This document discusses memory management techniques used in operating systems, including:
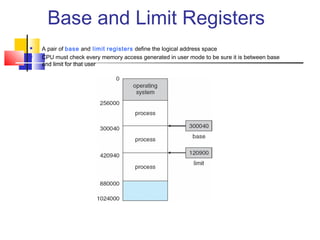
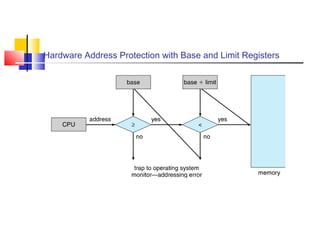
- Base and limit registers that define the logical address space and protect memory accesses.
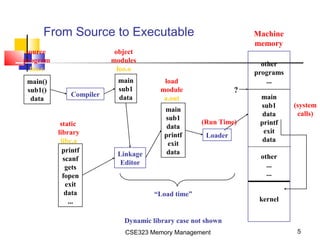
- Address binding from source code to executable addresses at different stages.
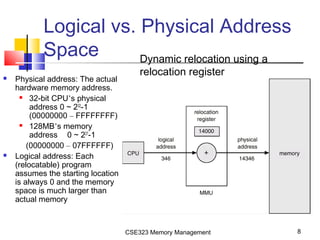
- The memory management unit (MMU) that maps virtual to physical addresses using base/limit registers.
- Segmentation architecture that divides memory into logical segments like code, data, stack, heap.