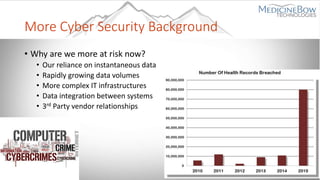
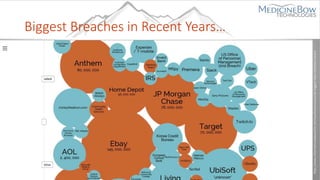
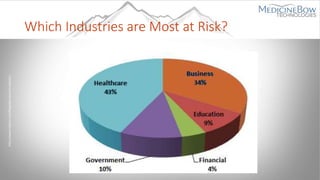
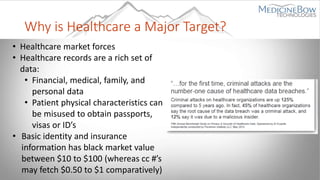
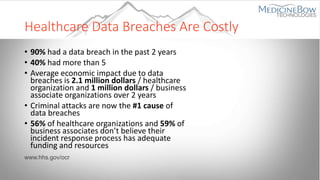
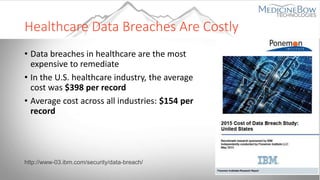
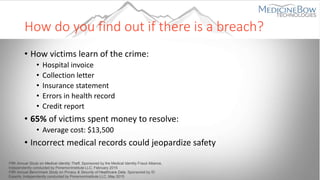
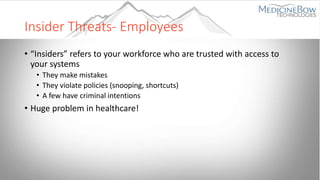
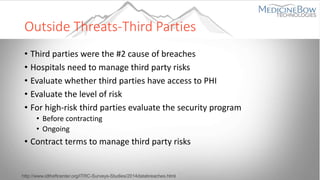
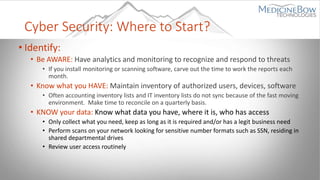
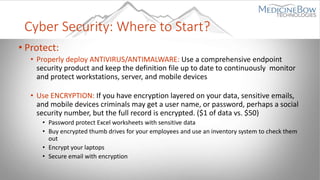
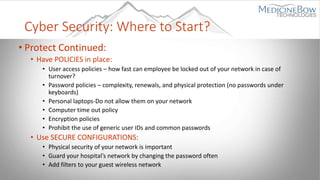
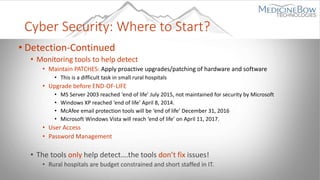
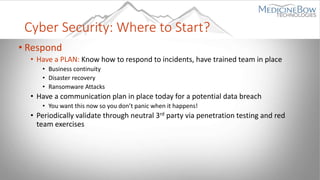
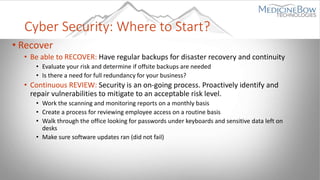
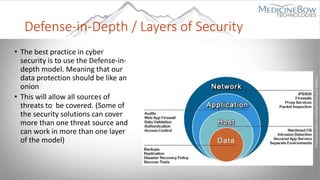
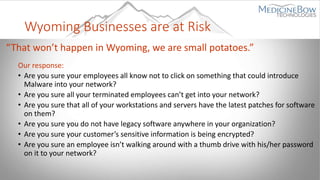
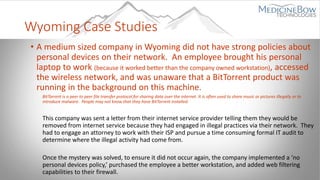
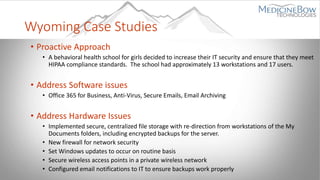
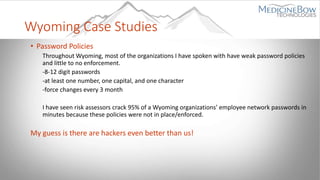
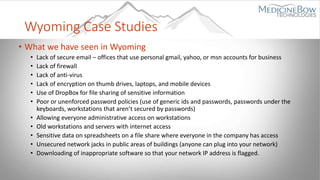
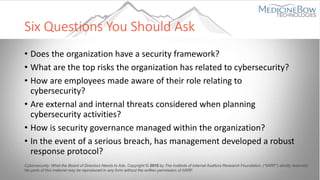
The document provides an overview of the current state of cybersecurity, emphasizing the rising threats posed by organized cybercrime, particularly in the healthcare sector, which faces significant data breach risks and high remediation costs. It outlines best practices for improving security, including identifying vulnerabilities, protecting sensitive data, detecting breaches, responding to incidents, and recovering from attacks. Additionally, it highlights real-life case studies from Wyoming to illustrate the consequences of weak cybersecurity measures and the necessity for proactive strategies in various organizations.