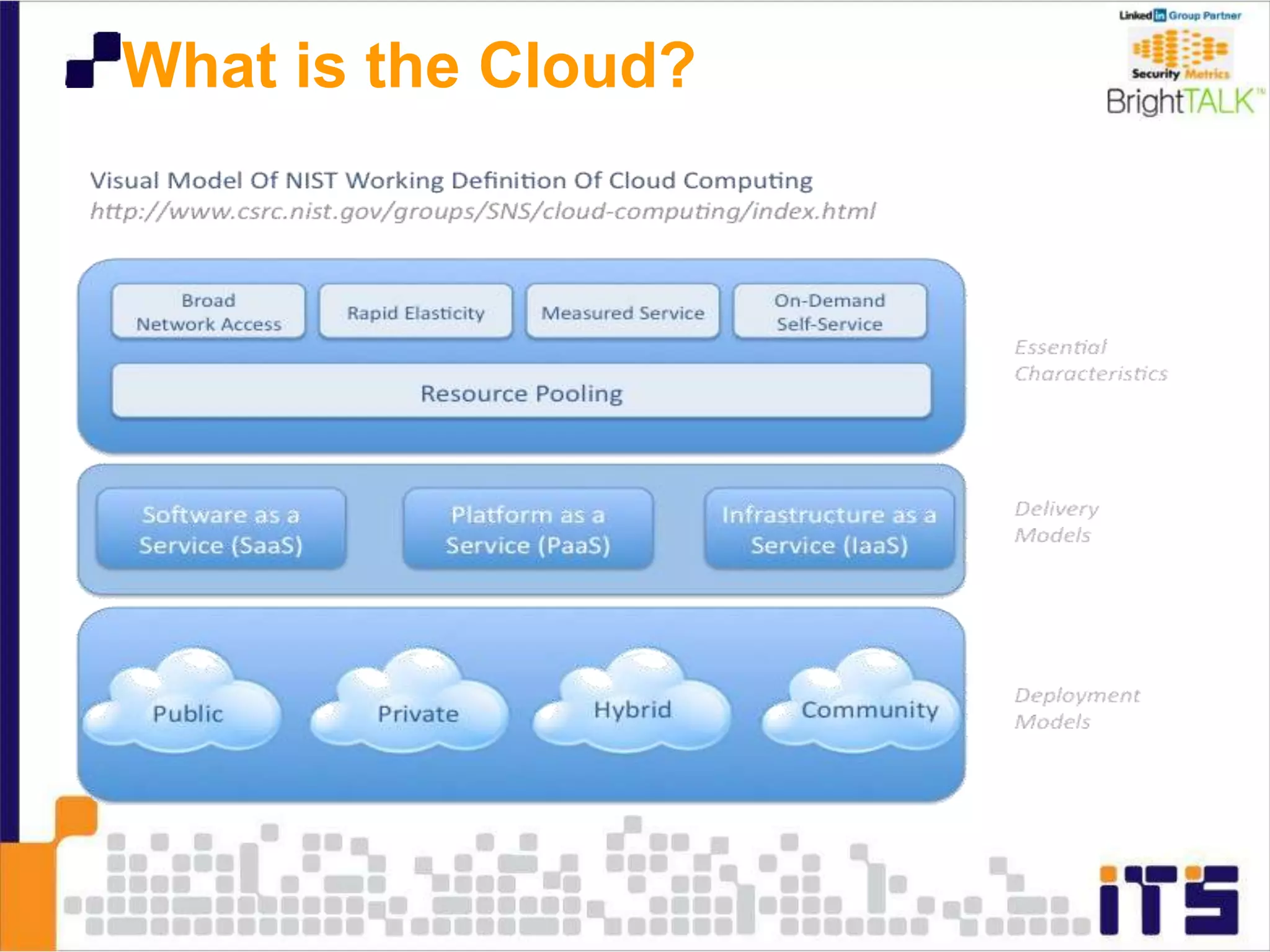
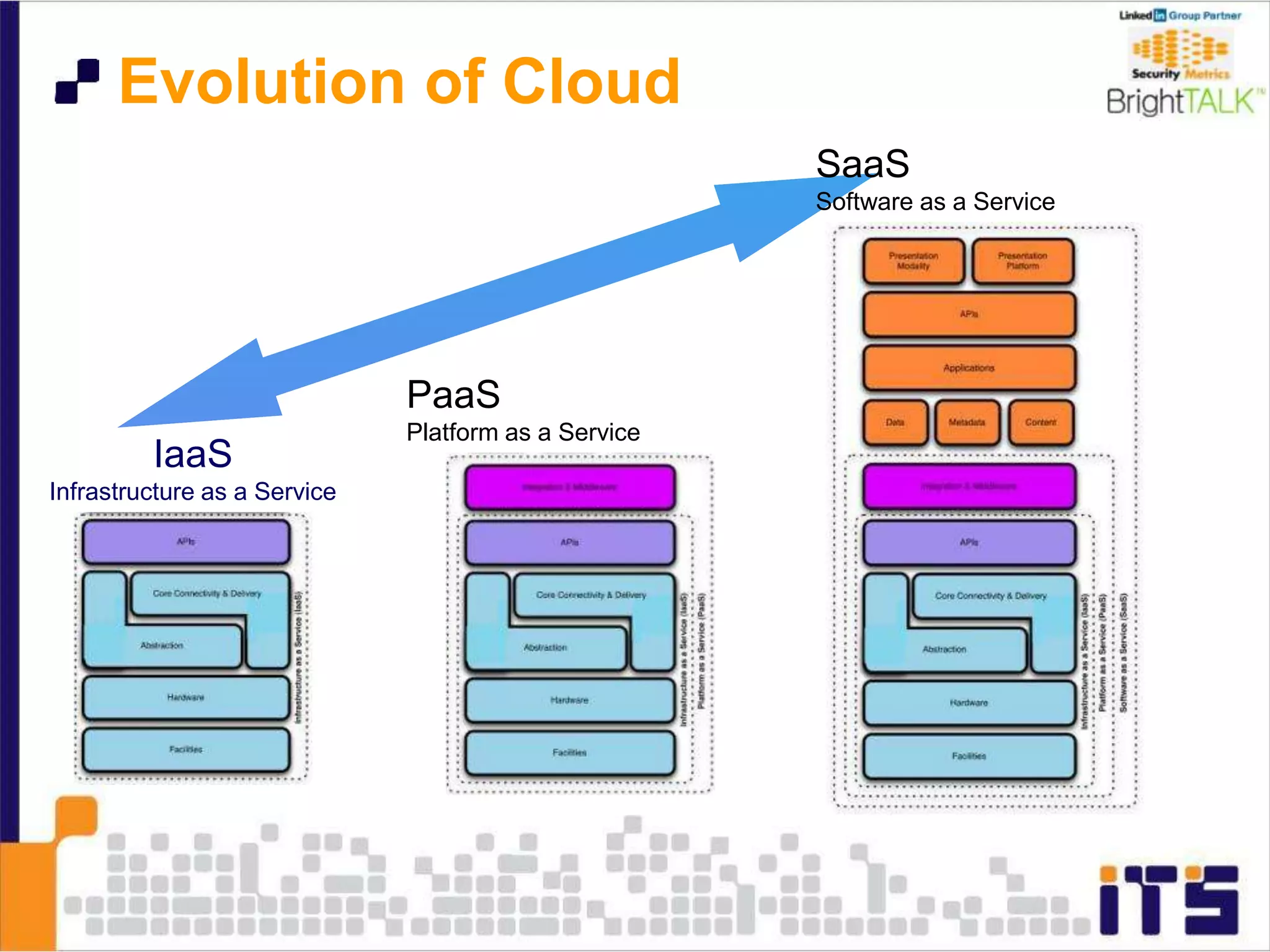
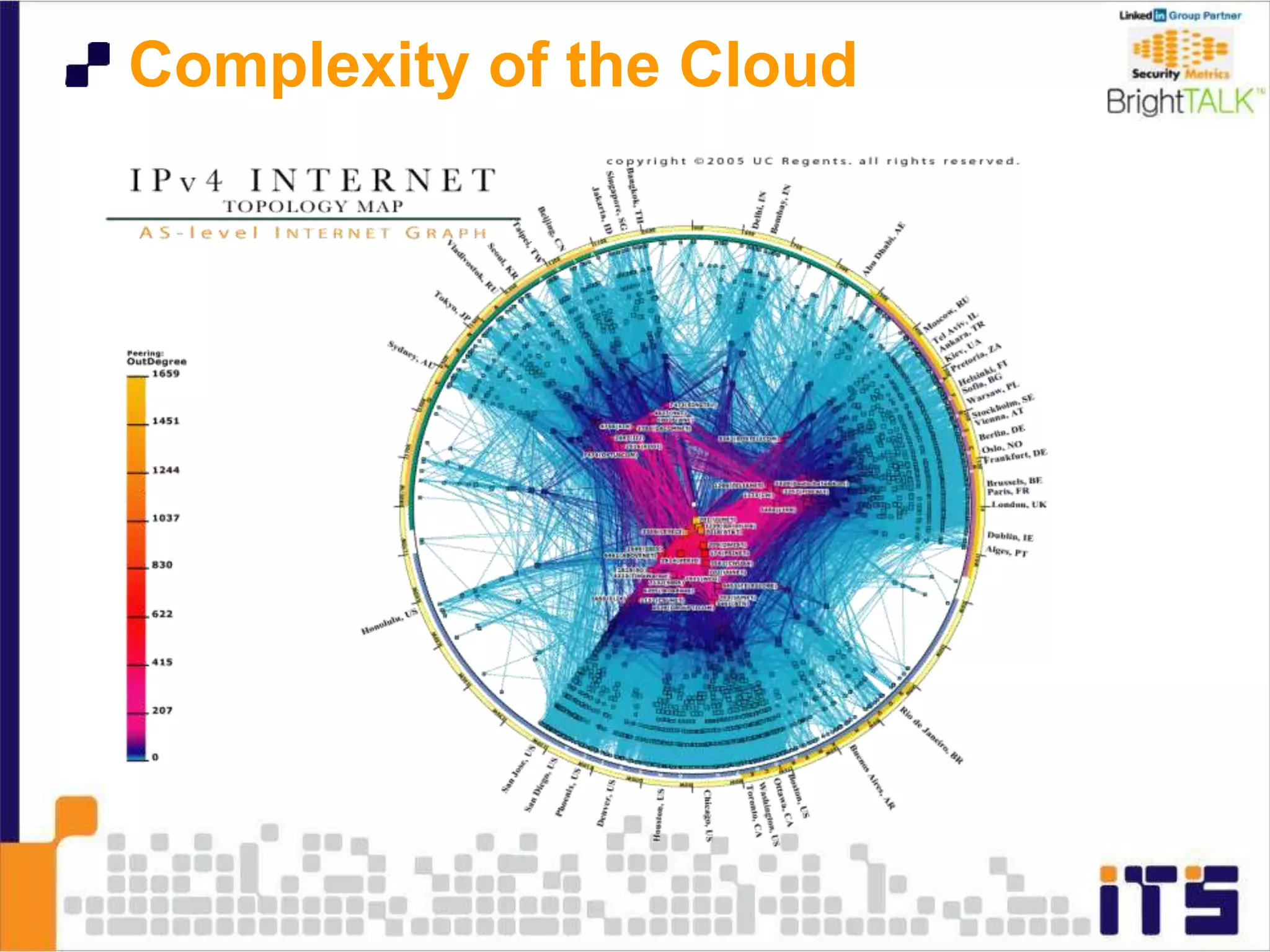
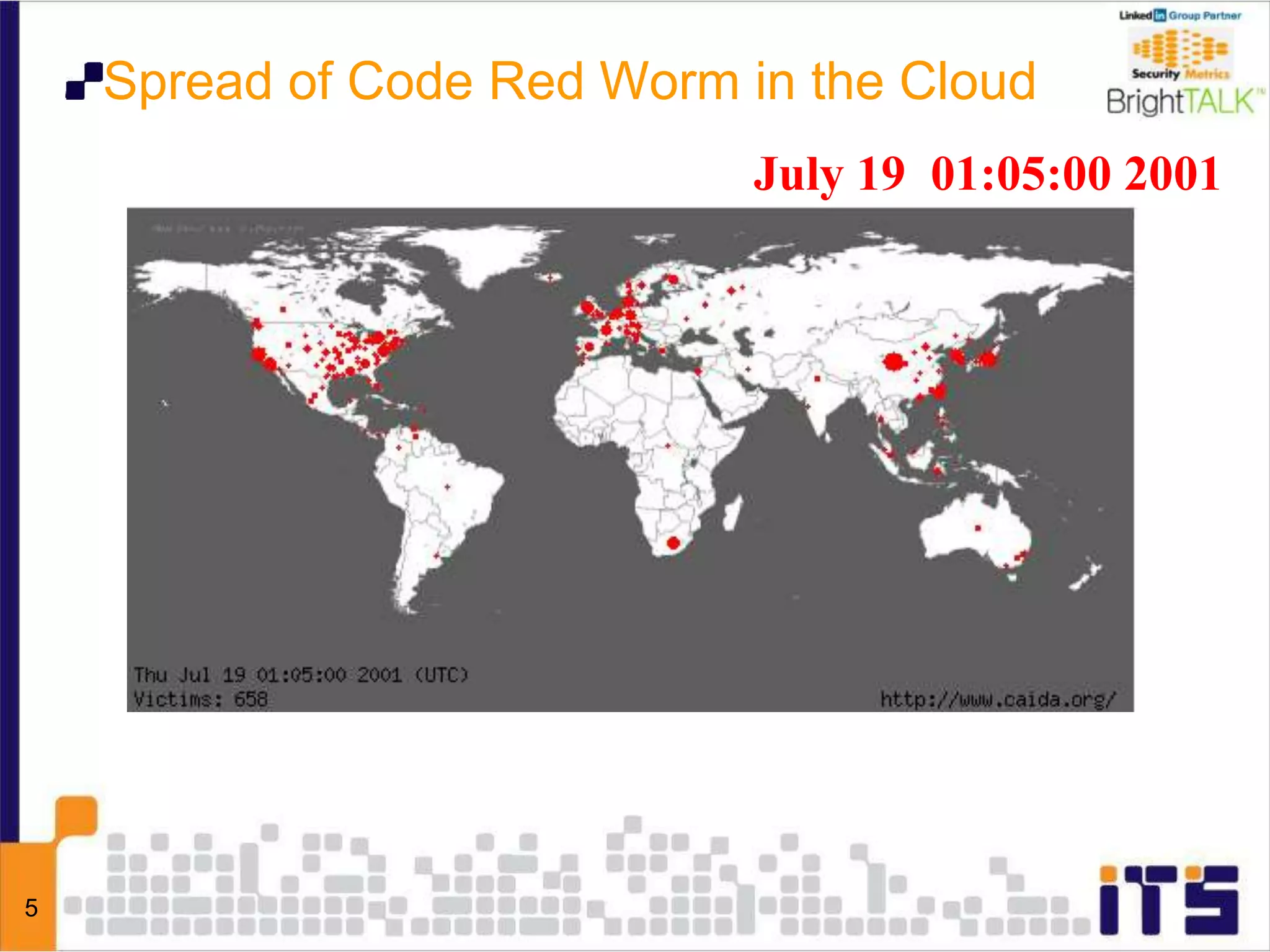
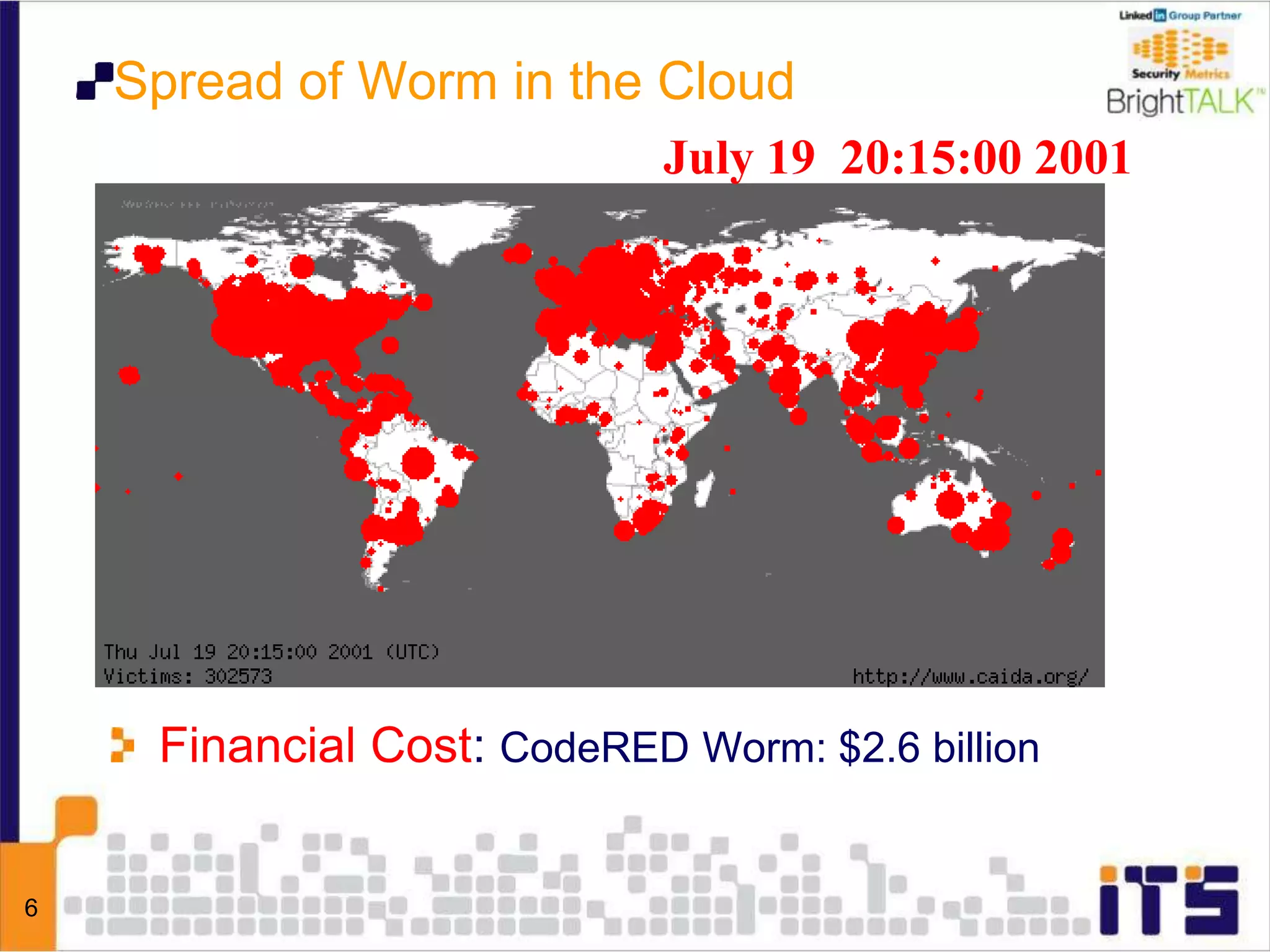
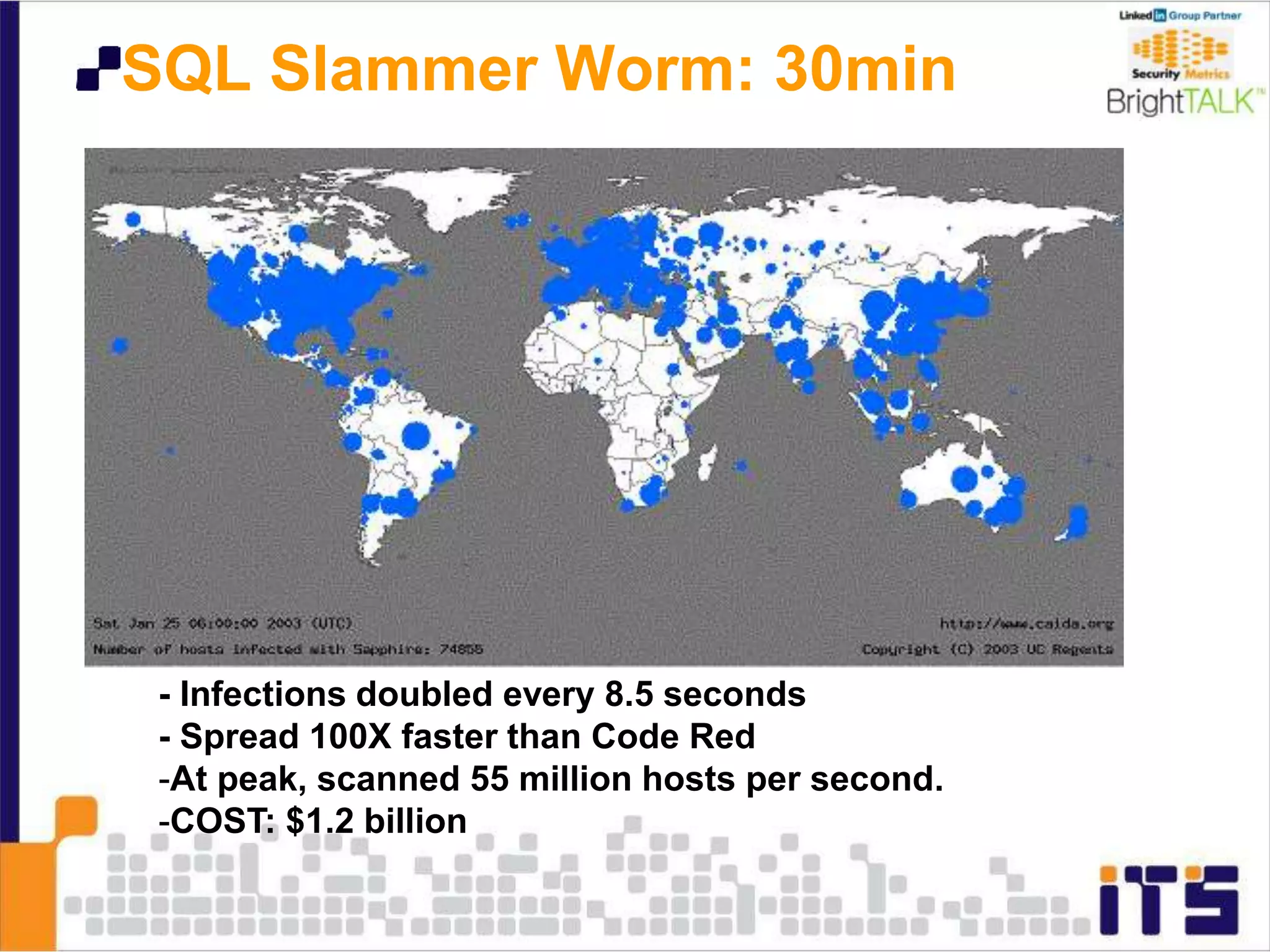
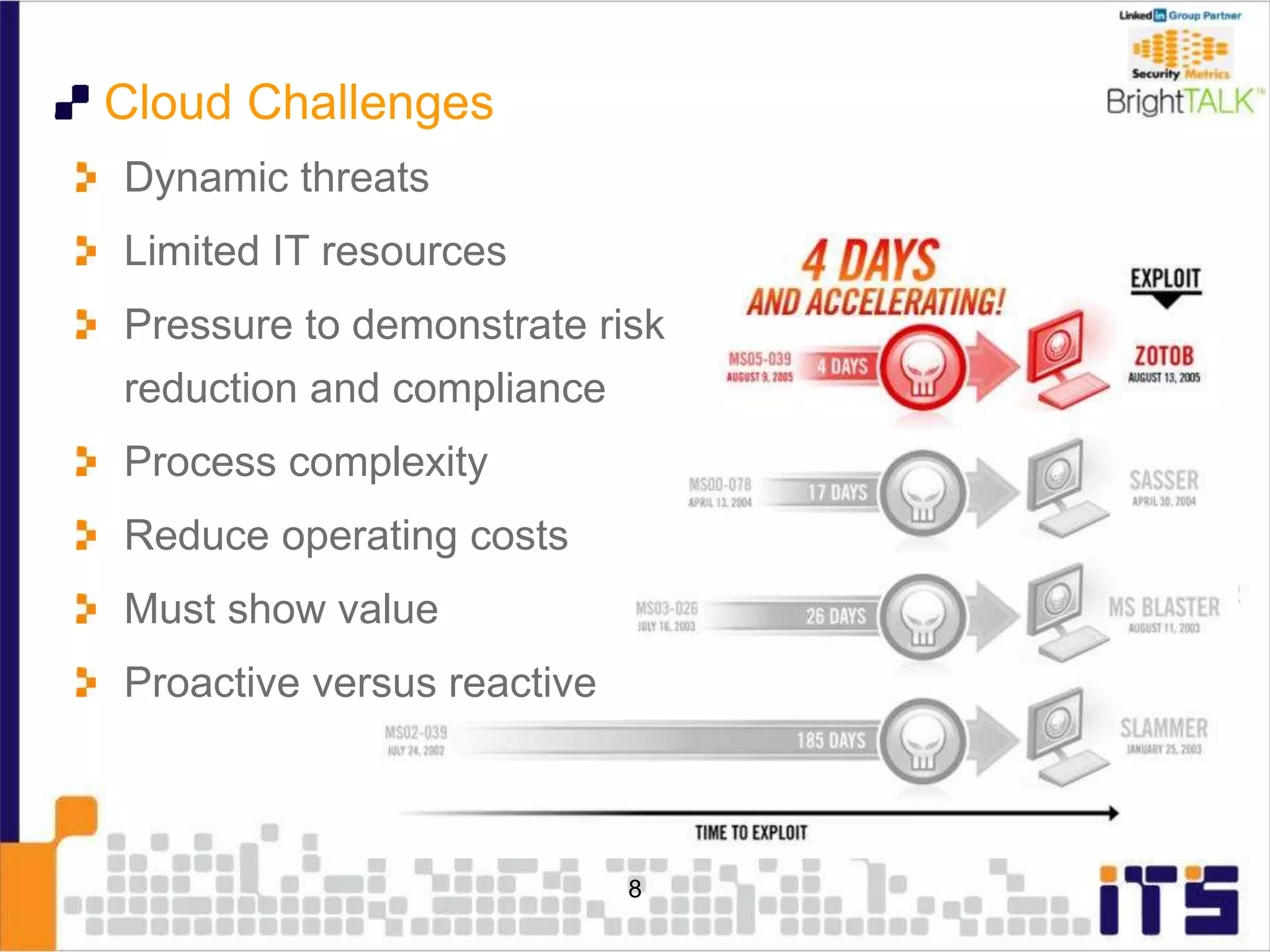
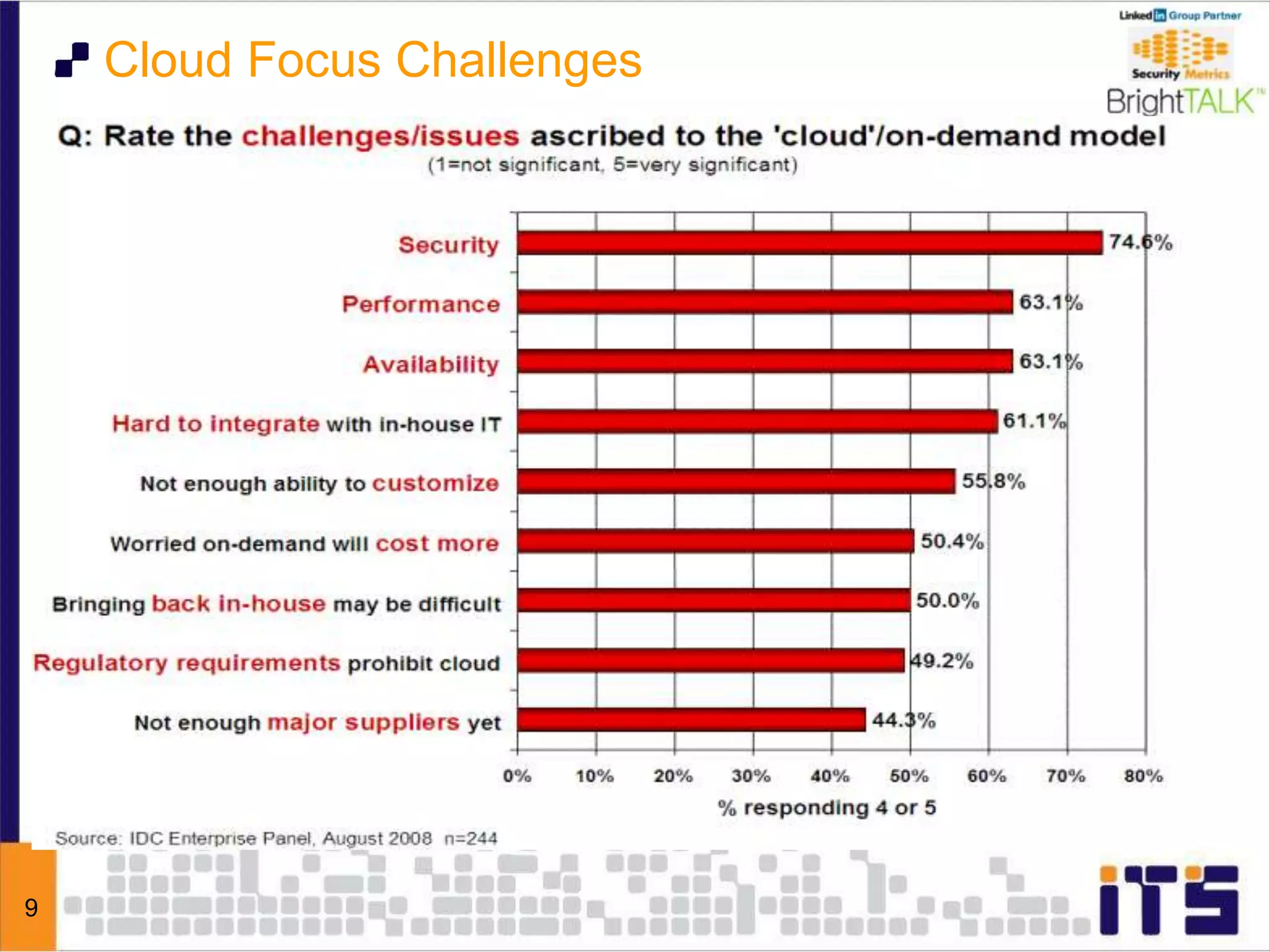
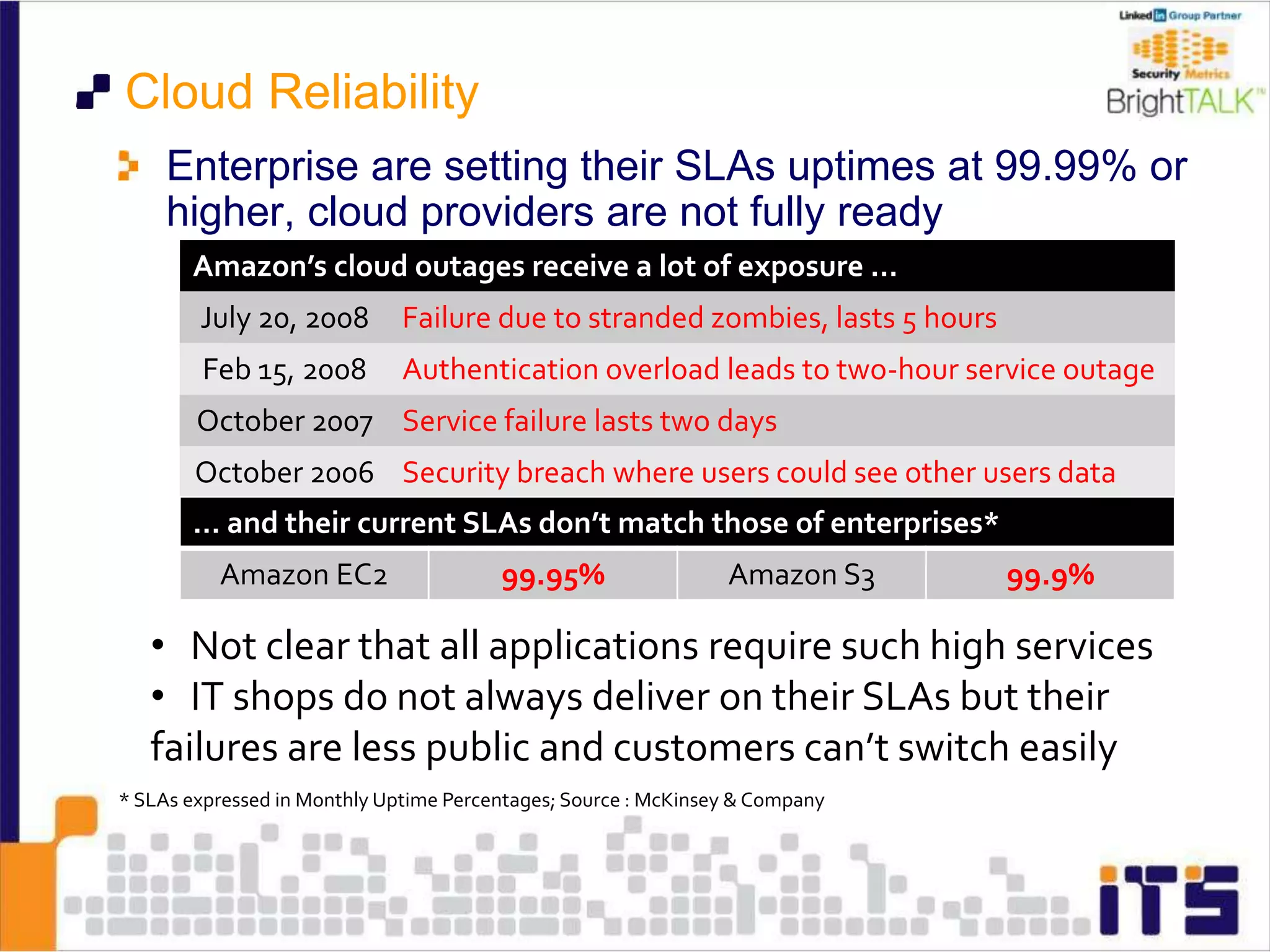
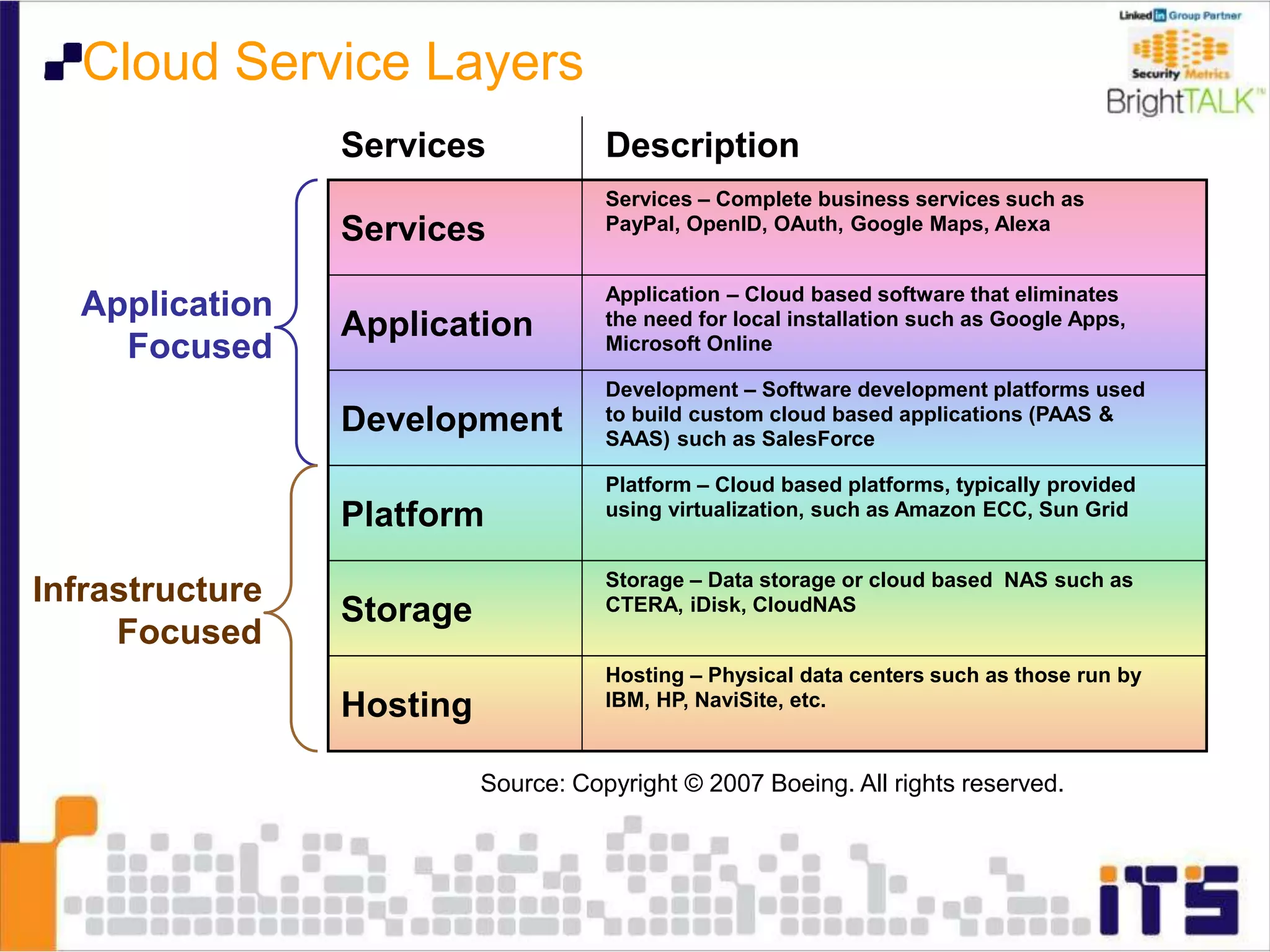
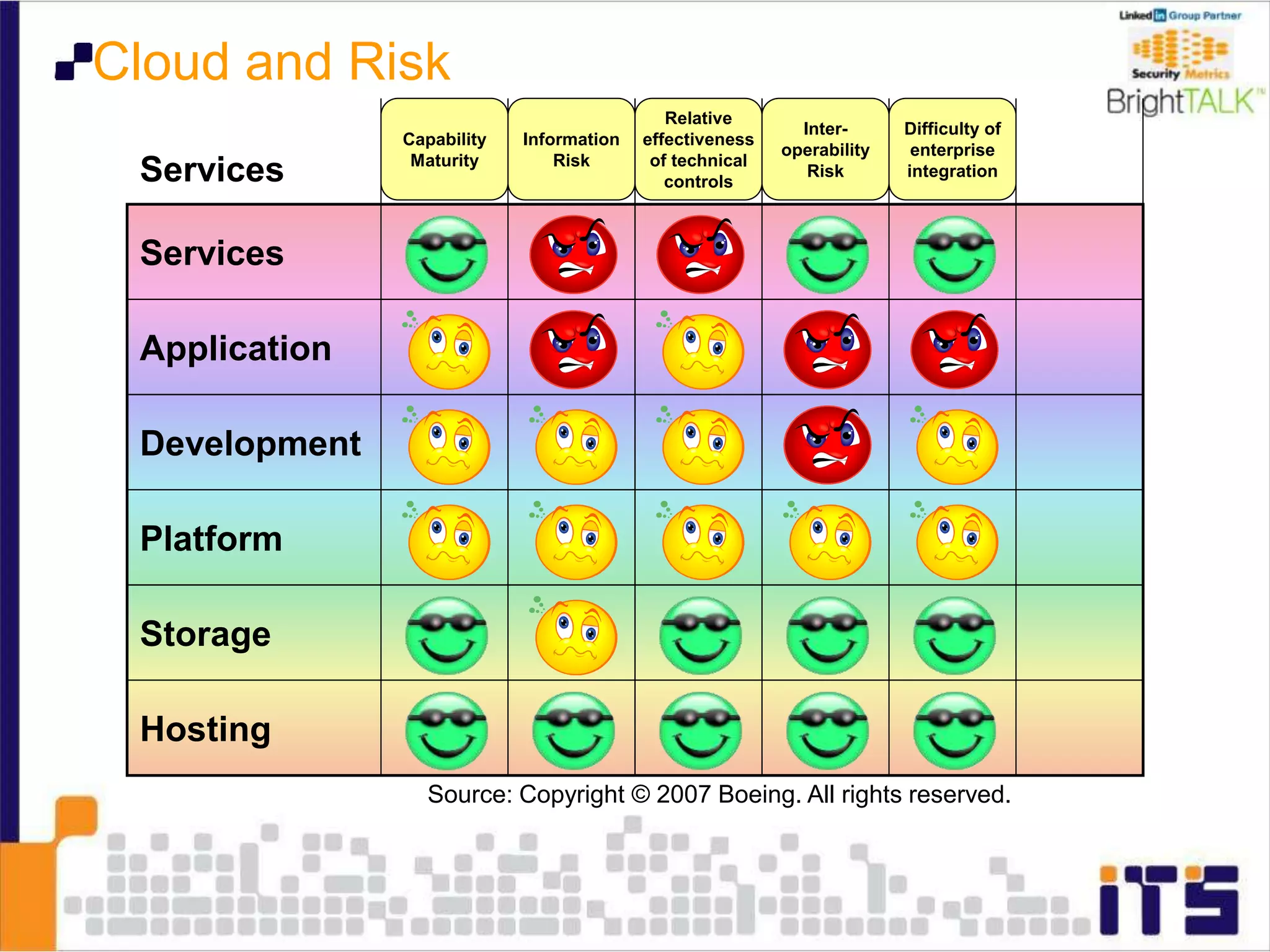
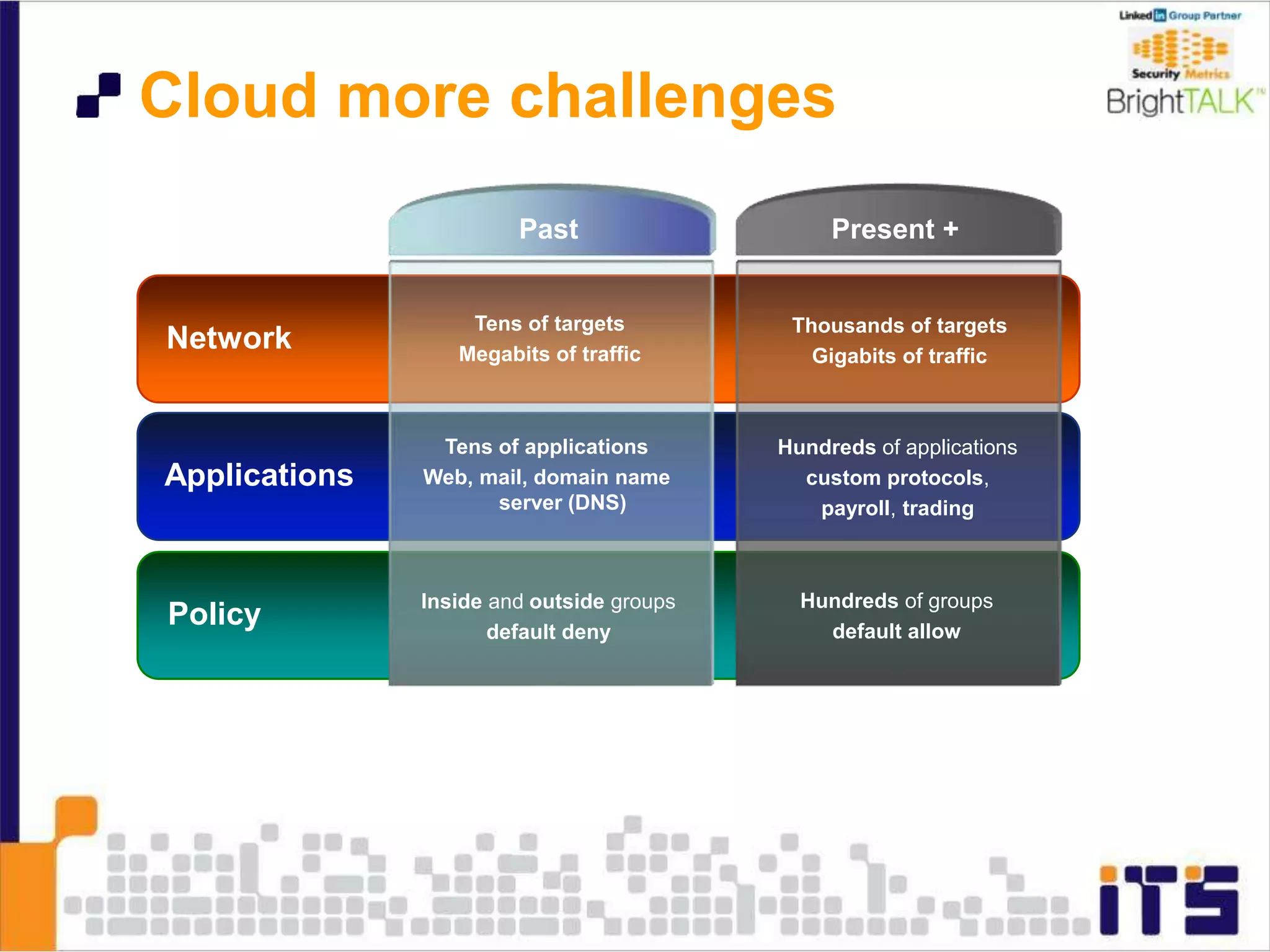
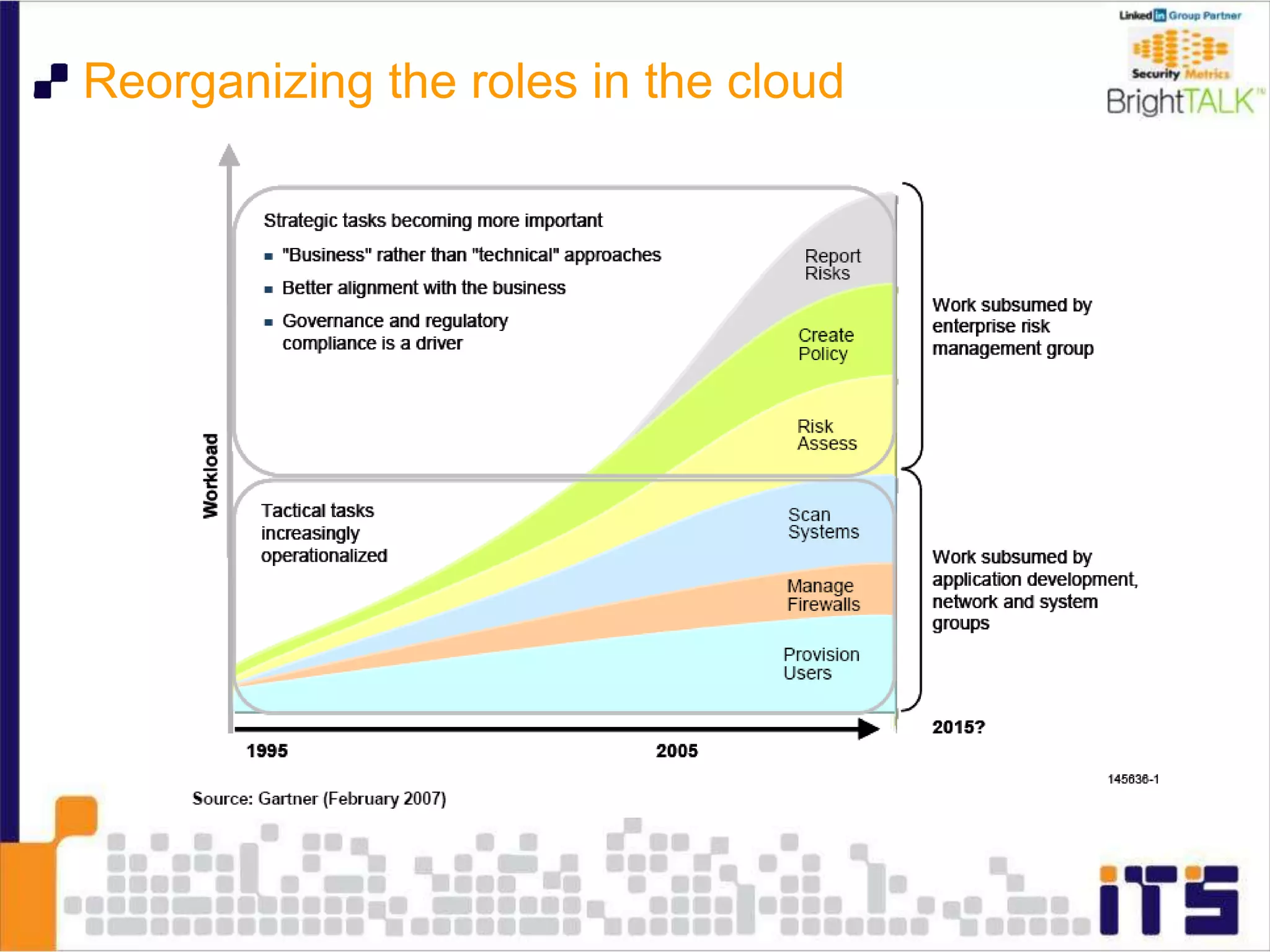
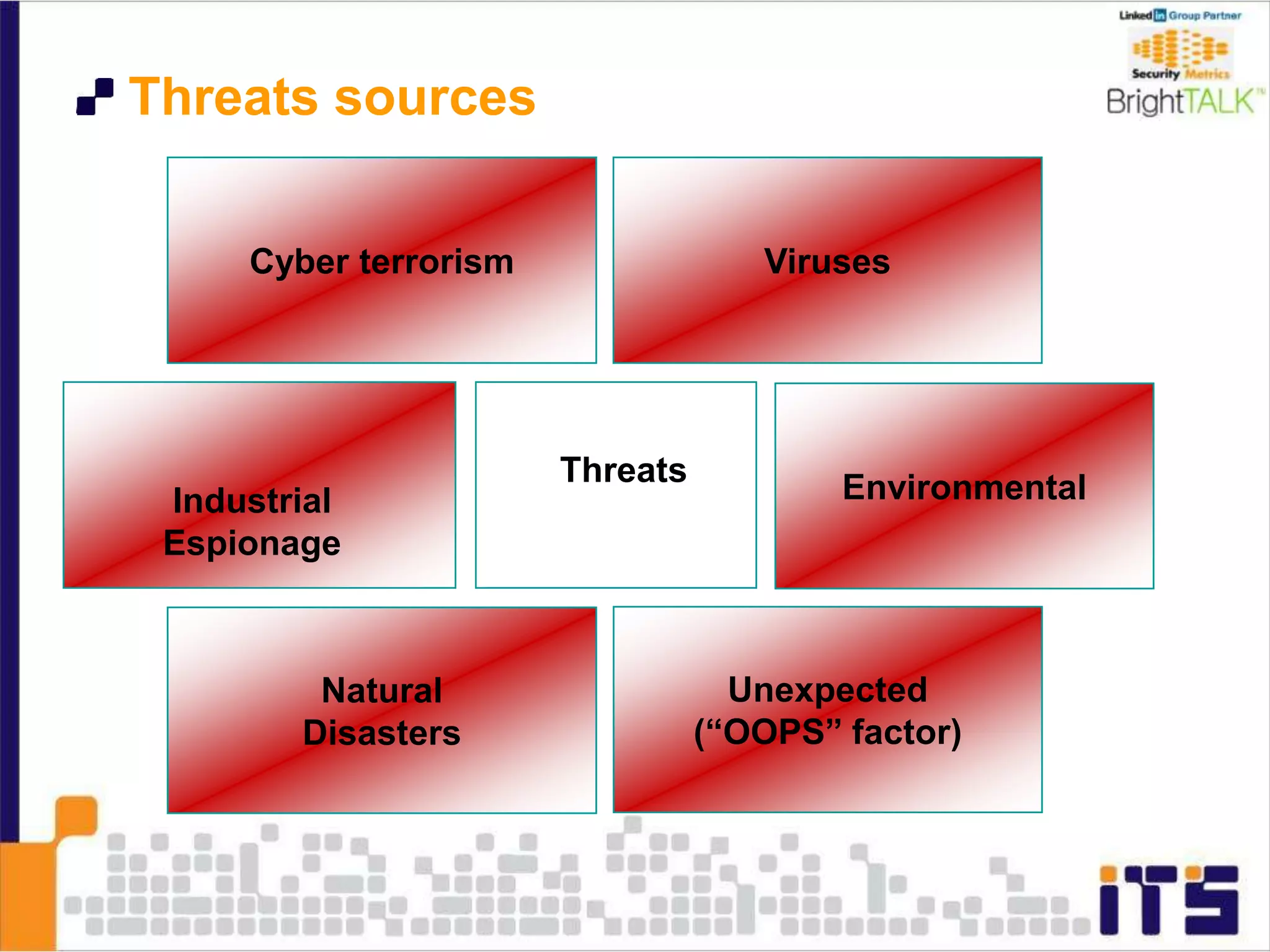
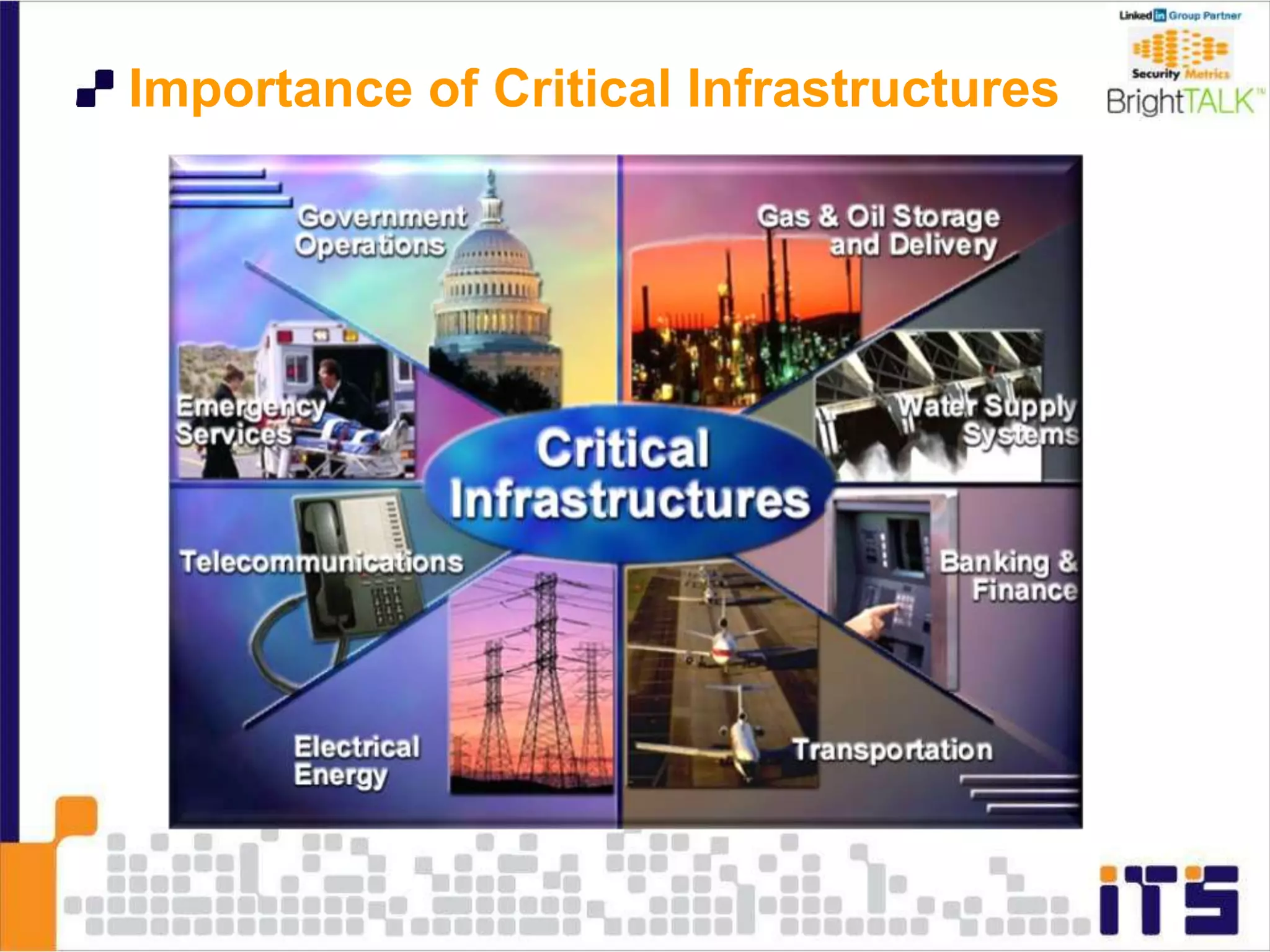
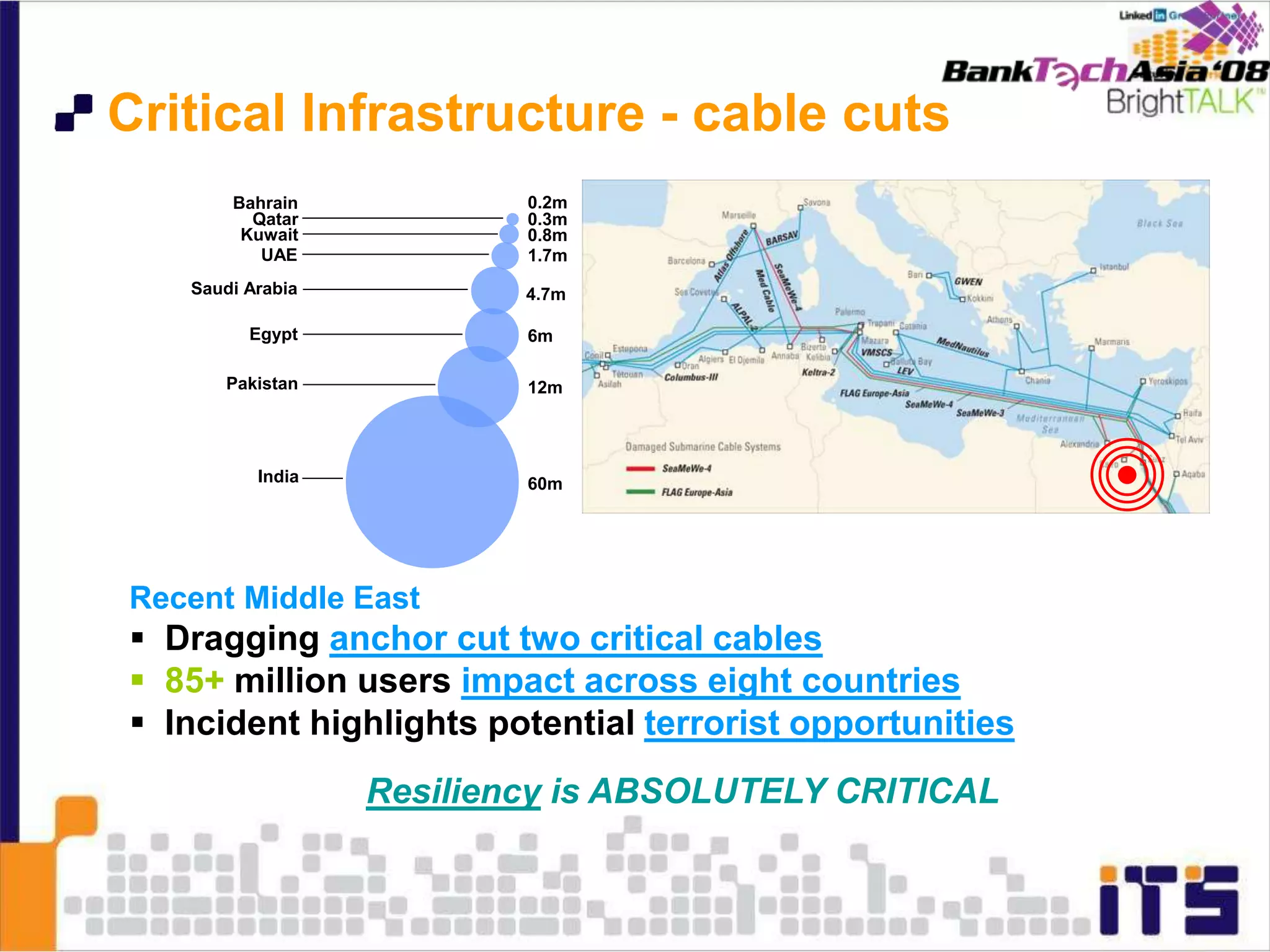
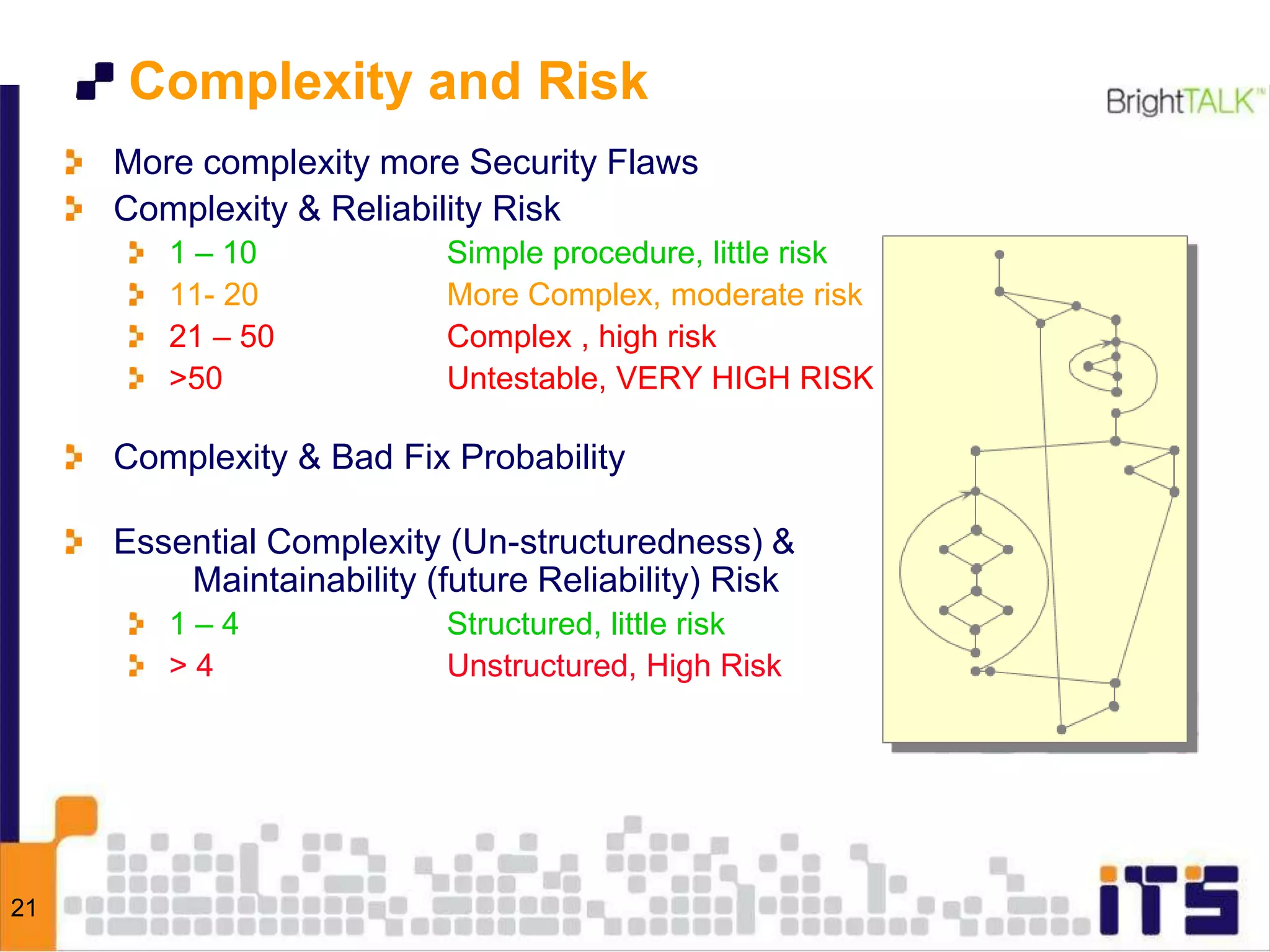
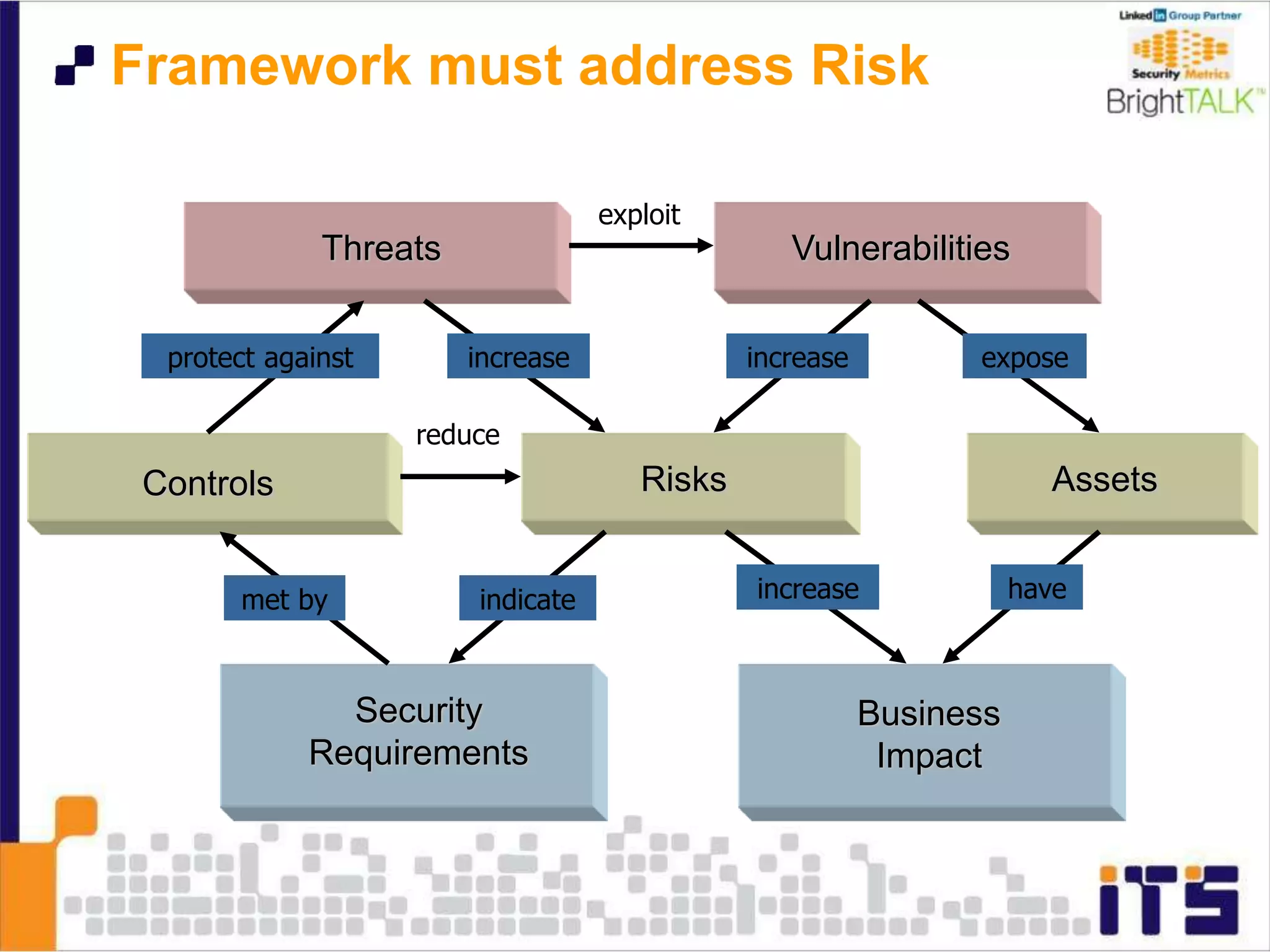
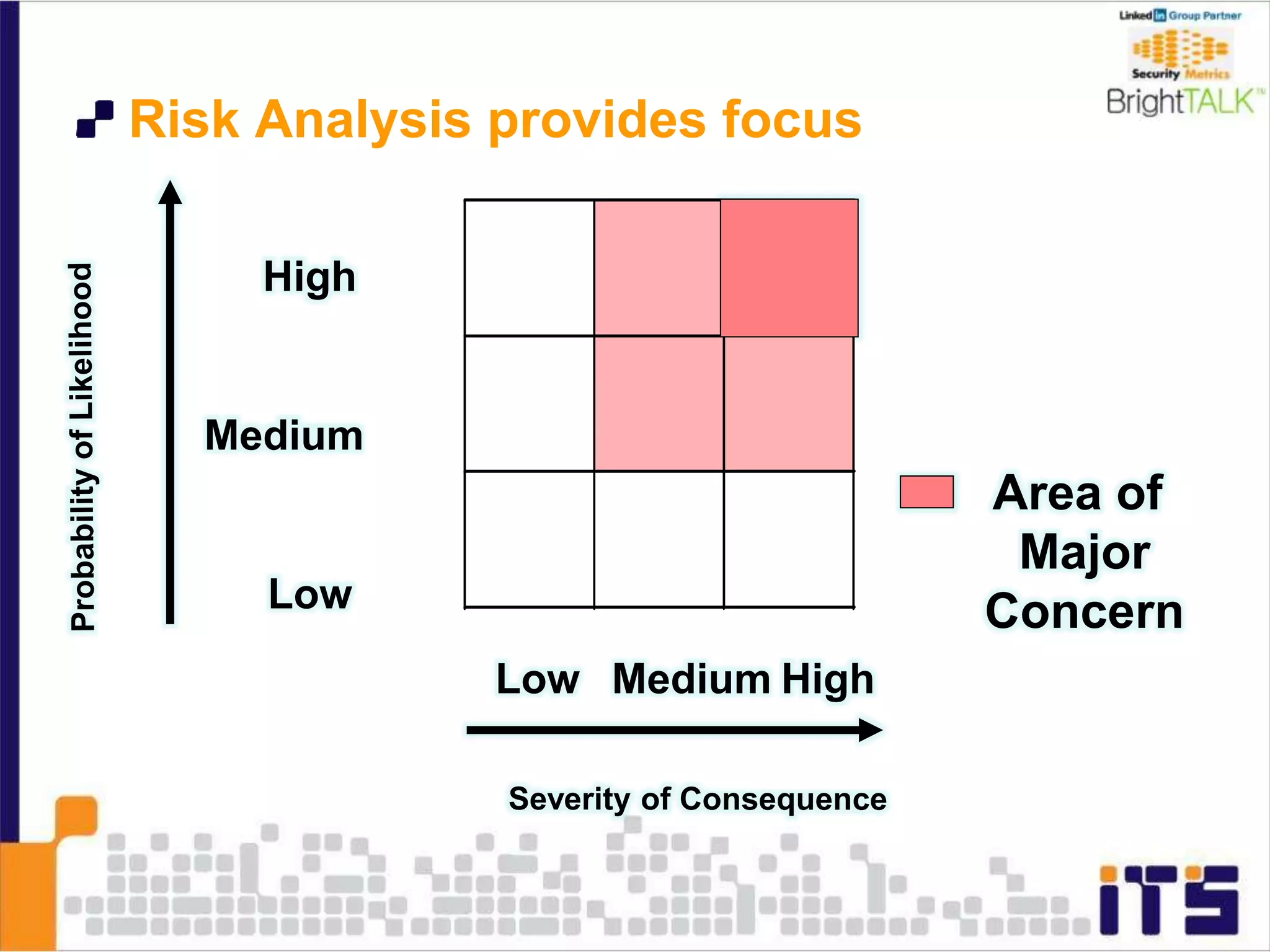
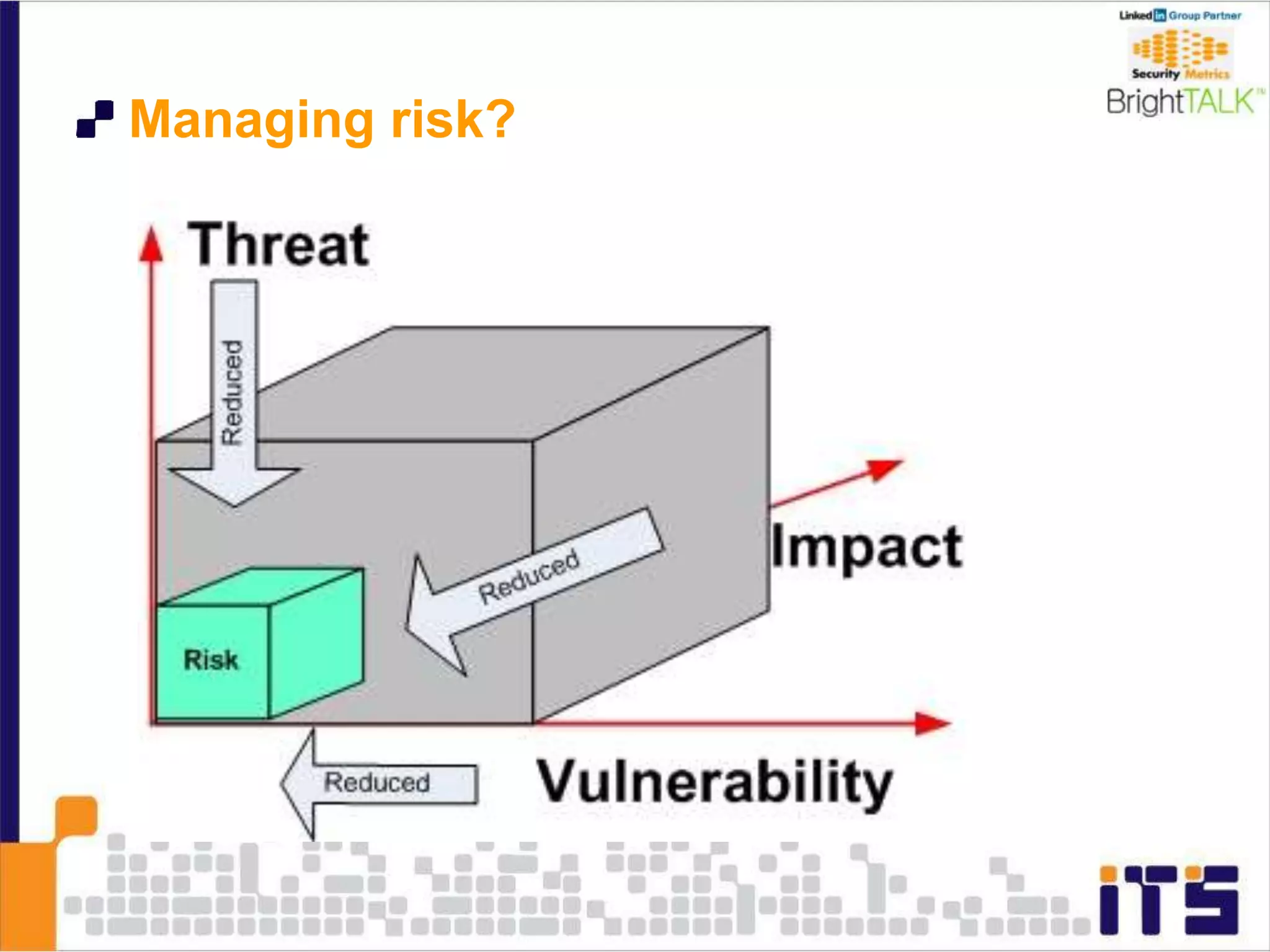
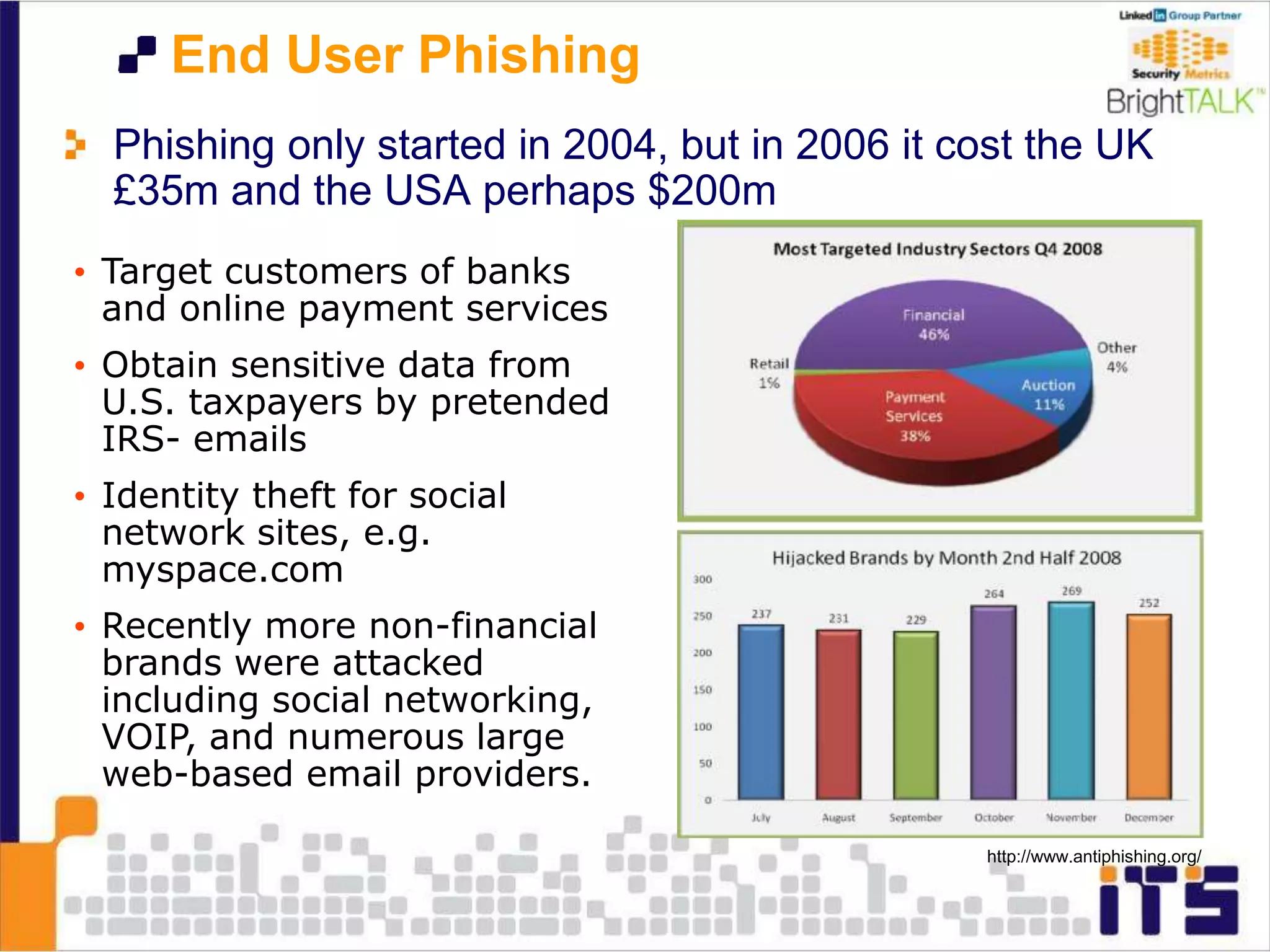
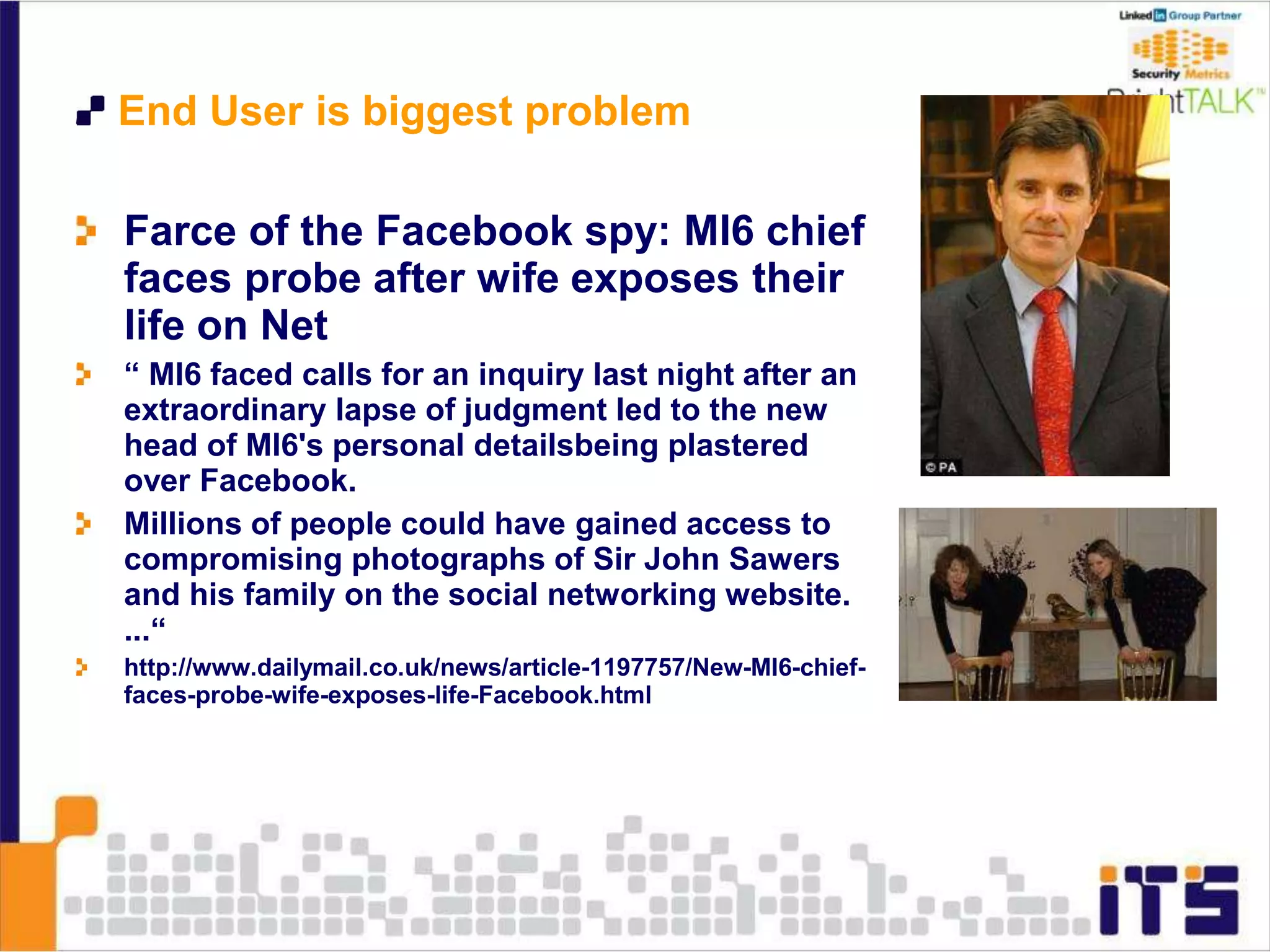
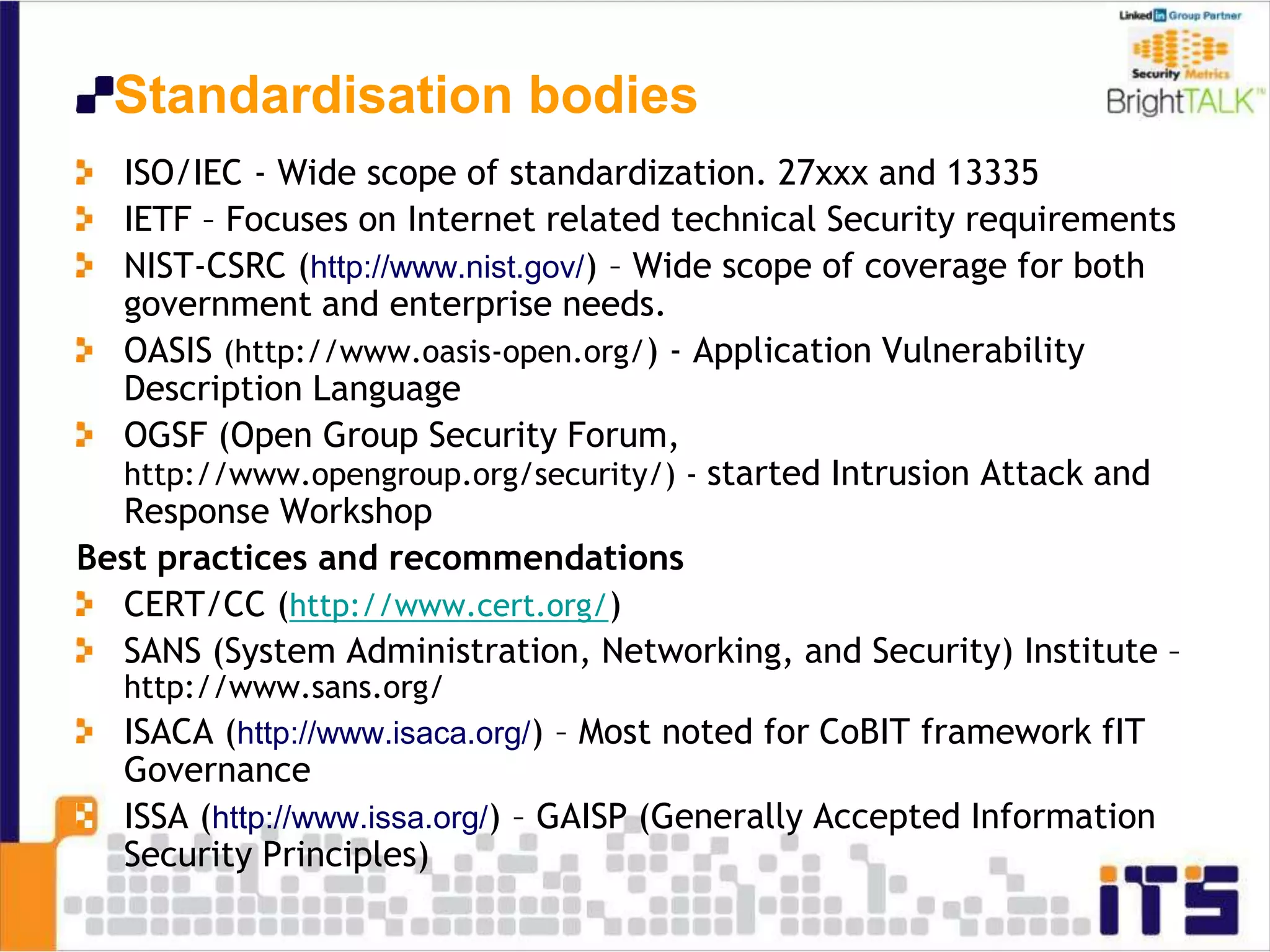
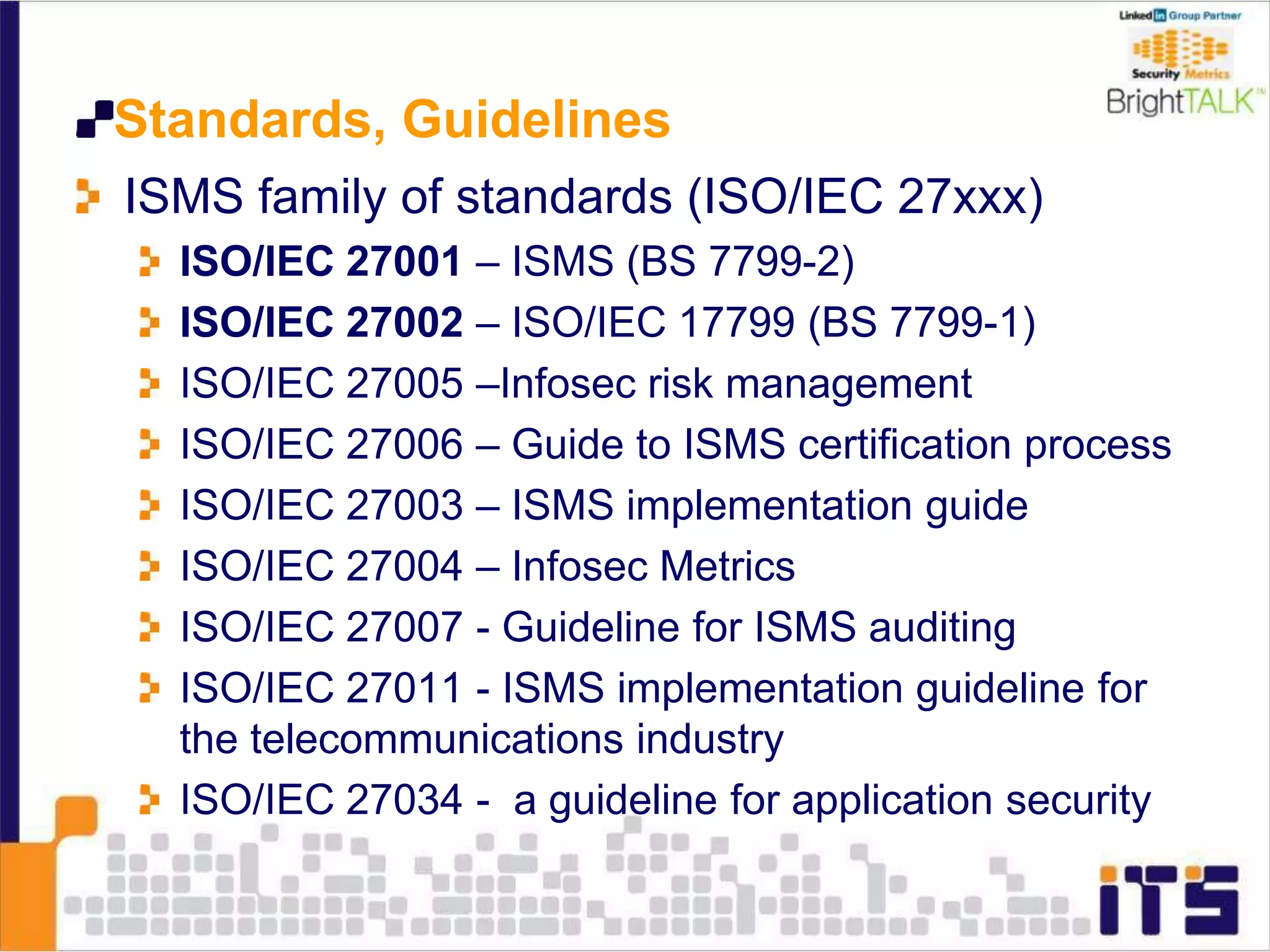
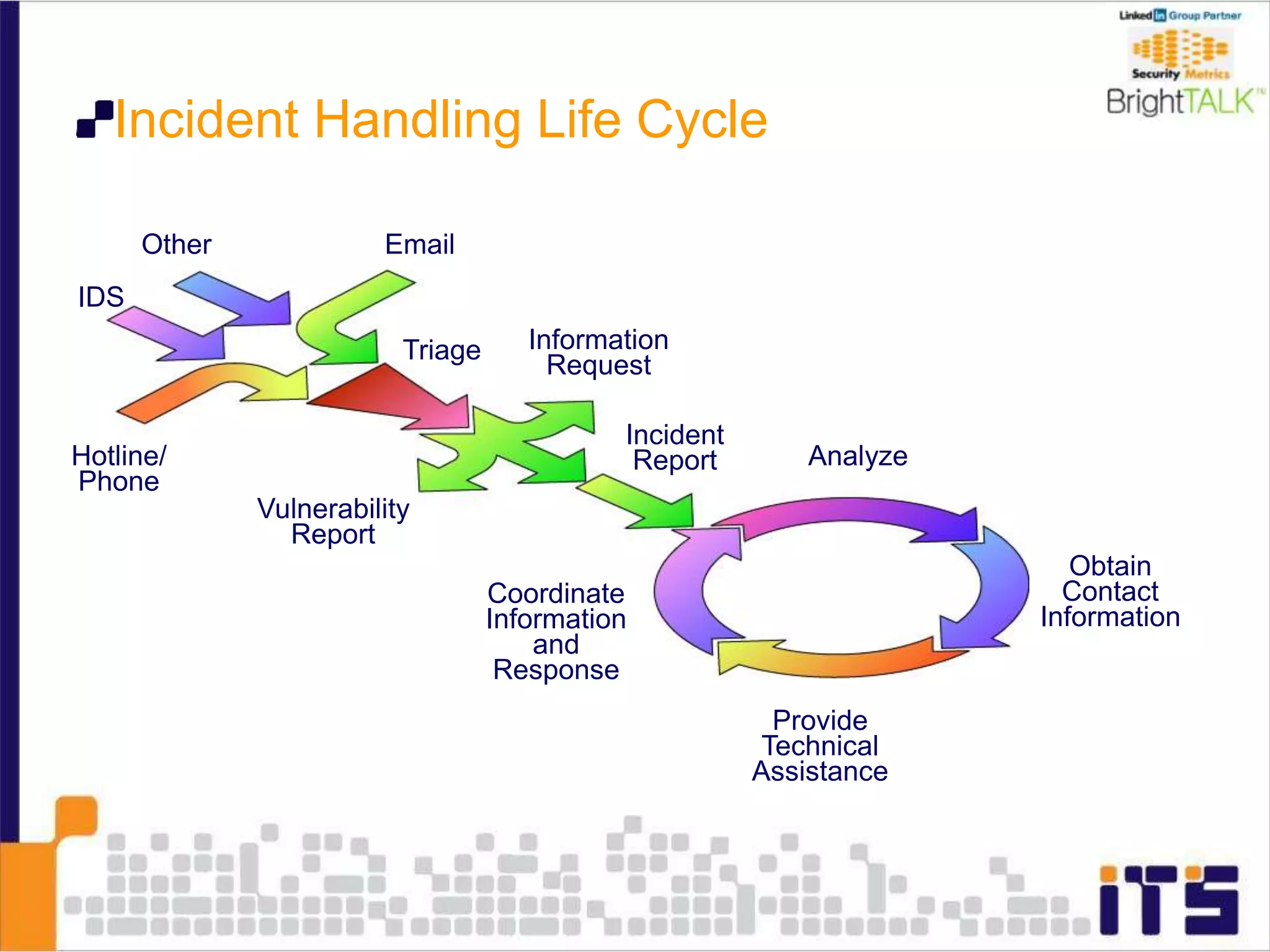
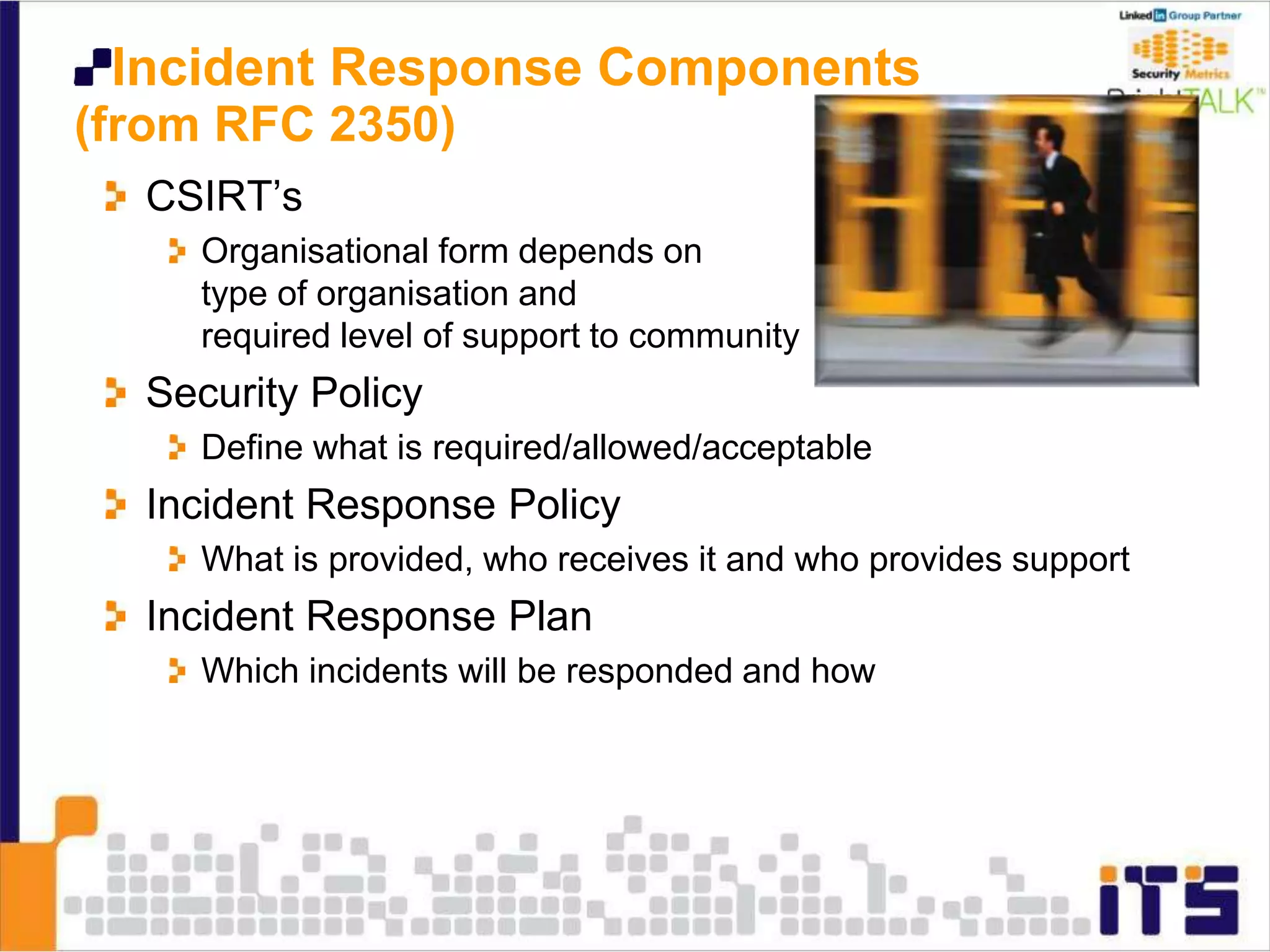
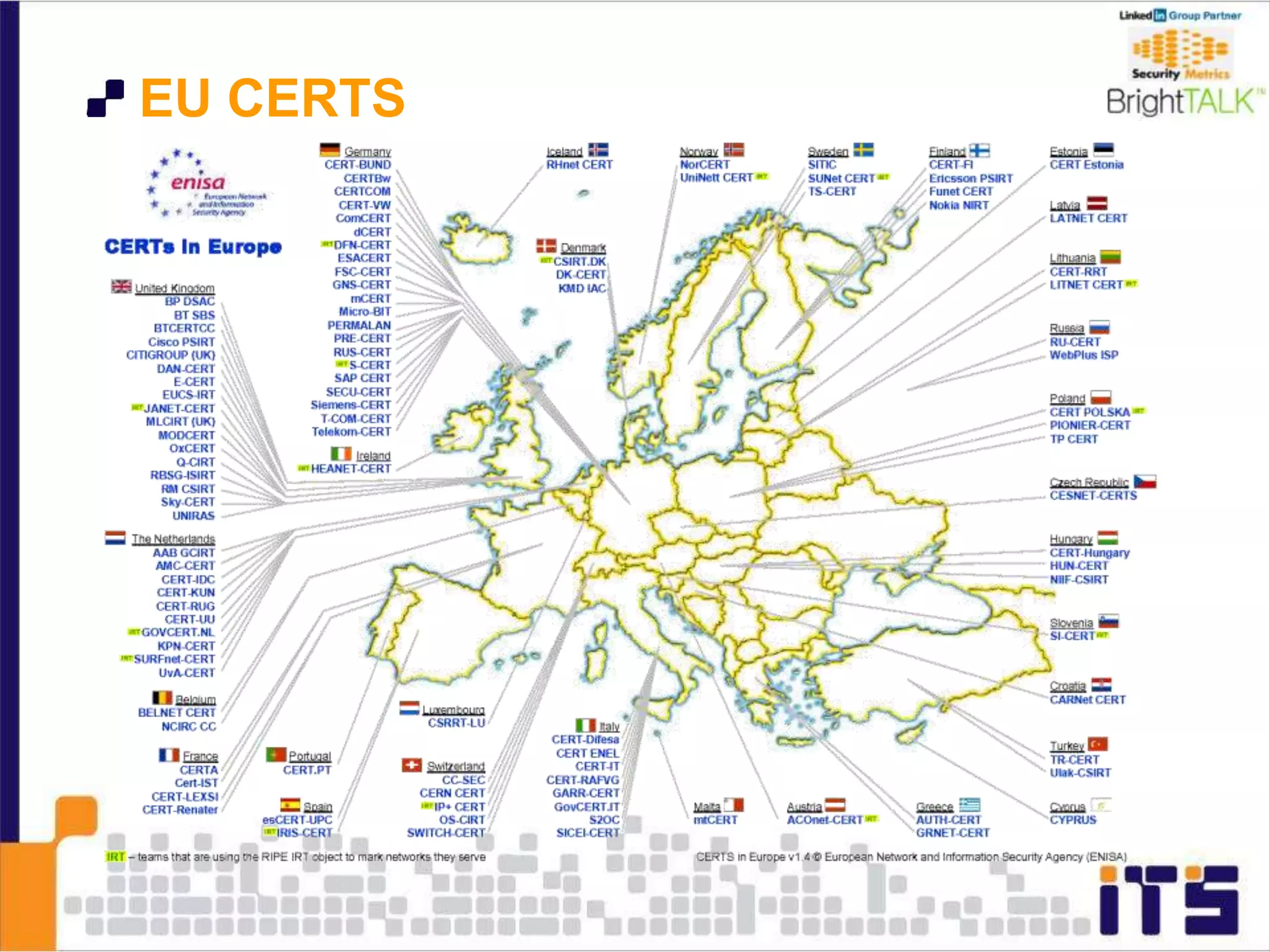
The document discusses the evolution of cloud services and highlights the challenges associated with cloud security, business continuity, and risk management. It addresses historical cybersecurity incidents, the need for reliable service level agreements (SLAs), and outlines the impact of complexity on security vulnerabilities. The text emphasizes the importance of proactive risk management, continuous monitoring, and collaboration among organizations to enhance cloud security and resilience.