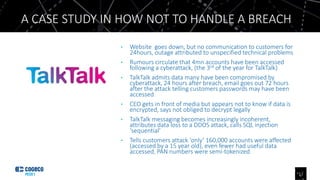
Daniel Beazer authored an article identifying five technology shibboleths for 2017. The article discusses how: (1) not all workloads will move to the public cloud, as some organizations still require customization or sensitive data isolation; (2) while outsourcing is growing, some organizations will keep critical systems in-house; and (3) despite frequent headlines, security sometimes takes a backseat to business priorities for many organizations. The article also analyzes a case study of how TalkTalk in the UK poorly handled a data breach.