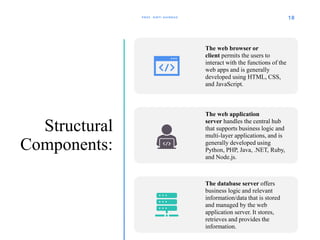
The document provides an overview of web security. It discusses the internet and the World Wide Web, vulnerabilities and threats to web applications like phishing and SQL injection, as well as countermeasures. It also outlines a generic security model covering security policies, host security, network security, organizational security, and legal security. Finally, it examines the components of web application architecture like user interface elements, structural components involving web browsers, application servers, and database servers.