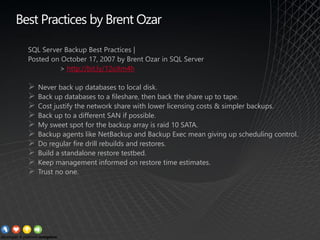
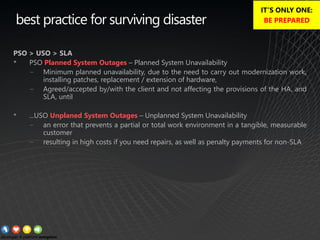
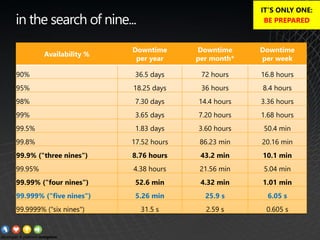
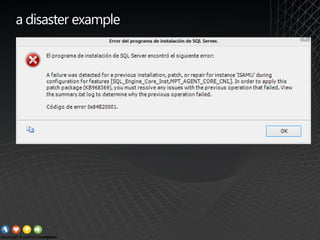
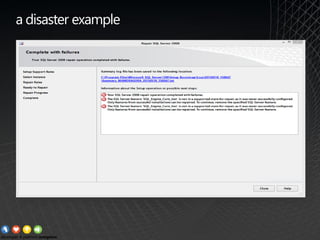
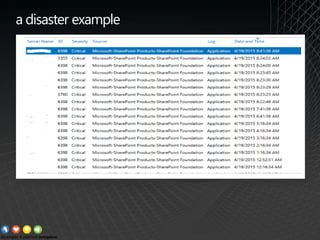
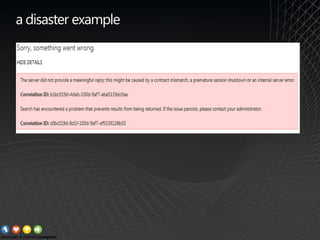
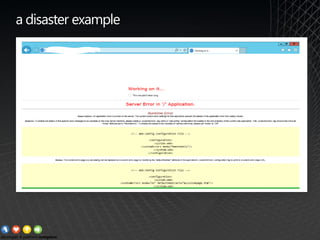
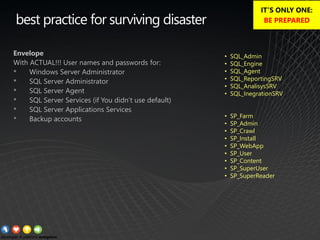
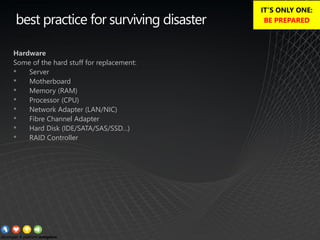
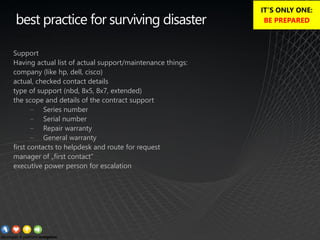
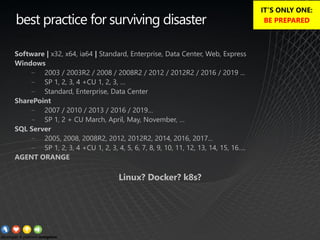
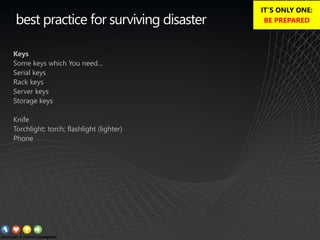
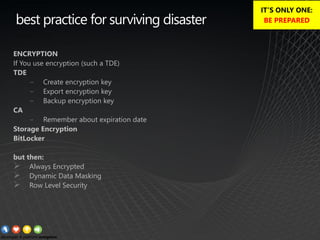
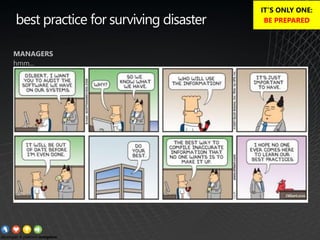
The document outlines best practices for disaster preparedness, particularly focusing on backup and recovery strategies for SQL databases and other systems. Key recommendations include regular backups, testing recovery procedures, ensuring clear communication regarding disaster roles, and maintaining up-to-date hardware and software inventories. The overarching theme emphasizes the importance of being prepared and minimizing potential downtime during disasters.