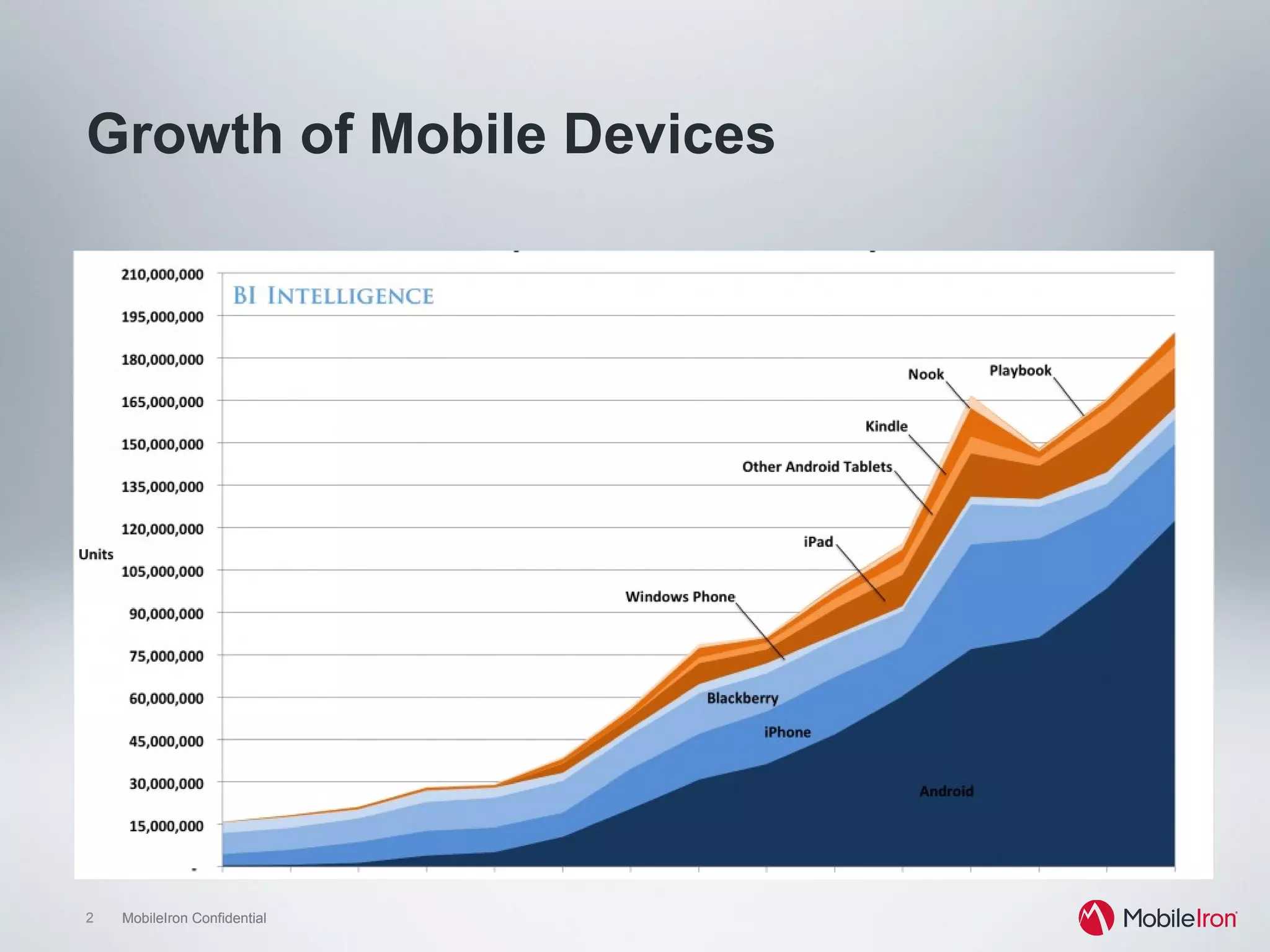
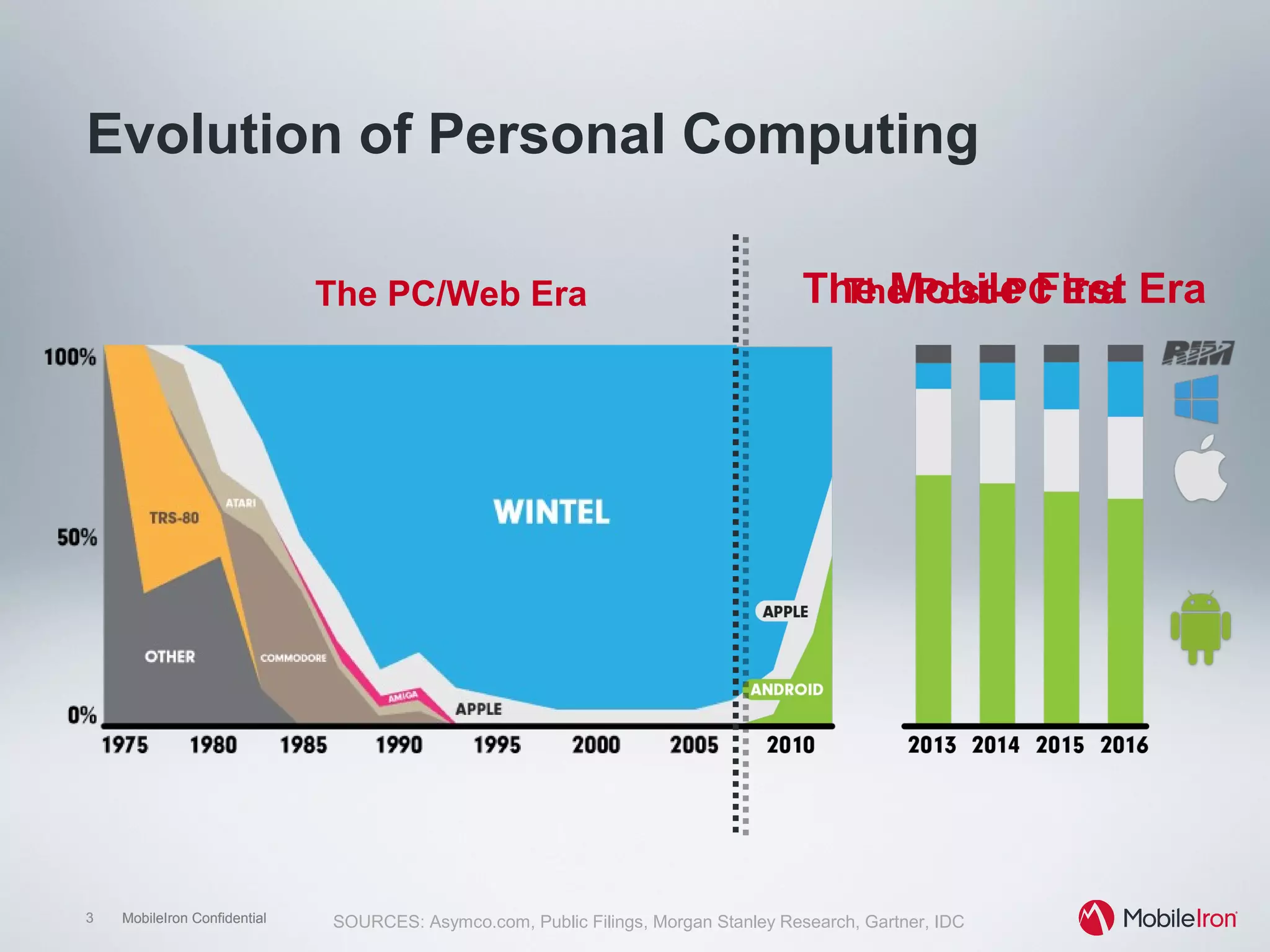
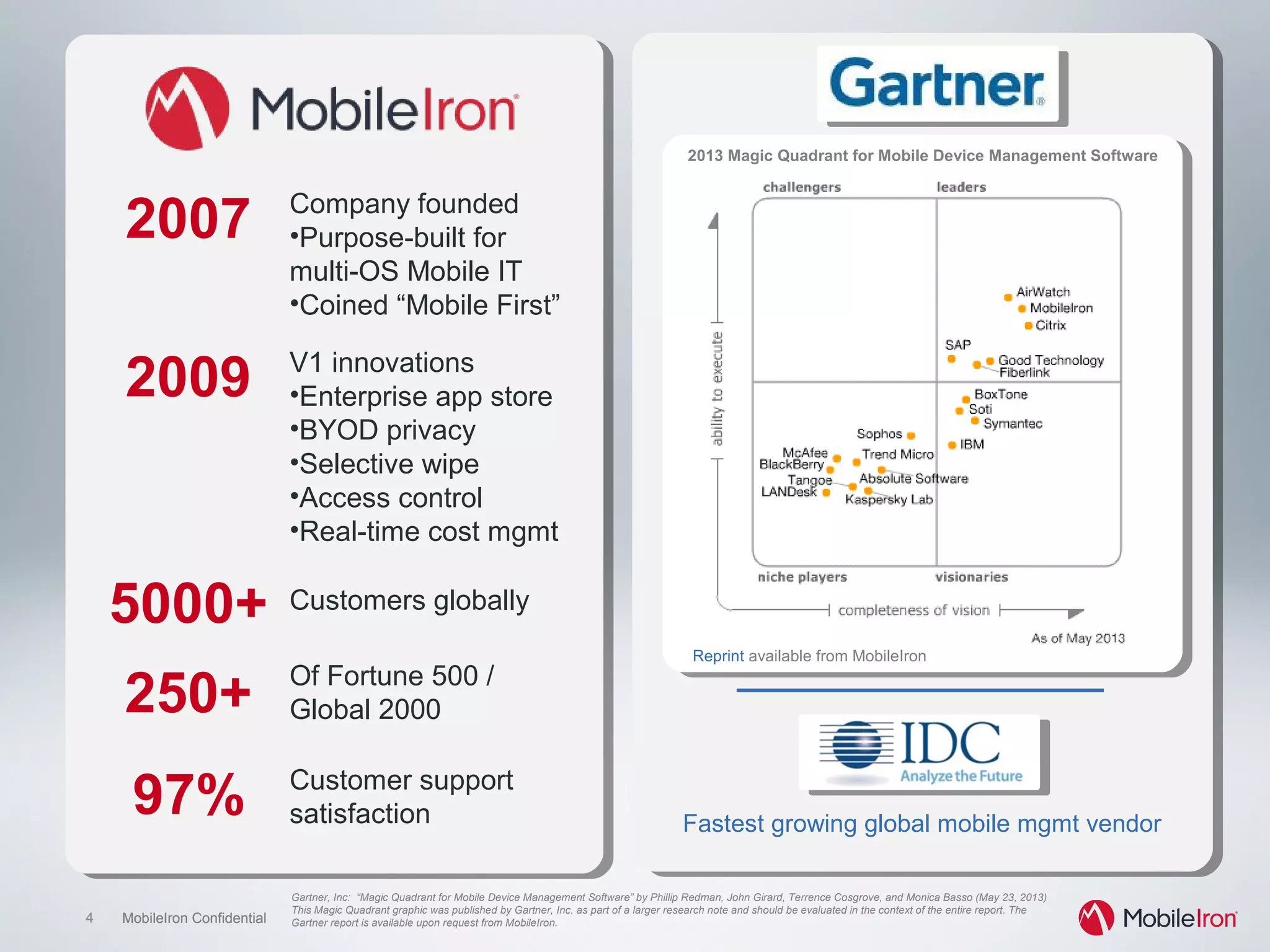
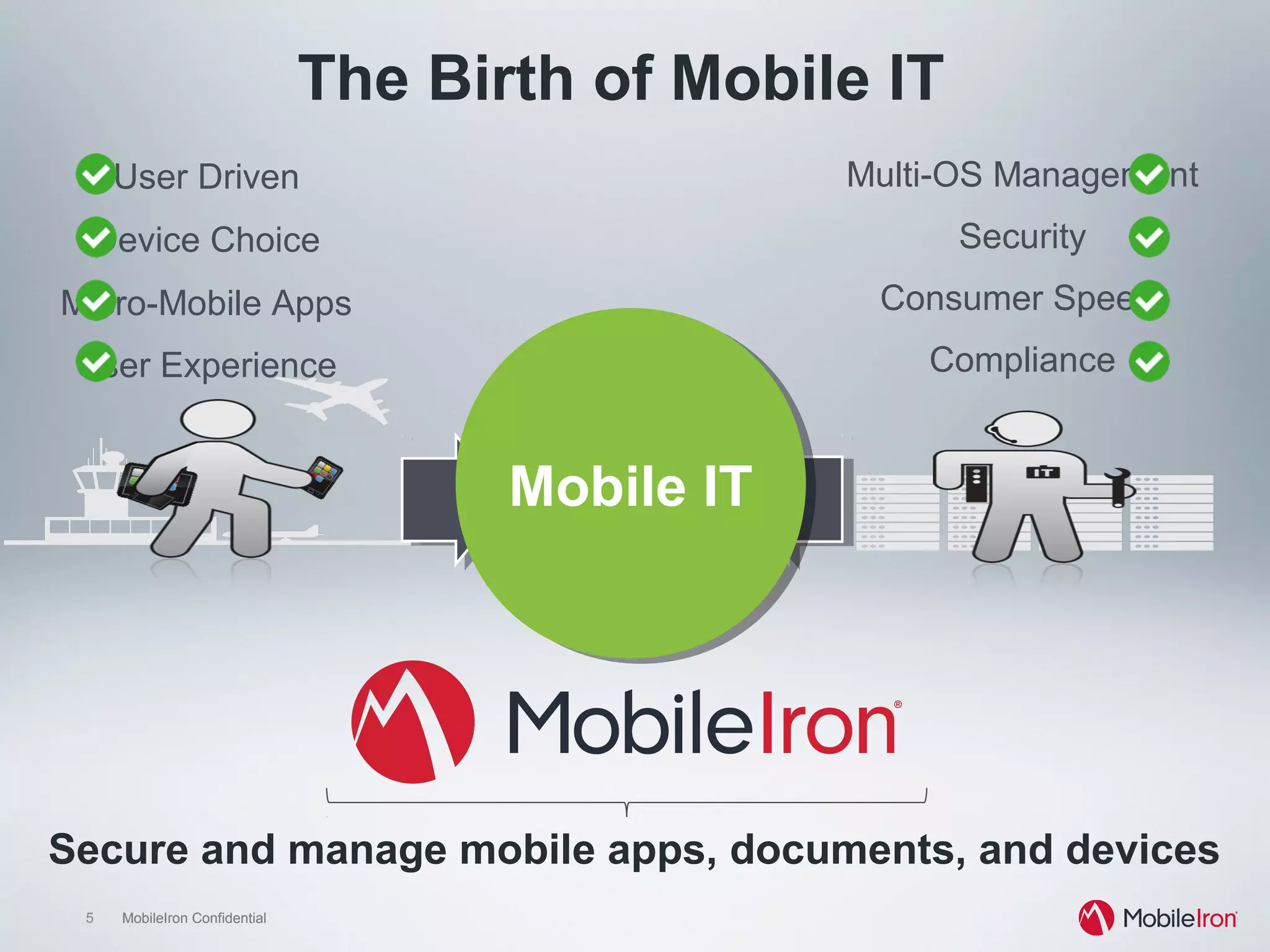
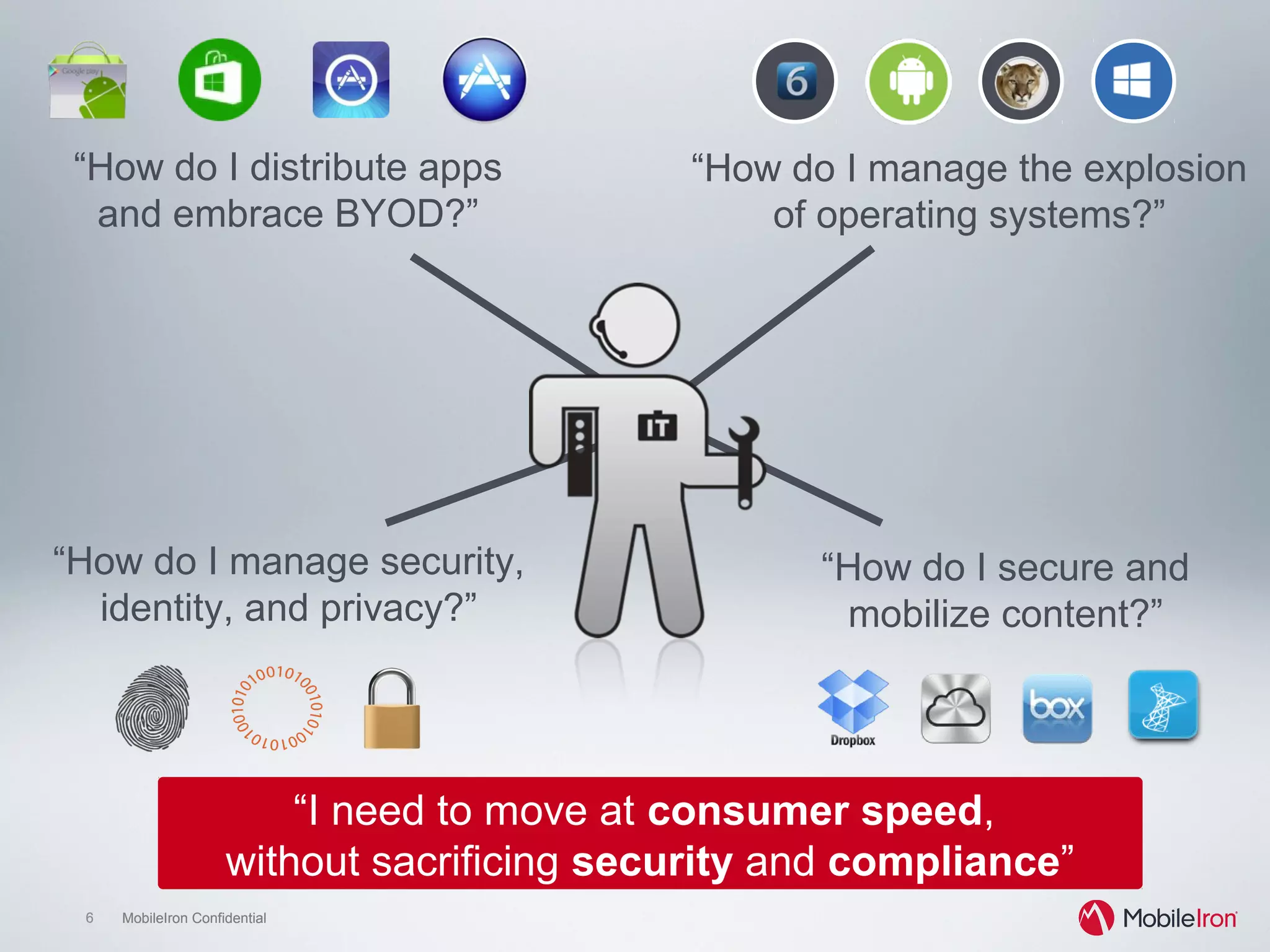
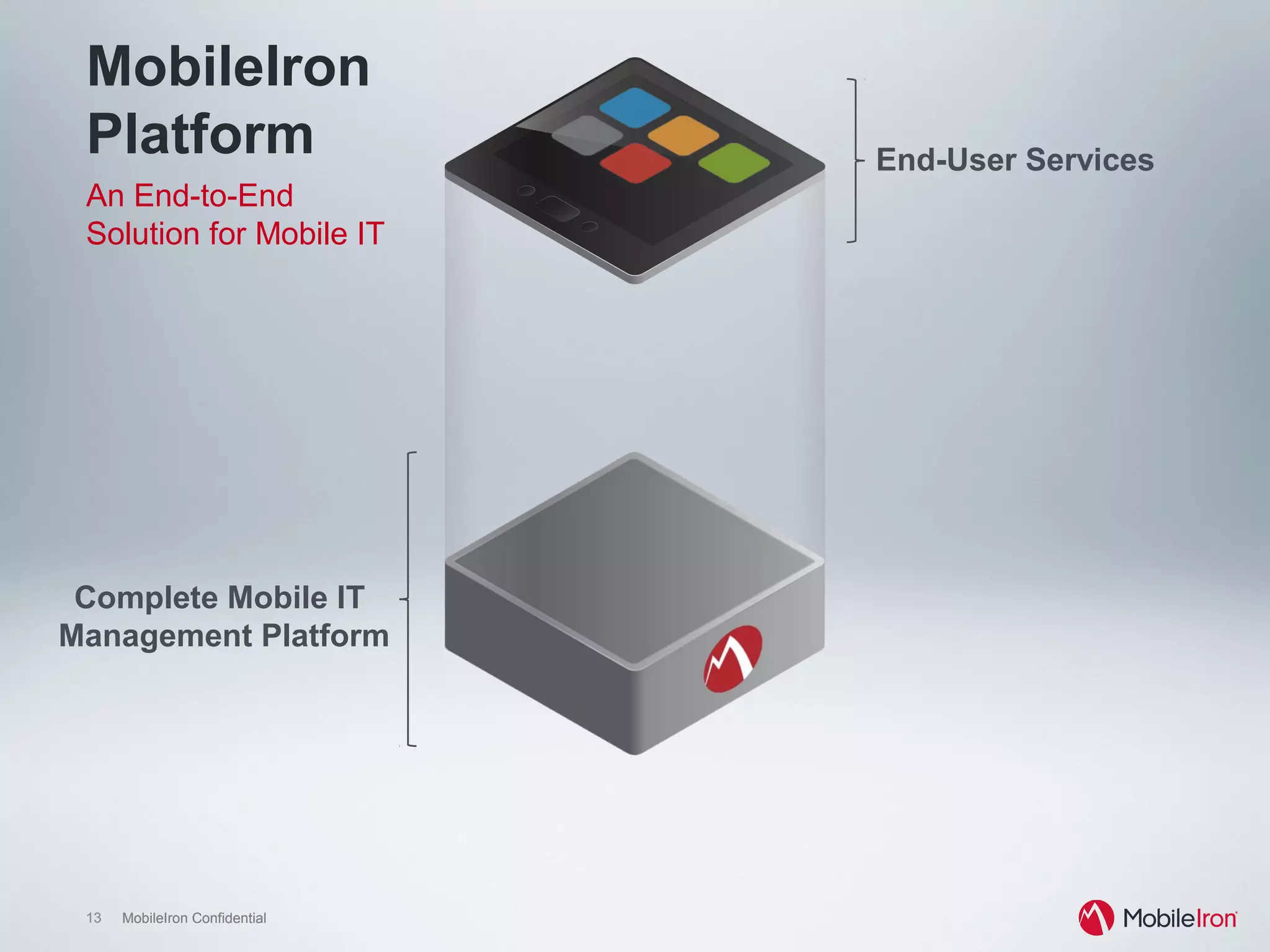
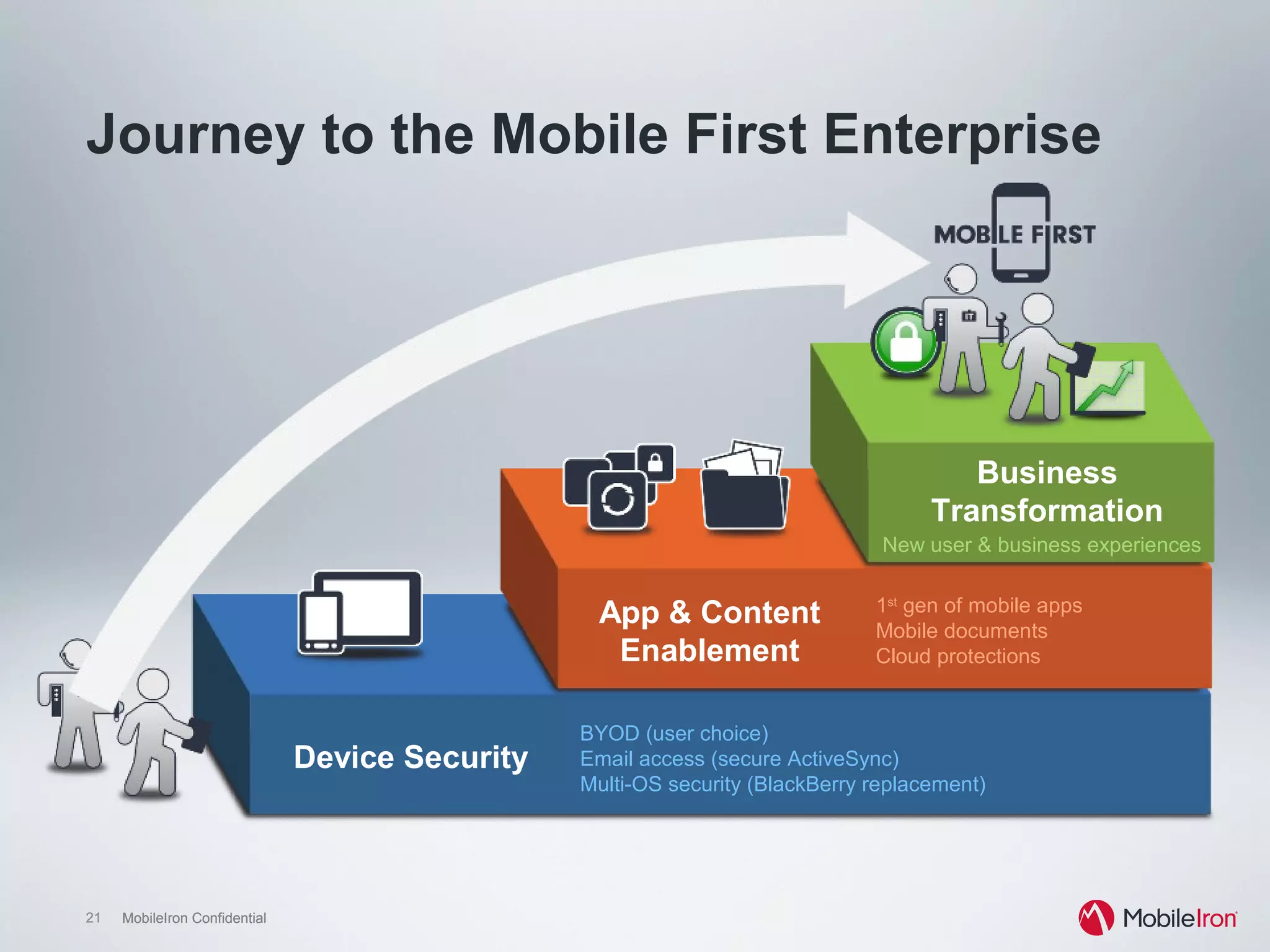
The document discusses the evolution towards a 'mobile first' organizational strategy facilitated by MobileIron's management platform, which supports multi-OS mobile IT and enhances security and compliance. It highlights the increasing use of mobile devices across enterprises, with a focus on managing applications, content, and devices effectively, while also improving user experience and operational efficiency. Case studies demonstrate successful implementations in various sectors, showcasing benefits such as increased employee productivity and satisfaction.






![24 MobileIron Confidential24 MobileIron Confidential
Click image for story
Click image for story
Barclays Capital
Creating an internal app storefront
“My iPad is fully secure. I have an internal
app store we deployed with MobileIron and
there is heavy mobile device management
on it. It knows where it is, and what
networks it is allowed to attach to.”
“Obviously, you can’t stick [an internal app]
into Google’s store or Apple’s store, so you
have to be able to deploy it where you want
it, very securely. That’s the basis for an
internal app store.”
Shaygan Kheradpir, COO, Barclays Retail](https://image.slidesharecdn.com/dsshtmobileiron2013-130813130837-phpapp02/75/DSS-ITSEC-Webinars-2013-Network-Access-Control-Mobile-Security-MobileIron-24-2048.jpg)