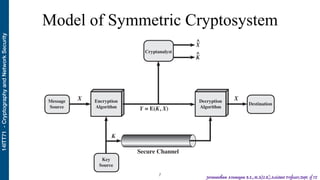
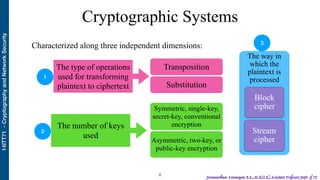
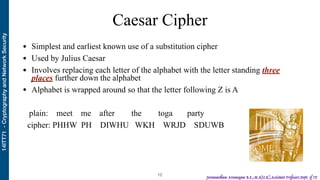
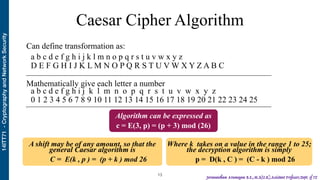
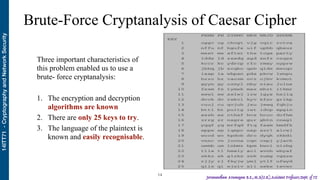
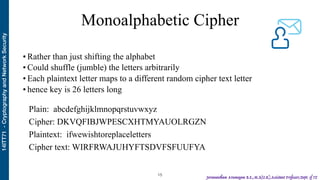
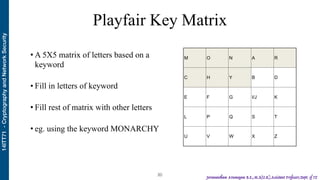
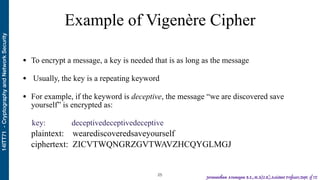
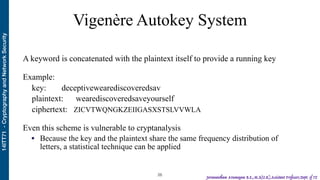
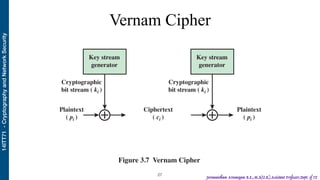
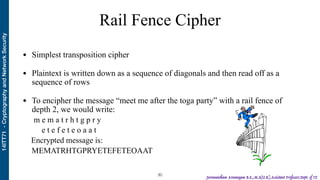
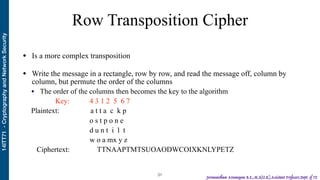
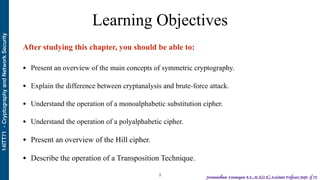
The document discusses classical encryption techniques used in cryptography. It begins with an overview of symmetric encryption and the basic concepts of plaintext, ciphertext, encryption, and decryption. It then covers various classical encryption techniques like the Caesar cipher, monoalphabetic cipher, Playfair cipher, polyalphabetic ciphers including the Vigenère cipher, Vernam cipher, and the theoretically unbreakable one-time pad cipher. It also discusses transposition techniques like the rail fence cipher and row transposition cipher.
![14ITT71-CryptographyandNetworkSecurity
Jeevanantham Arumugam B.E.,M.S(U.K),Assistant Professor,Dept. of IT
Basic Terms
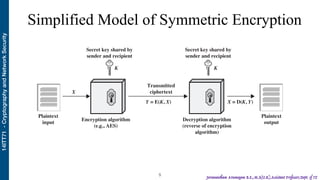
• An original message is known as the plaintext
• The coded message is called the ciphertext
• The process of convert- ing from plaintext to ciphertext is known as enciphering or
encryption
• Restoring the plaintext from the ciphertext is deciphering or decryption
• The area of study known as cryptography
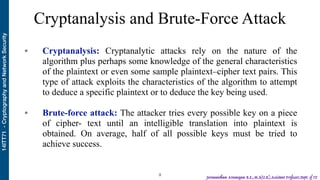
• Techniques used for deciphering a message without any knowledge of the enciphering
details fall into the area of cryptanalysis [“breaking the code”]
• The areas of cryptography and cryptanalysis together are called cryptology
!4](https://image.slidesharecdn.com/s-200813044423/85/Classical-Encryption-Techniques-3-320.jpg)