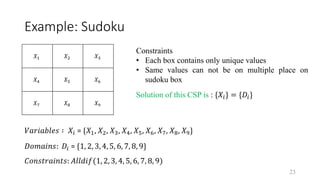
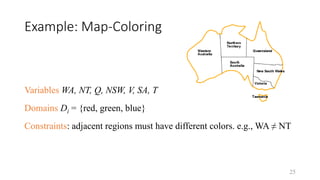
Constraint satisfaction problems (CSPs) involve assigning values to variables from given domains so that all constraints are satisfied. CSPs provide a general framework that can model many combinatorial problems. A CSP is defined by variables that take values from domains, and constraints specifying allowed value combinations. Real-world CSPs include scheduling, assignment problems, timetabling, mapping coloring and puzzles. Examples provided include cryptarithmetic, Sudoku, 4-queens, and graph coloring.






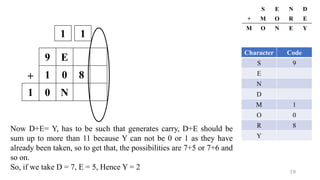
![17
+
9 E
1 0
1 0 N
+
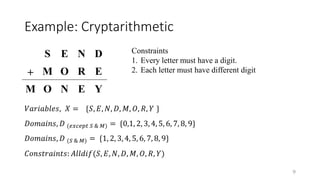
S E N D
M O R E
M O N E Y
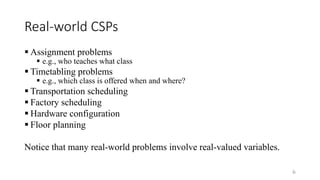
Character Code
S 9
E
N
D
M 1
O 0
R
Y
1
Expression:
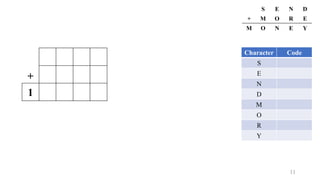
1. E + 1 = N [ N & E differ by 1 ]
2. N + R (+1) = E + 10 [ (+1) will be considered only if needed ]](https://image.slidesharecdn.com/constraintsatisfactionproblem-210628171638/85/Constraint-Satisfaction-Problem-CSP-Cryptarithmetic-Graph-Coloring-4-Queen-Sudoku-17-320.jpg)
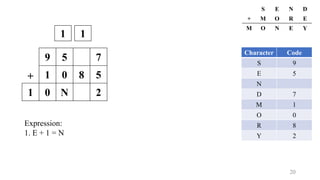
![18
+
9 E
1 0
1 0 N
+
S E N D
M O R E
M O N E Y
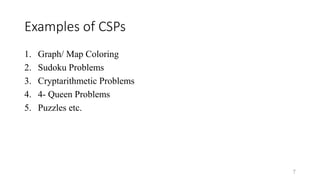
Character Code
S 9
E
N
D
M 1
O 0
R 8
Y
1
Expression:
1. E + 1 = N [ N & E differ by 1 ]
2. N + R (+1) = E + 10 [ (+1) will be considered only if needed ]
Substituting the values:
E + 1 + R (+1) = E + 10
Hence, R (+1) = 9
If we do not consider carry then
R must be 9 but which is not
possible because 9 has already
taken, so R might be 8.](https://image.slidesharecdn.com/constraintsatisfactionproblem-210628171638/85/Constraint-Satisfaction-Problem-CSP-Cryptarithmetic-Graph-Coloring-4-Queen-Sudoku-18-320.jpg)