Embed presentation
Download to read offline







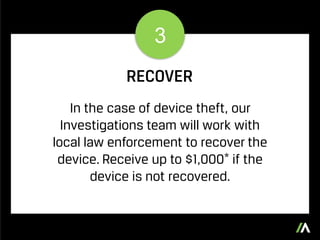


Absolute Safe Schools aims to create a safer learning environment by addressing the risks associated with mobile devices in educational settings. The program provides training for students and staff, promotes campus safety through awareness campaigns, and offers assistance in recovering stolen devices. Schools can receive financial support for unrecovered devices, enhancing overall security and technology protection.