cyber bullying parent workshop 2012
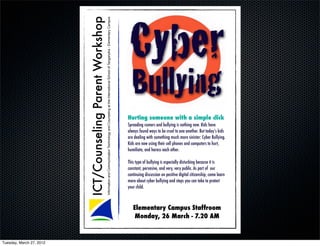
- 1. Cyber ICT/Counseling Parent Workshop Information and Communication Technology and Counseling at the International School of Tanganyika - Elementary Campus Bullying Hurting someone with a simple click Spreading rumors and bullying is nothing new. Kids have always found ways to be cruel to one another. But today’s kids are dealing with something much more sinister: Cyber Bullying. Kids are now using their cell phones and computers to hurt, humiliate, and harass each other. This type of bullying is especially disturbing because it is constant, pervasive, and very, very public. As part of !our continuing discussion on positive digital citizenship, come learn more about cyber bullying and steps you can take to protect your child. Elementary Campus Staffroom Monday, 26 March - 7.20 AM Tuesday, March 27, 2012
- 2. Tuesday, March 27, 2012
- 3. bullying Tuesday, March 27, 2012
- 4. bullying defined Bullying is an act of repeated aggressive behavior in order to intentionally hurt another person, physically or mentally. Bullying is characterized by an individual behaving in a certain way to gain power over another person. Besag V.E. Tuesday, March 27, 2012
- 5. cyber bullying Tuesday, March 27, 2012
- 6. cyber bullying defined The use of information and communication technologies to support deliberate, repeated, and hostile behavior by an individual or group, that is intended to harm others. Bill Belsey Tuesday, March 27, 2012
- 7. What’s the vs difference? Tuesday, March 27, 2012
- 8. What’s the vs difference? •Can be annonymous •Can occur in your own home •Can be 24/7 •No witnessing by teachers or parents •Can be viewed by an entire class, friendship group or community instantly Tuesday, March 27, 2012
- 9. video - cyber bullying http://www.youtube.com/watch?v=S03Br1dwJR8 Childnet International Tuesday, March 27, 2012
- 10. discussion • How did this film make you feel as a parent? • How was what you saw in this film different than what you experienced? Tuesday, March 27, 2012
- 11. mum’s perspective http://www.youtube.com/watch?v=Y6XIPogWZPU Childnet International Tuesday, March 27, 2012
- 12. questions • At your child's current age, can you identify possible ways that cyber bullying could occur? • How are our children interacting online? Tuesday, March 27, 2012
- 13. video - social media http://www.commonsensemedia.org/advice-for-parents/social-networking-tips Common Sense Media Tuesday, March 27, 2012
- 14. Here are that should be considered about social networking sites. introducing Stay positive about social networking sites – try to strike a balance between educating children and young people to behave safely and trusting them to get on with it. Get involved – ask them how to create a profile, get them to show you theirs and ask them to add you to their friends list! the Make sure that children know how to protect themselves on social networking sites through the tools provided. It’s important to discuss the value of privacy with children. Encourage your child to keep their passwords private and work with them to check the privacy settings on their account 5Ps which limit how much of their information can be seen by others – for example, encourage your child to change their settings to private so that only people they allow can see what they post and comment on their space, rather than public which leaves their site open to be viewed by anyone. It’s natural that children will want to include a photo on their site or profile, but help them think about the implications of posting photos and what is suitable. It is important to think about the type of picture and the kind of attention it might attract, the information it could divulge and who could see it. Suggest that your child ask permission of other people in the images that they post. Also, be aware that photos can be easily copied, changed, shared, used elsewhere, and can potentially stay online forever. One question to ask about your child is “would they want a future employer to see this photo?” The ability to interact with this media and comment on other people’s sites is part of what makes these sites so attractive. However, make sure you social networking help your child to think before they post. Set some ground rules about what is and isn’t OK to say in a blog or profile. This relates to what the child says about others as much as about themselves. What starts off as a joke or gossip can quickly escalate to cause real pain which cannot be taken back. It’s really important that you encourage your child to tell you about inappropriate or illegal activity they may come across. If you suspect your child is being groomed by someone with a sexual interest in children, it’s vital that you help them keep a copy of the offending images or messages and report them to the police via the Child Exploitation and Online Protection Centre website . If they are being harassed by another user, report that person’s screen name to the SN provider which hopefully will act on violations to its terms of service. Tuesday, March 27, 2012
- 15. Here are that should be considered about positive social networking sites. Stay positive about social networking sites – try to strike a balance between educating children and young people to behave safely and trusting them to get on with it. Get involved – ask them how to create a profile, get them to show you theirs and ask them to add you to their friends list! privacy Make sure that children know how to protect themselves on social networking sites through the tools provided. It’s important to discuss the value of privacy with children. Encourage your child to keep their passwords private and work with them to check the privacy settings on their account which limit how much of their information can be seen by others – for example, encourage your child to change their settings to private so that only people they allow can see what they post and comment on their space, rather than public which leaves their site open to be viewed by anyone. photos It’s natural that children will want to include a photo on their site or profile, but help them think about the implications of posting photos and what is suitable. It is important to think about the type of picture and the kind of attention it might attract, the information it could divulge and who could see it. Suggest that your child ask permission of other people in the images that they post. Also, be aware that photos can be easily copied, changed, shared, used elsewhere, and can potentially stay online forever. One question to ask your child is “would they want a future employer to see this photo?” posting The ability to interact with this media and comment on other people’s sites is part of what makes these sites so attractive. However, make sure you help your child to think before they post. Set some ground rules about what is and isn’t OK to say in a blog or profile. This relates to what the child says about others as much as about themselves. What starts off as a joke or gossip can quickly escalate to cause real pain which cannot be taken back. police It’s really important that you encourage your child to tell you about inappropriate or illegal activity they may come across. If you suspect your child is being groomed by someone with a sexual interest in children, it’s vital that you help them keep a copy of the offending images or messages and report them to the police via the Child Exploitation and Online Protection Centre website . If they are being harassed by another user, report that person’s screen name to the SN provider which hopefully will act on violations to its terms of service. Tuesday, March 27, 2012
- 16. video - cyber bullying happens http://www.youtube.com/watch?v=D7uyScK3-CU Tuesday, March 27, 2012
- 17. smart rules Childnet has produced 5 key SMART rules which remind young people to be SMART online. It can be helpful to go through these tips with your children. Keep safe by being careful not to give out personal information, – such as your full name, e-mail address, phone number, home address, photos or school name – either to people you are chatting with online or by posting it online where other people can see it. Meeting someone you have only been in touch with online can be dangerous. Only do so with your parents’ or carers’ permission and even then only when they can be present. Accepting e-mails, IM messages, or opening files, pictures or texts from people you don’t know or trust can lead to problems – they may contain viruses or nasty messages! Information you find on the internet may not be true, or someone online may be lying about who they are. Tell your parent, carer or a trusted adult if someone or something makes you feel uncomfortable or worried, or if you or someone you know is being bullied online. Tuesday, March 27, 2012
- 18. smart rules Childnet has produced 5 key SMART rules which remind young people to be SMART online. It can be helpful to go through these tips with your children. Safe Keep safe by being careful not to give out personal information, – such as your full name, e-mail address, phone number, home address, photos or school name – either to people you are chatting with online or by posting it online where other people can see it. Meeting Meeting someone you have only been in touch with online can be dangerous. Only do so with your parents’ or carers’ permission and even then only when they can be present. Accepting Accepting e-mails, IM messages, or opening files, pictures or texts from people you don’t know or trust can lead to problems – they may contain viruses or nasty messages! Reliable Information you find on the internet may not be true, or someone online may be lying about who they are. Tell Tell your parent, carer or a trusted adult if someone or something makes you feel uncomfortable or worried, or if you or someone you know is being bullied online. Tuesday, March 27, 2012
- 19. Additional Resources: http://isttech.wordpress.com/ Tuesday, March 27, 2012
- 20. Additional Resources: http://isttech.wordpress.com/ Tuesday, March 27, 2012
- 21. references http://questgarden.com images http://artistsinspireartists.com/graphic_design/awesome-illustrations-gary-taxali http://www.youtube.com/watch?v=S03Br1dwJR8 videos http://www.youtube.com/watch?v=Y6XIPogWZPU http://www.youtube.com/watch?v=4B89yPghS6w http://www.youtube.com/watch?v=D7uyScK3-CU http://www.commonsensemedia.org/ information http://www.digizen.org/ Mikey McKillip Glen Blair ICT Coordinator Counselor/Vice Principal IST Elementary Campus IST Elementary Campus Tuesday, March 27, 2012