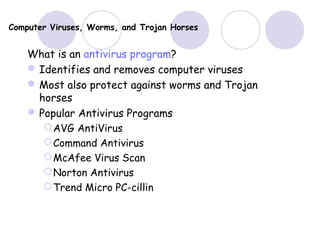
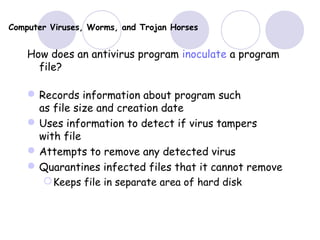
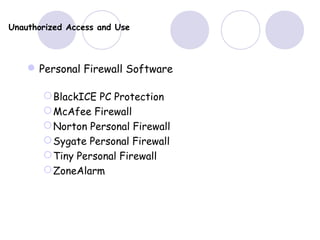
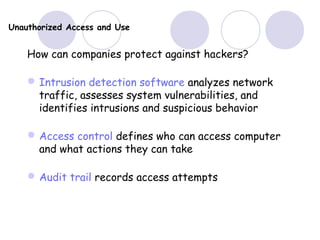
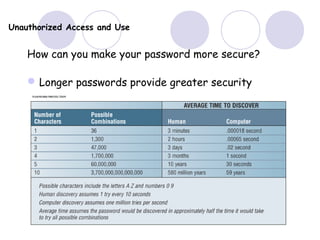
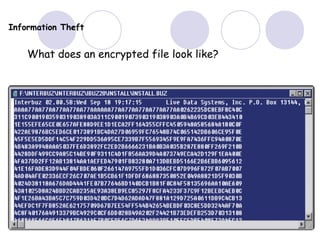
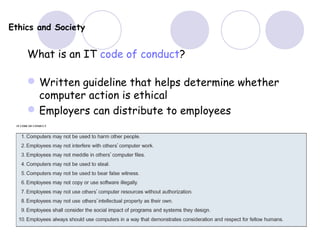
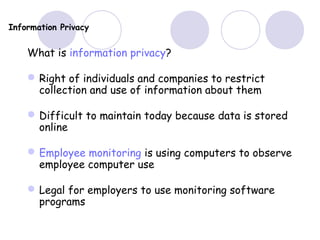
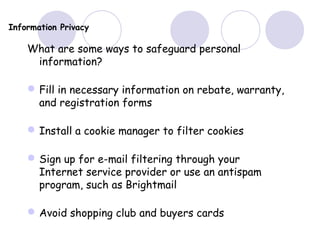
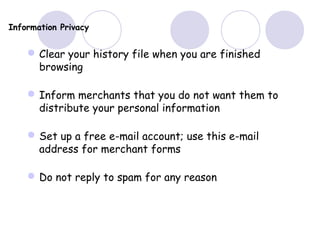
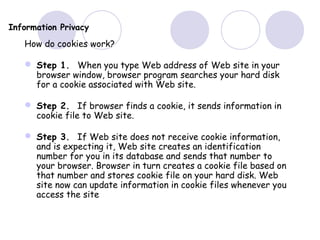
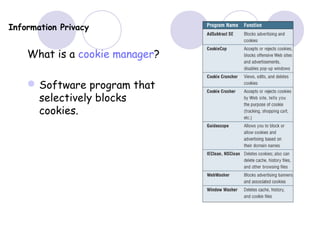
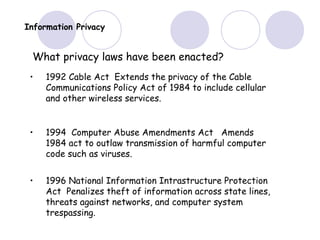
This document discusses computer security, privacy, and ethics. It covers types of security risks like viruses, unauthorized access, and hardware theft. It also discusses ways to protect against these risks, including installing antivirus software, using firewalls and passwords, backing up data, and encrypting sensitive information. The document also covers legal and ethical issues around topics like software piracy, privacy laws, and health concerns related to computer use.