This document provides definitions and explanations of various concepts in computer graphics:
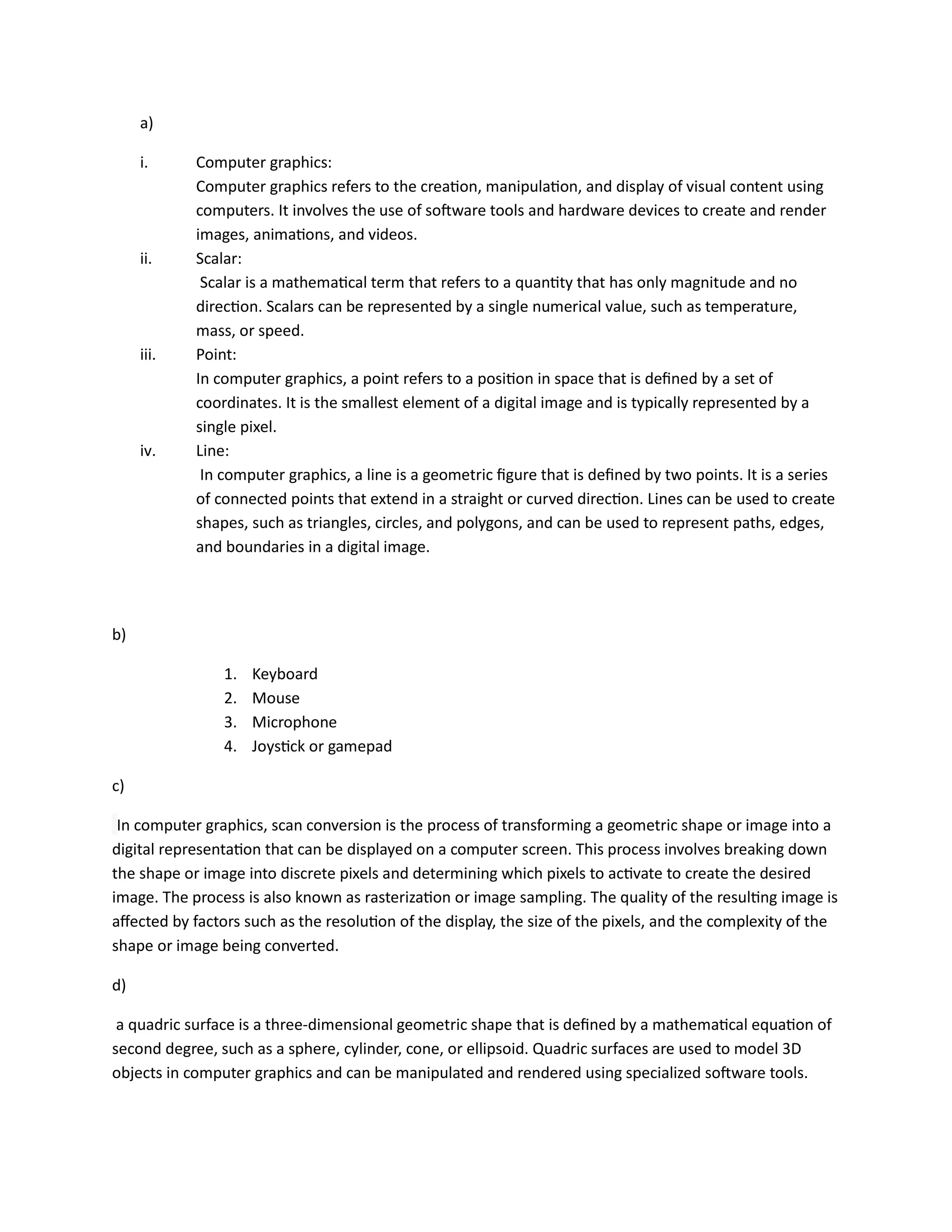
1. It defines key terms like computer graphics, scalar, point, and line and explains their meanings in the context of digital images.
2. It describes processes like scan conversion and different types of displays like raster scan and random scan displays.
3. It also covers topics such as color models, plotters, frame buffers, BRDF functions, and image file formats.