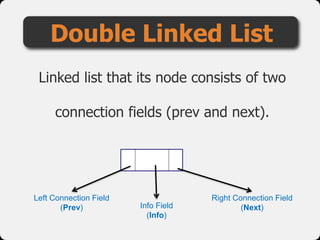
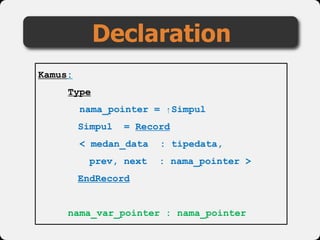
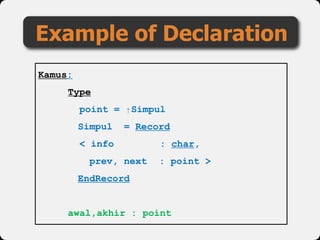
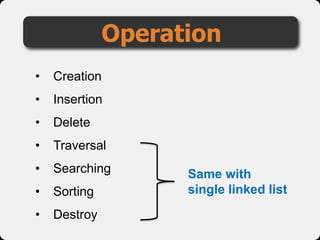
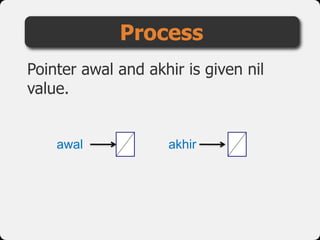
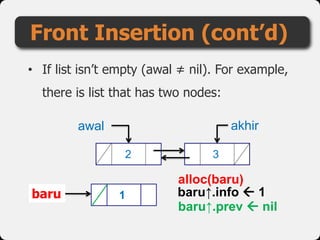
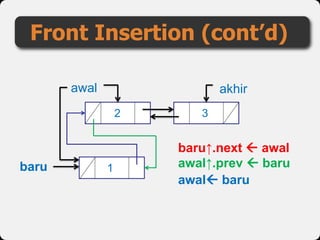
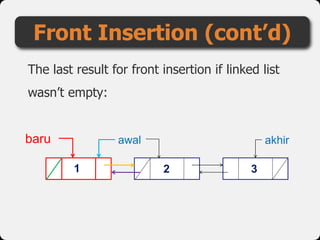
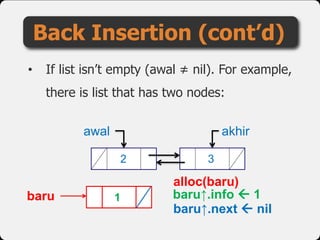
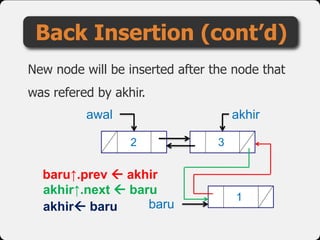
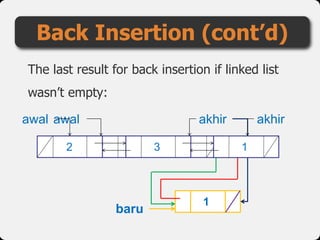
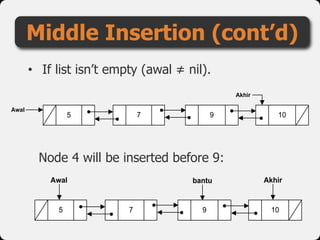
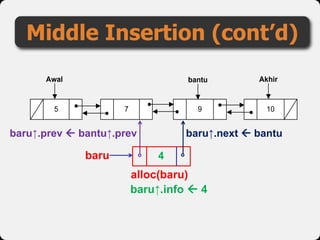
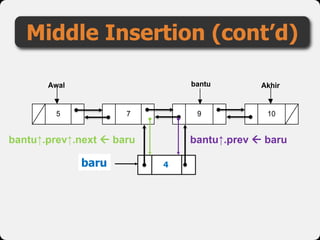
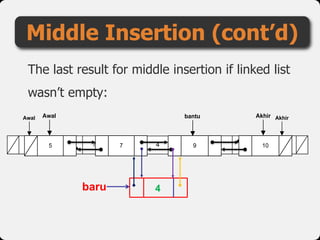
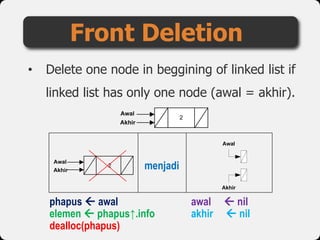
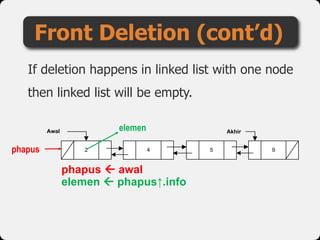
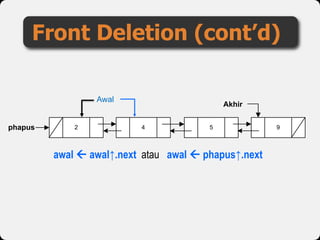
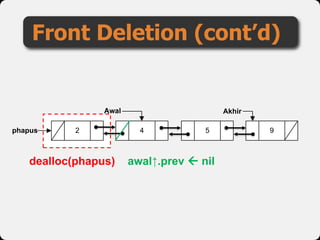
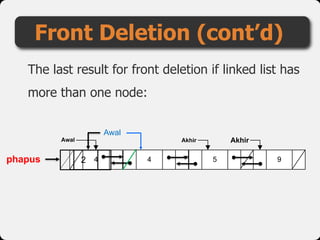
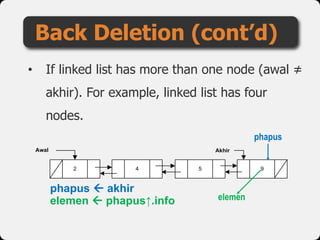
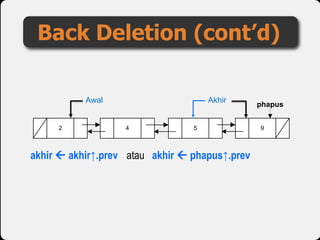
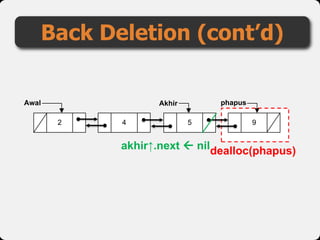
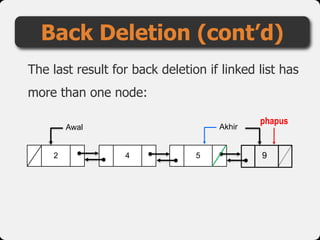
The document describes the structure and operations of a double linked list, detailing the node structure with 'prev' and 'next' connection fields. It outlines operations including creation, insertion (front, back, and middle), deletion (front, back, and middle), and traversal. Example code and procedural steps are provided for each operation, accompanied by contact information for further inquiries.