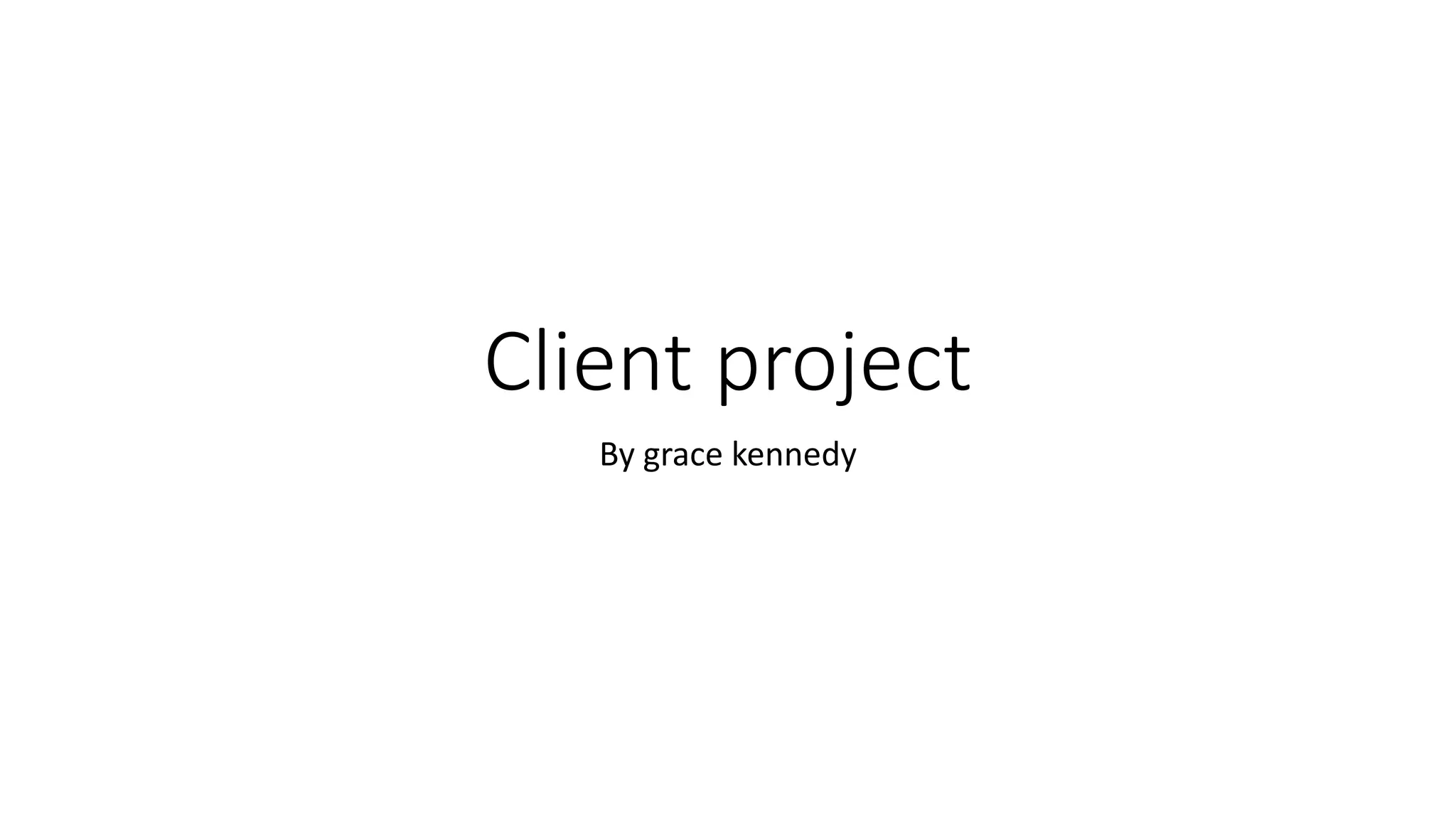
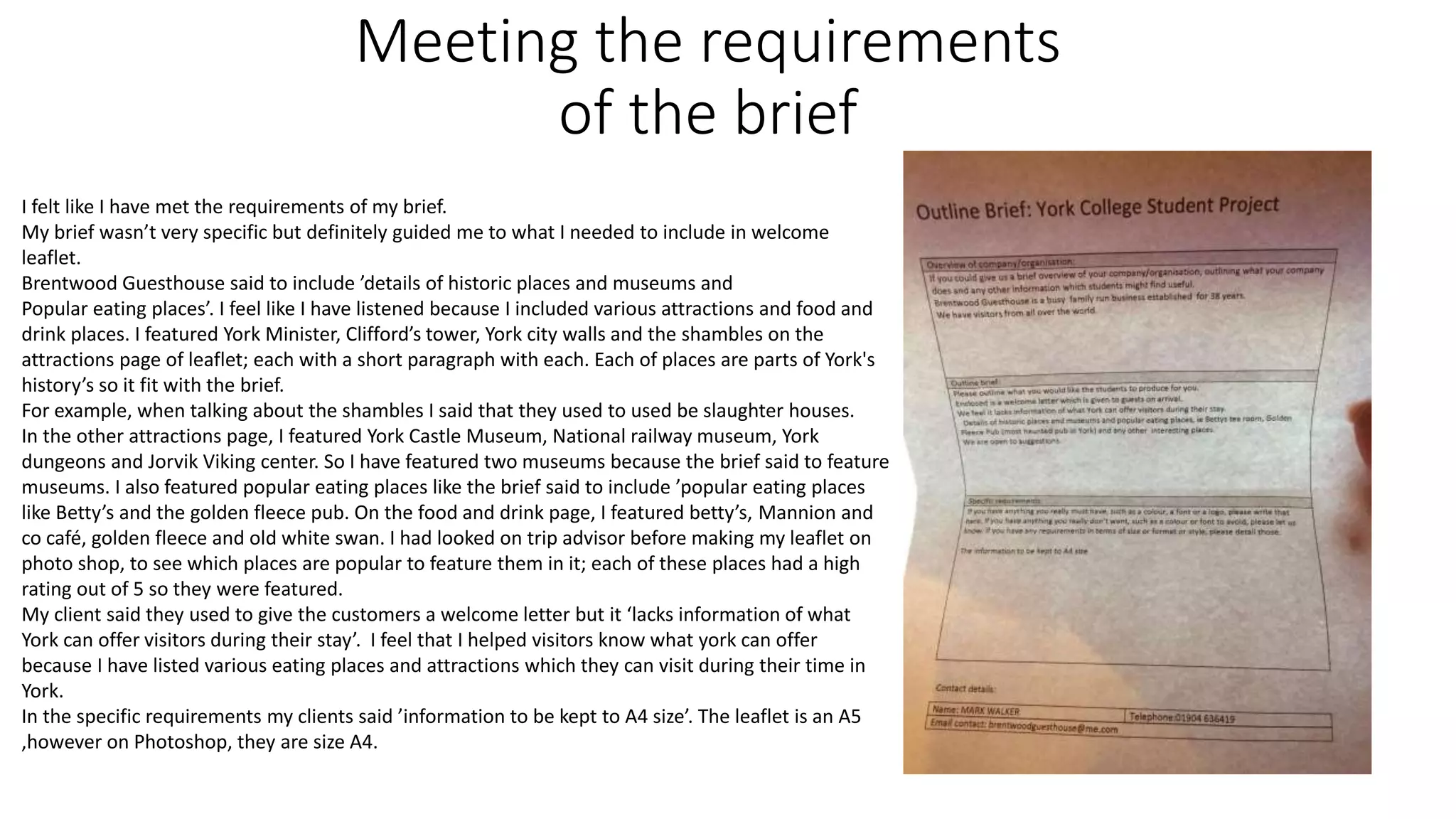
Client project for Brentwood Guesthouse in York. Legal constraints required taking original photos of attractions instead of using copyrighted online images, which was time consuming. Financial constraints were managing with provided college cameras. Project was managed by making pages in order and adding text and images. Time management could have been improved by taking photos earlier. Communicating with client was easy as they know each other personally. Requirements of detailing historic places, museums and restaurants were met by including attractions like York Minster and restaurants like Betty's. Lessons learned were to better plan by outlining descriptions in advance and managing time more effectively.