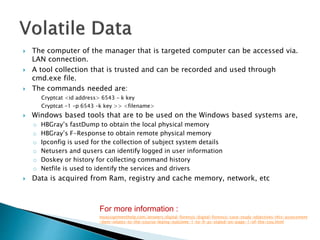
The document outlines a digital forensic investigation plan for a global finance company, detailing the need for a structured methodology, team resources, and tools required for data collection and analysis. Key steps include identifying and preserving digital evidence, analyzing potential security breaches, and preparing a comprehensive report summarizing findings. The document emphasizes the importance of maintaining data integrity and employing skilled personnel throughout the investigation process.