This document provides an overview of hierarchical network design principles and models. It discusses:
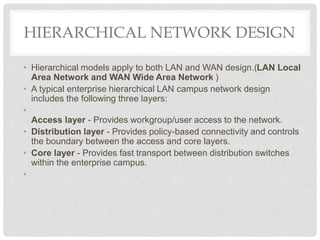
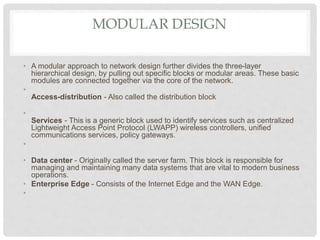
1) Hierarchical network design involves categorizing networks based on device count and dividing networks into access, distribution, and core layers.
2) Access layers provide user access, distribution layers provide connectivity and policy controls, and core layers provide fast transport.
3) Modular and hierarchical designs improve flexibility, management, and scalability. Common modules include campus, enterprise edge, data centers, and remote sites.