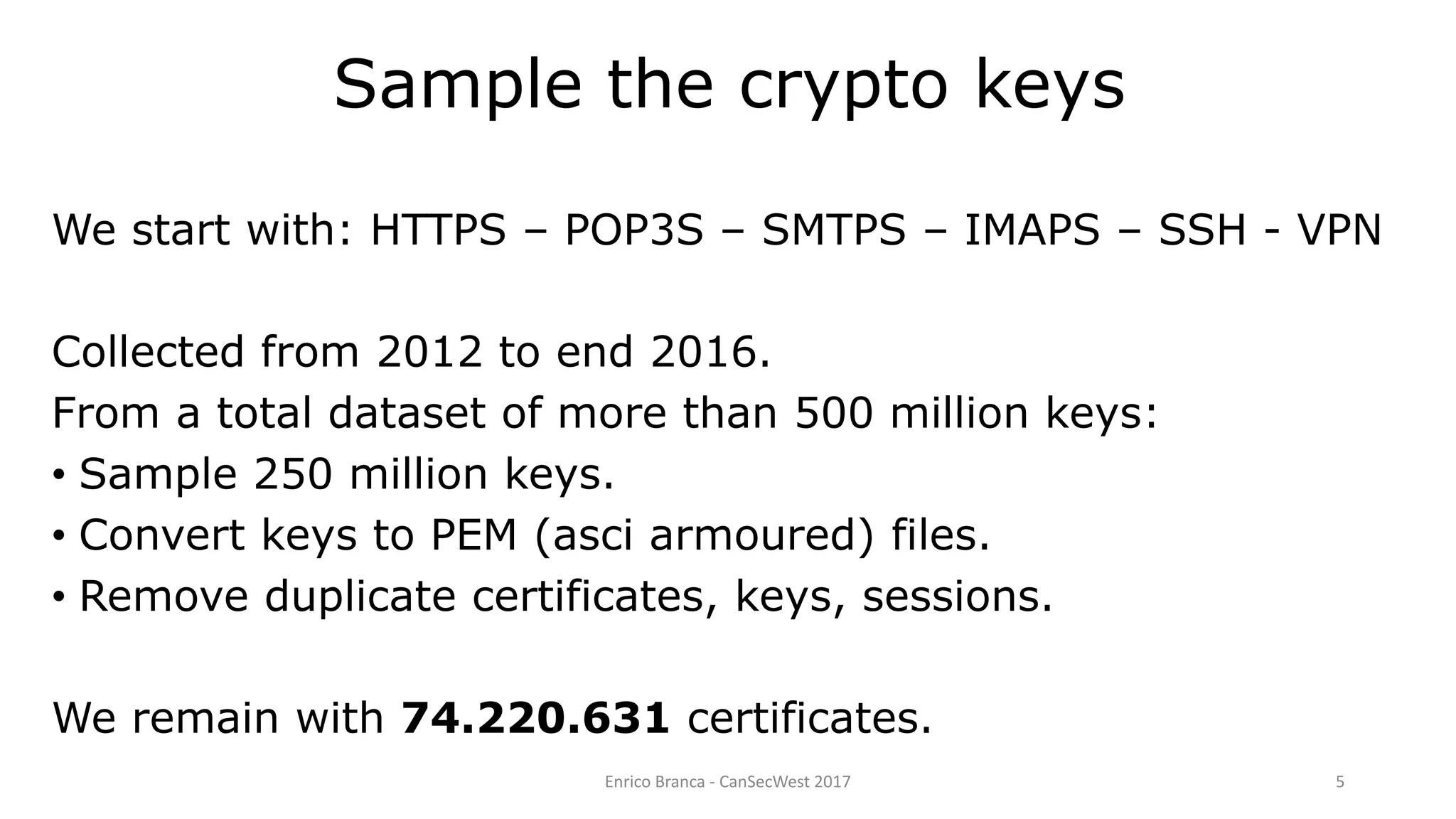
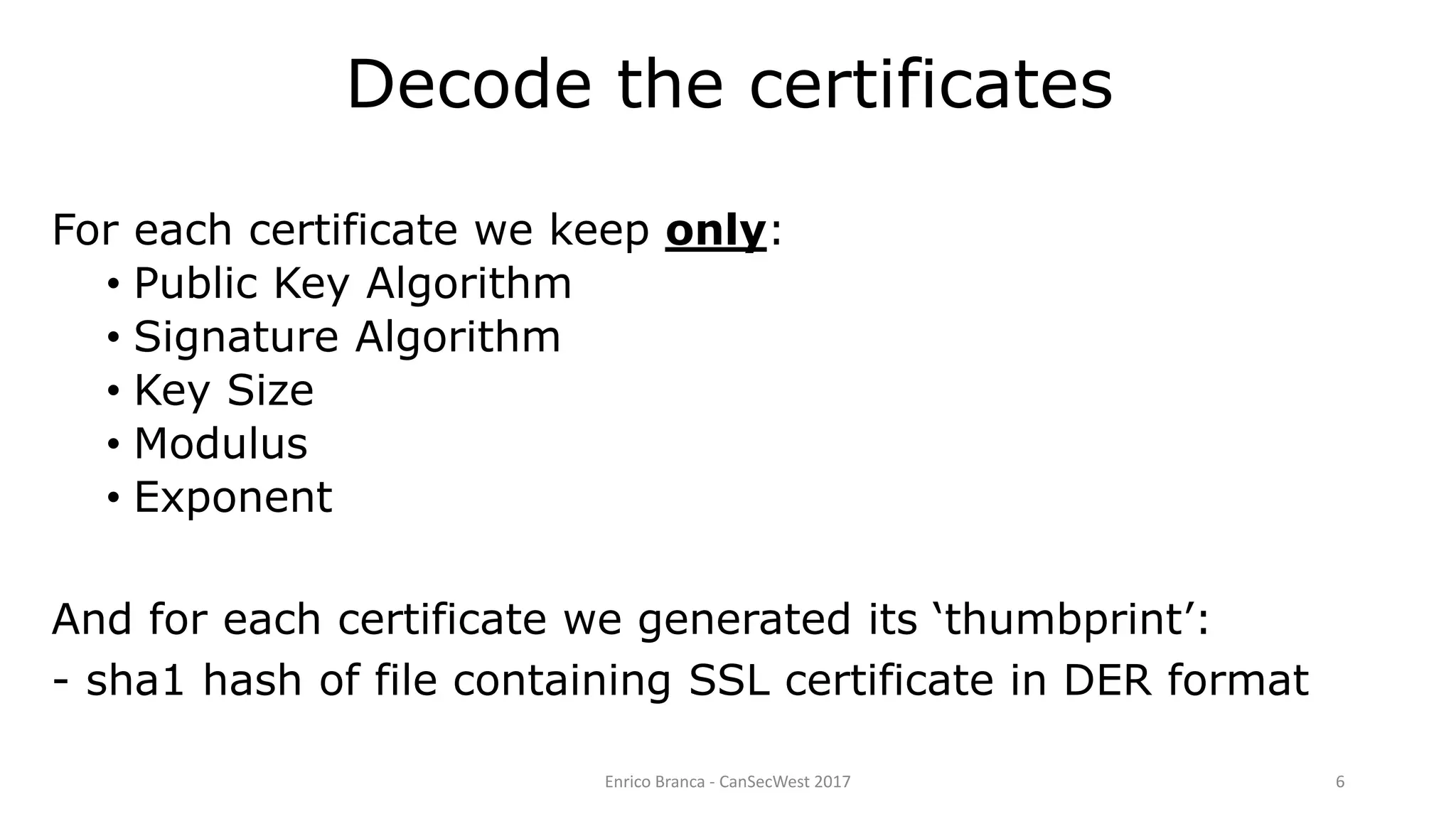
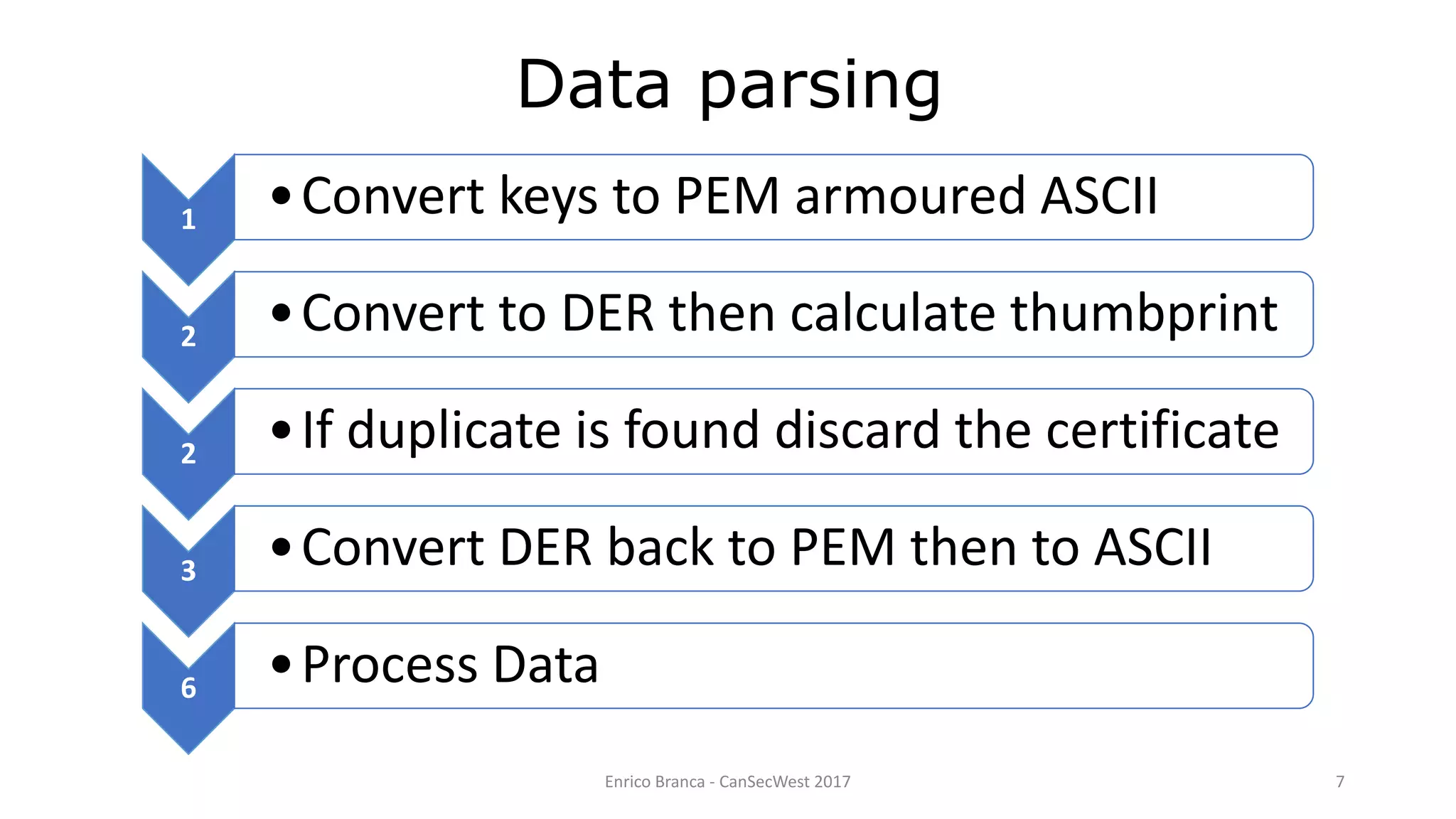
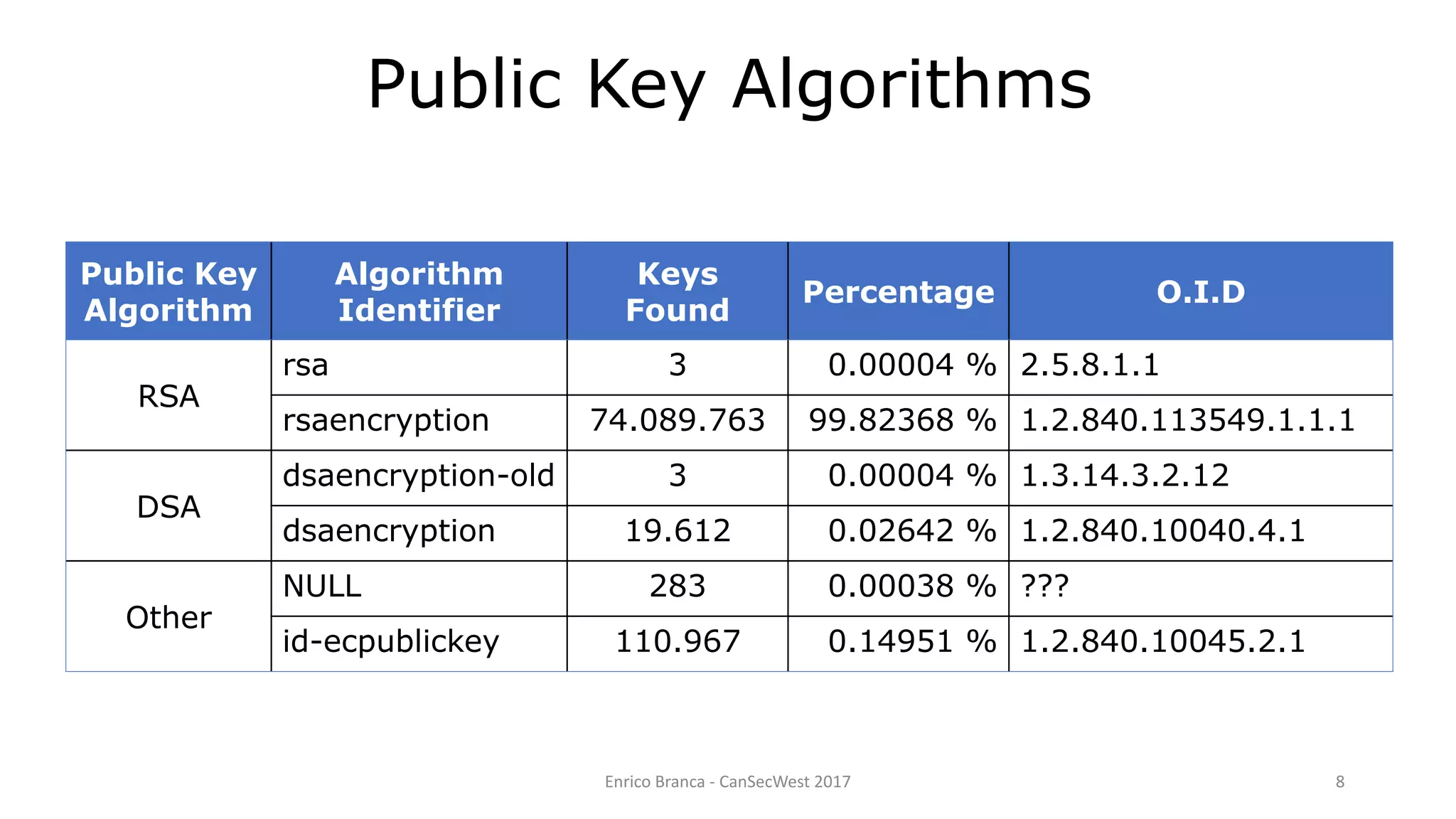
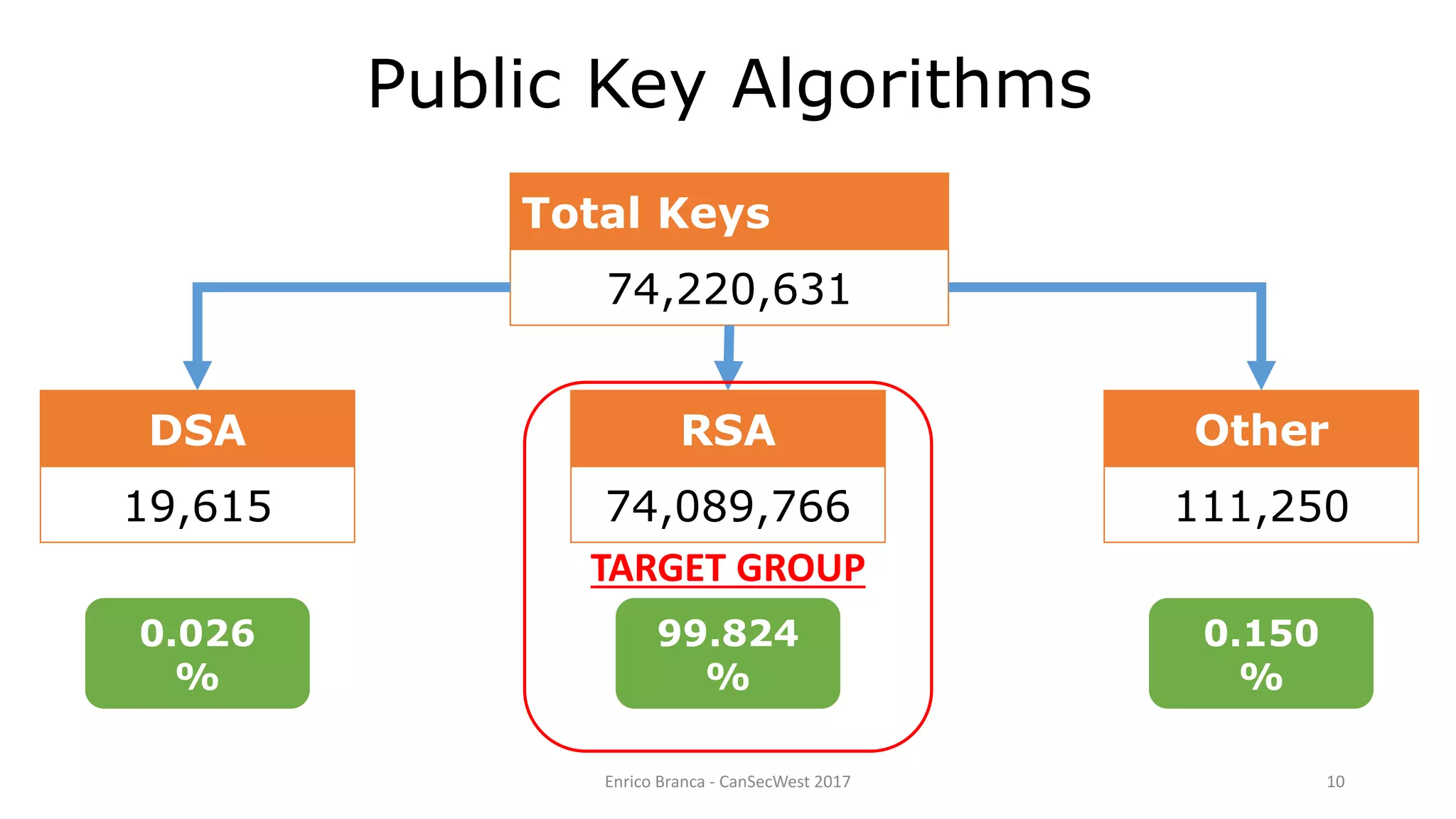
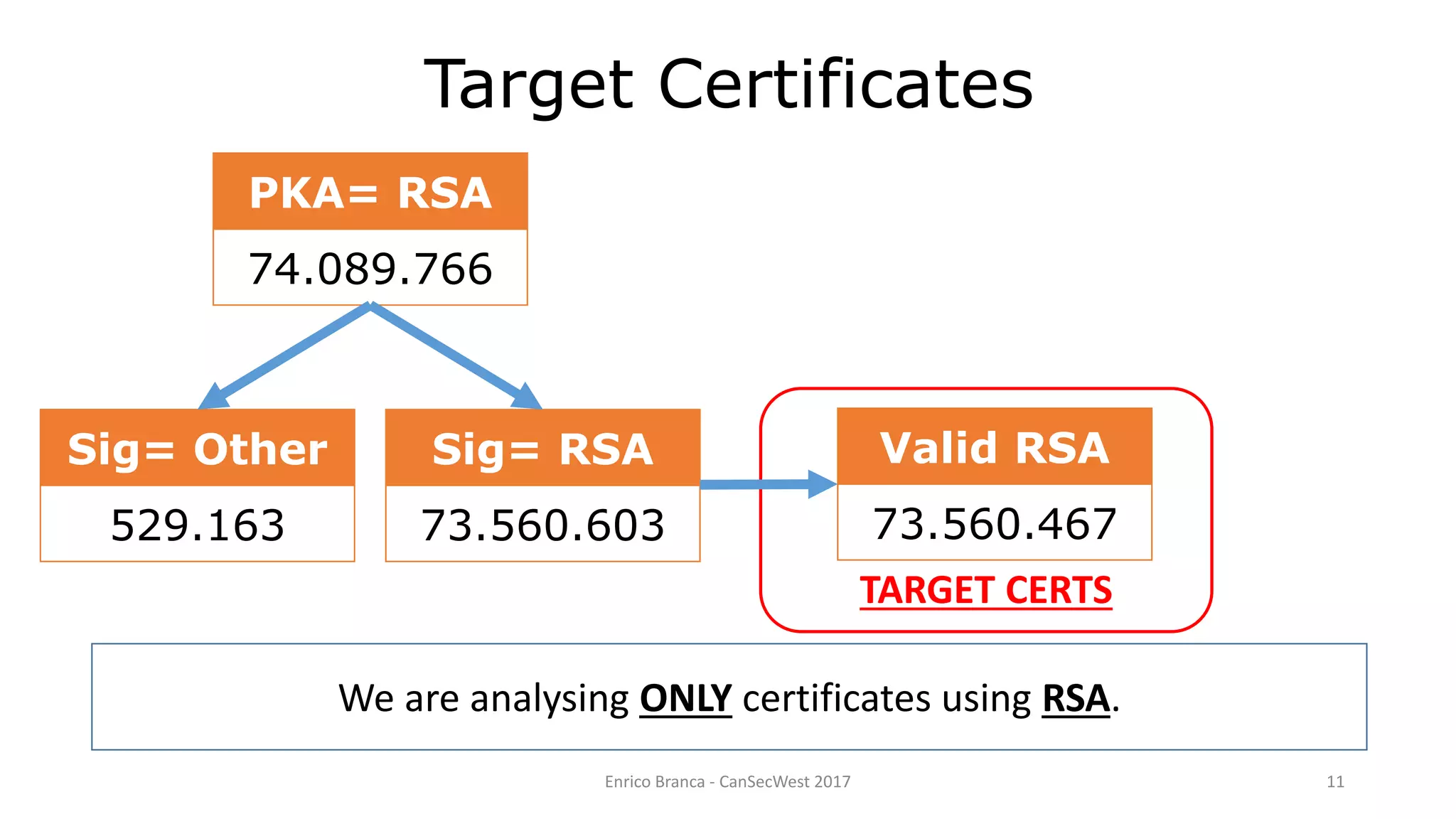
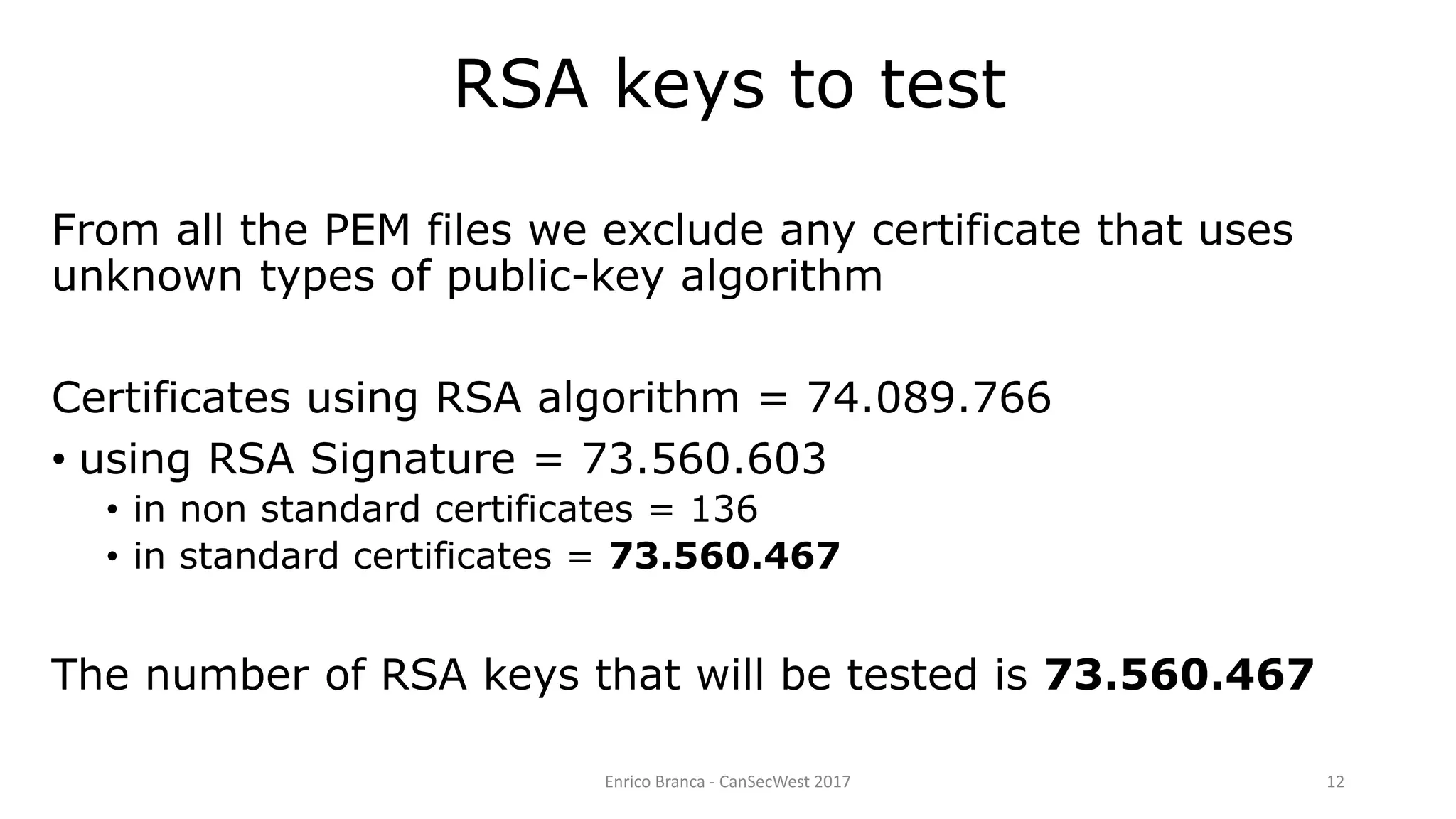
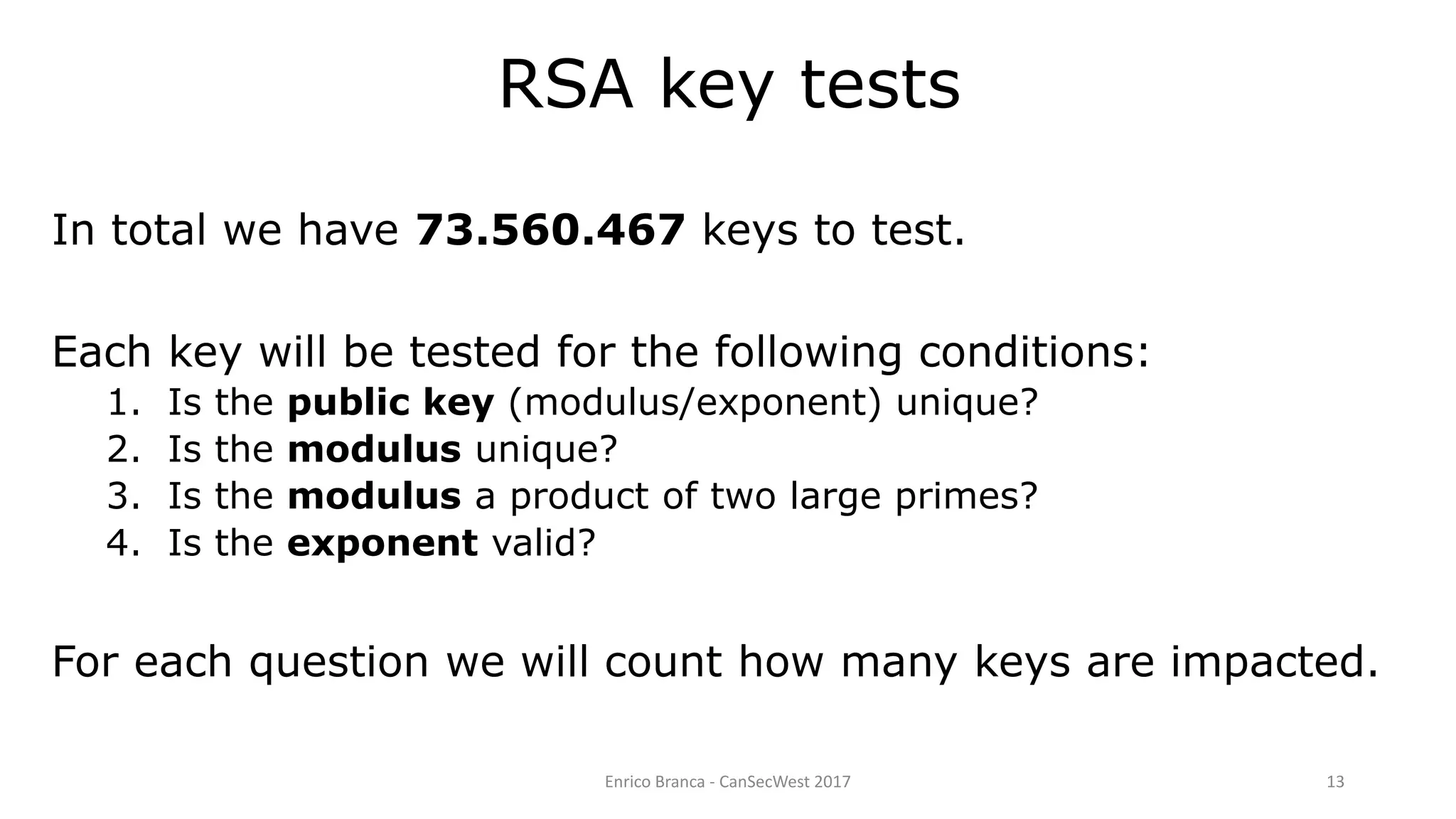
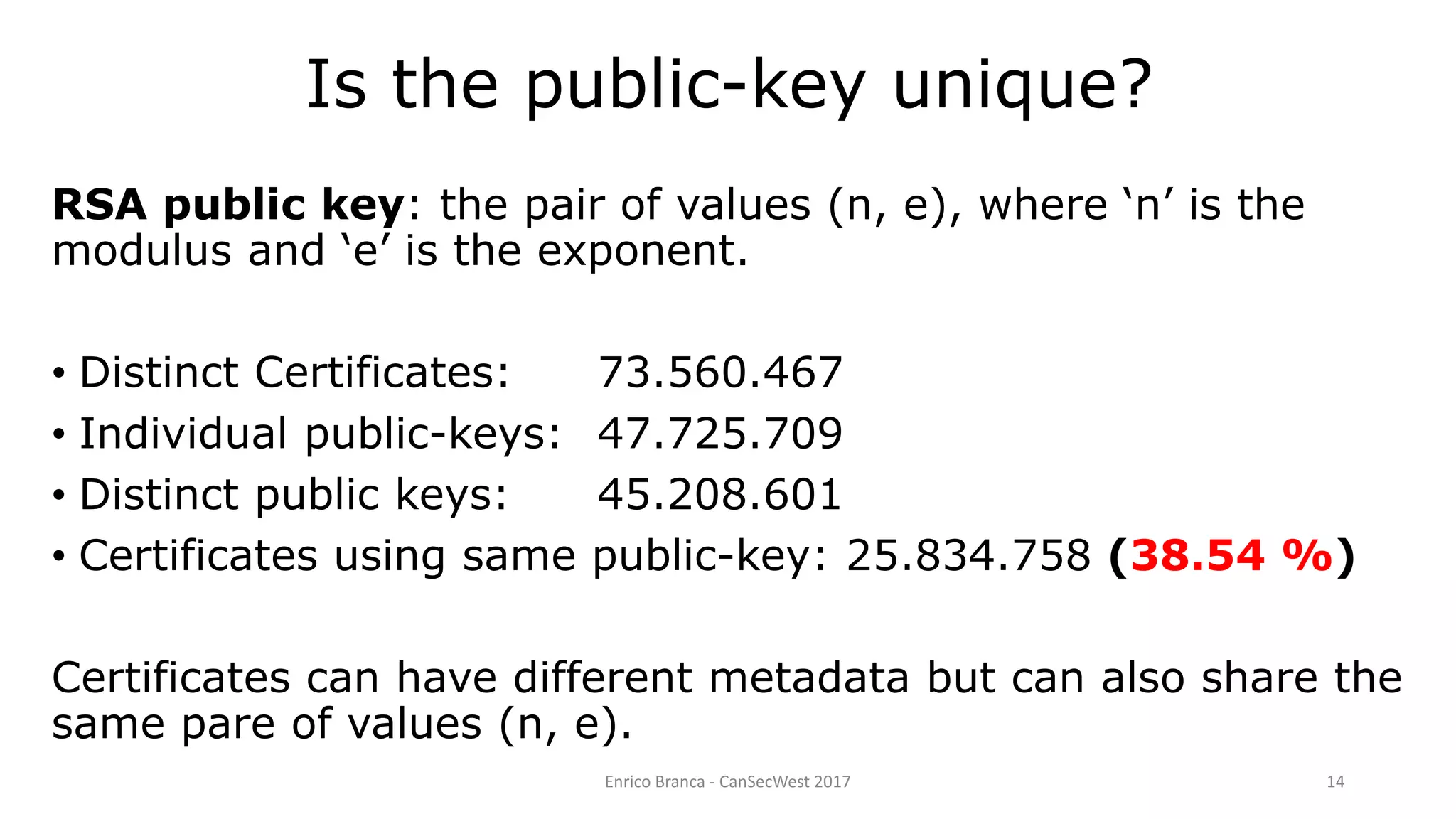
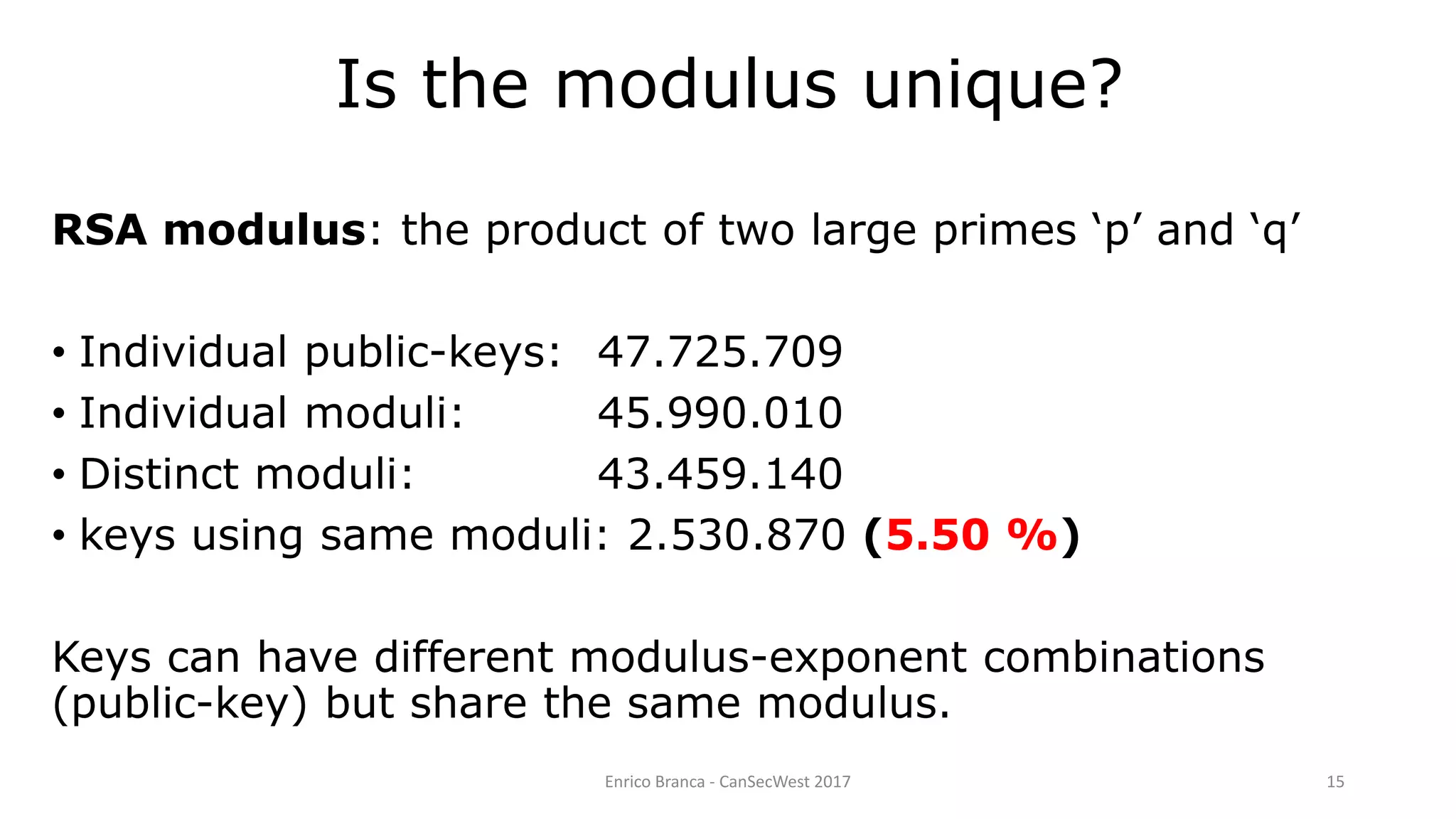
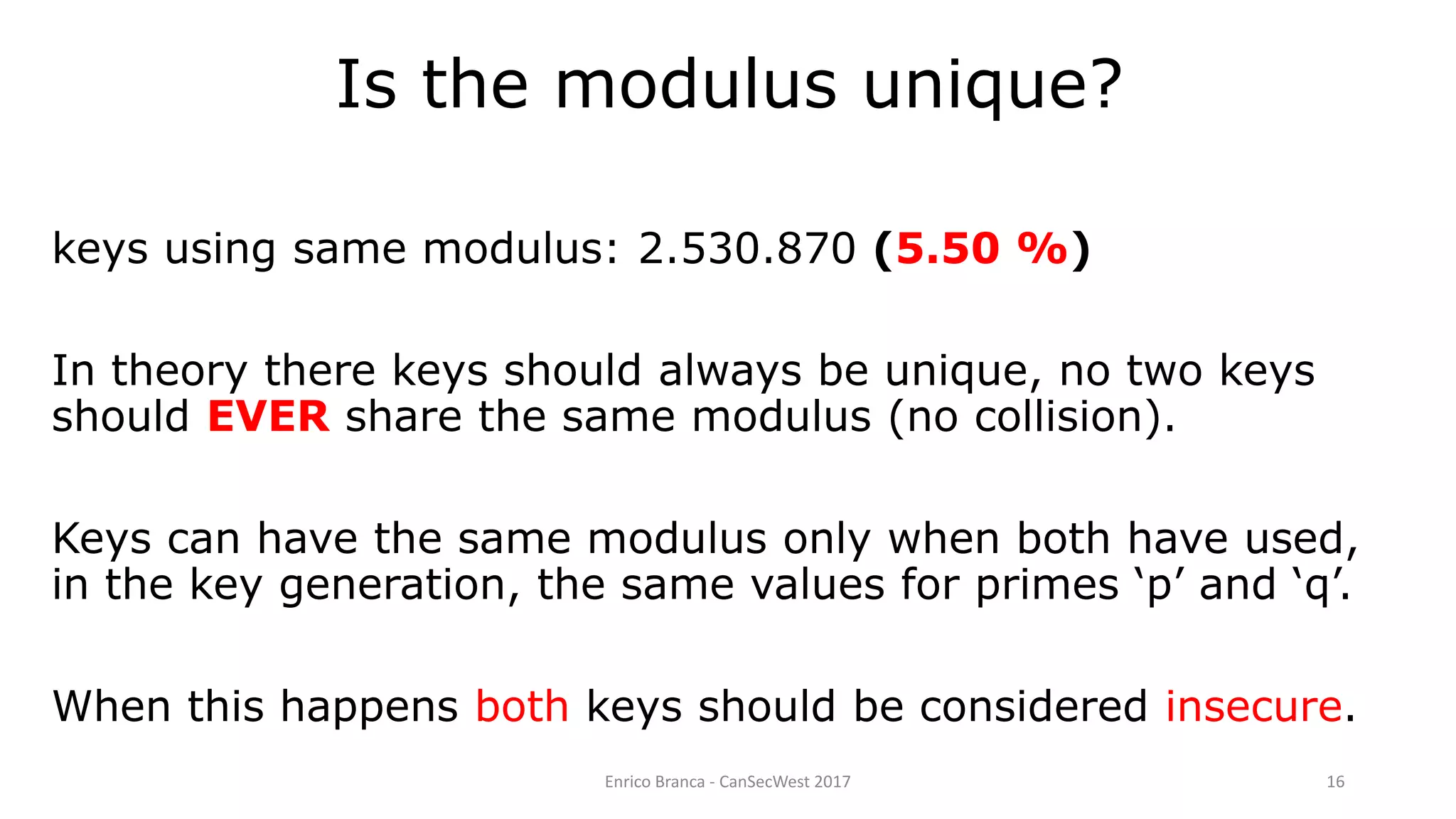
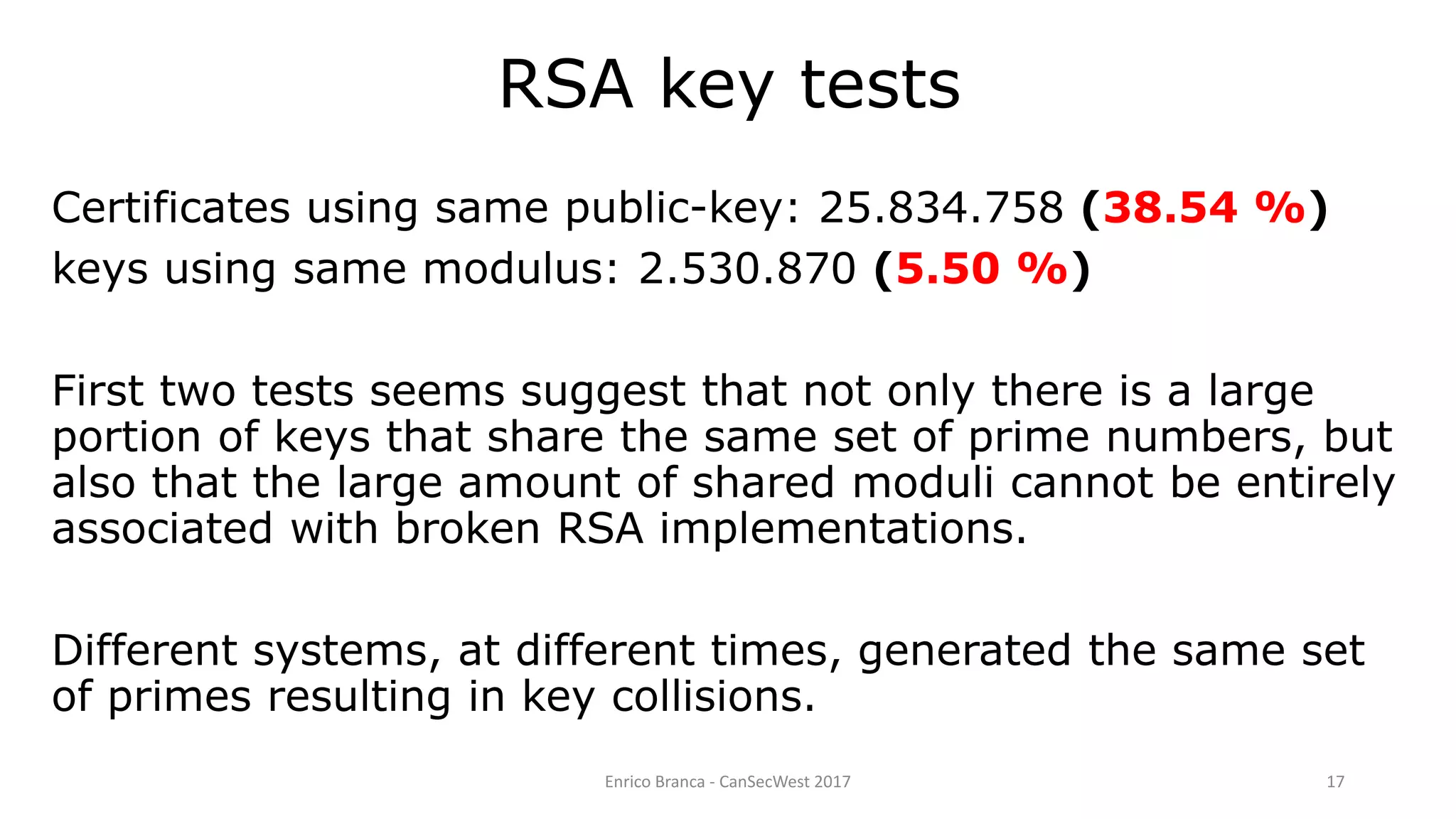
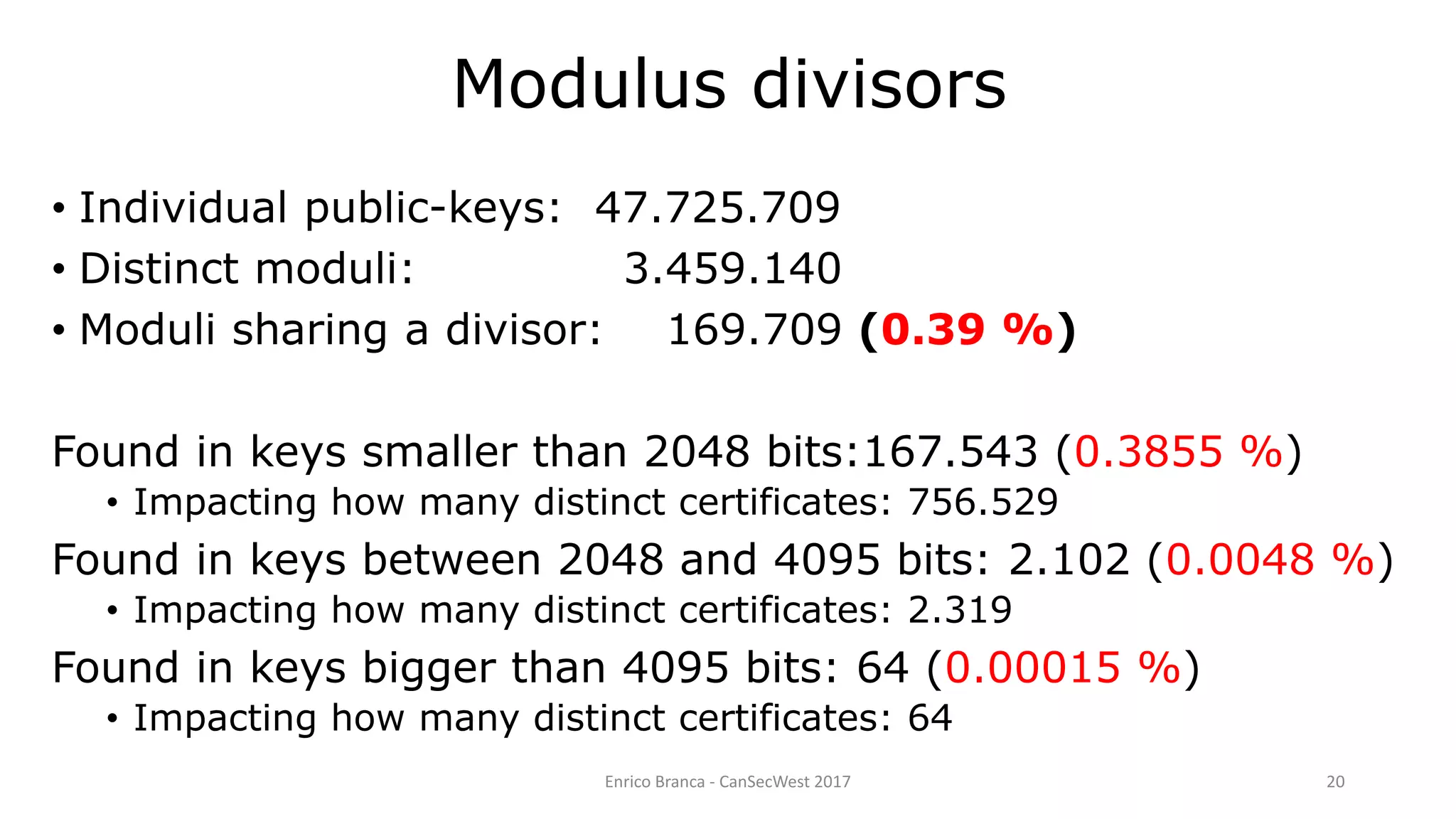
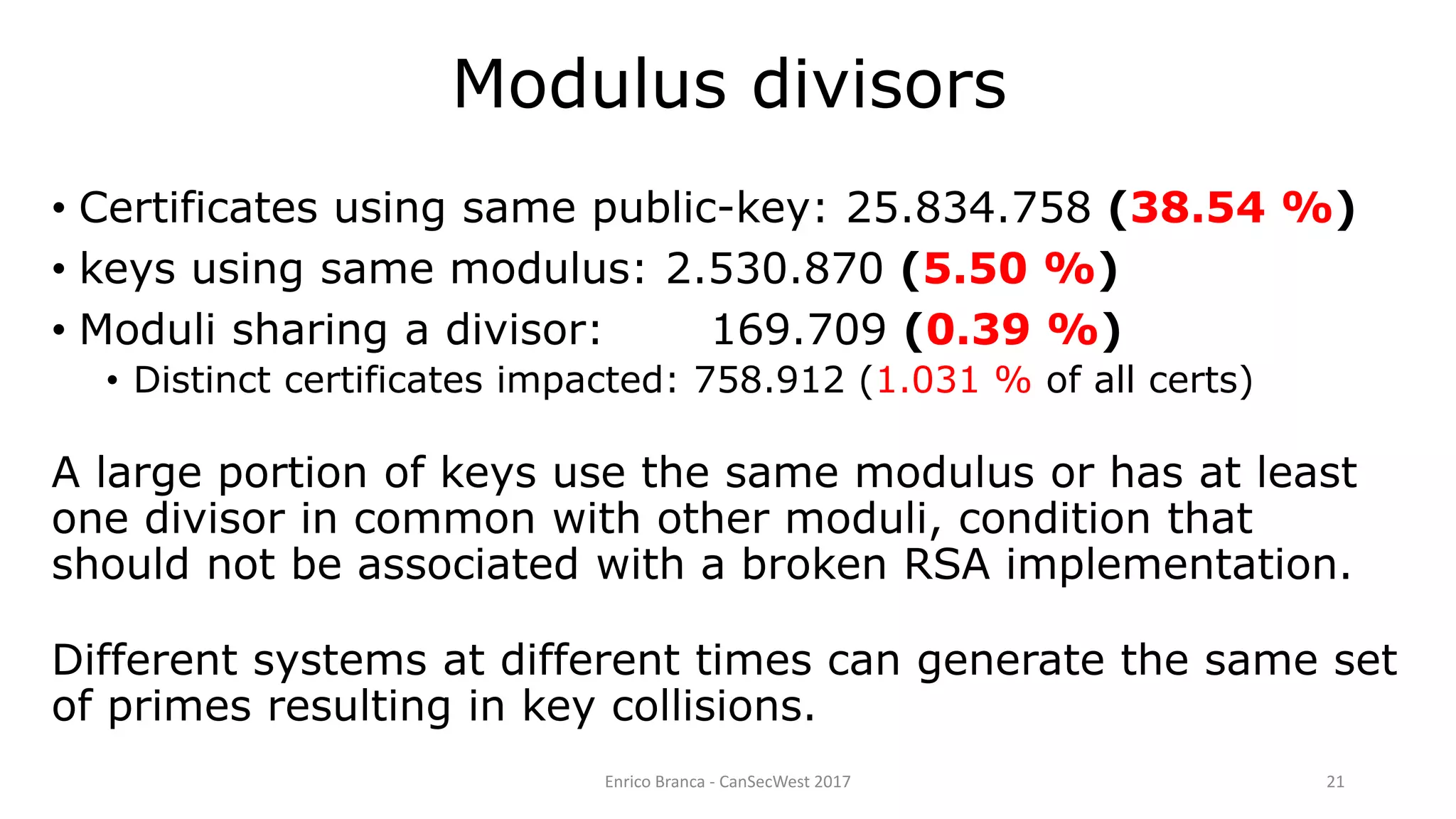
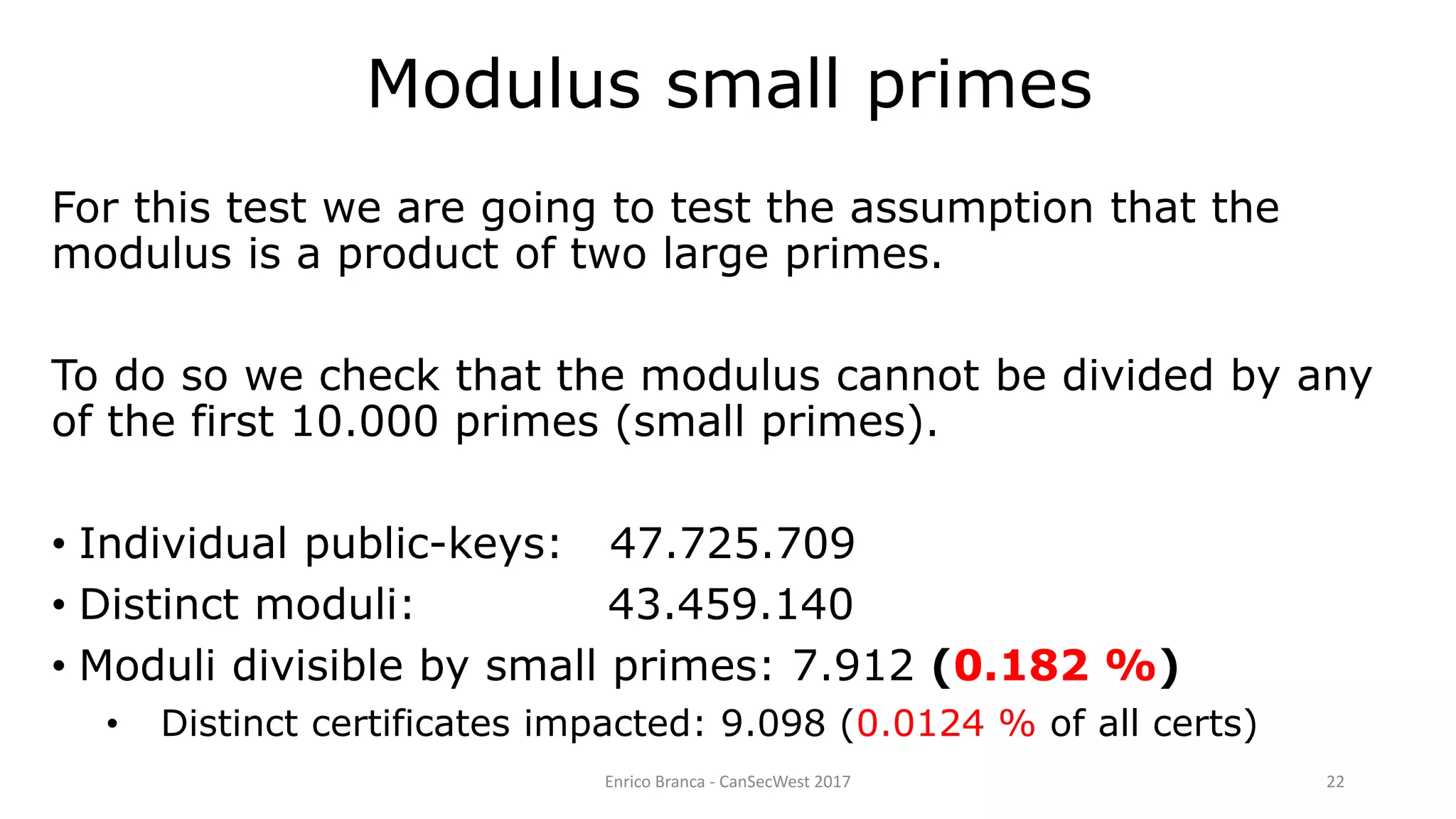
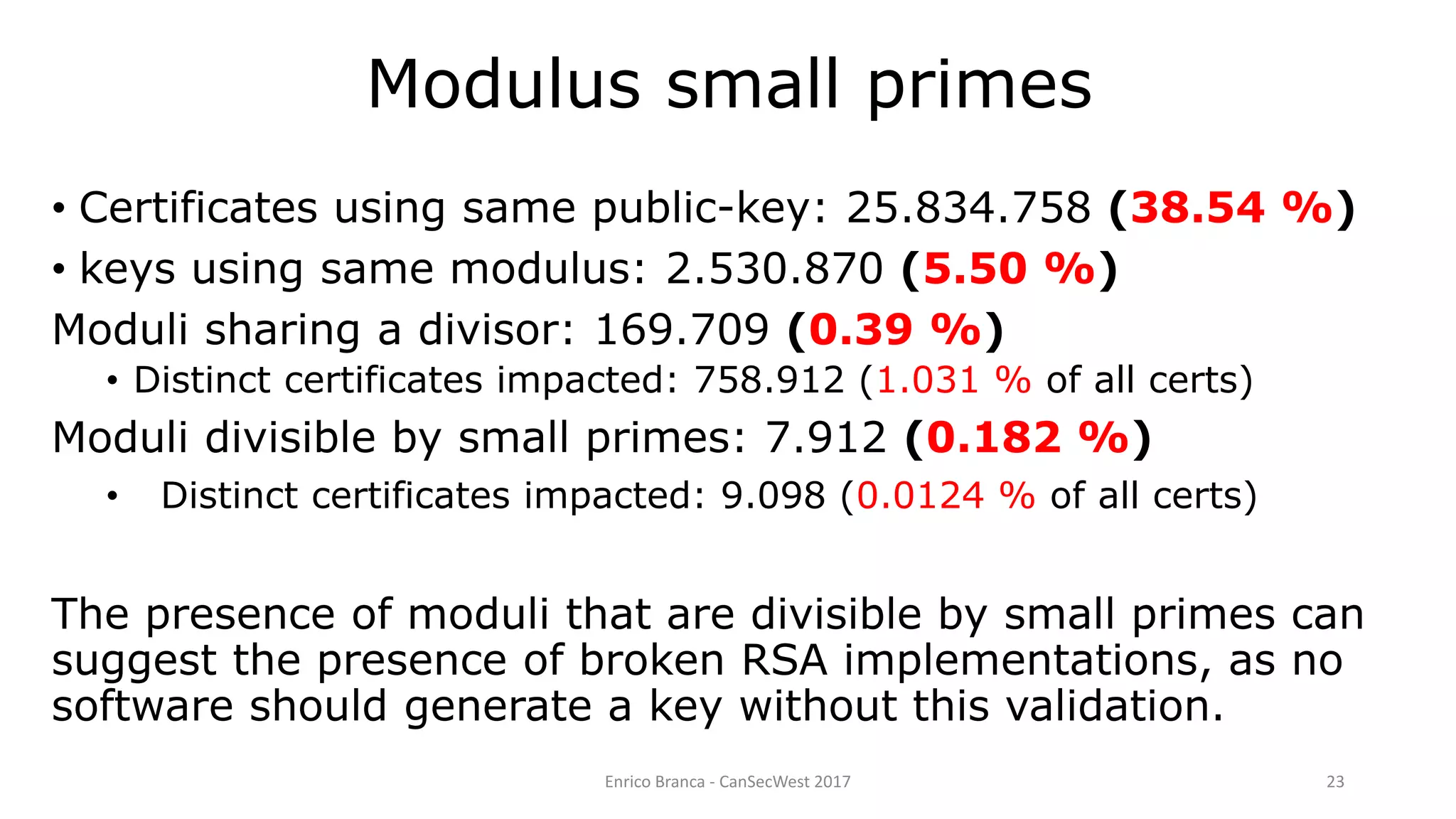
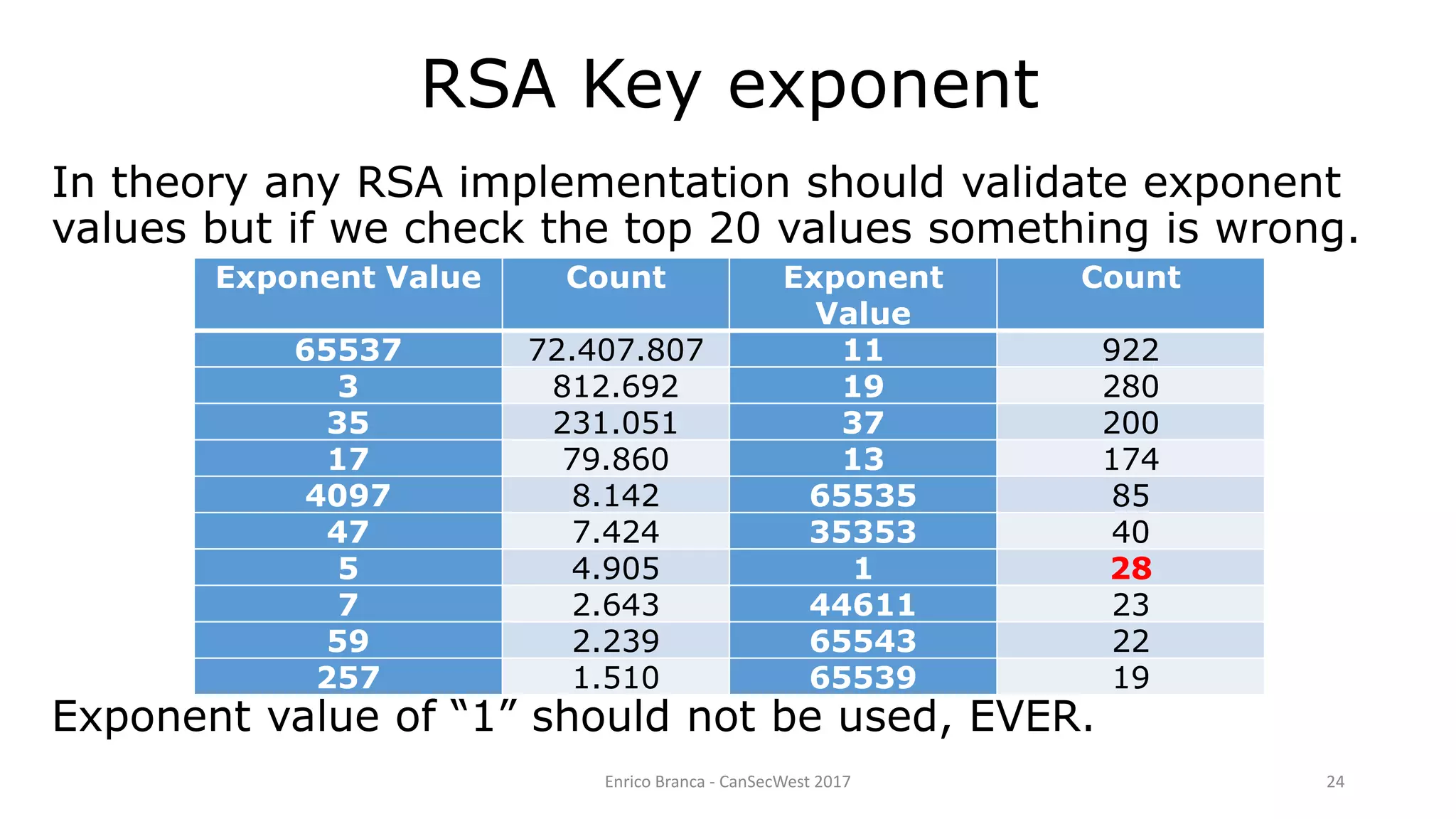
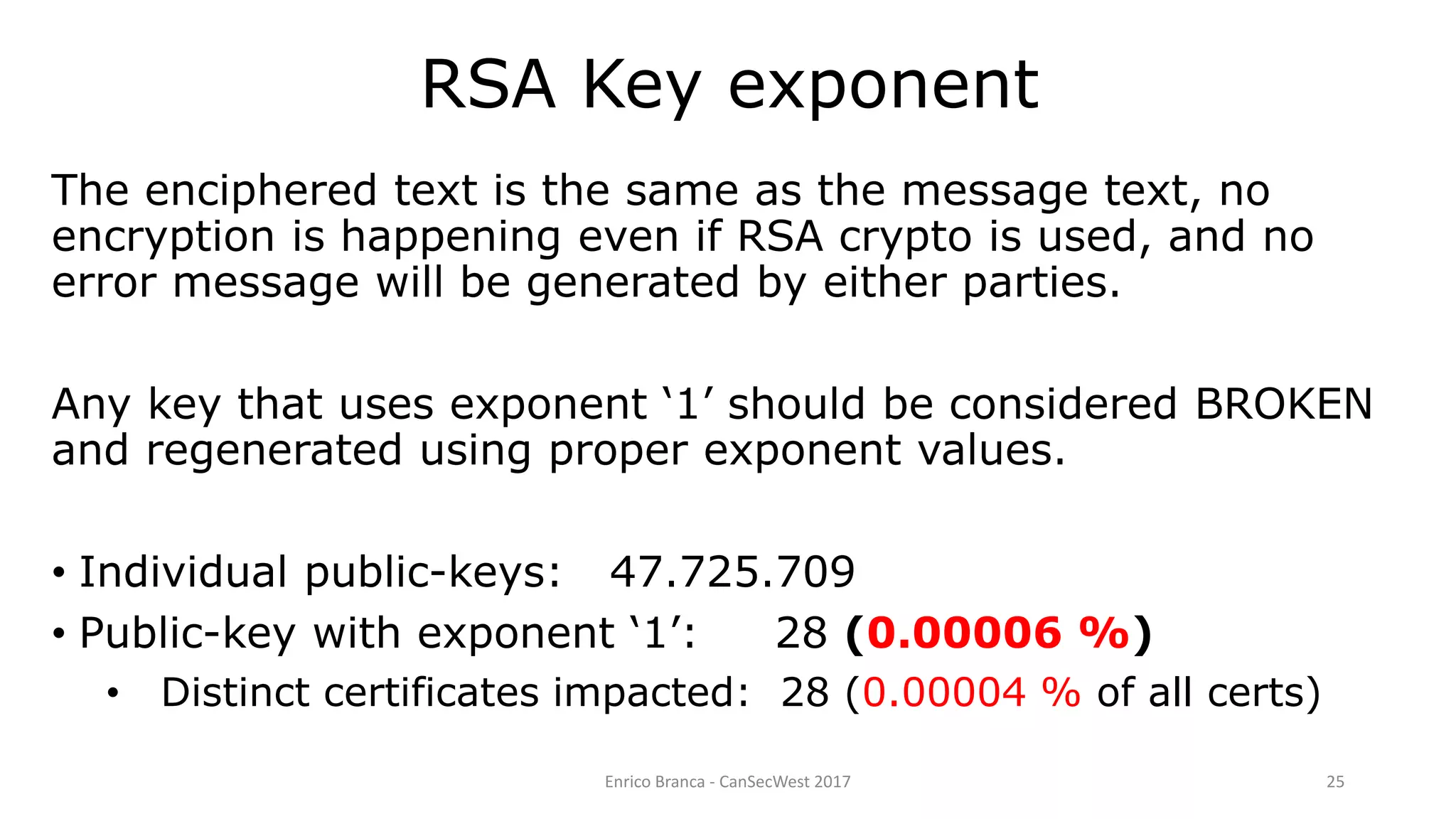
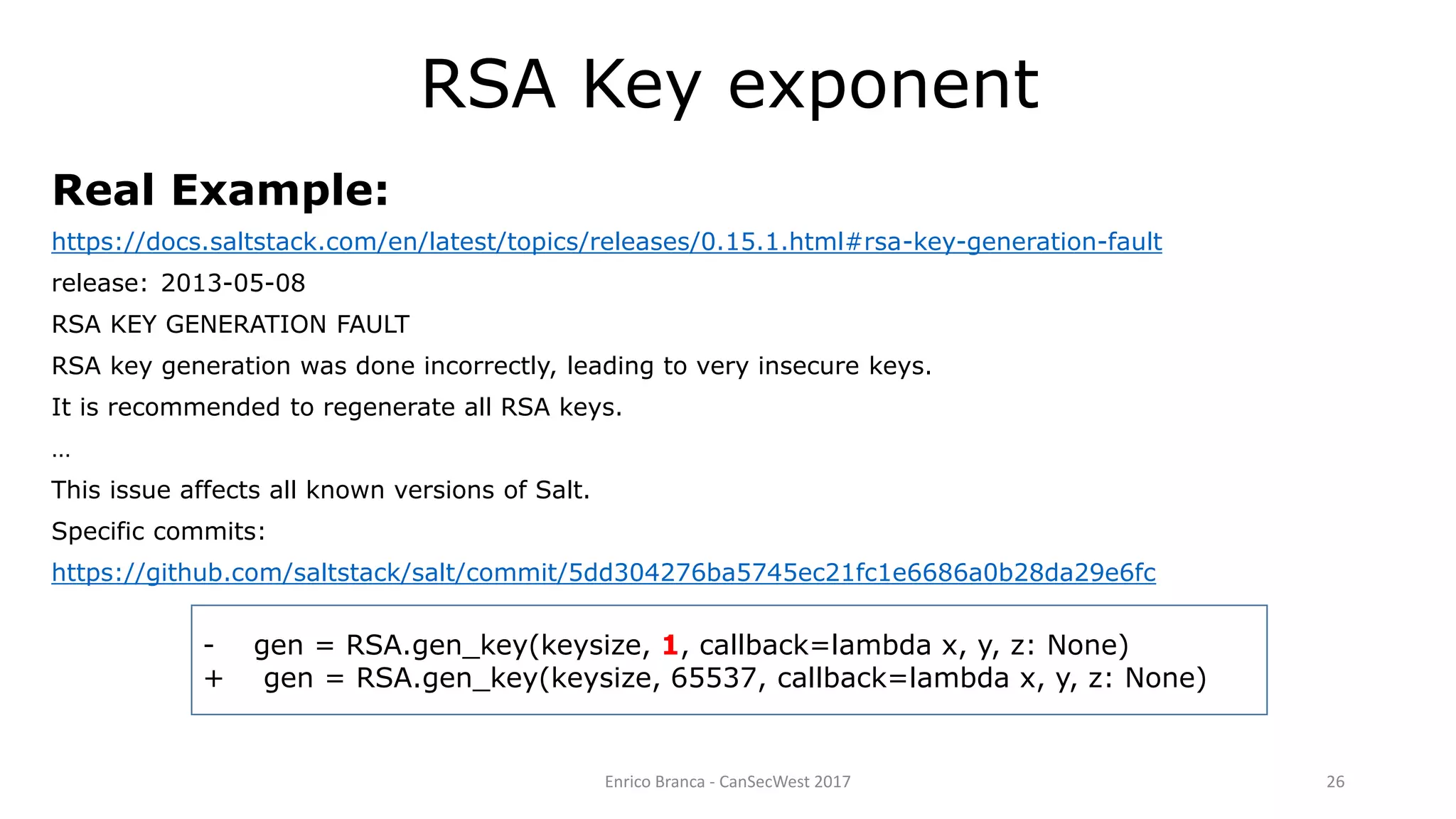
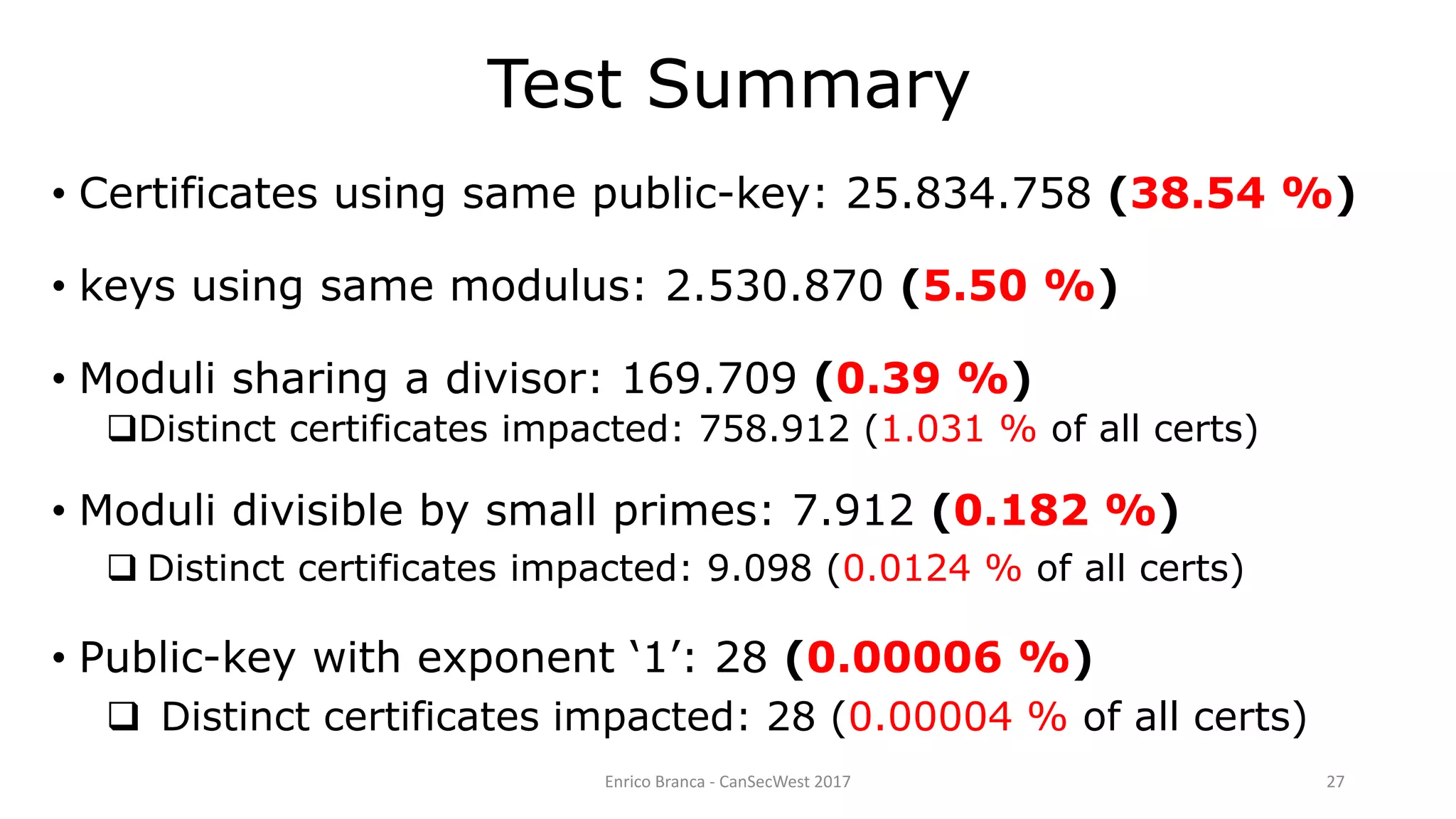
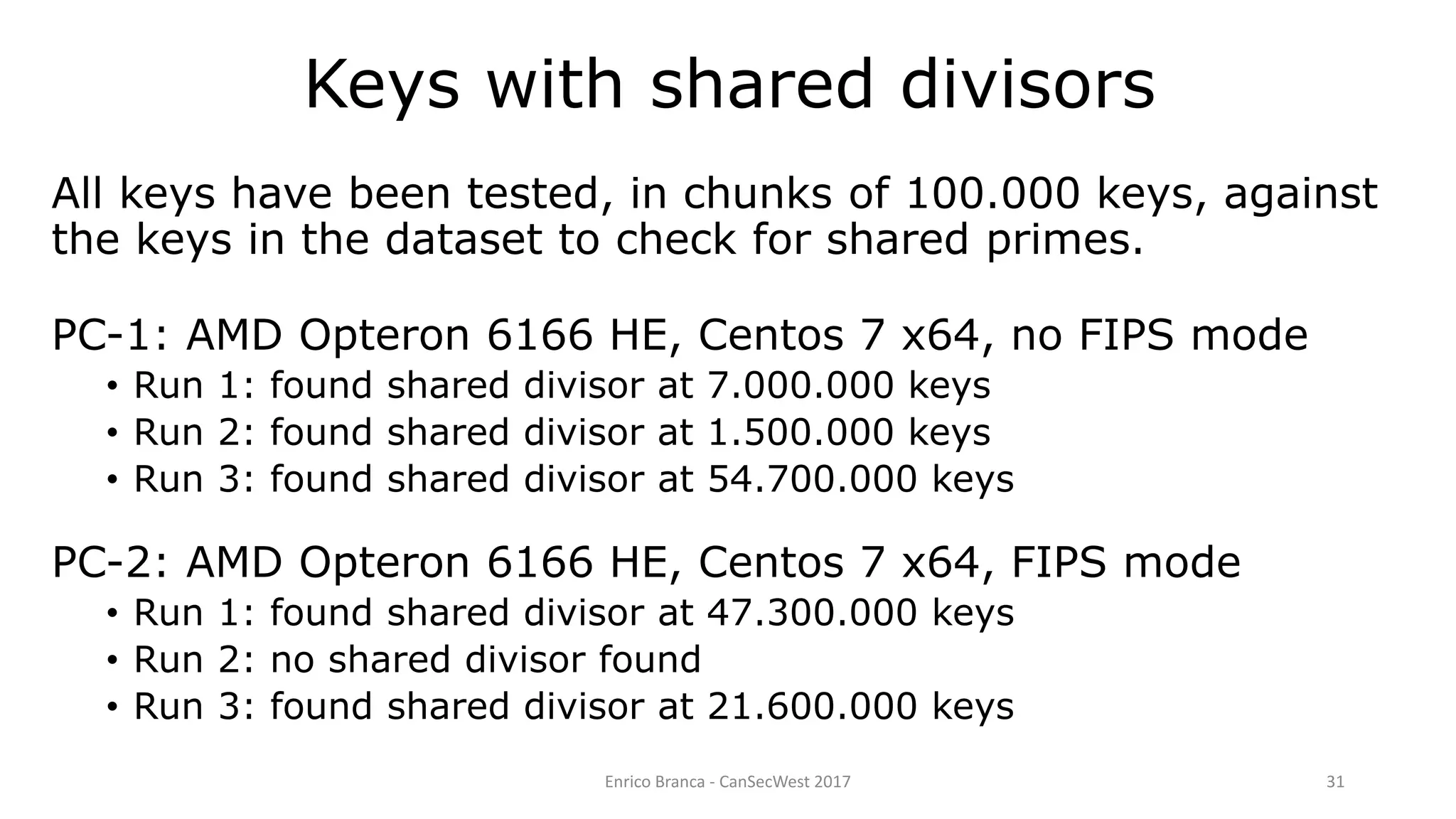
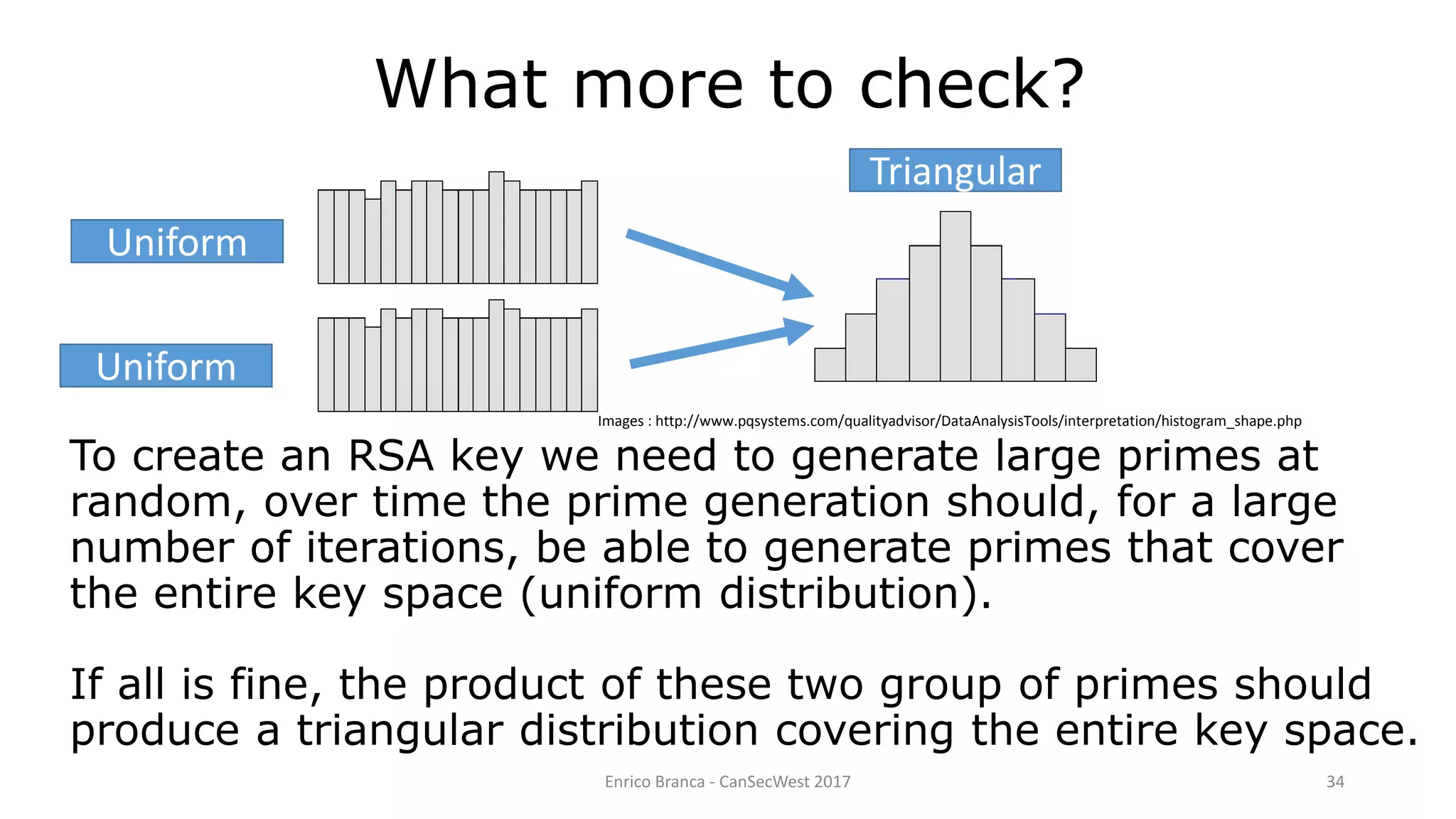
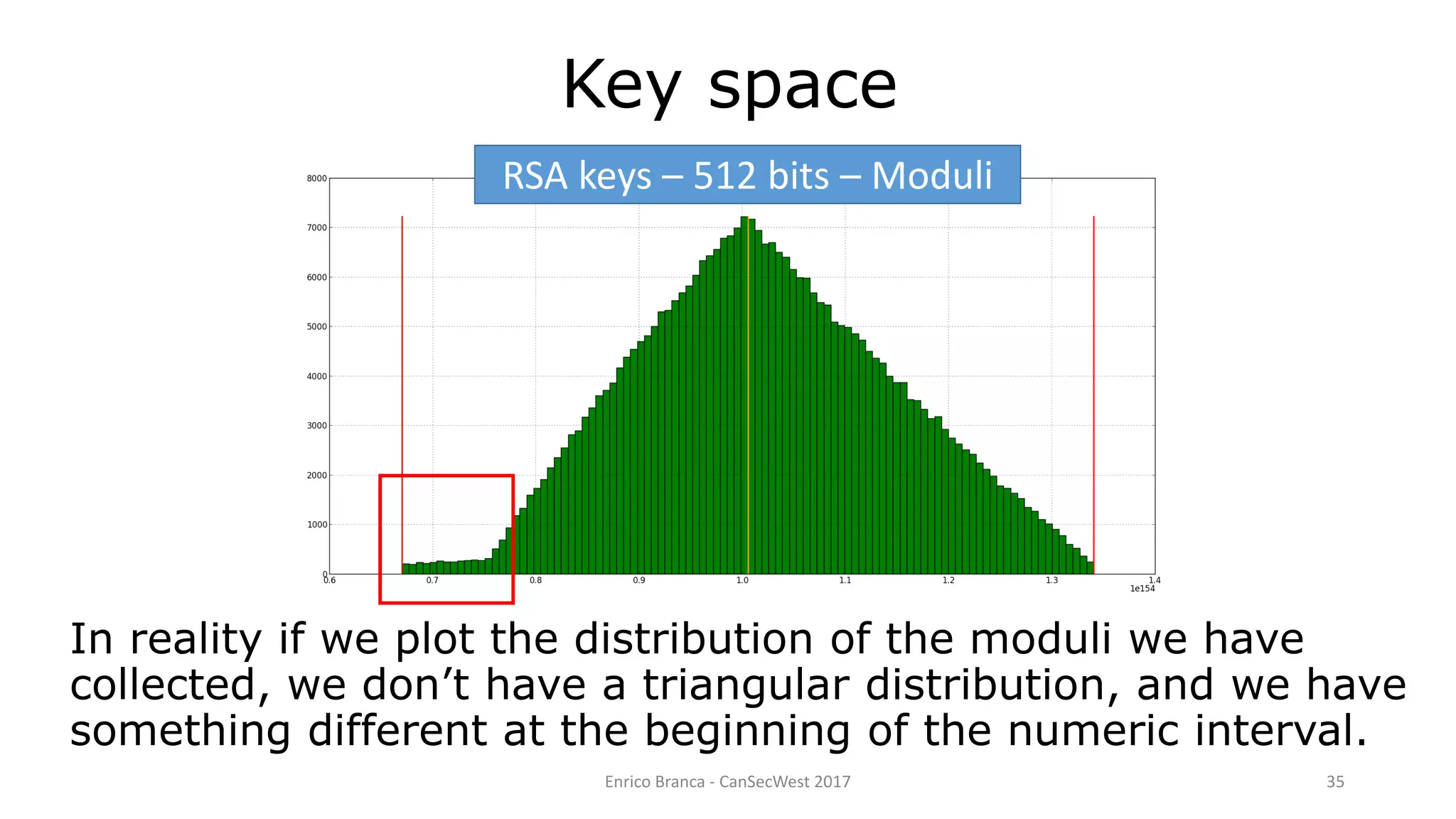
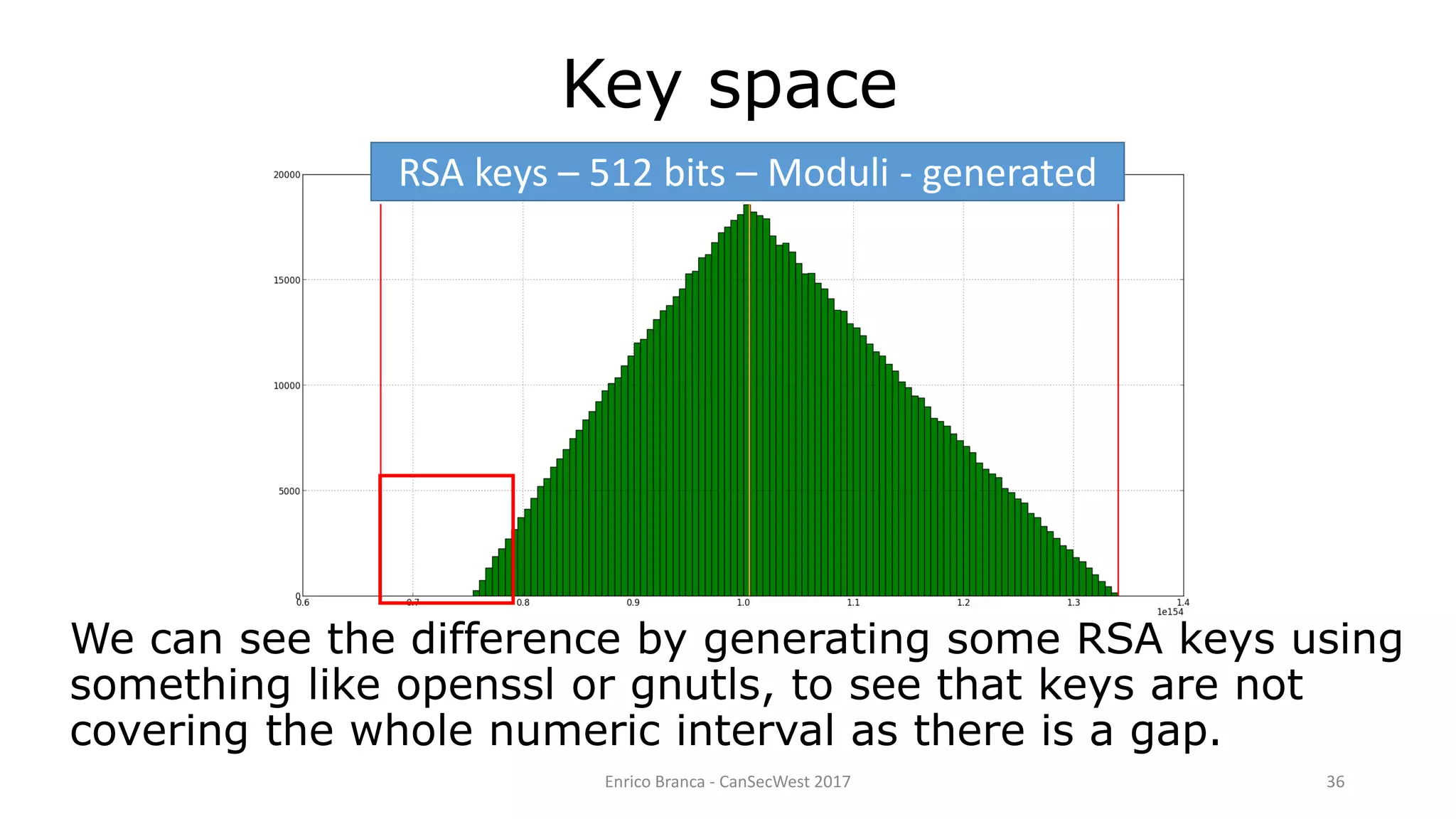
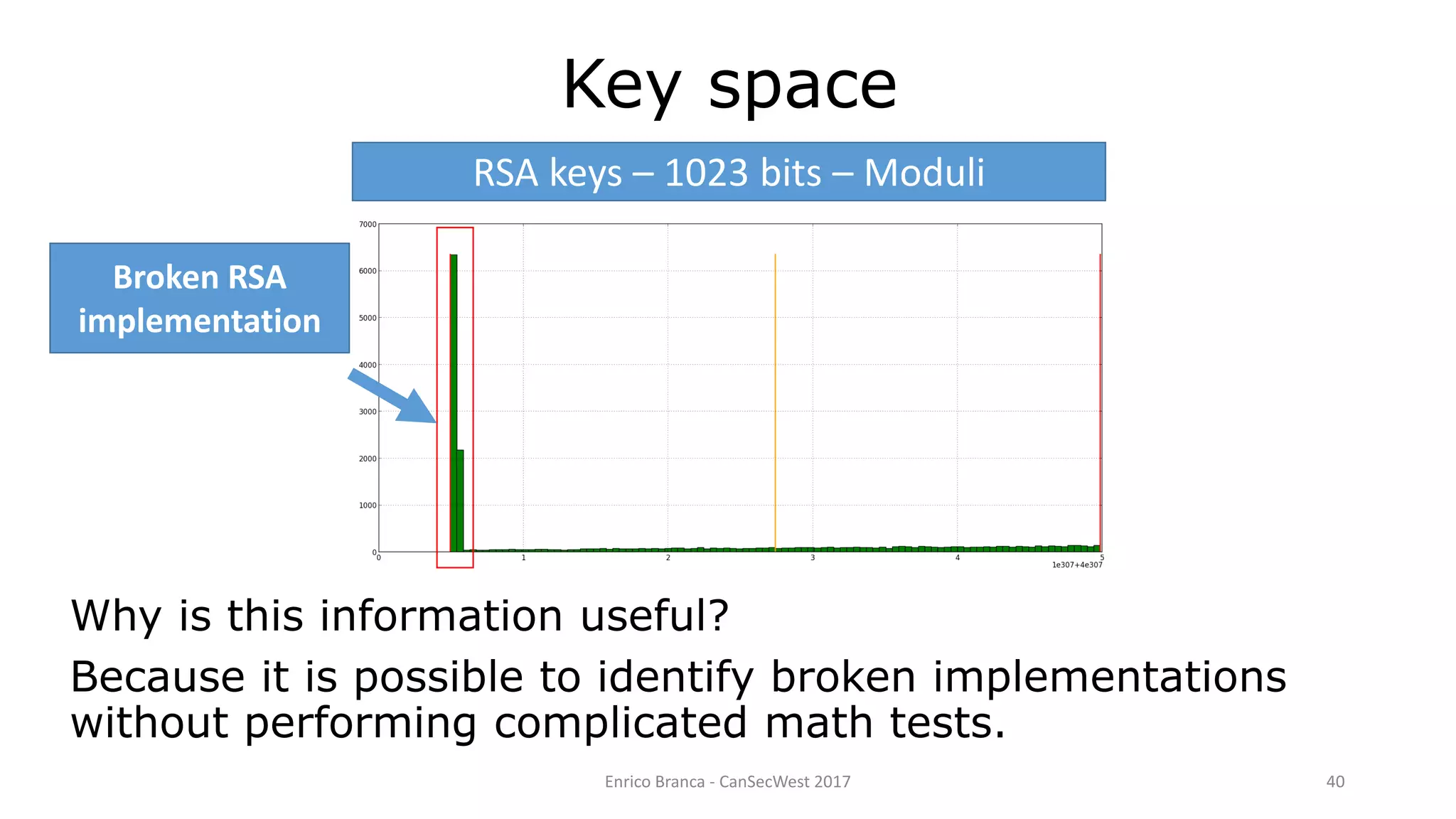
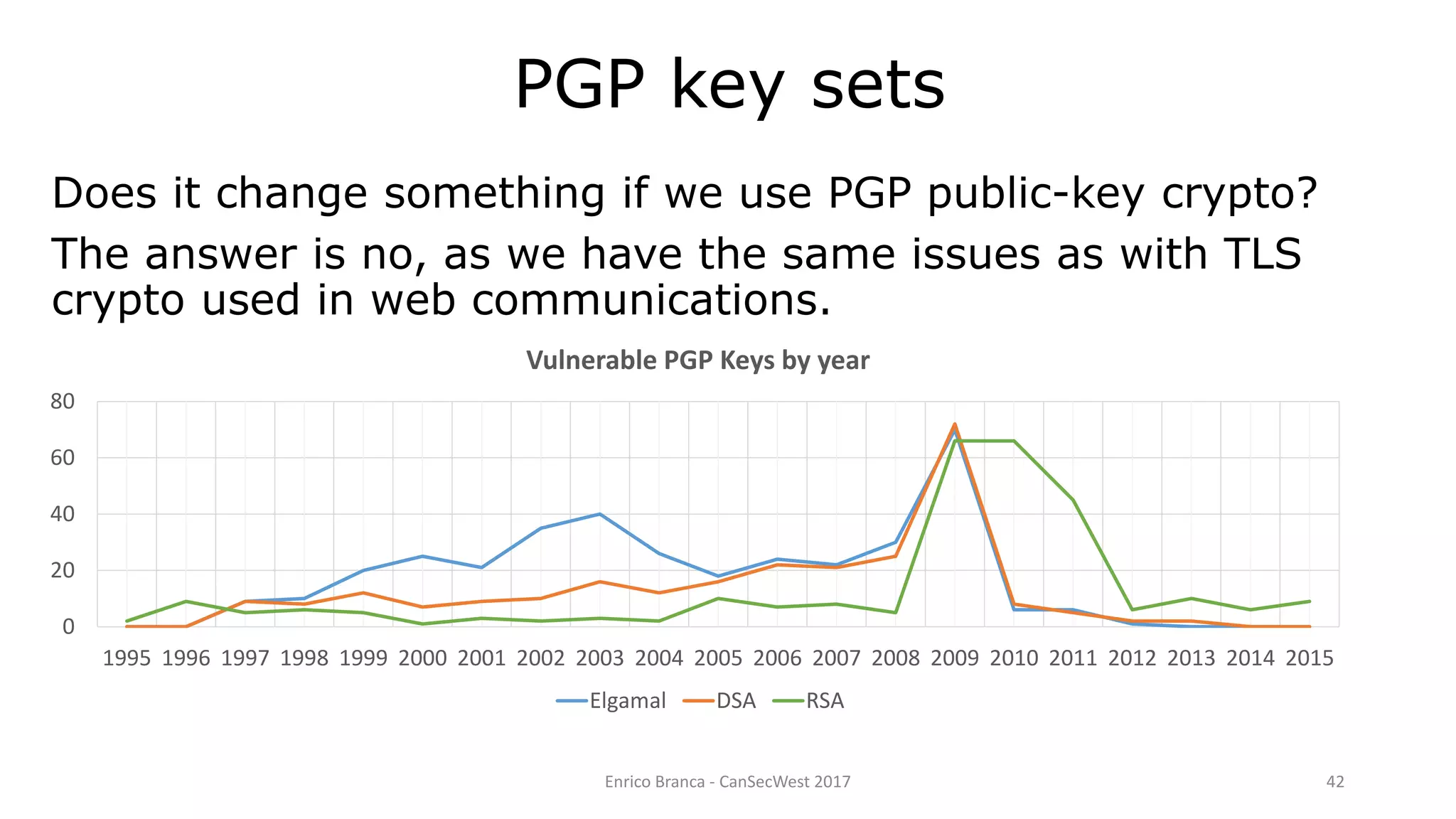
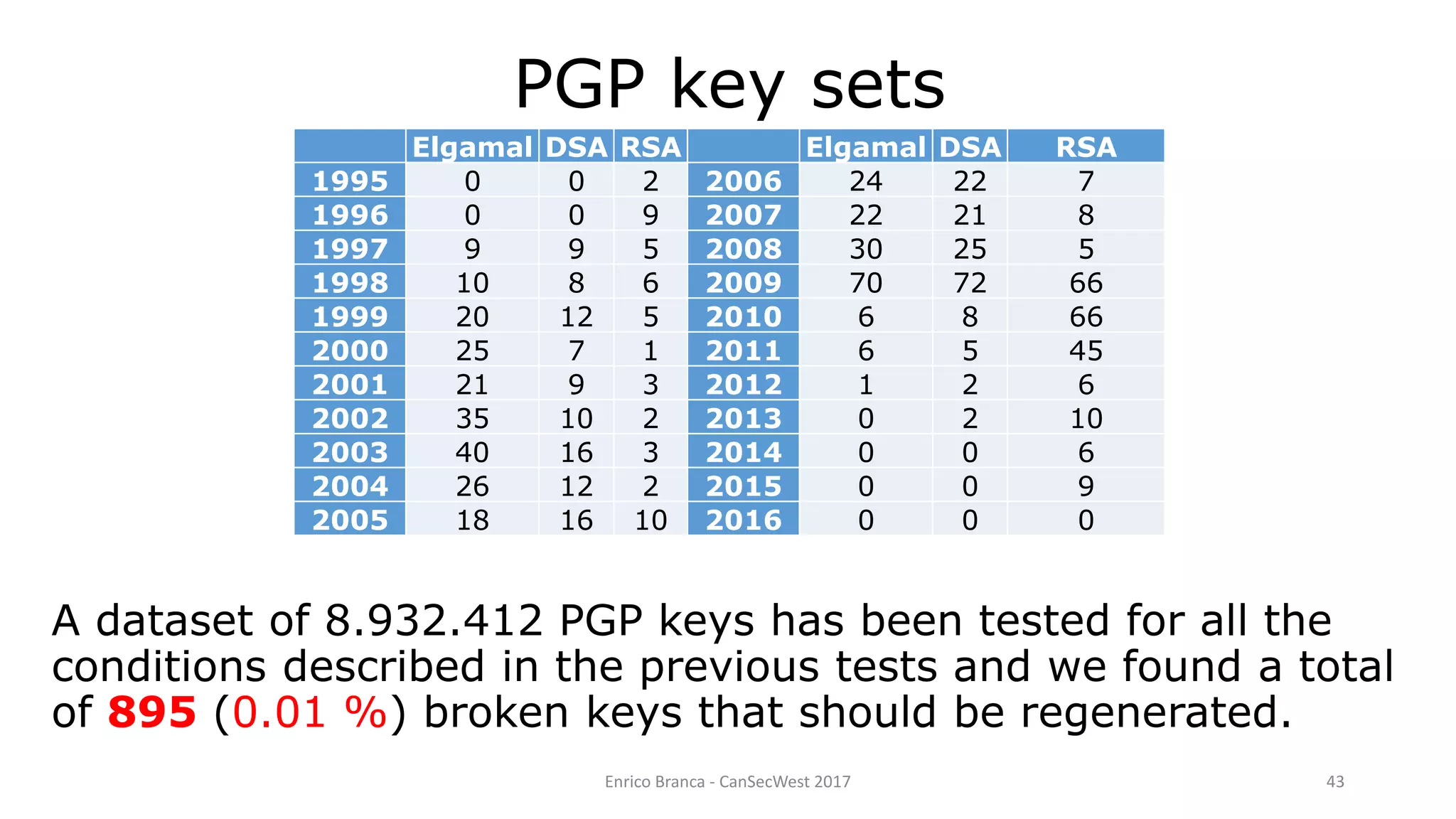
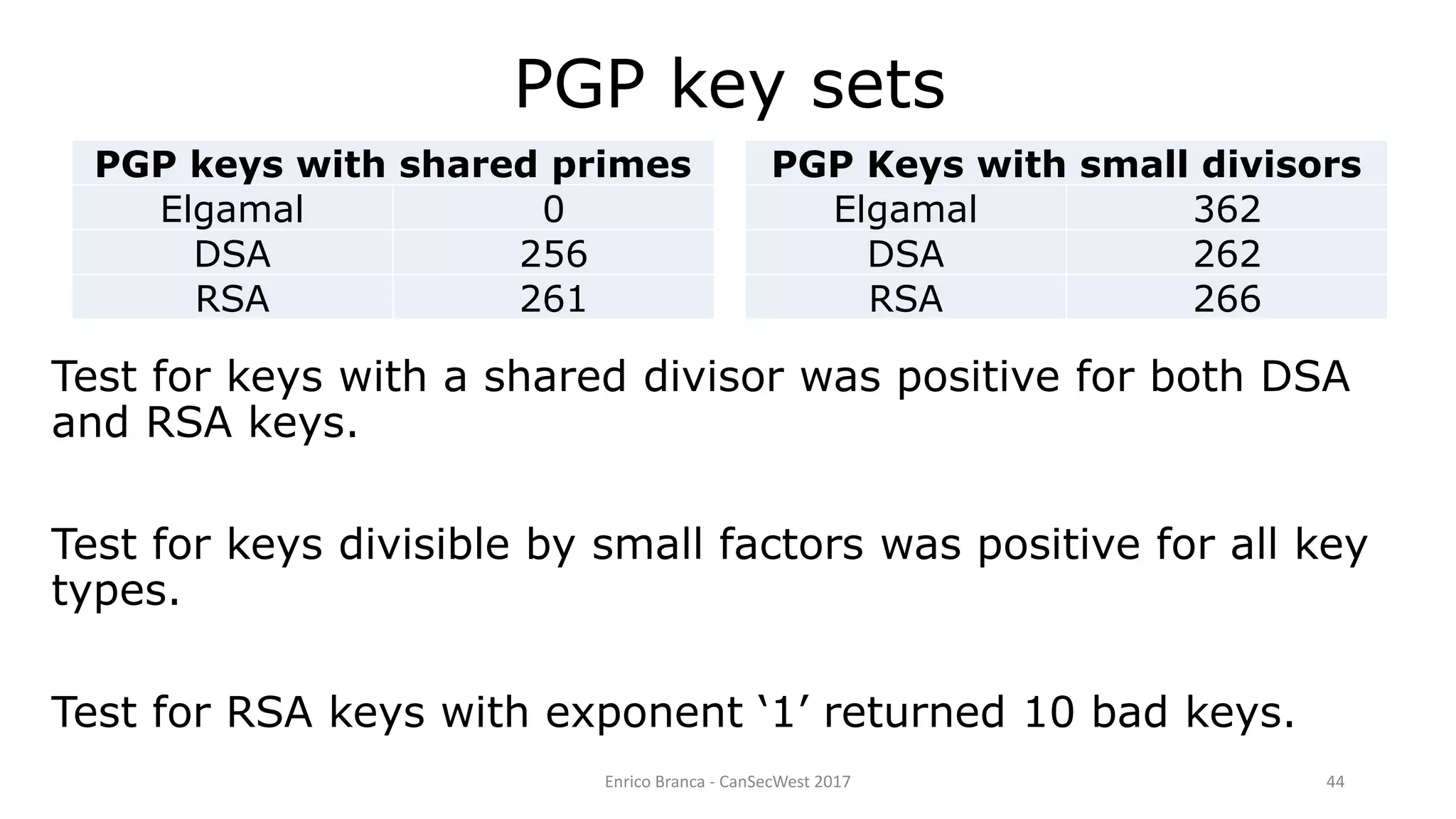
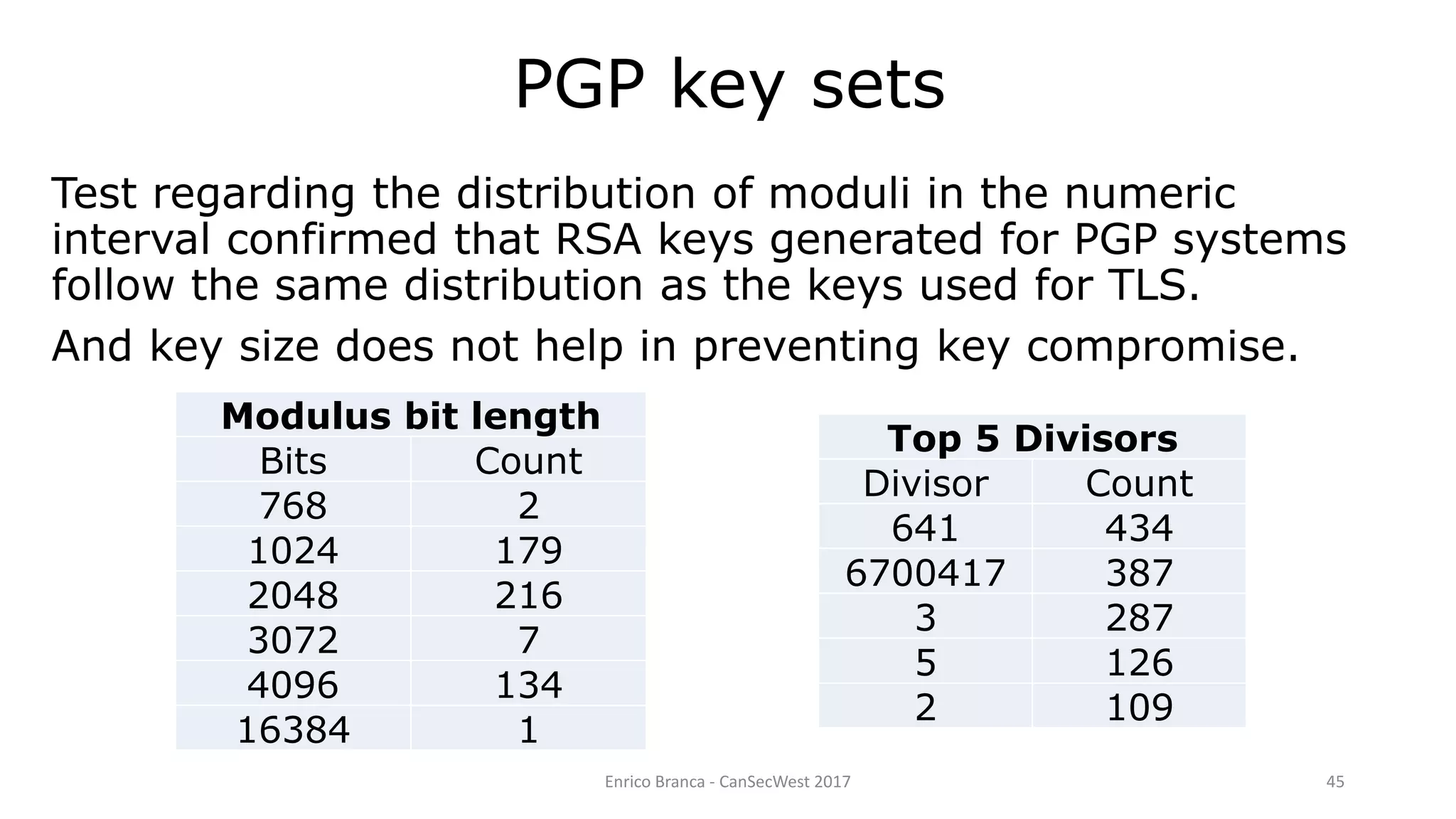
The document discusses analyzing over 73 million encryption certificates to test their security. It finds that over 25 million certificates share the same public key, over 2.5 million share the same modulus, and over 750,000 share divisors, indicating weak key generation. It also finds some certificates with invalid exponents, moduli divisible by small primes, and a few with an exponent of 1, all of which make the keys insecure. The analysis shows many keys assumed to be secure may actually be vulnerable to attacks due to flaws in key generation.