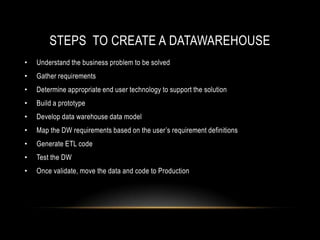
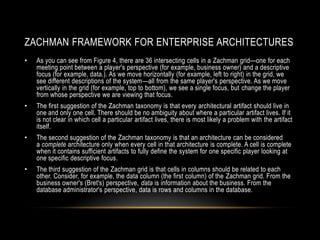
The document discusses data warehousing and business intelligence. It provides an overview of data warehouses, their components like the ETL process, data marts and OLAP. It also discusses the steps to create a data warehouse like understanding business needs, data modeling, ETL development and testing. Business intelligence is defined as using organizational capabilities to generate knowledge and opportunities.