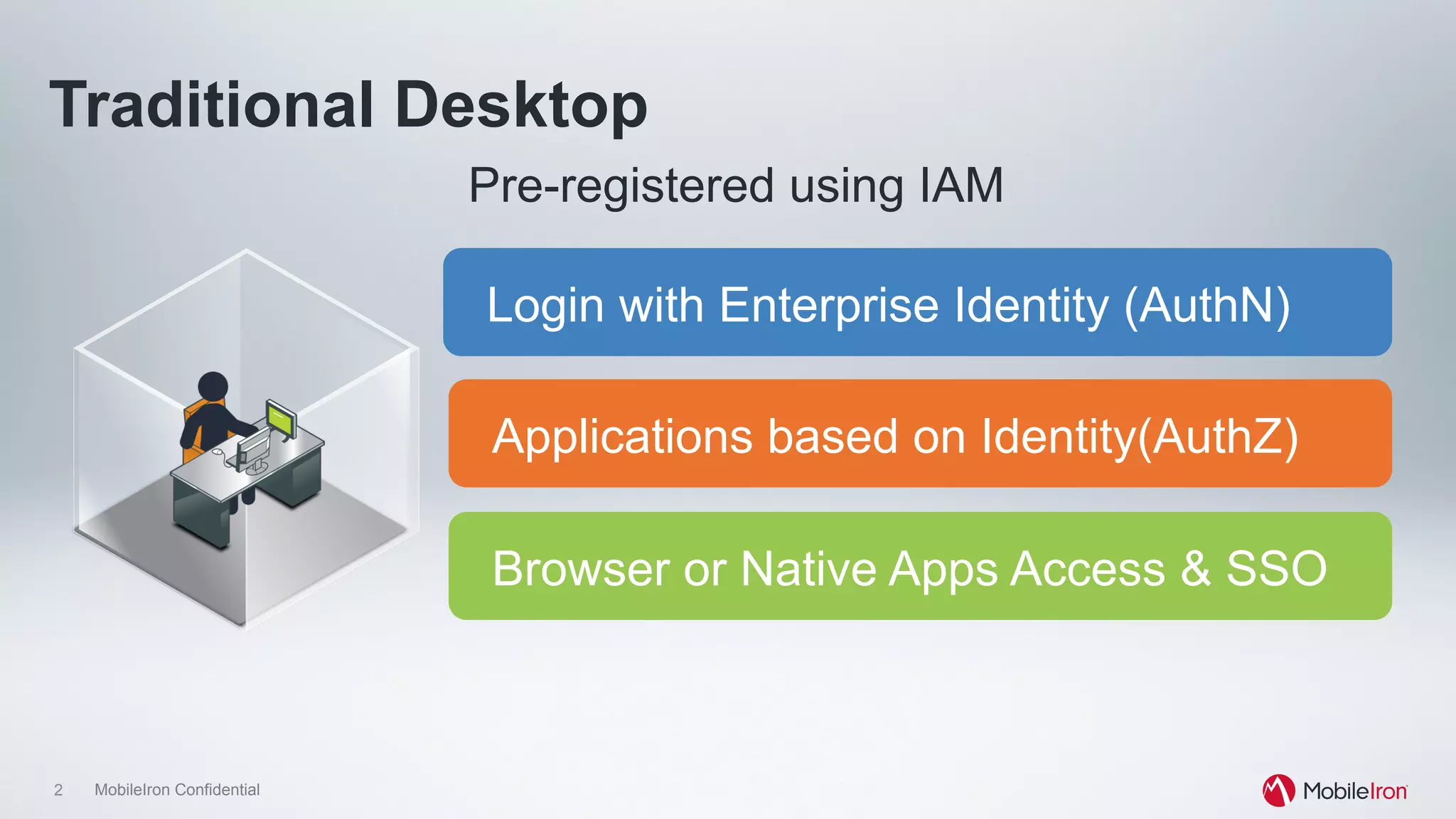
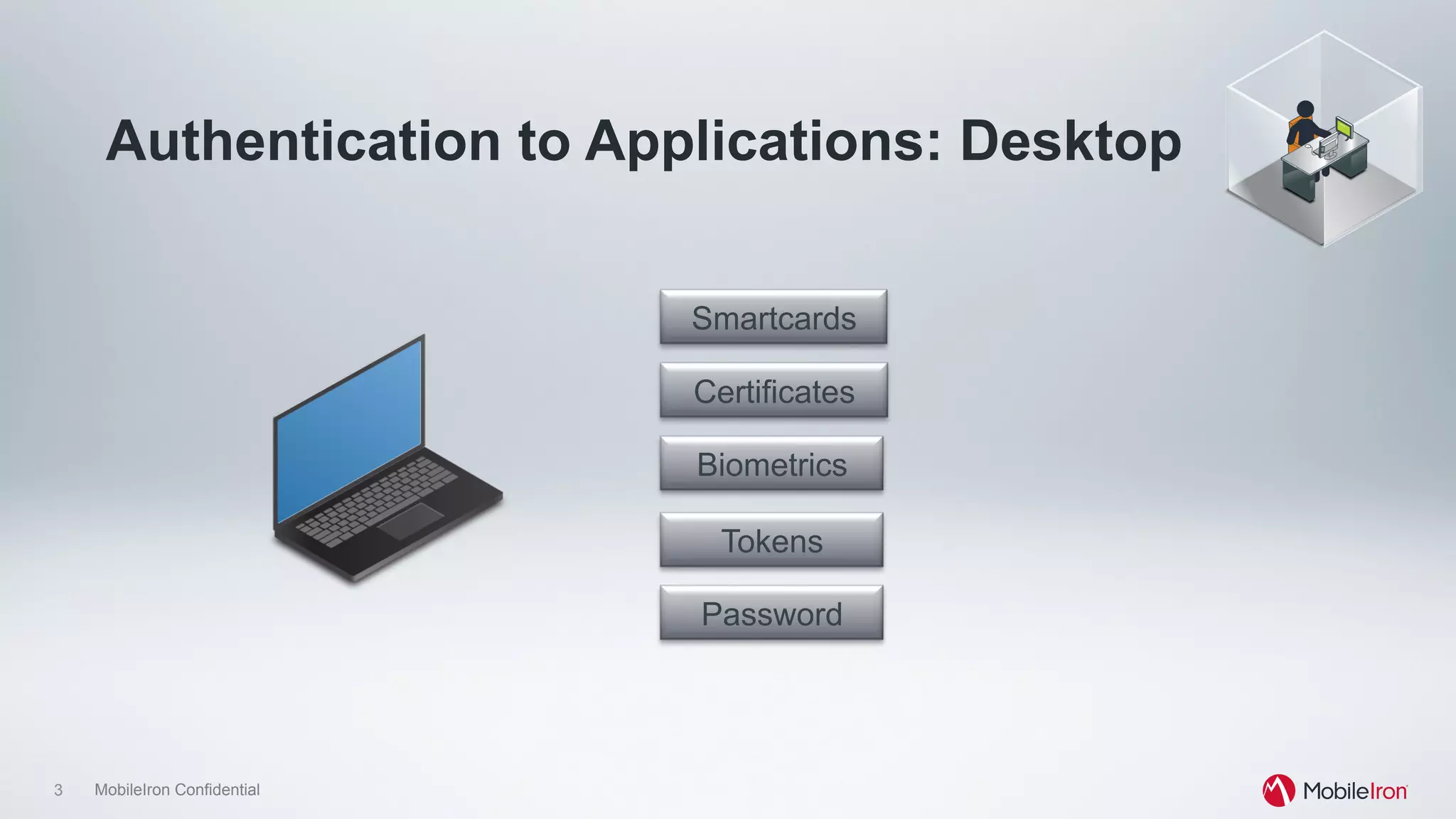
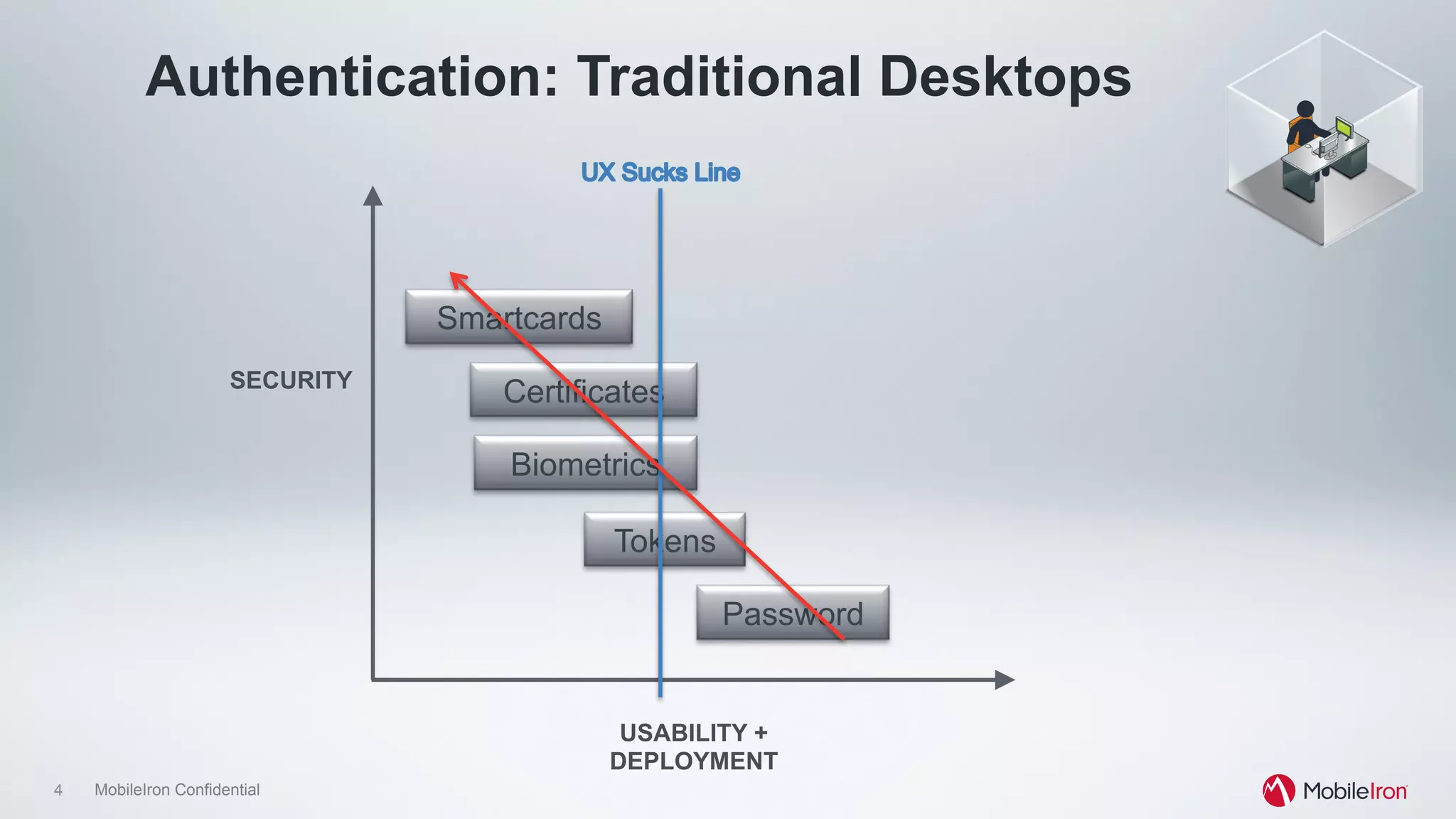
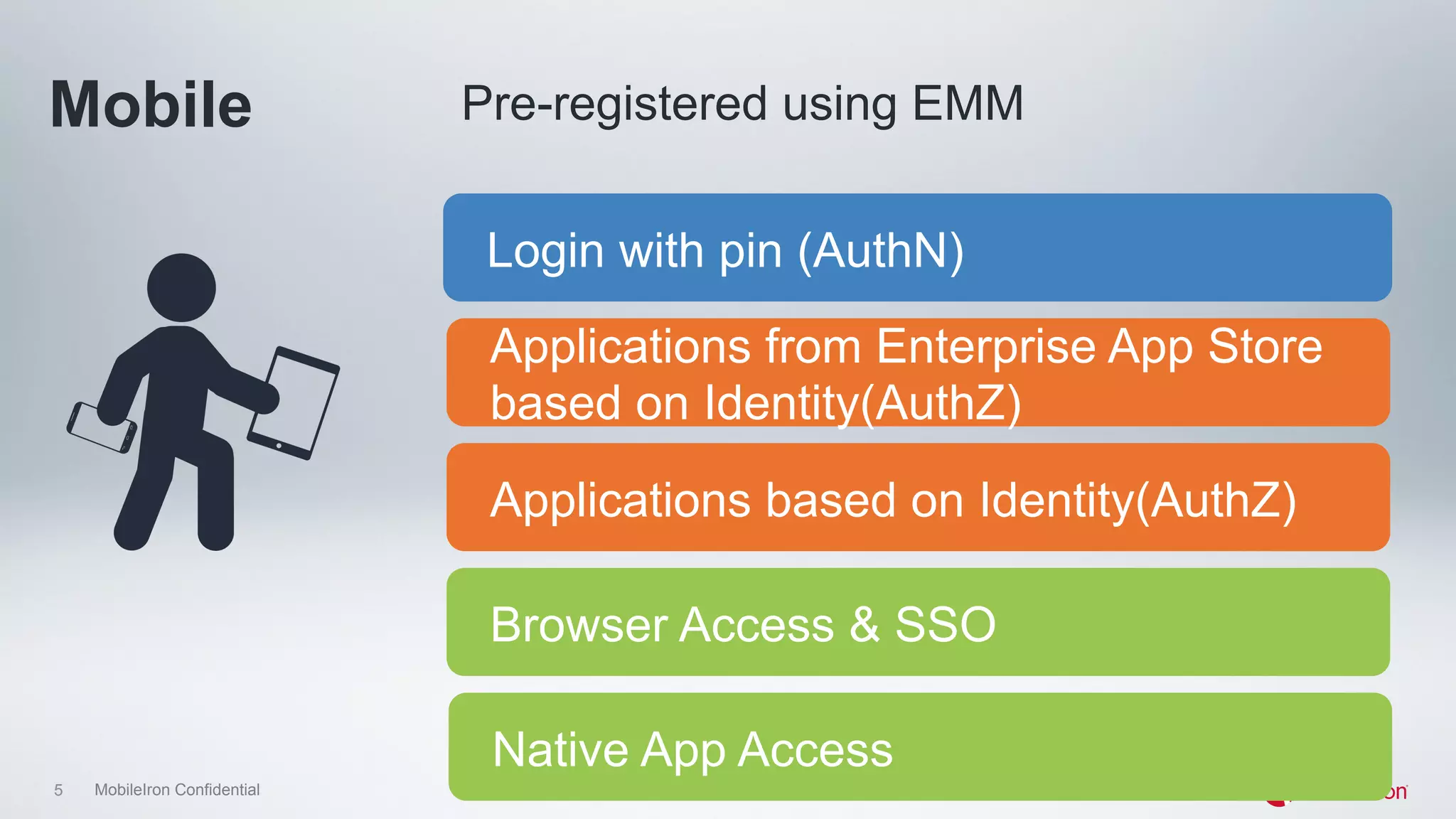
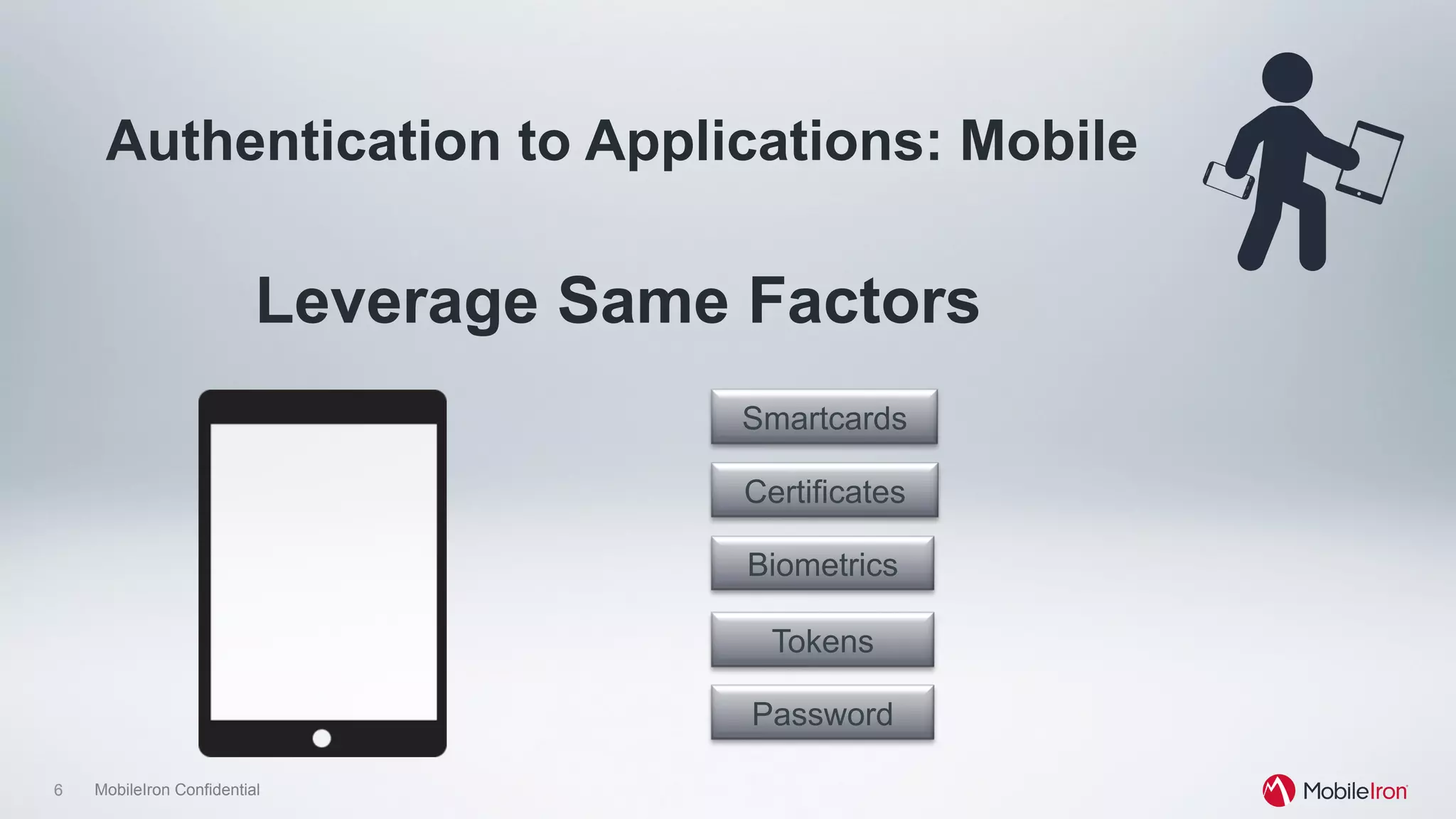
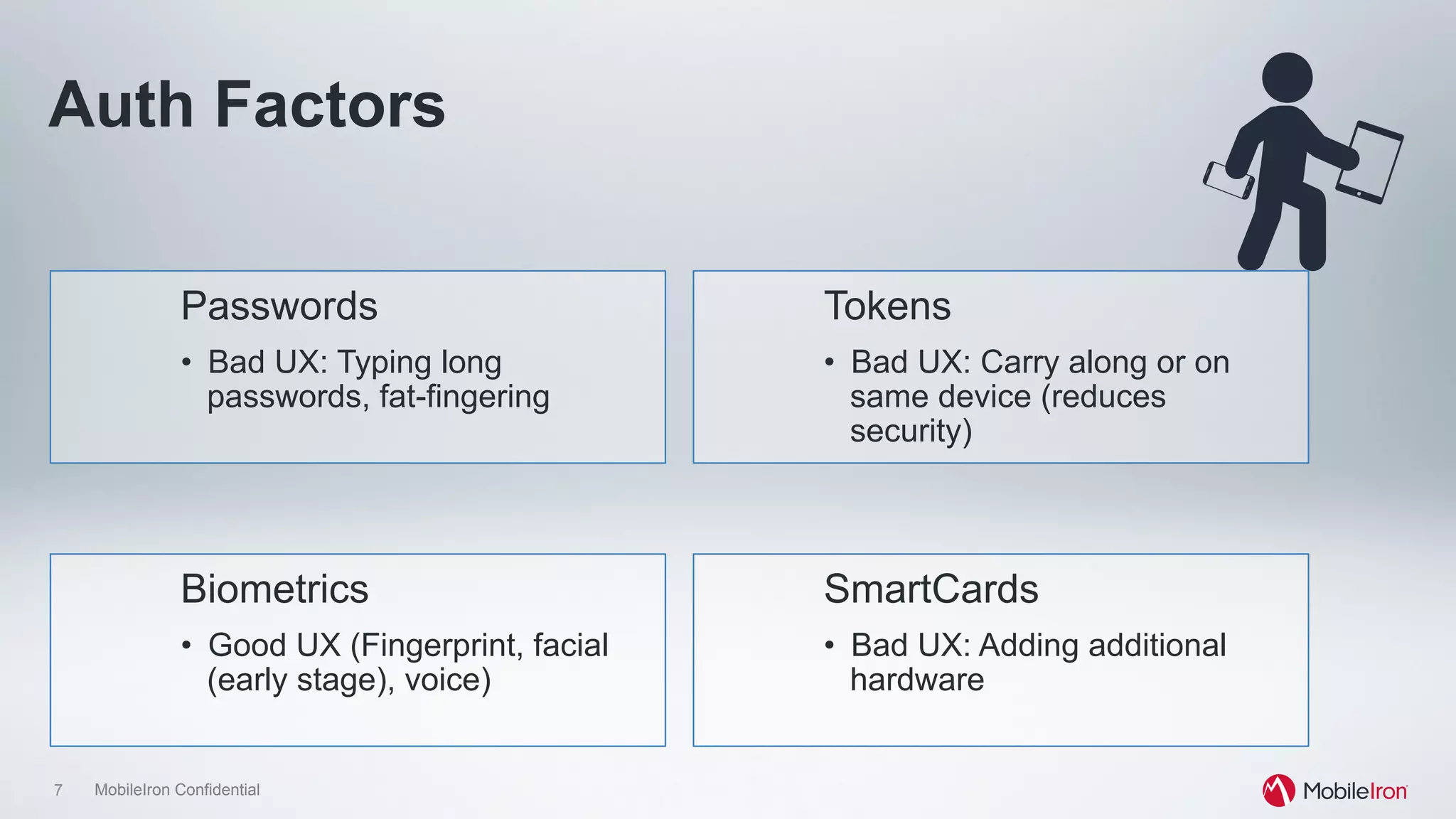
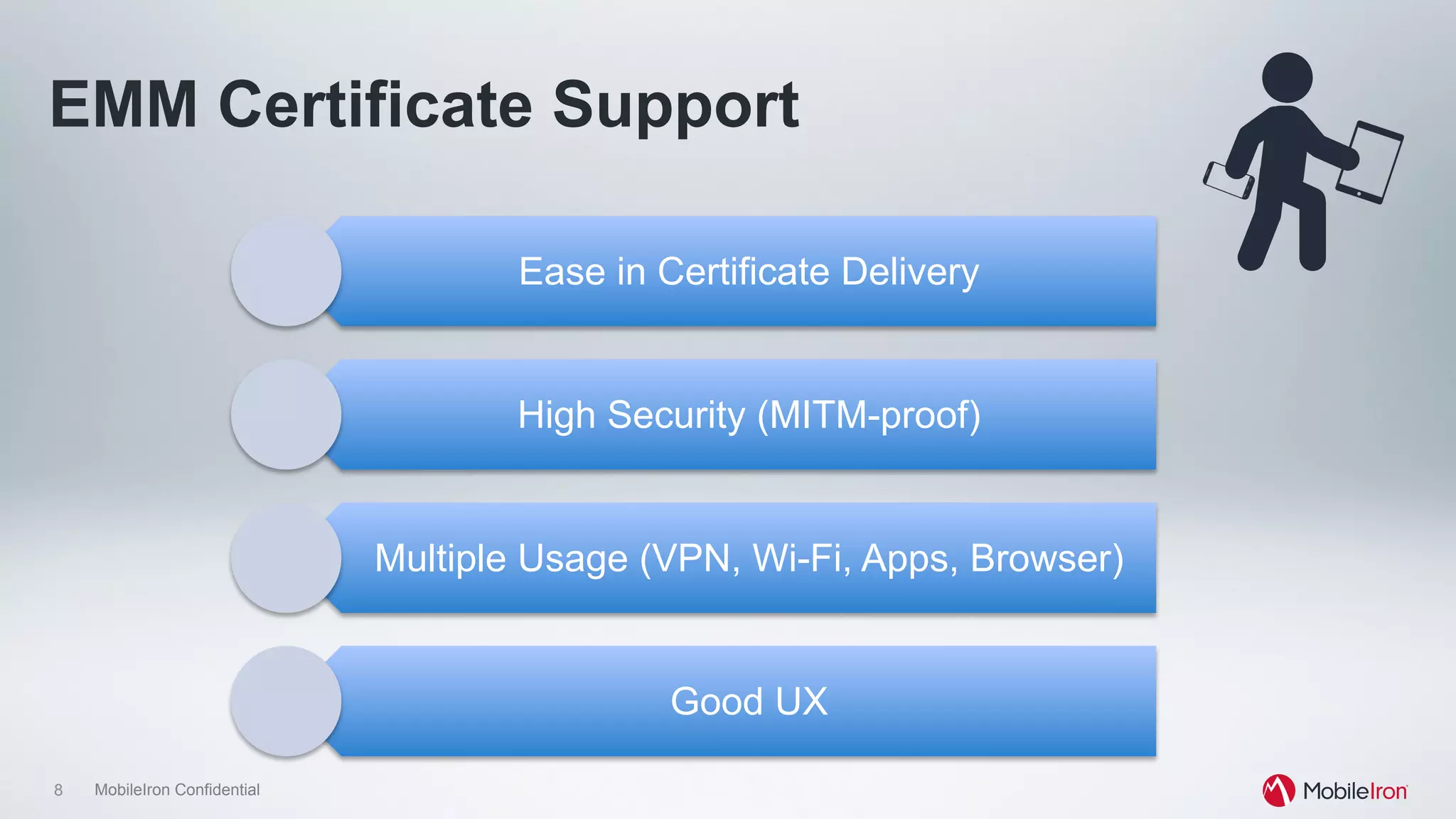
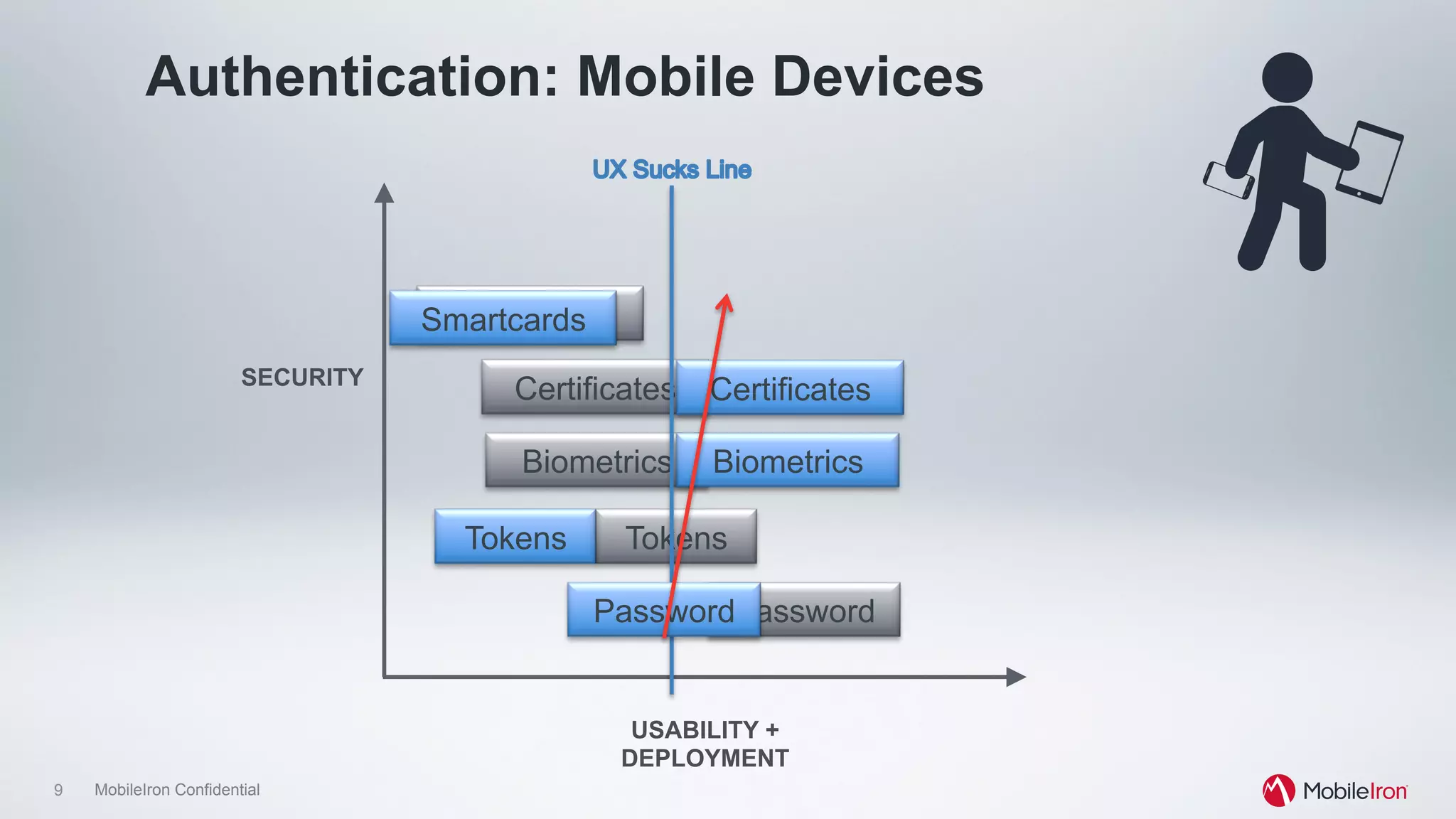
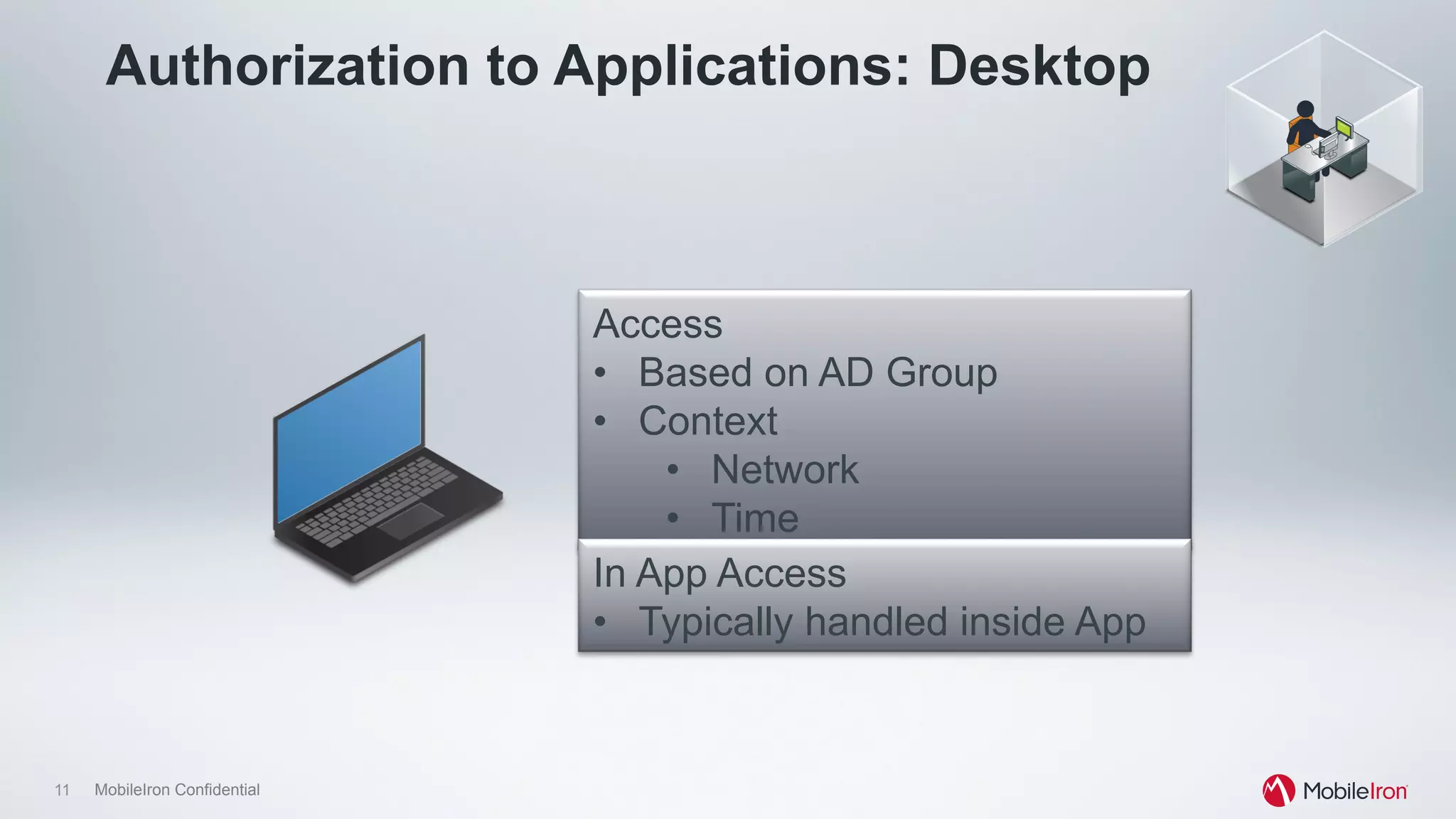
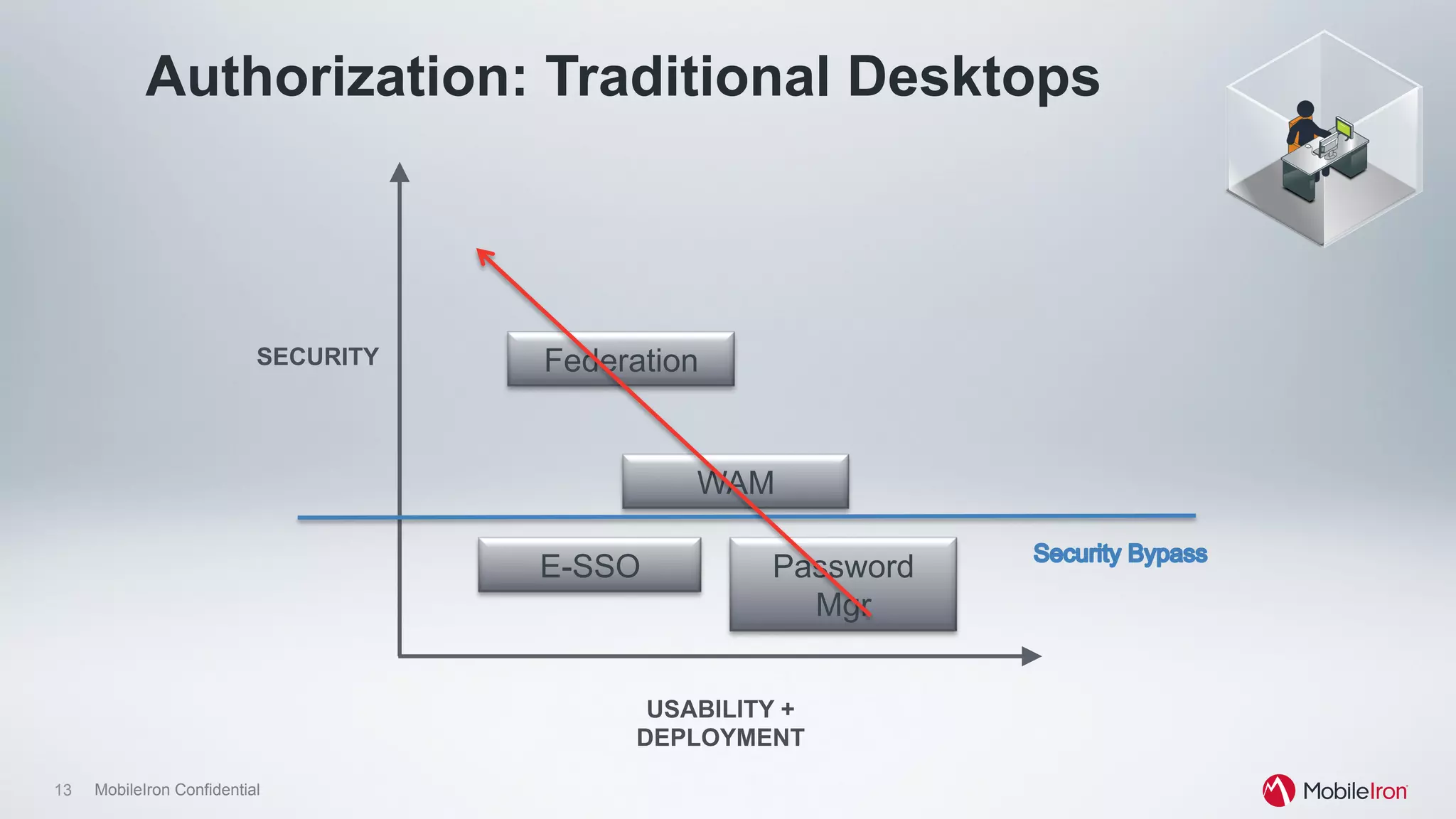
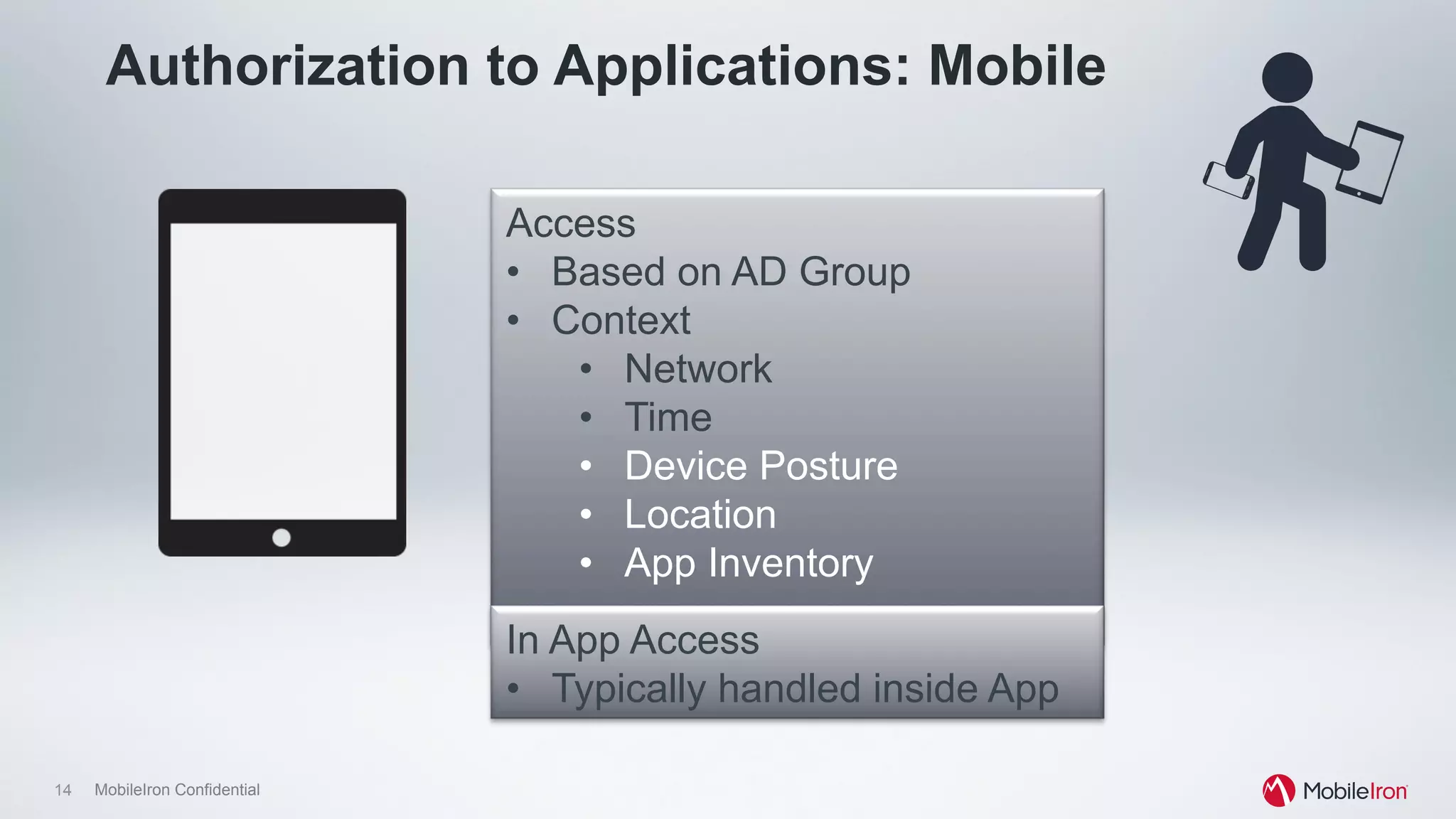
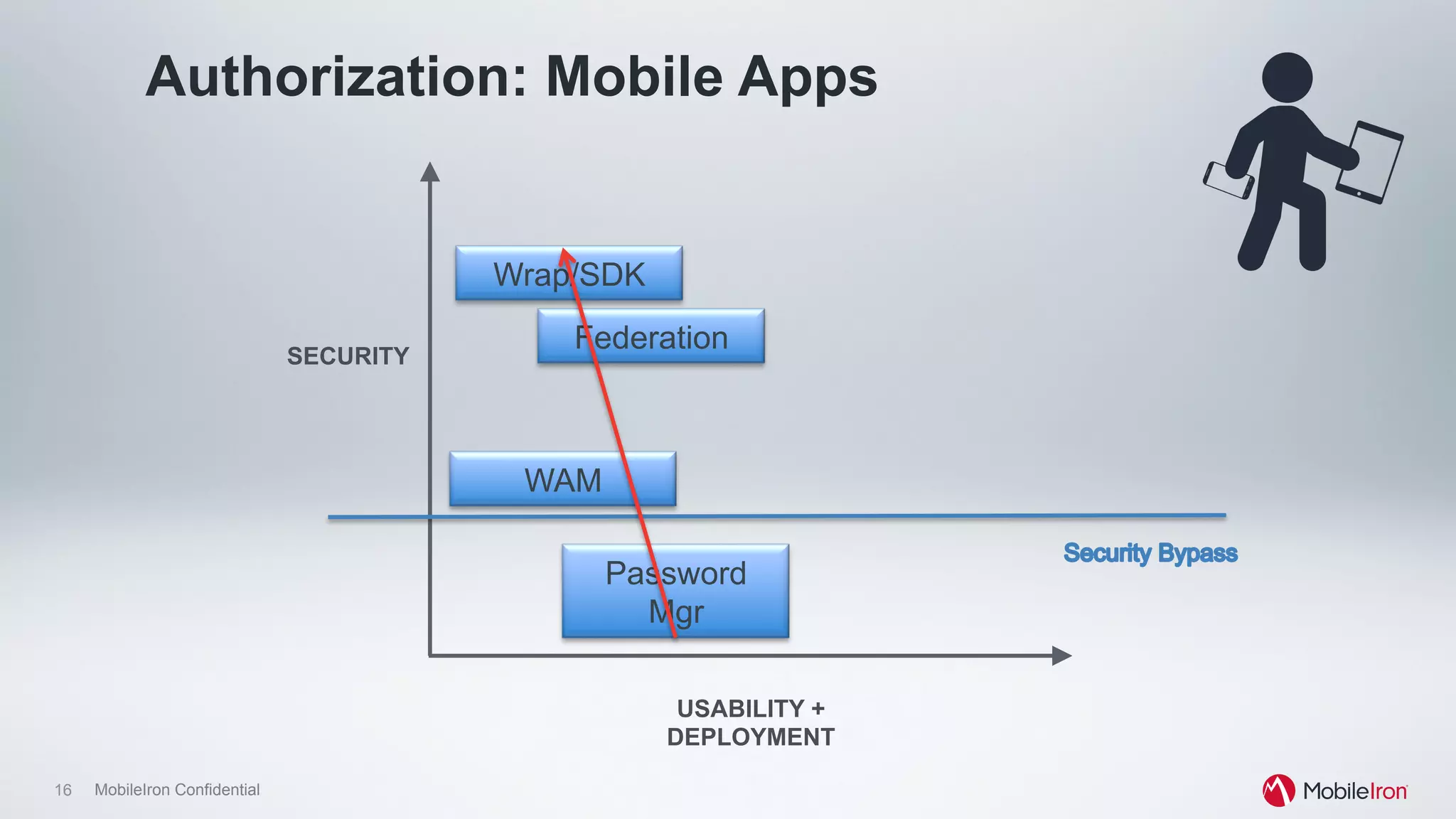
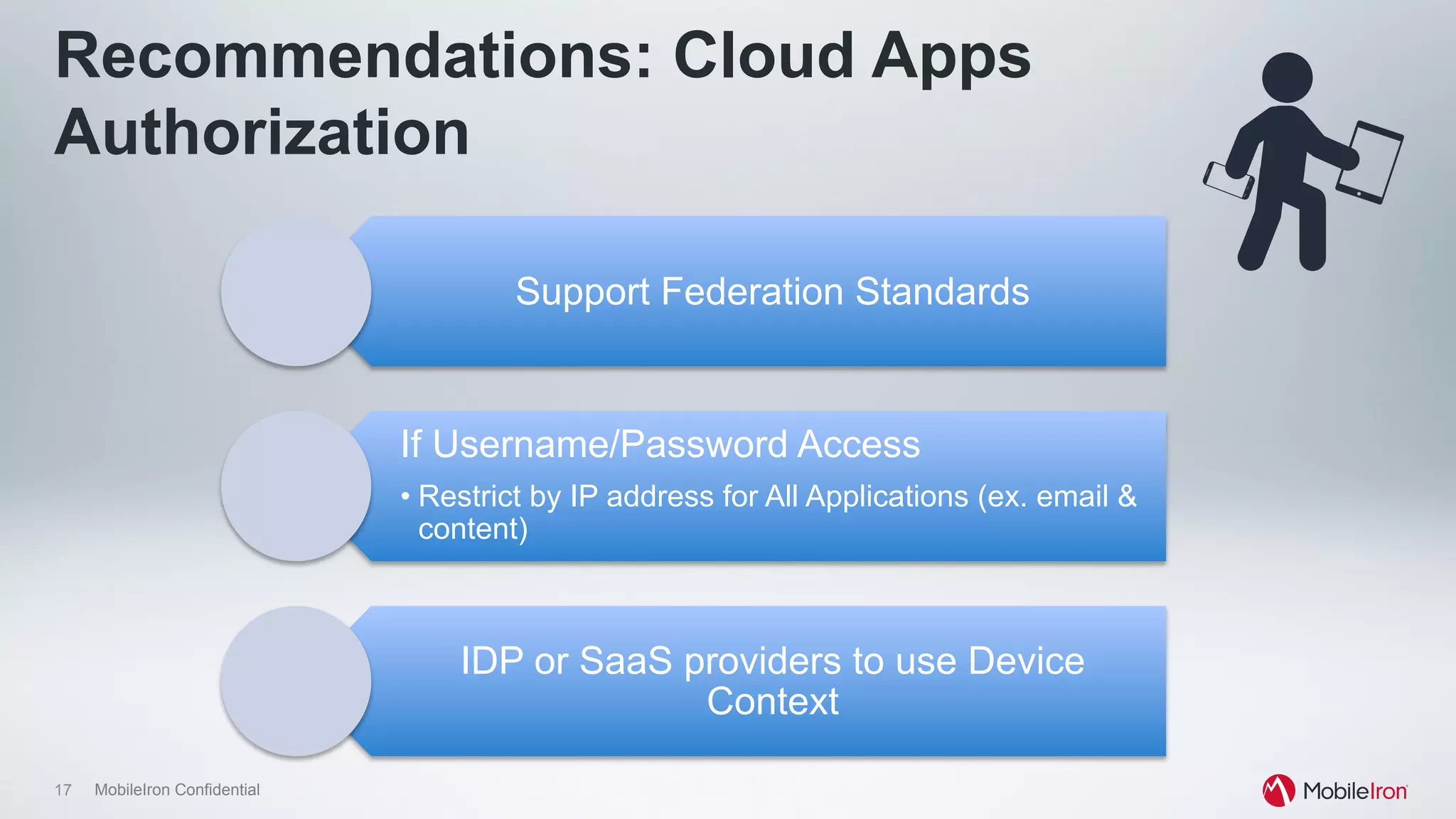
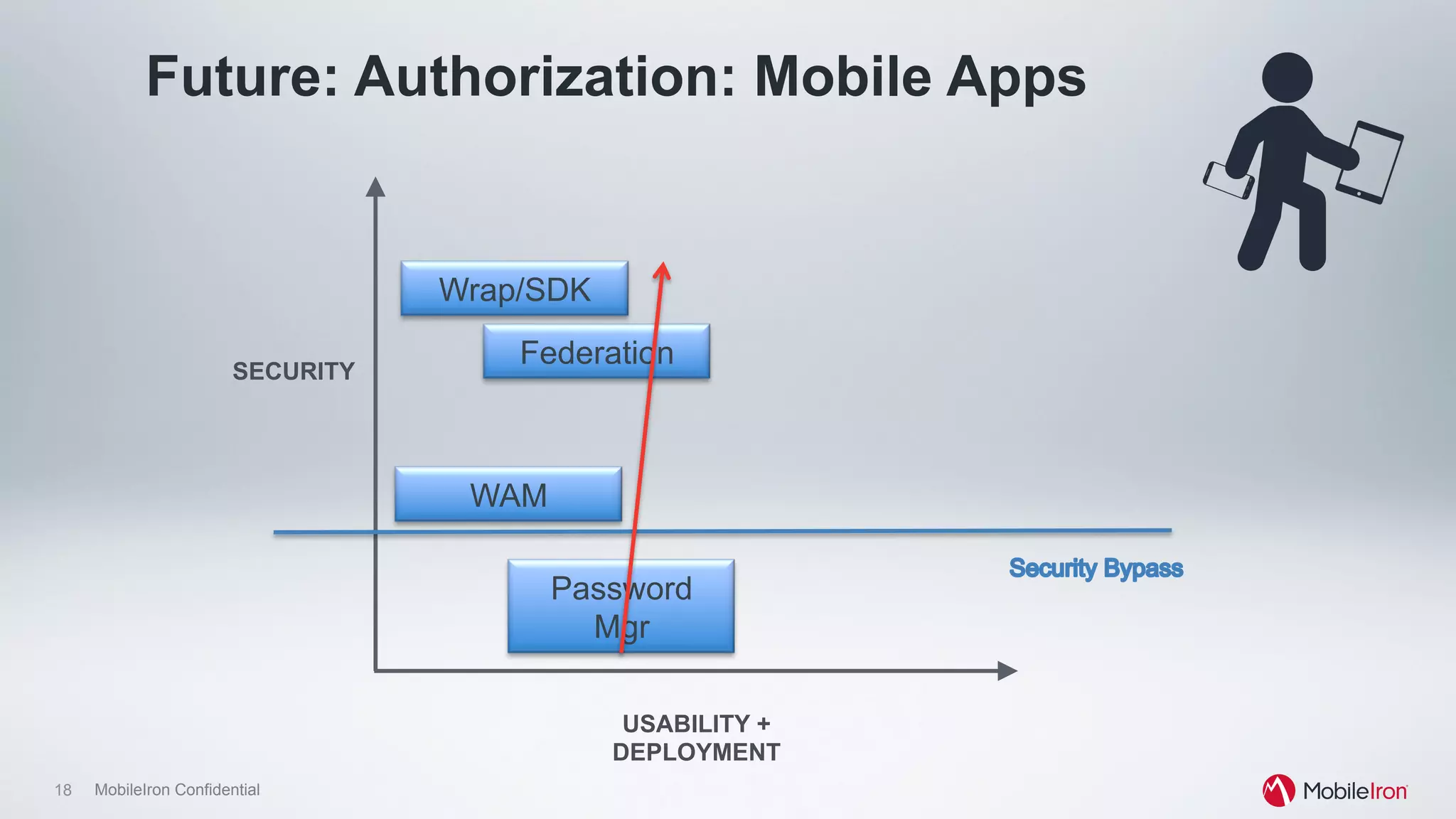
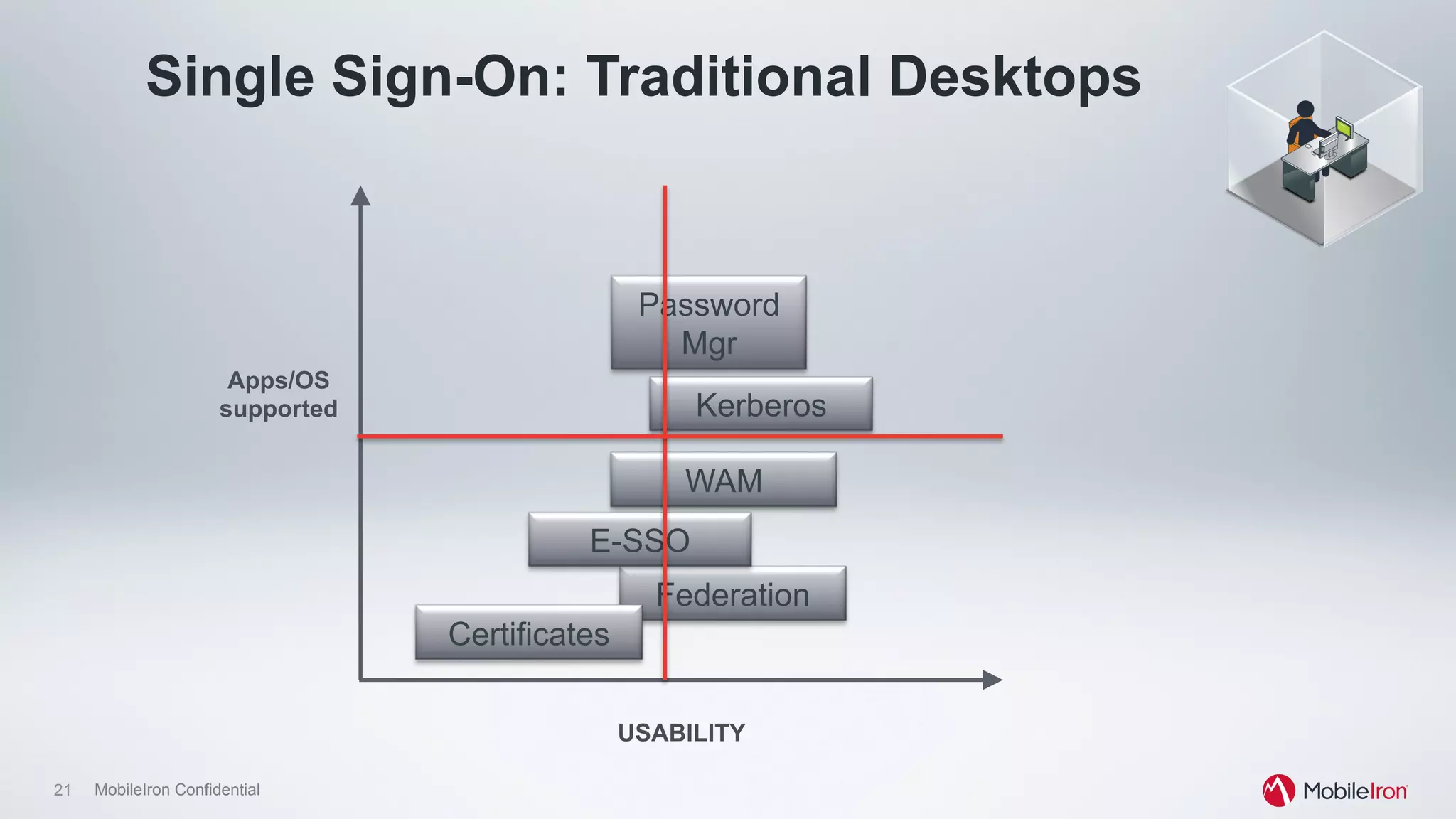
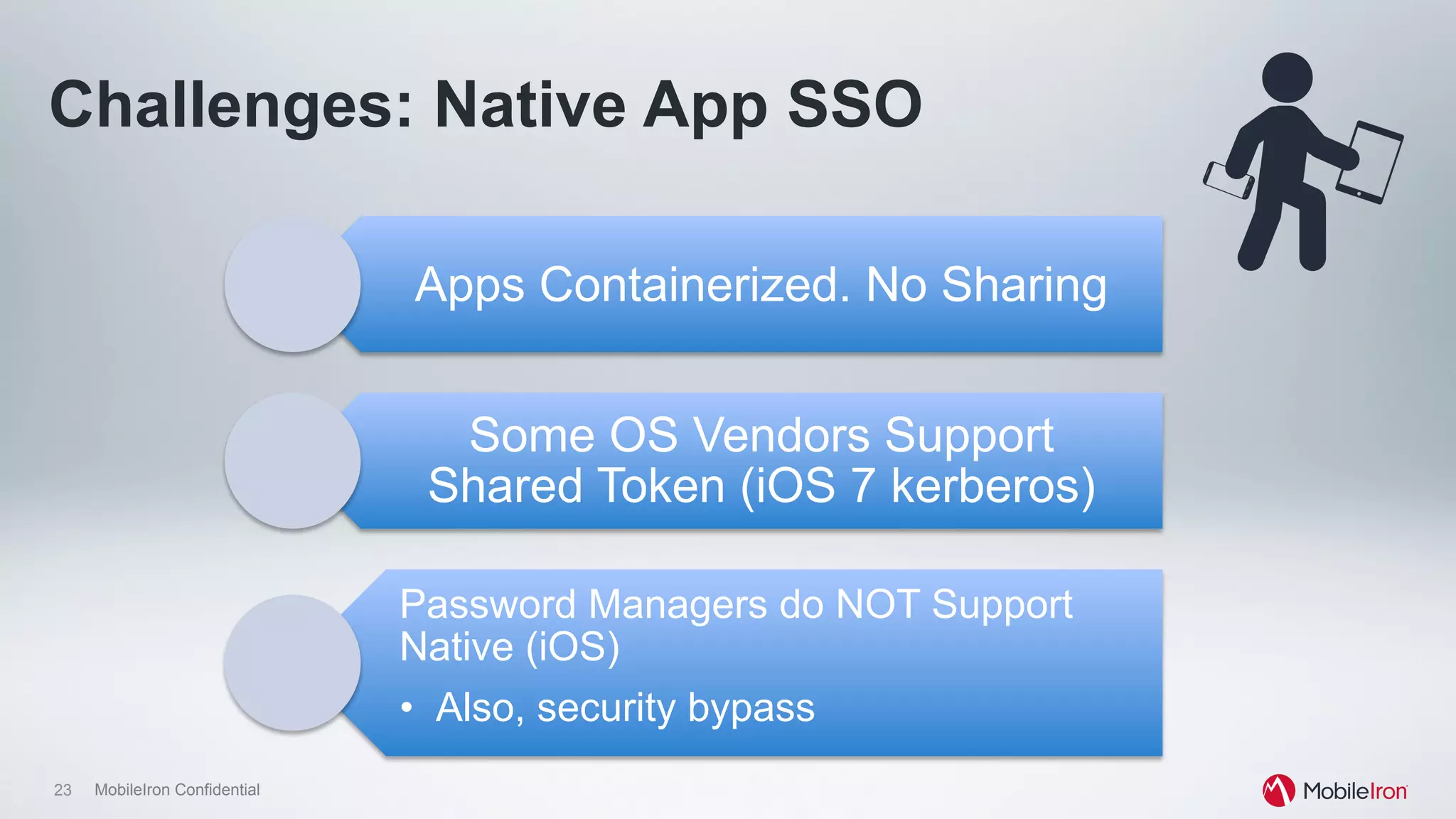
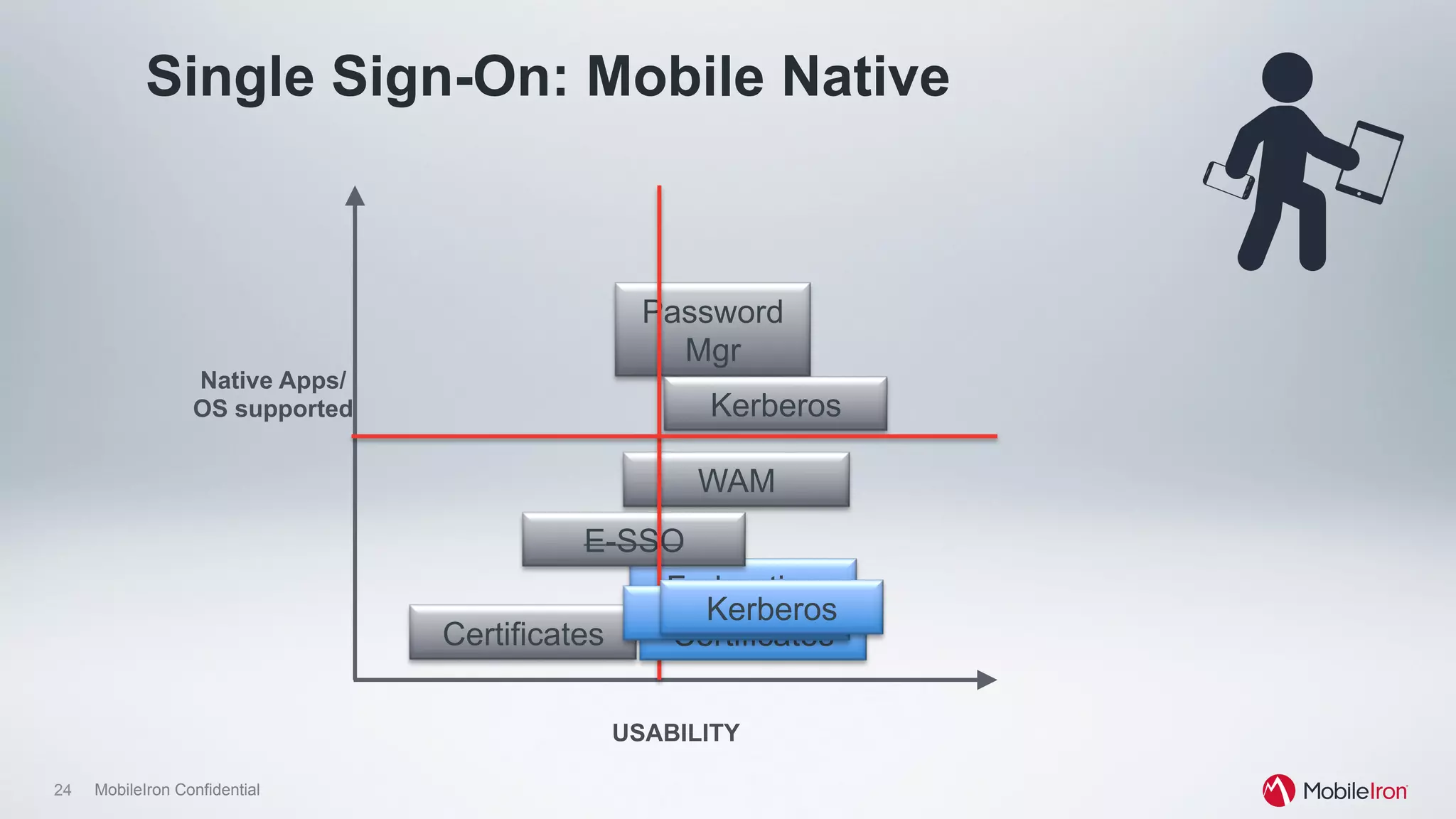
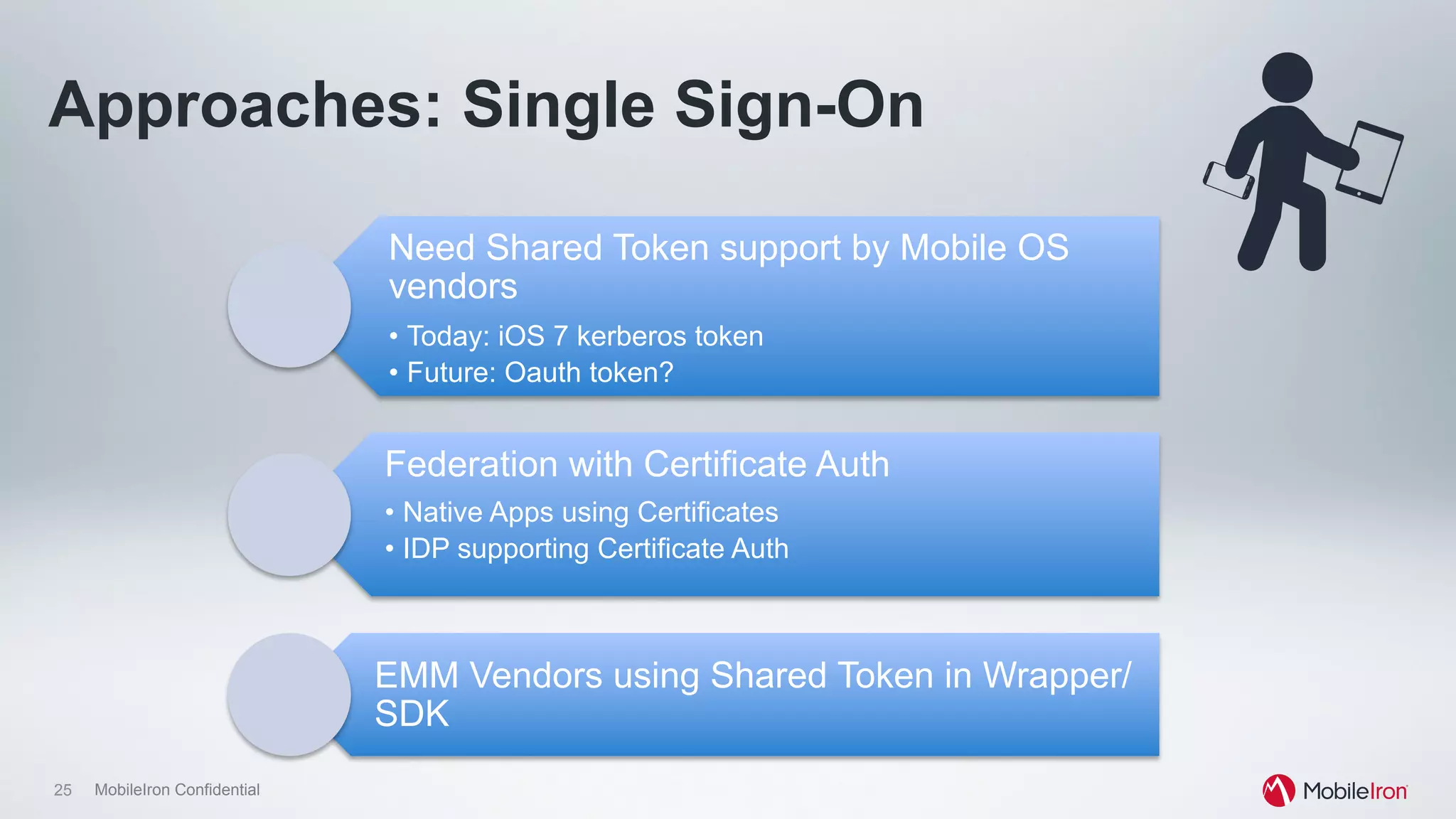
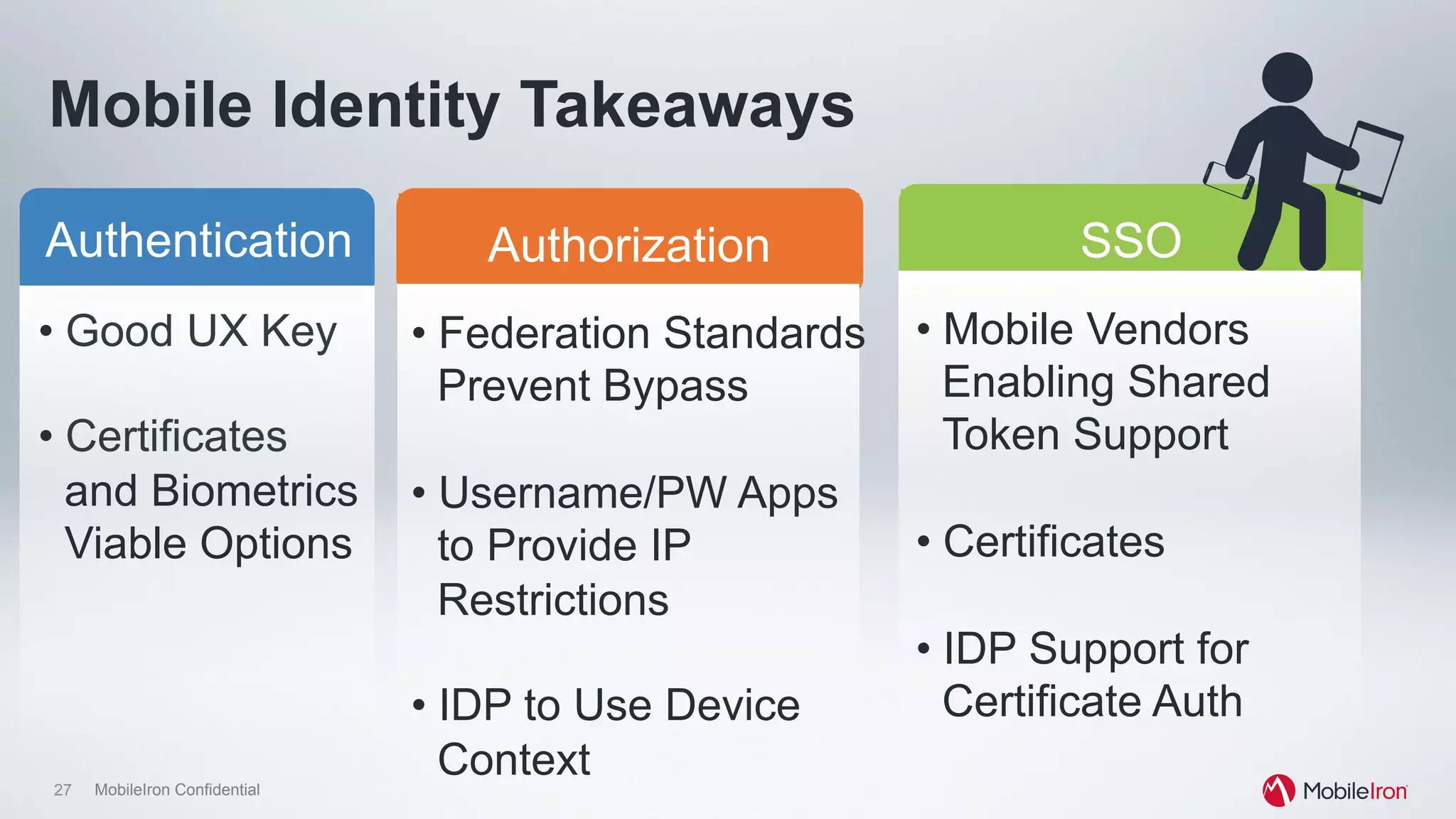
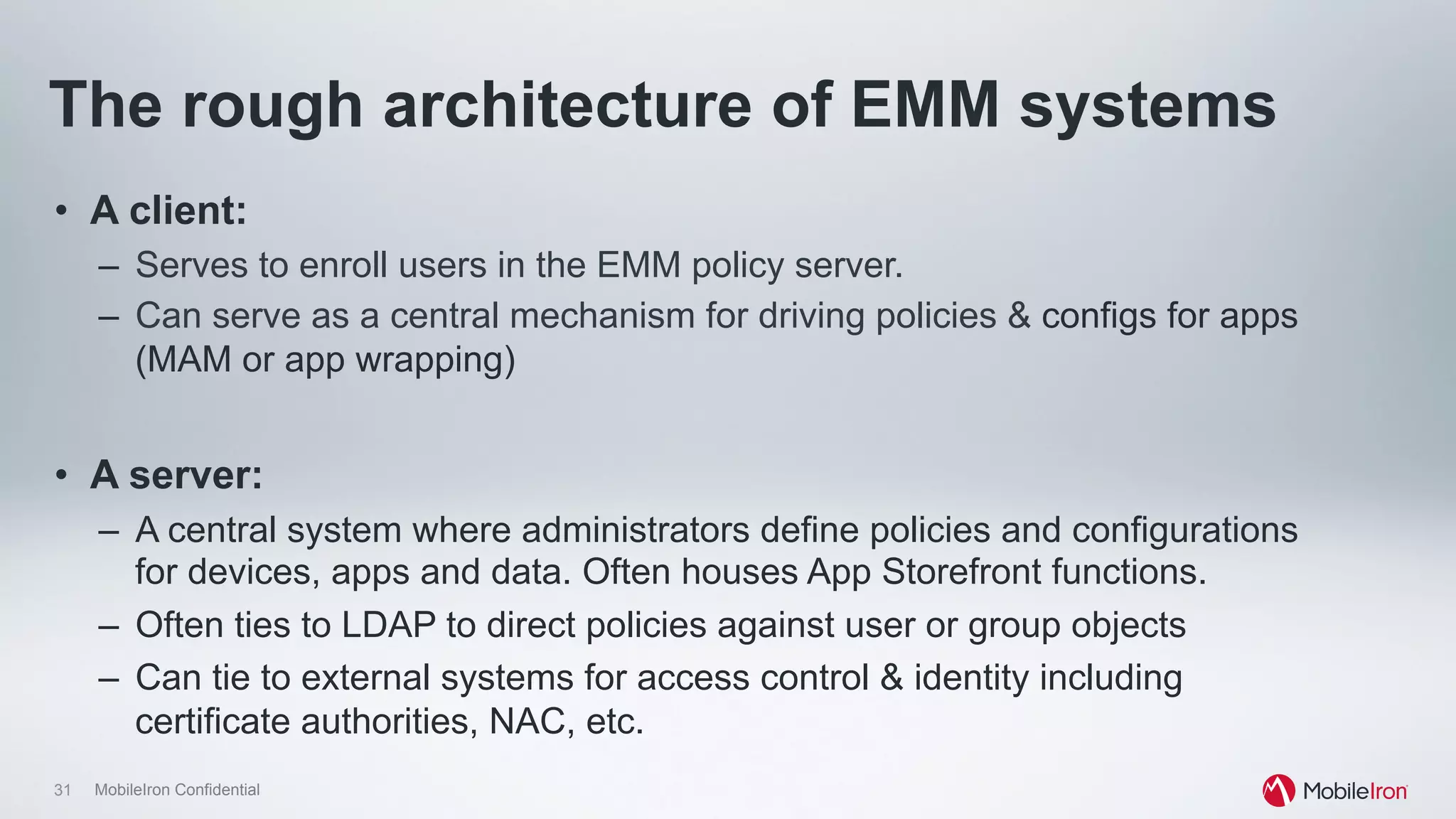
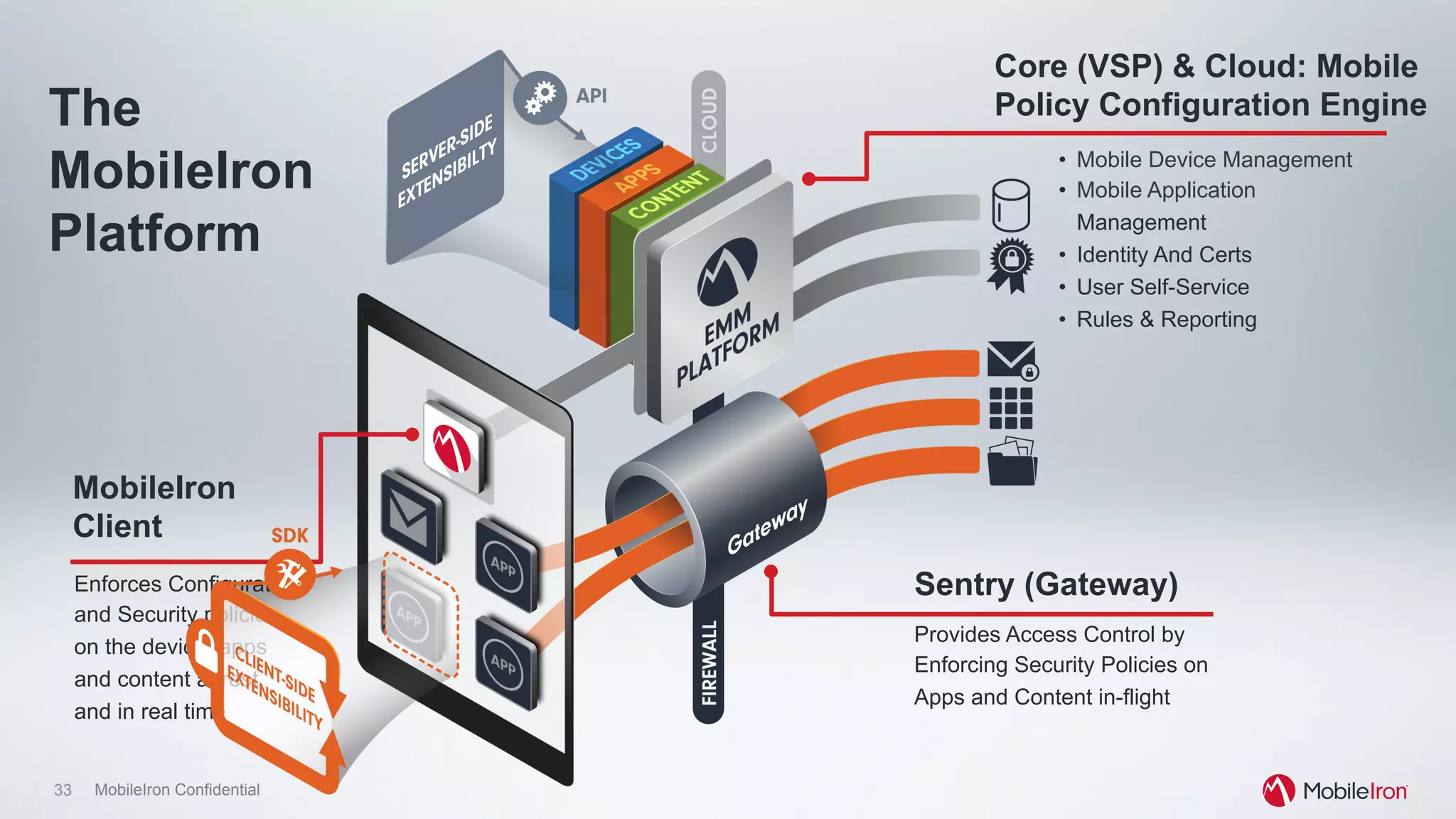
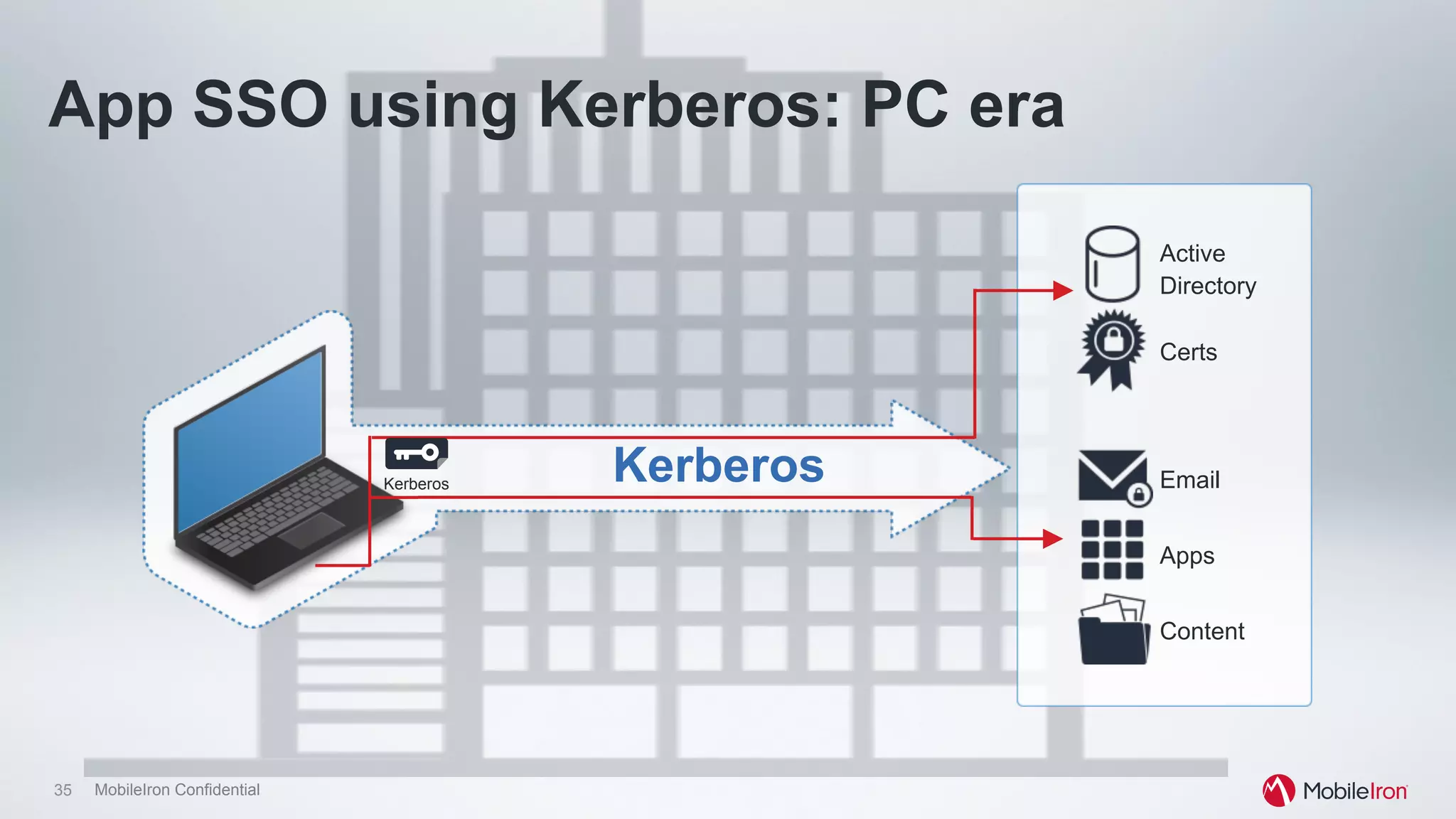
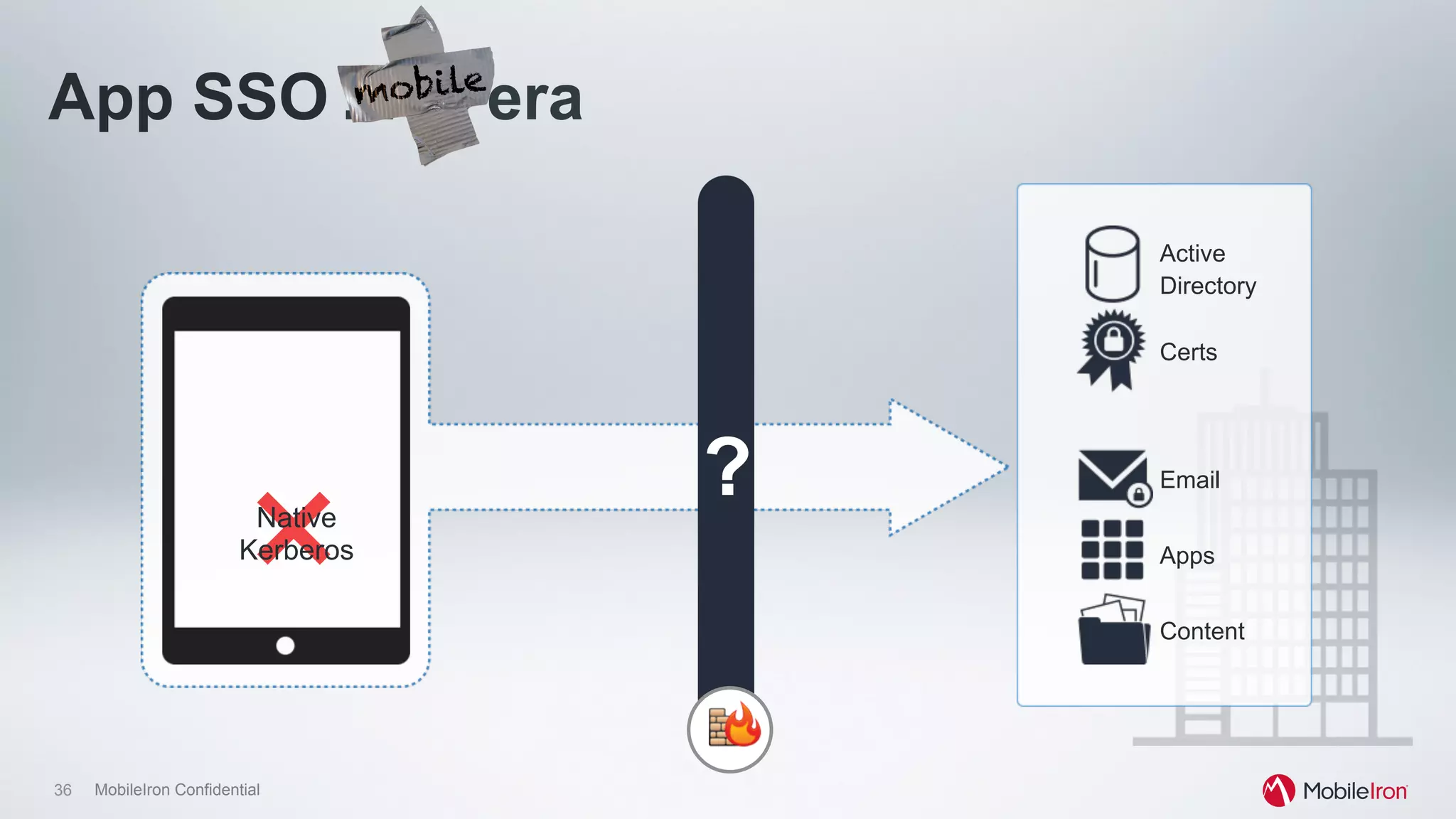
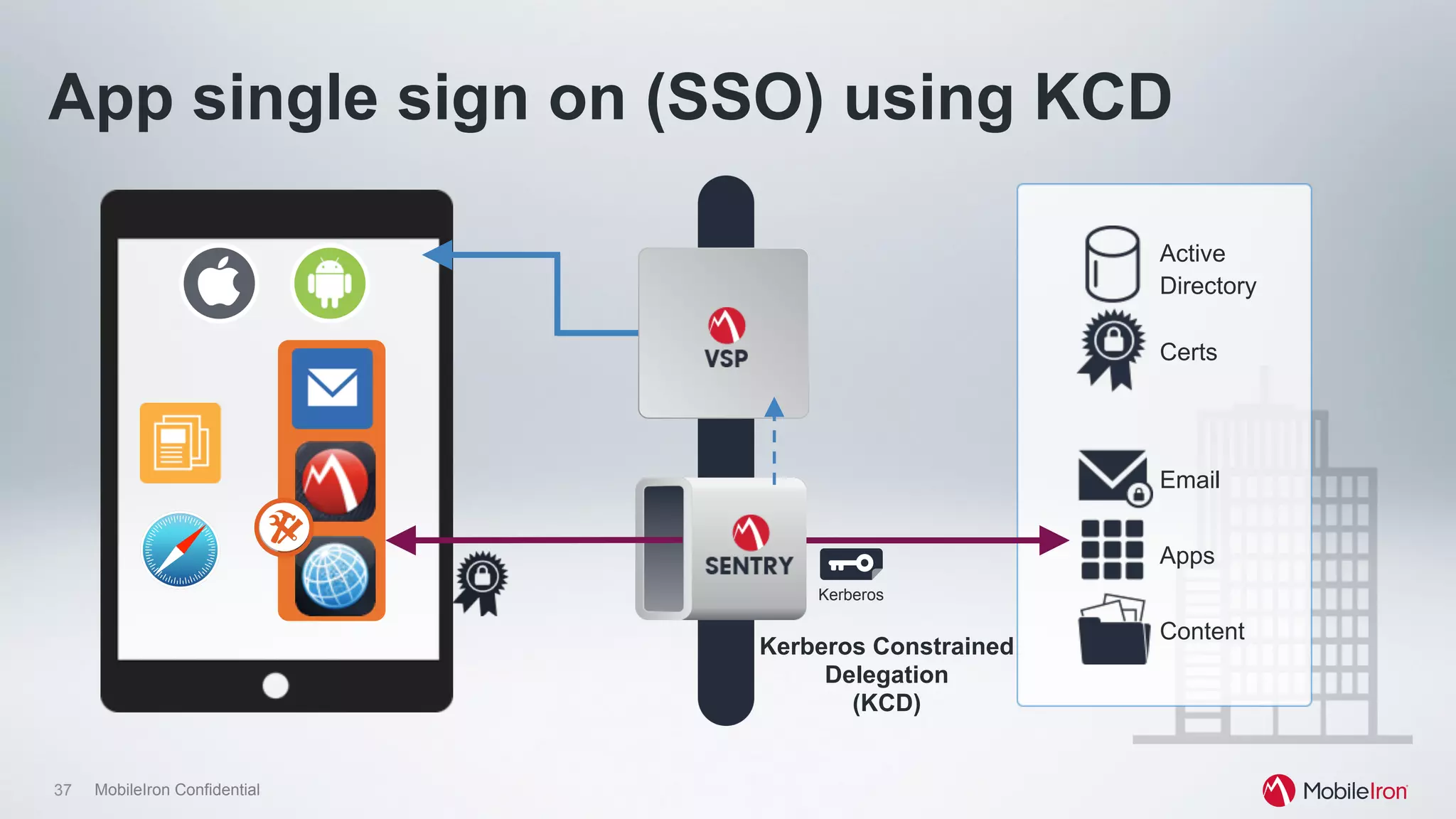
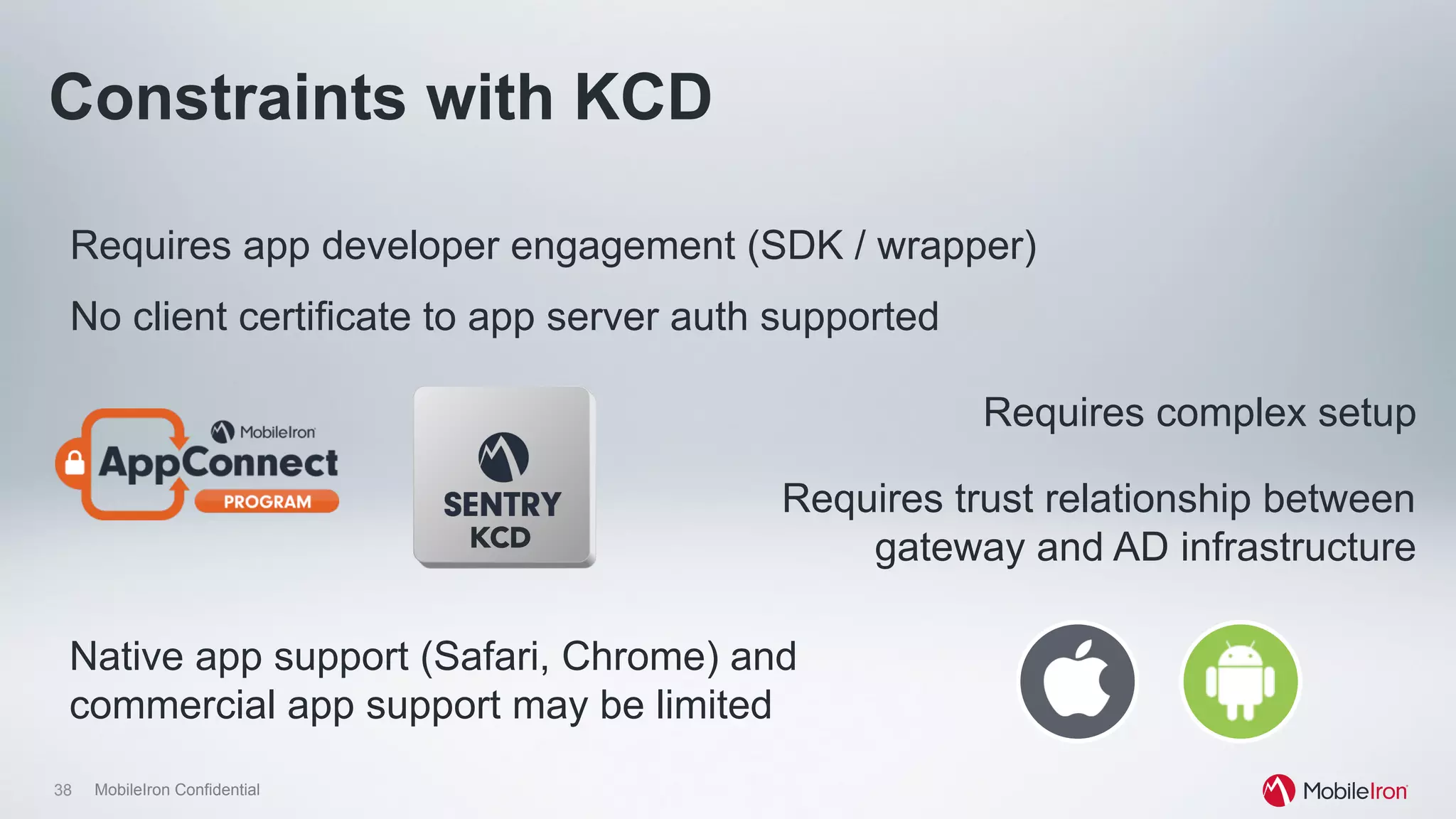
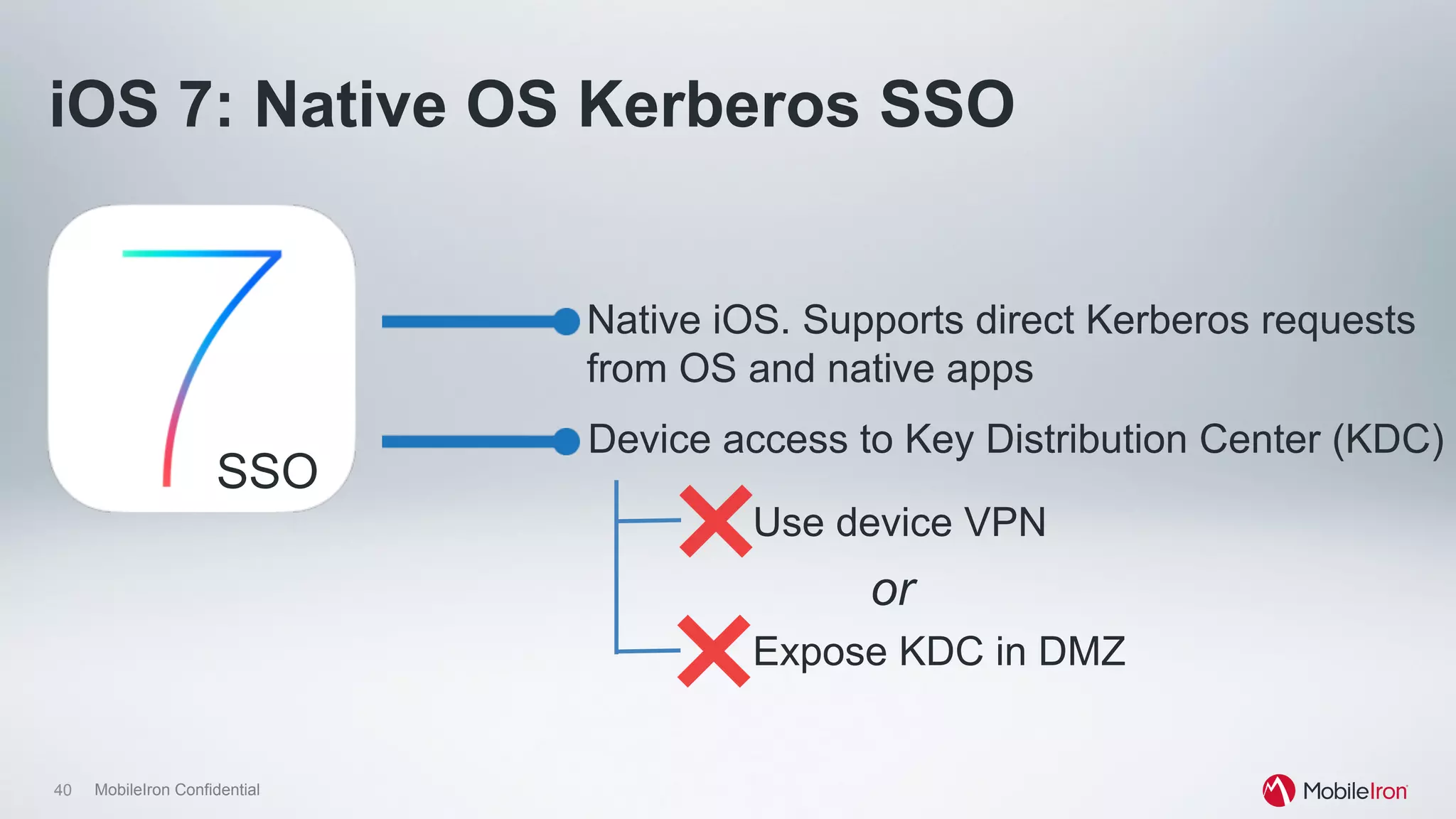
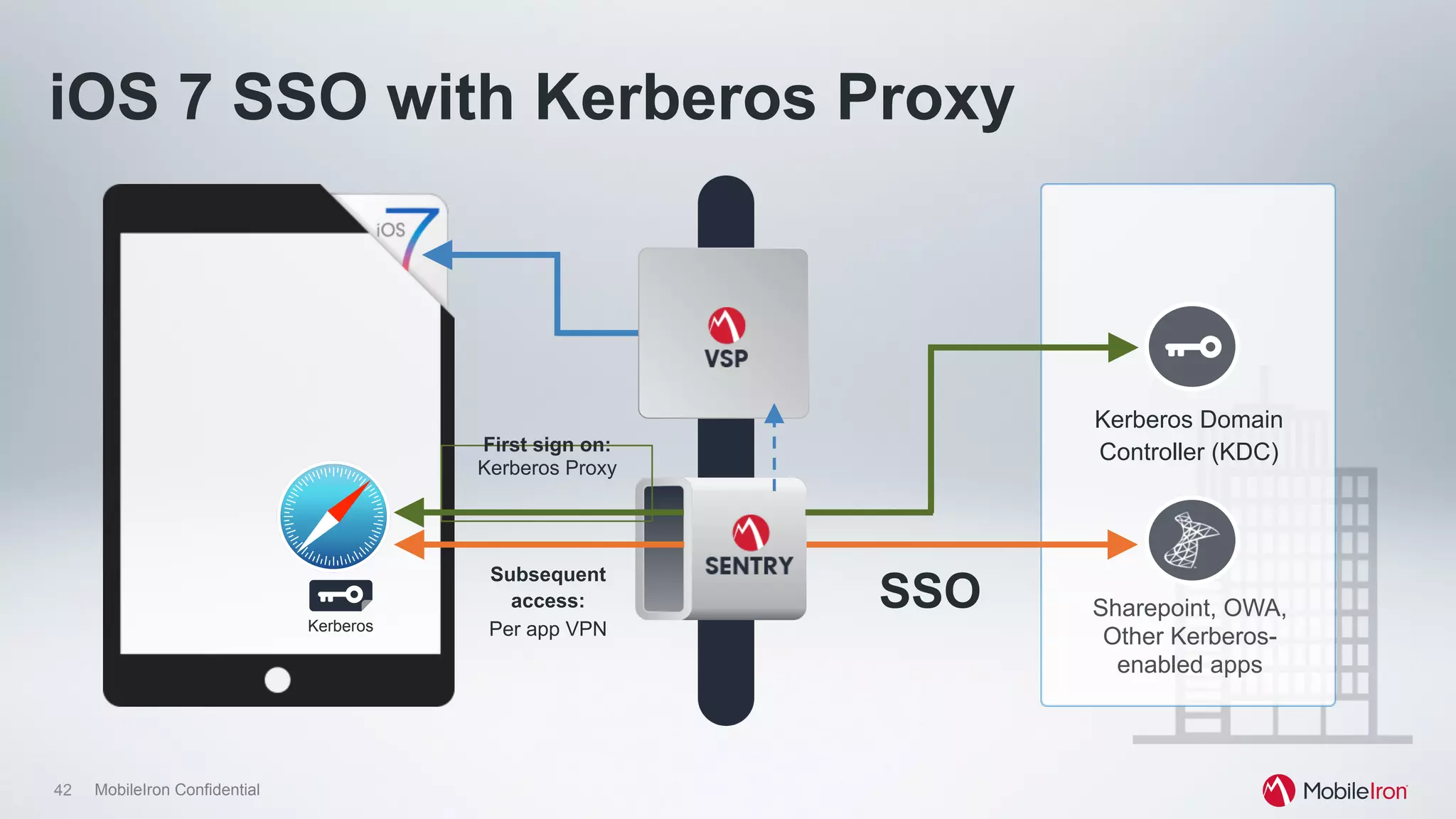
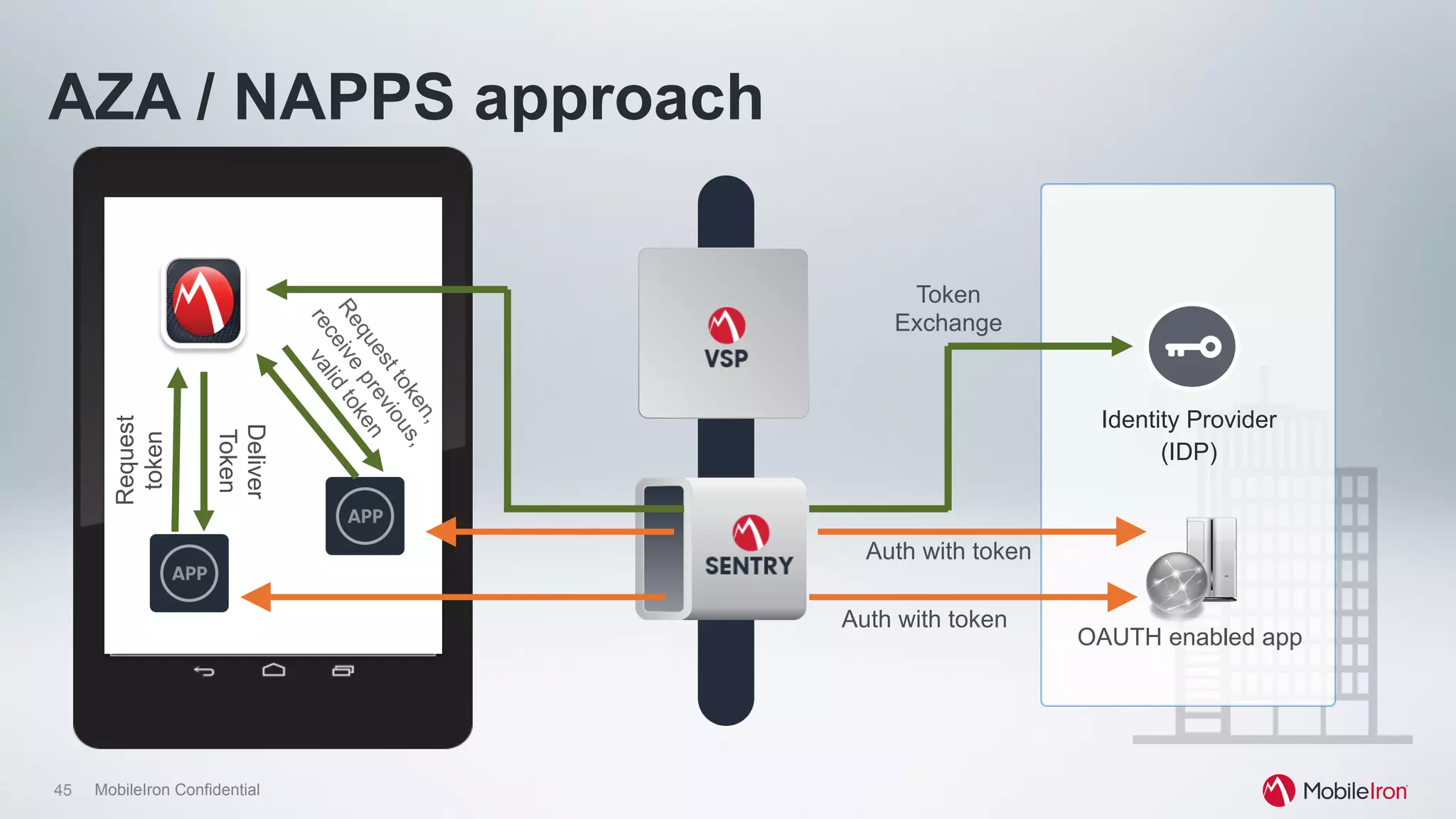
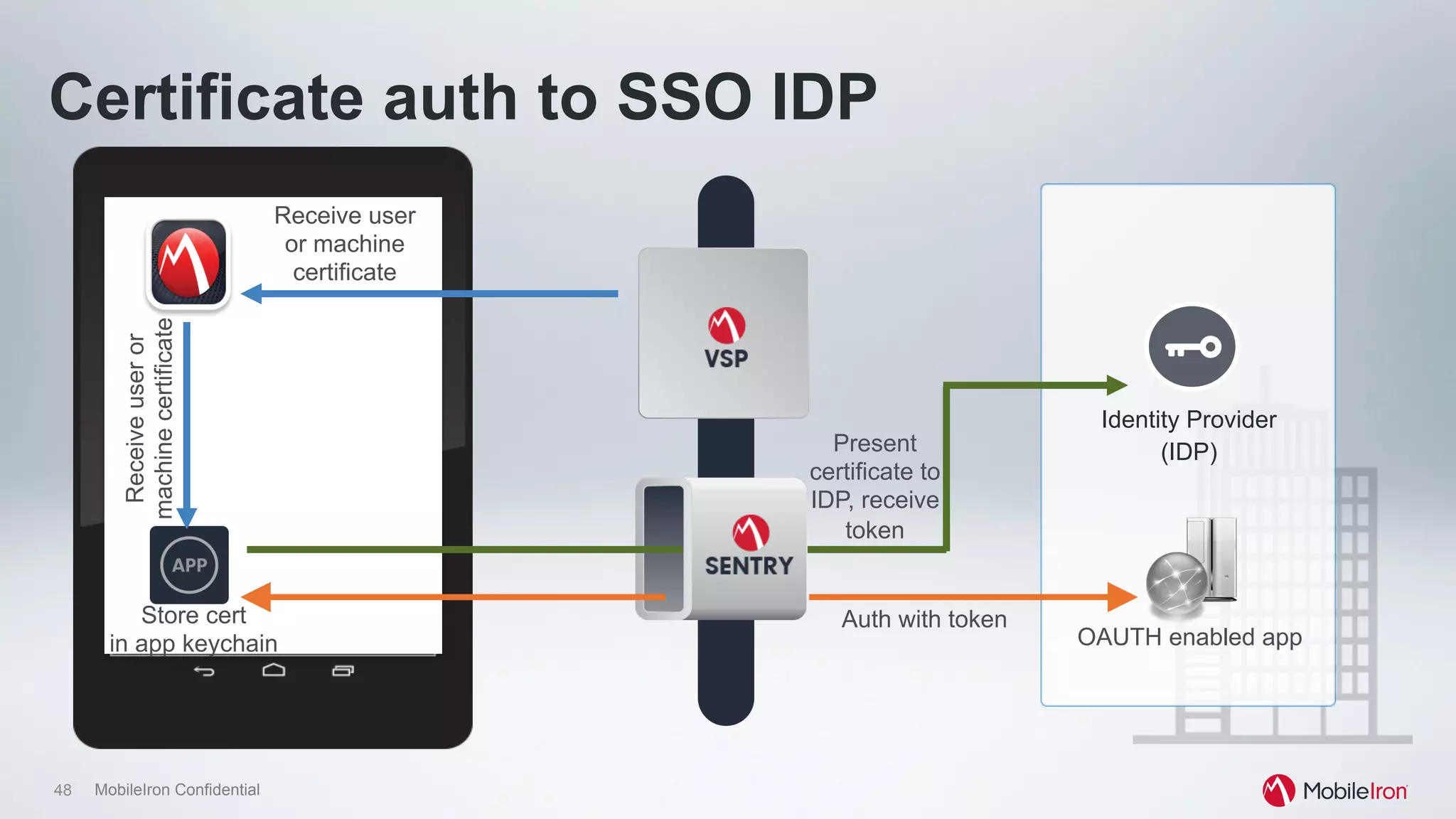
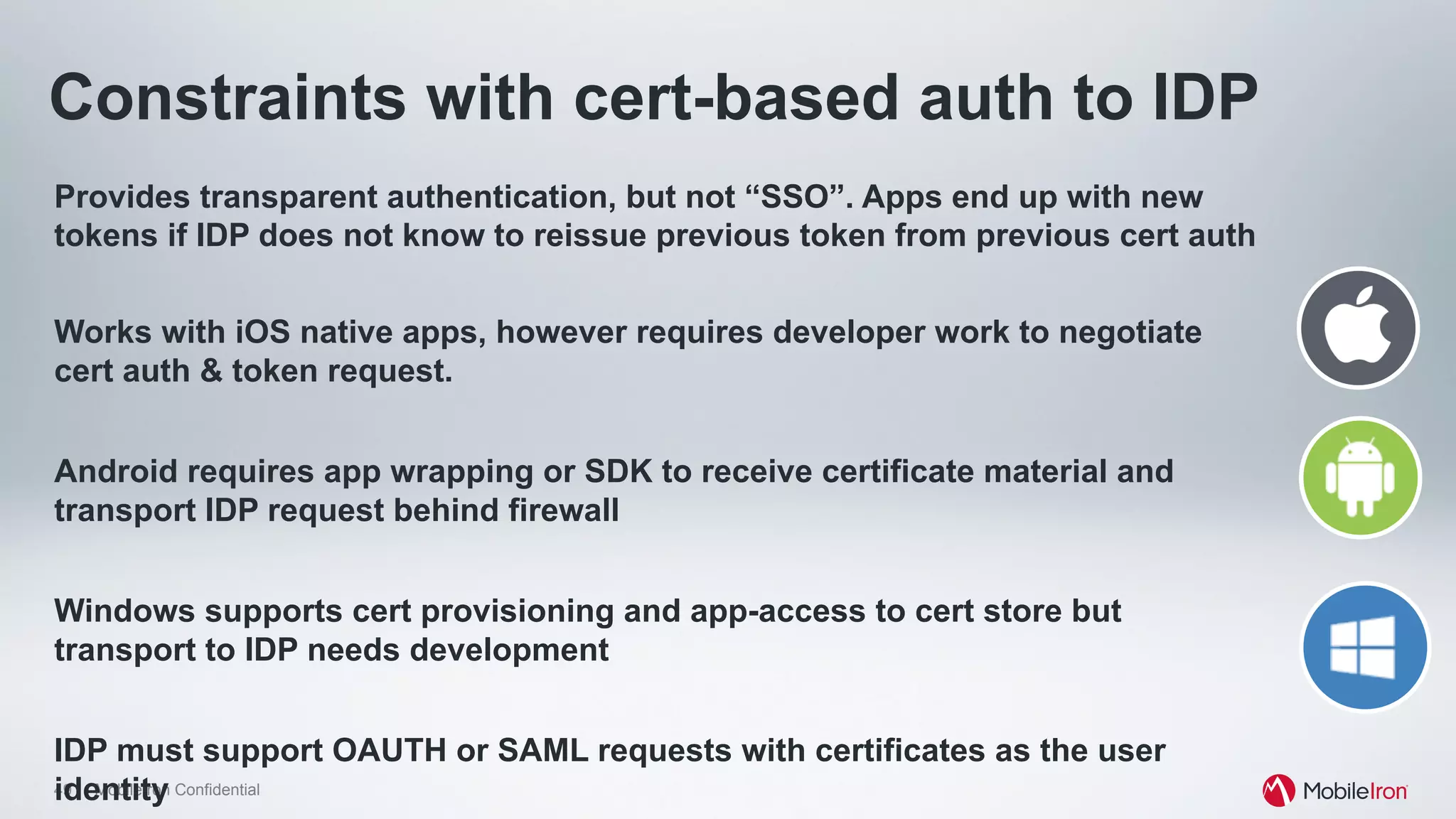
The document discusses security and identity management in a mobile-first world, highlighting various authentication methods such as passwords, biometrics, and certificates. It emphasizes the challenges and considerations for implementing single sign-on (SSO) in mobile applications, including the need for shared token support and seamless user experience. Additionally, it outlines the architecture of enterprise mobility management (EMM) systems and the evolution of standards in mobile identity and access management.