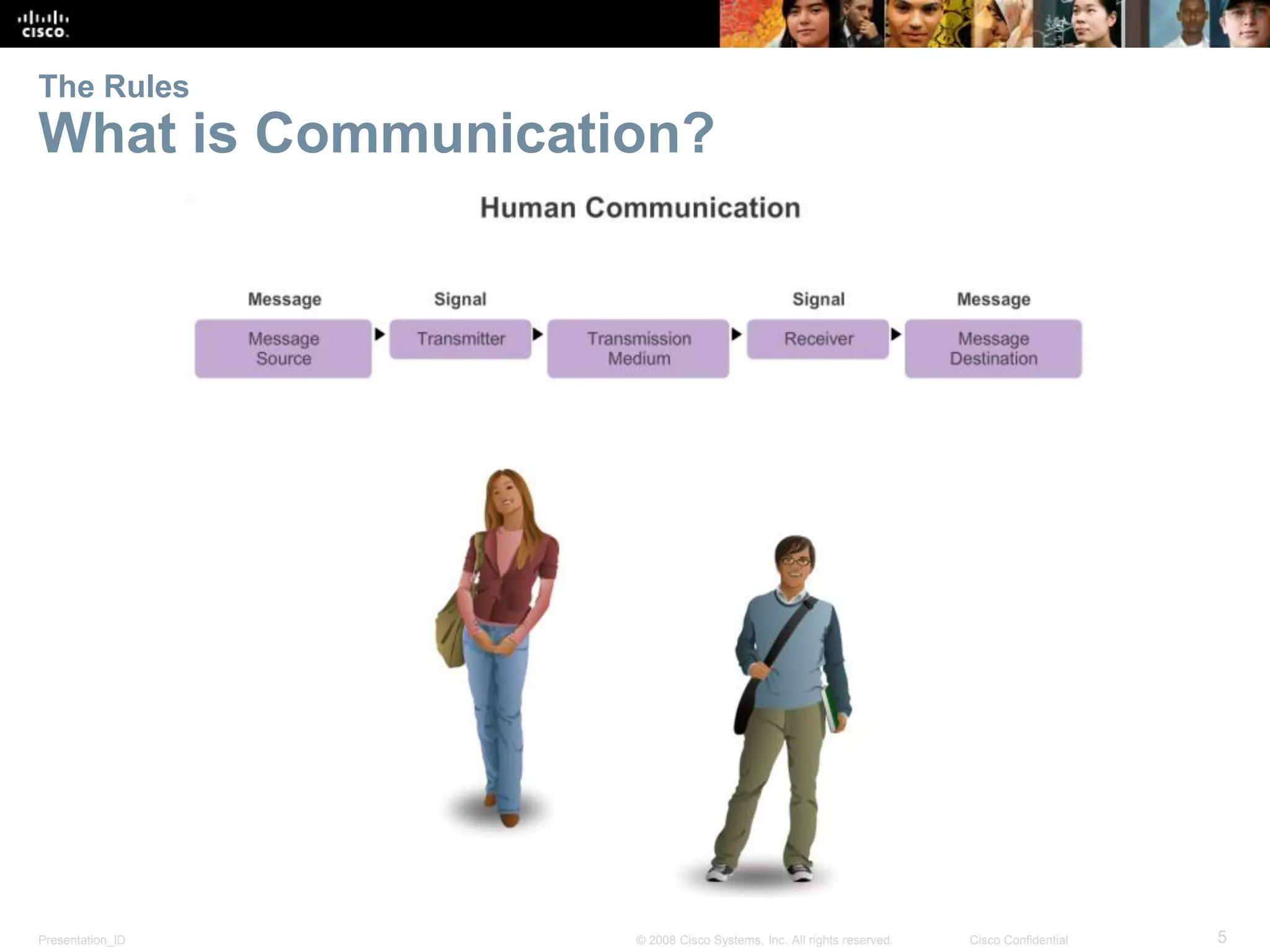
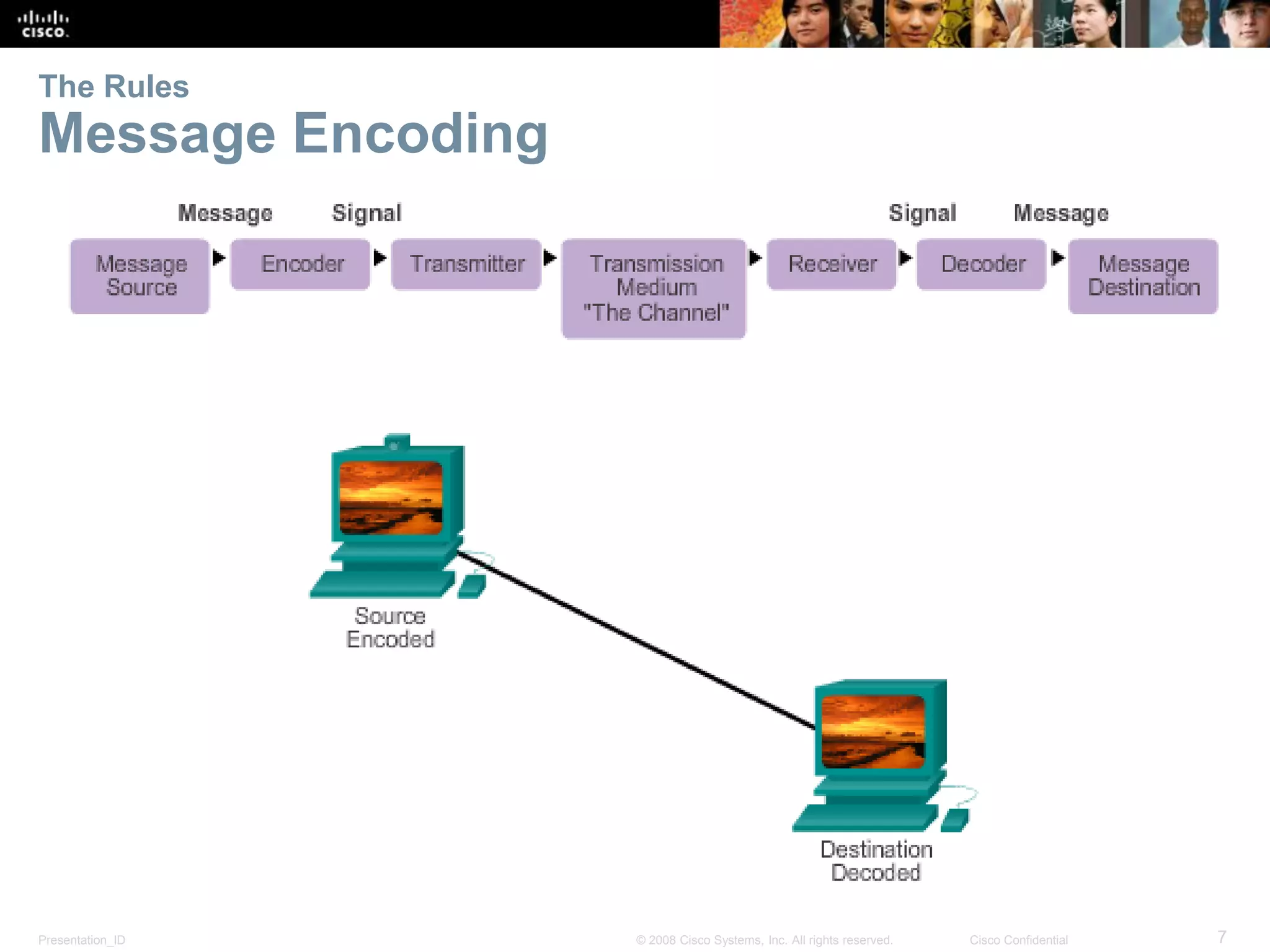
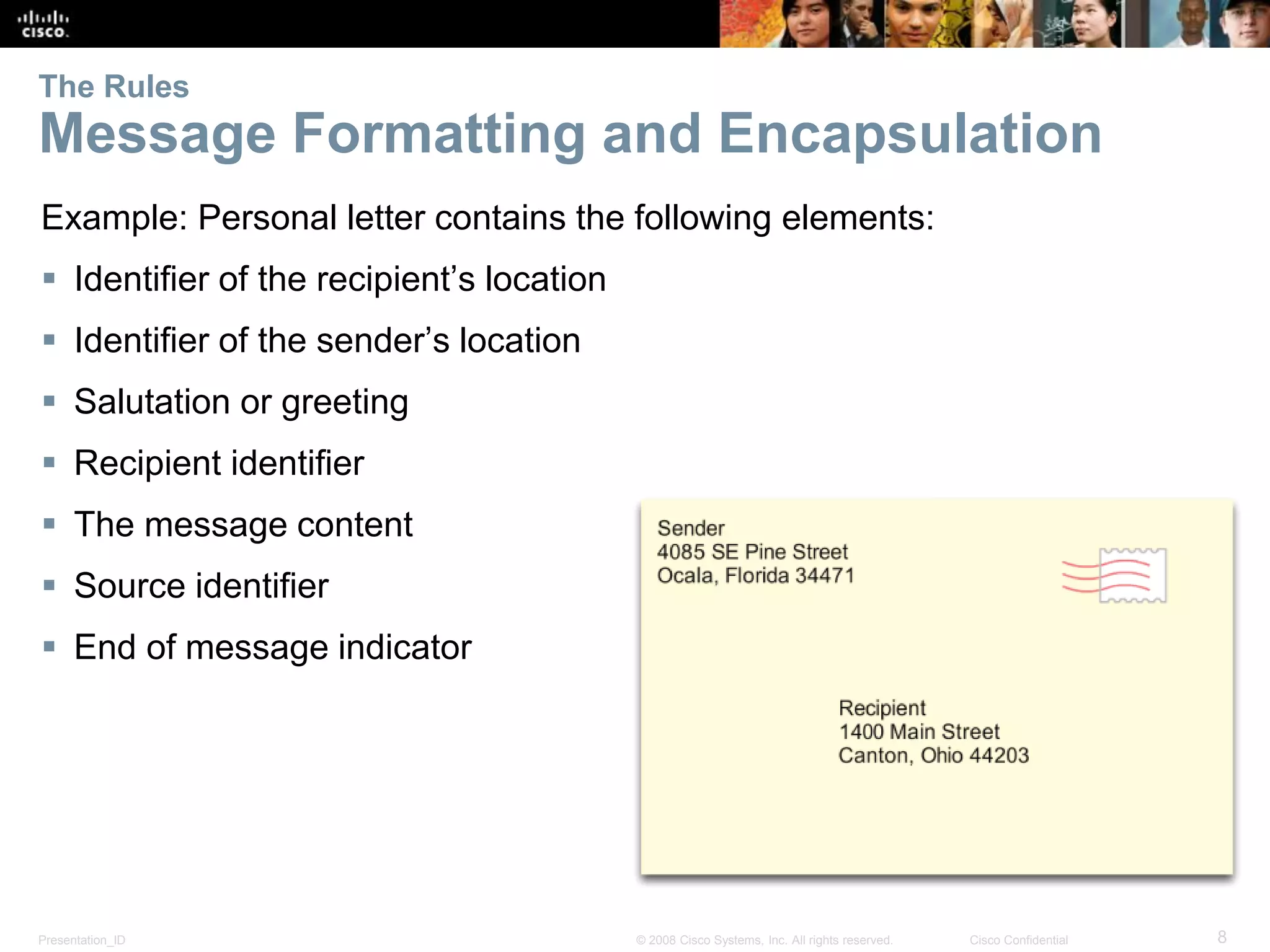
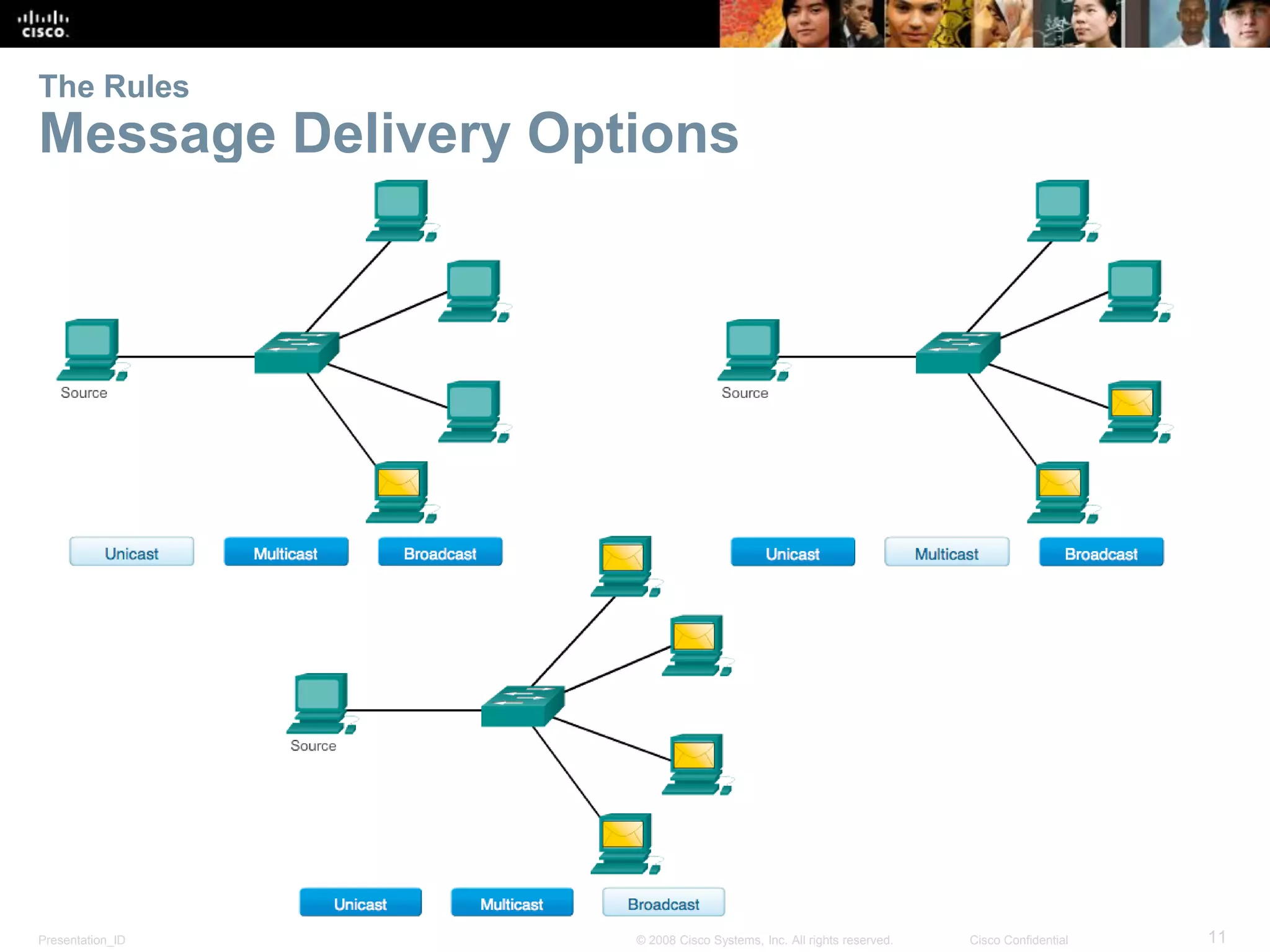
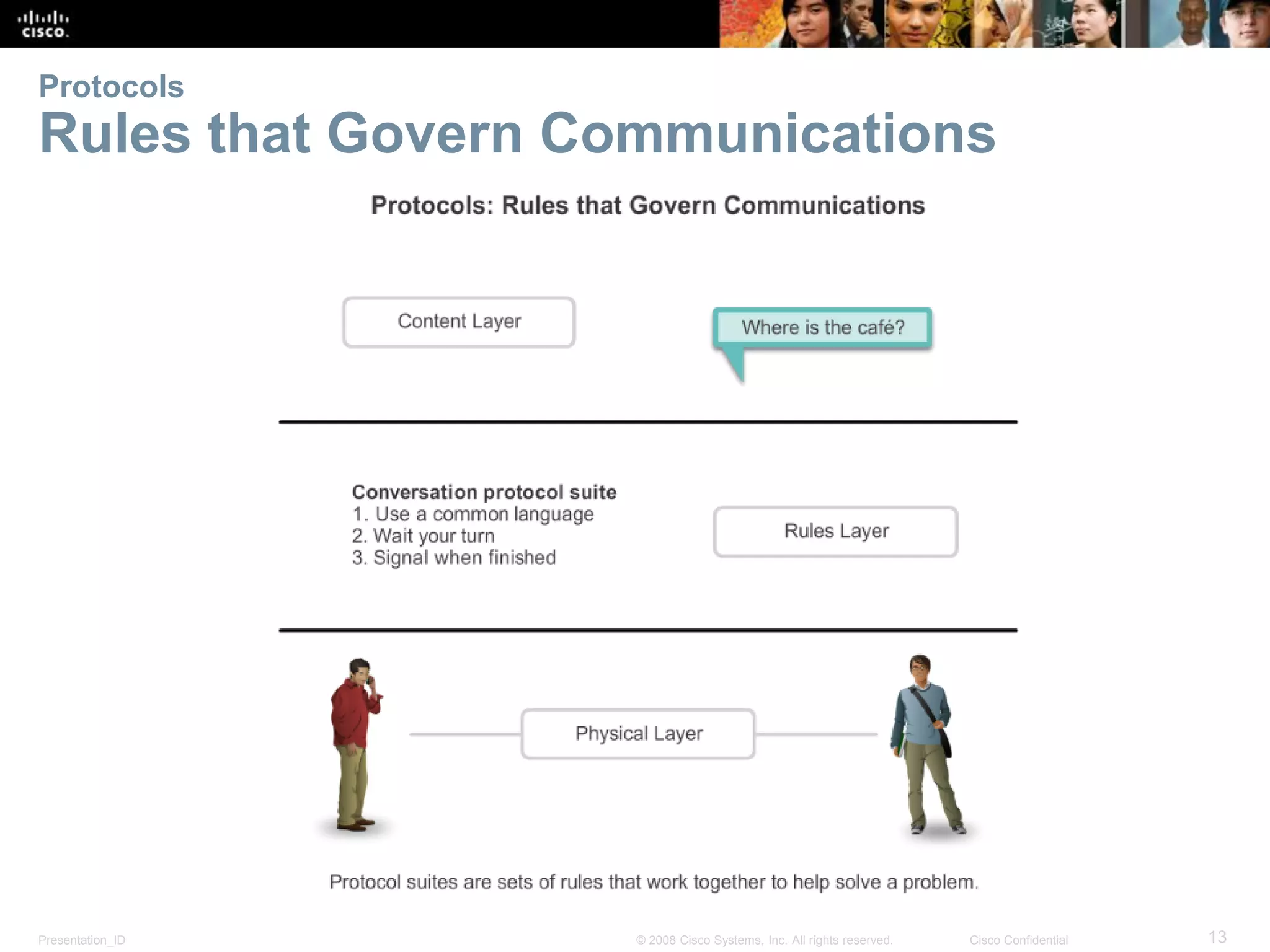
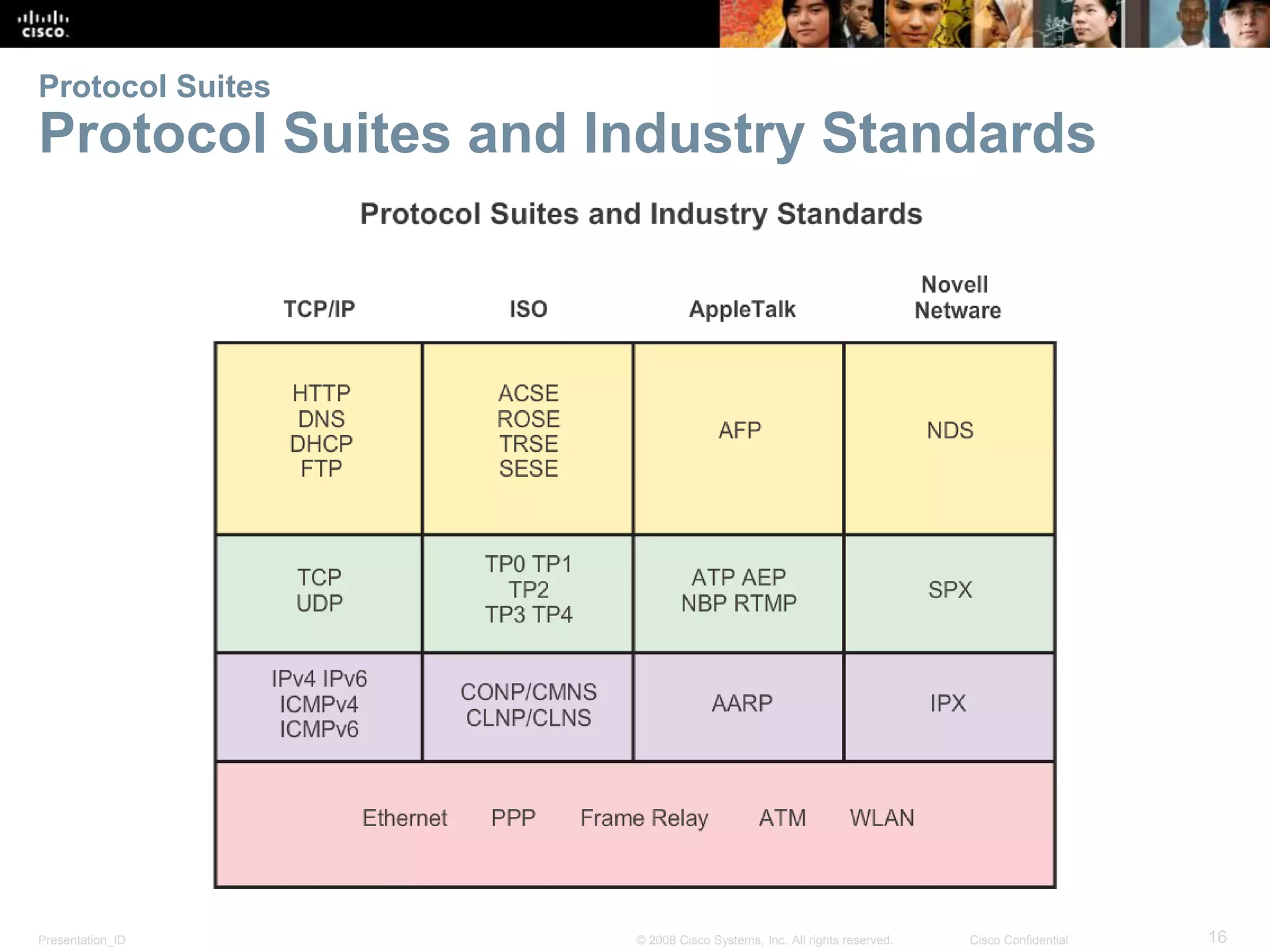
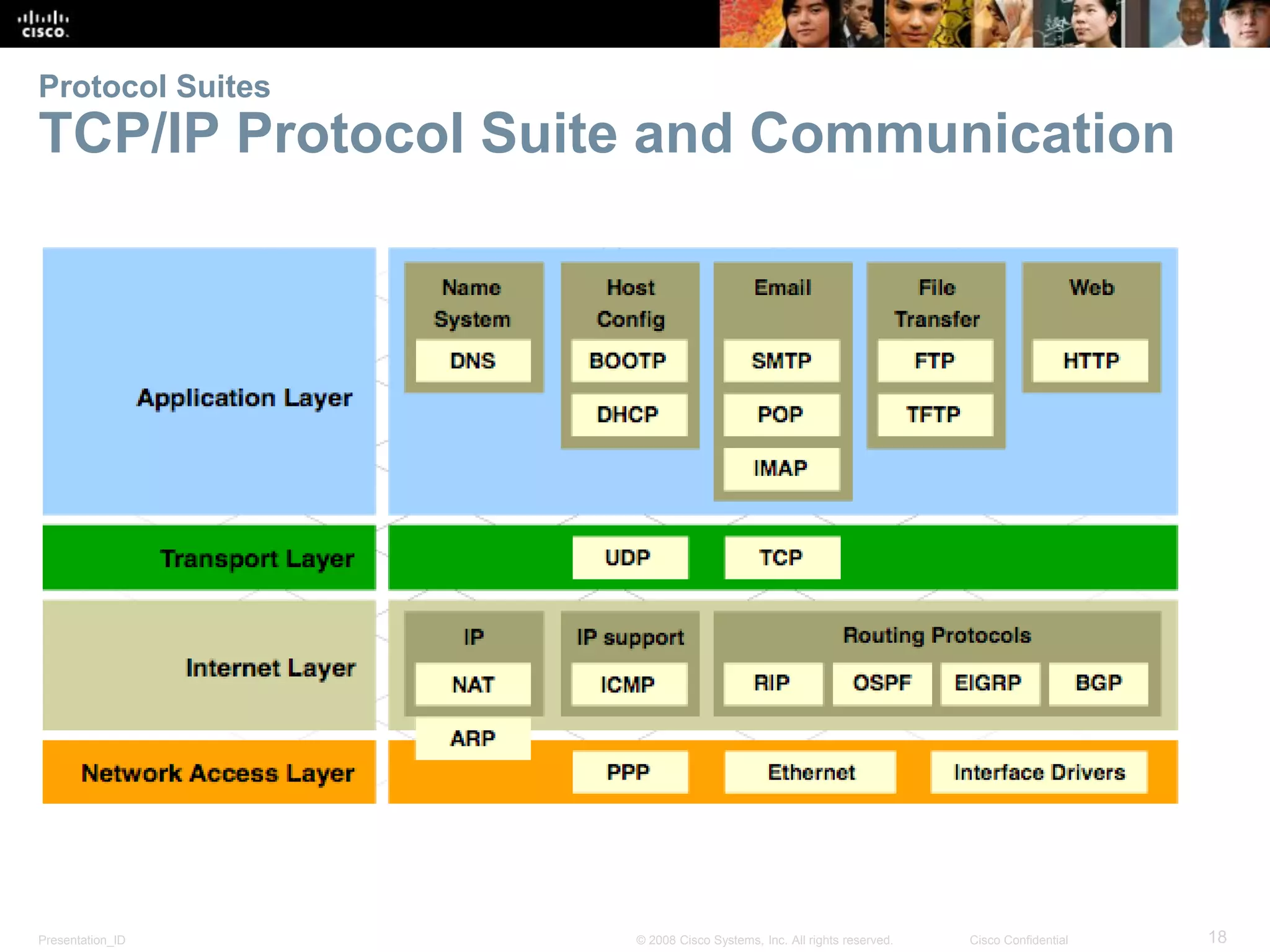
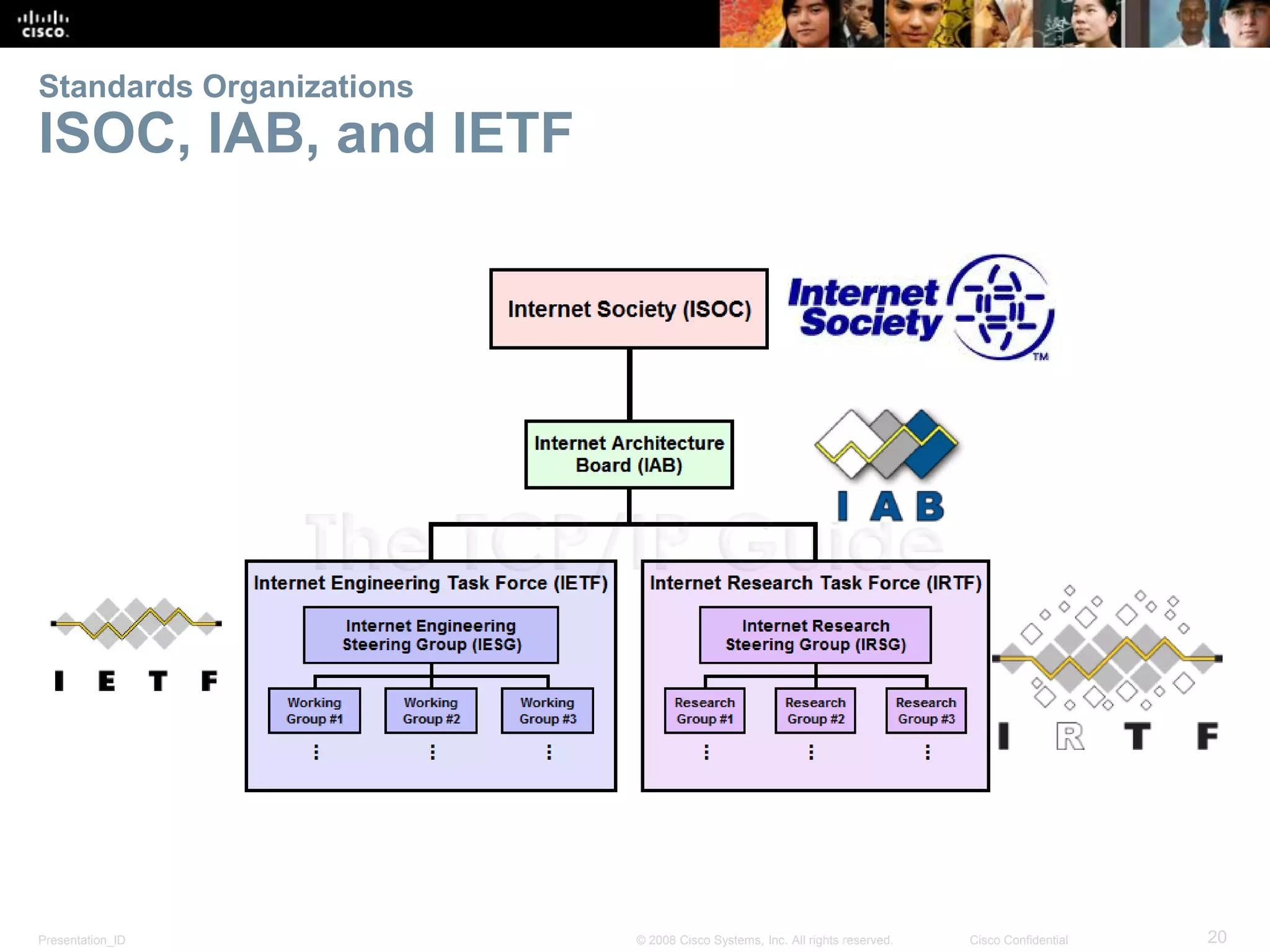
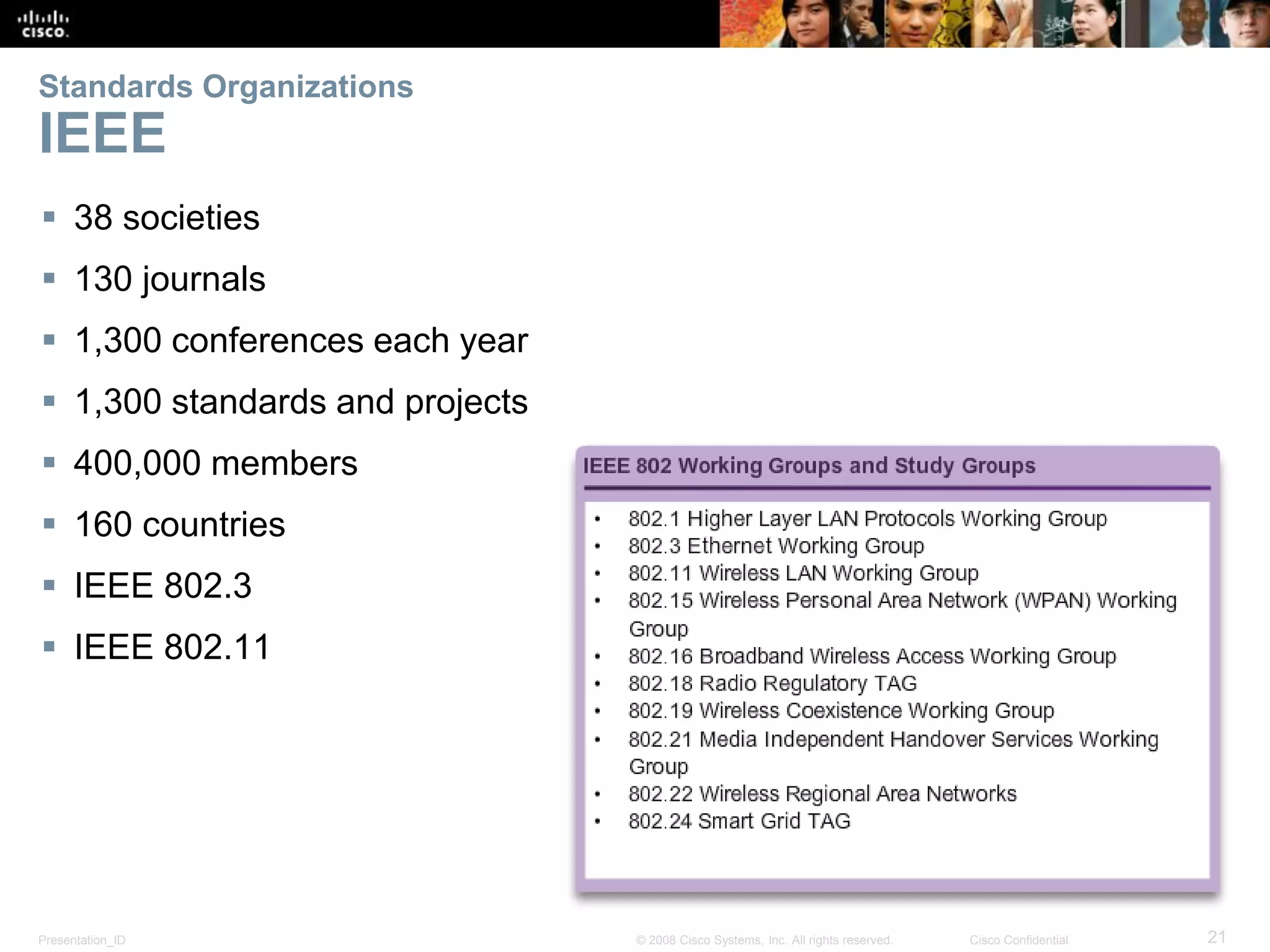
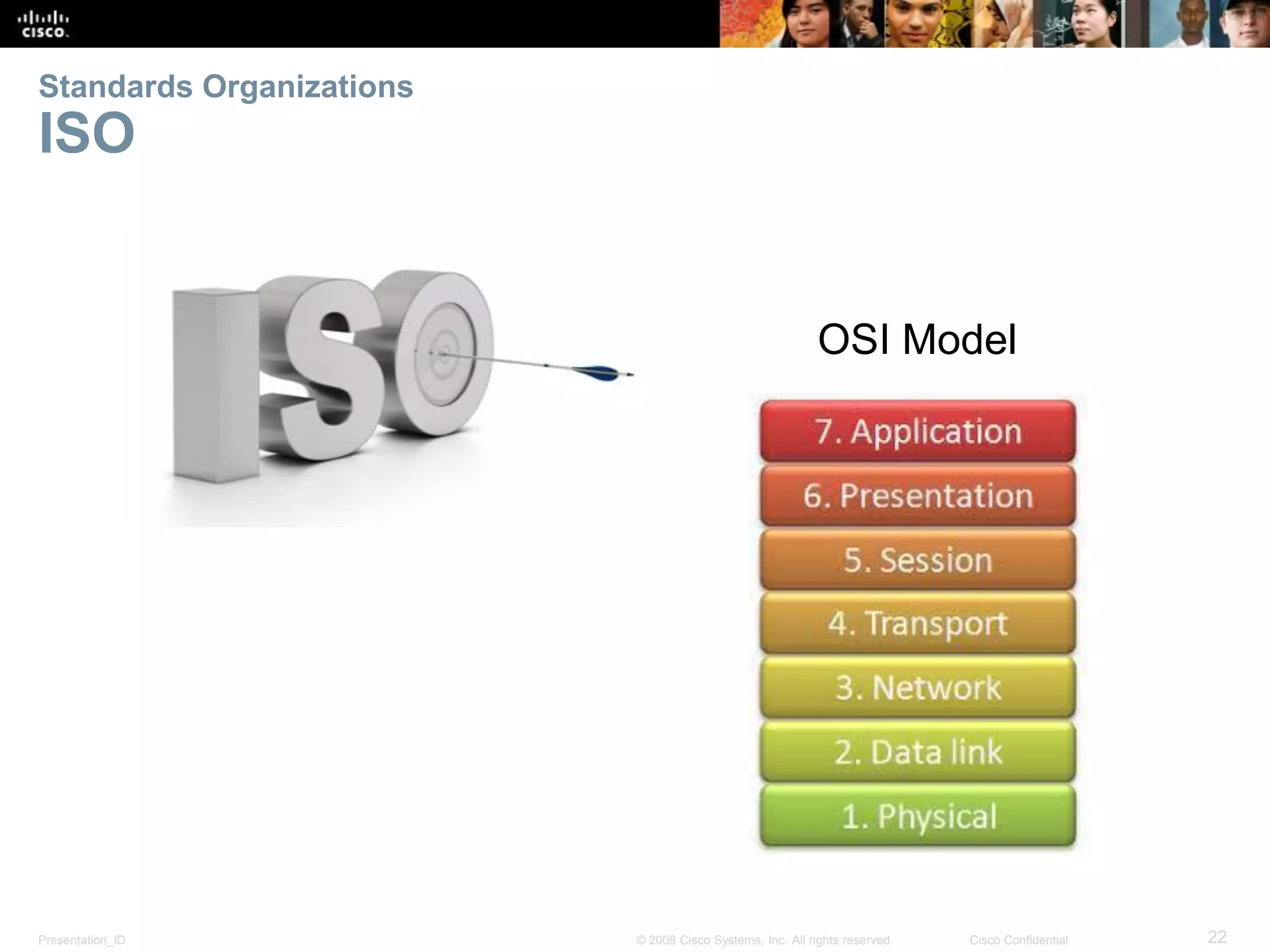
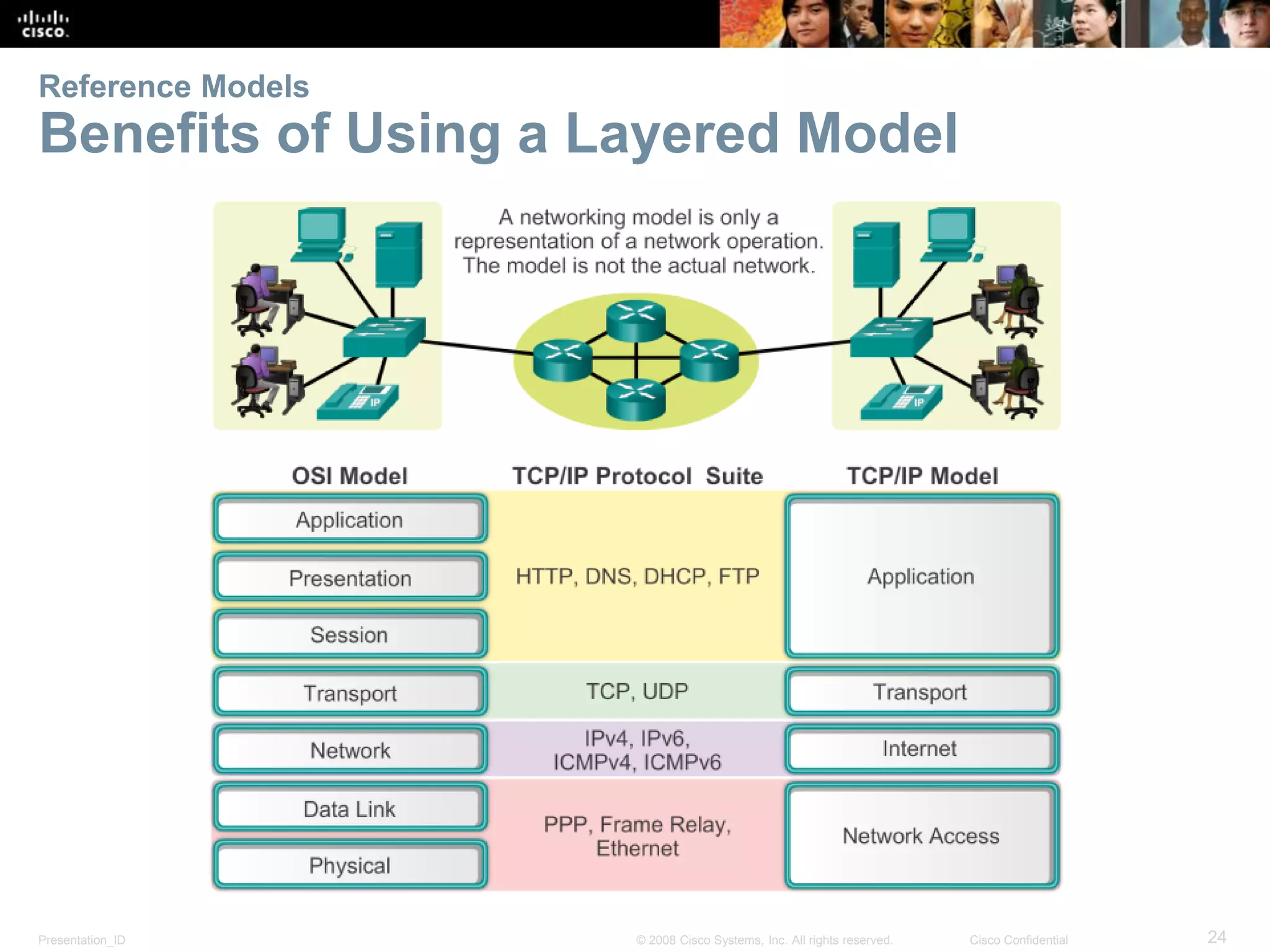
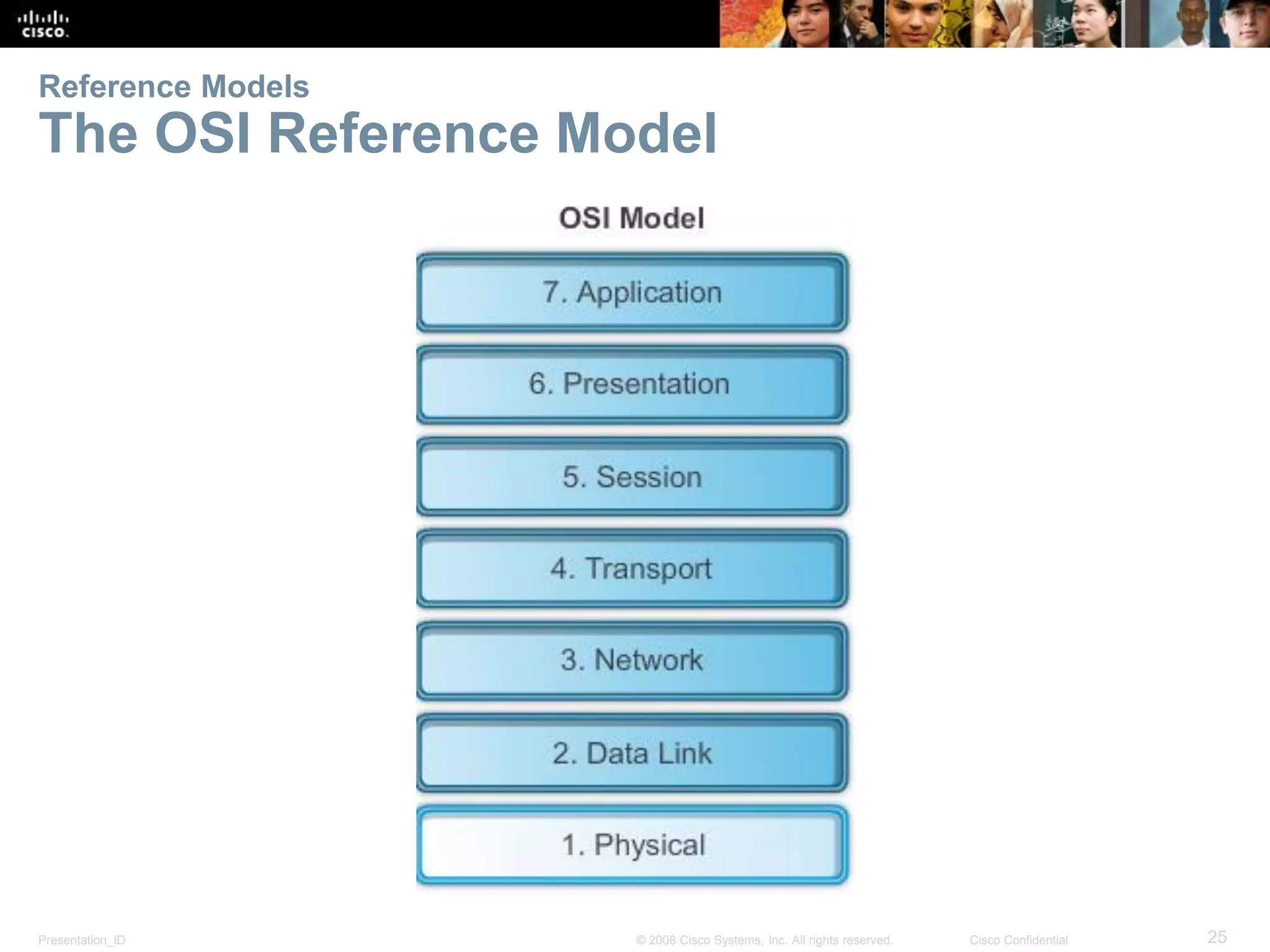
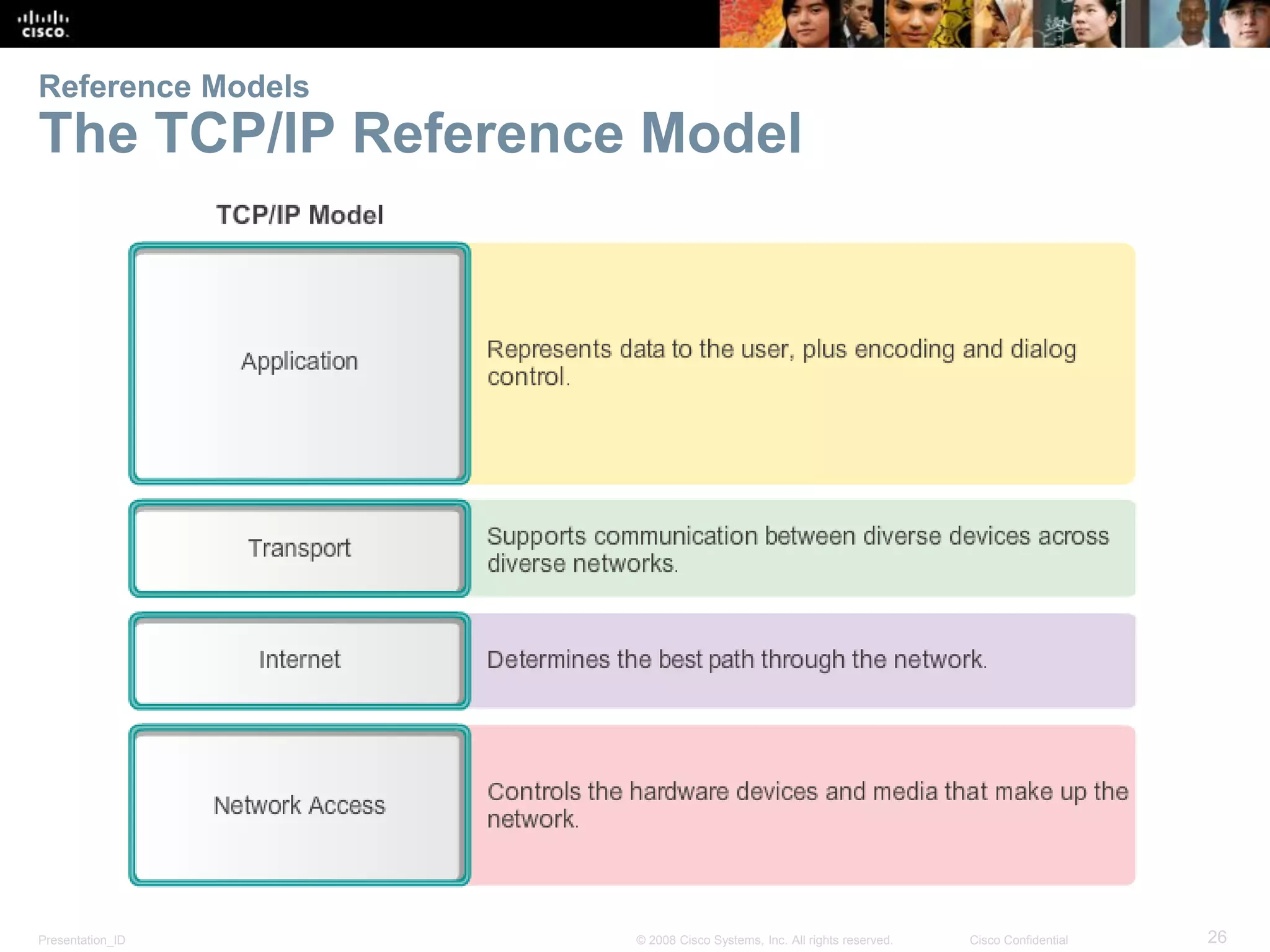
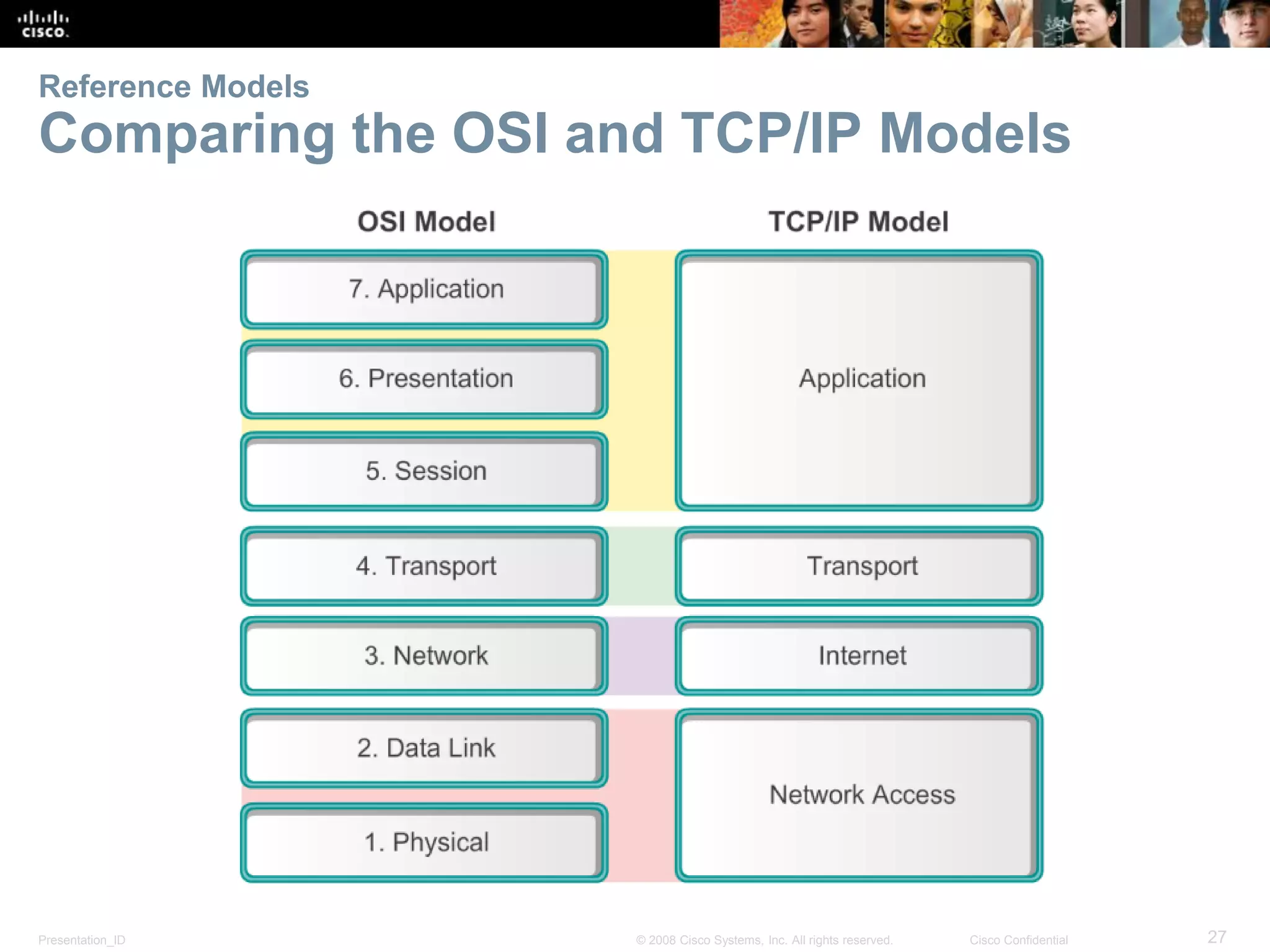
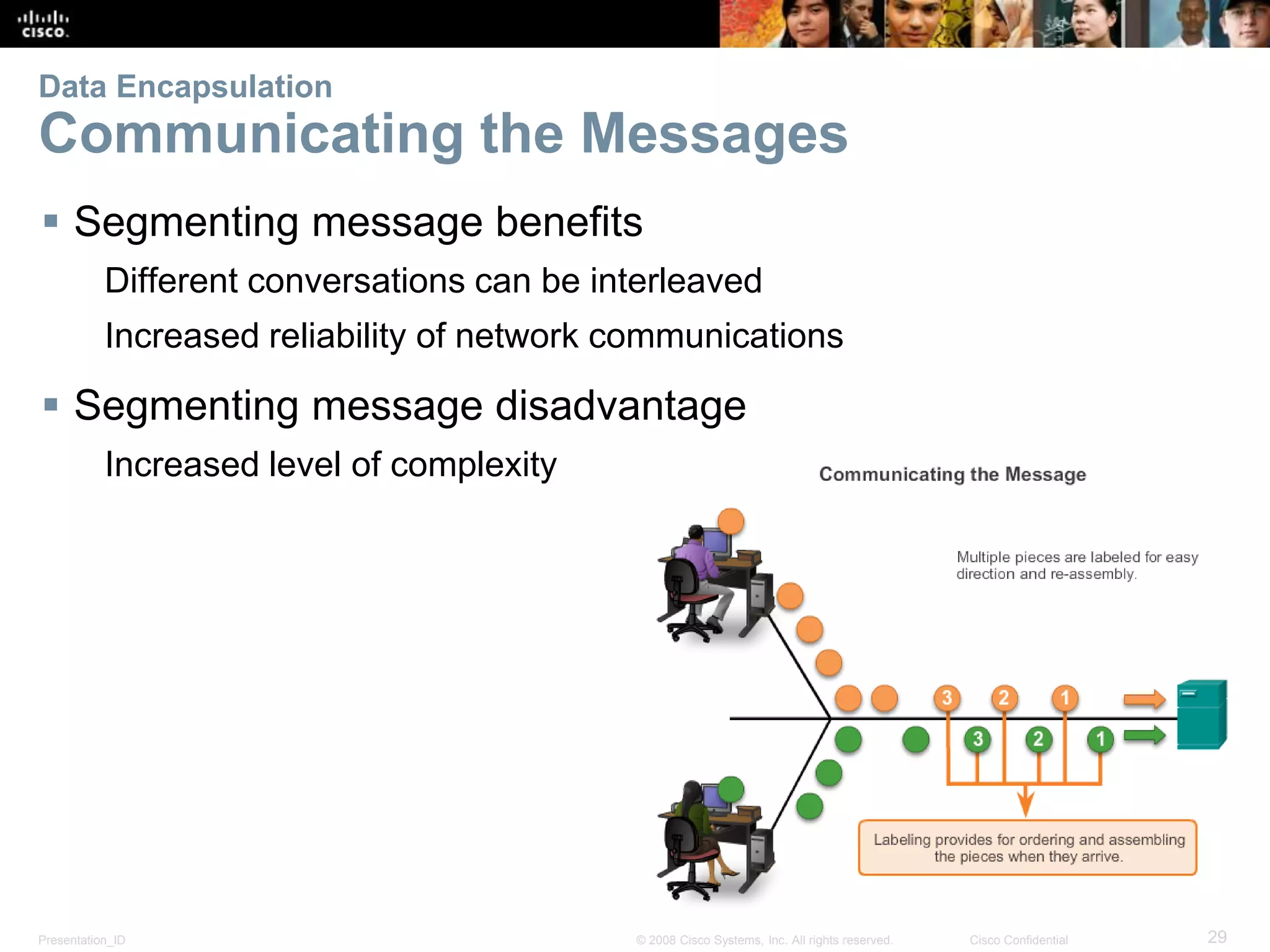
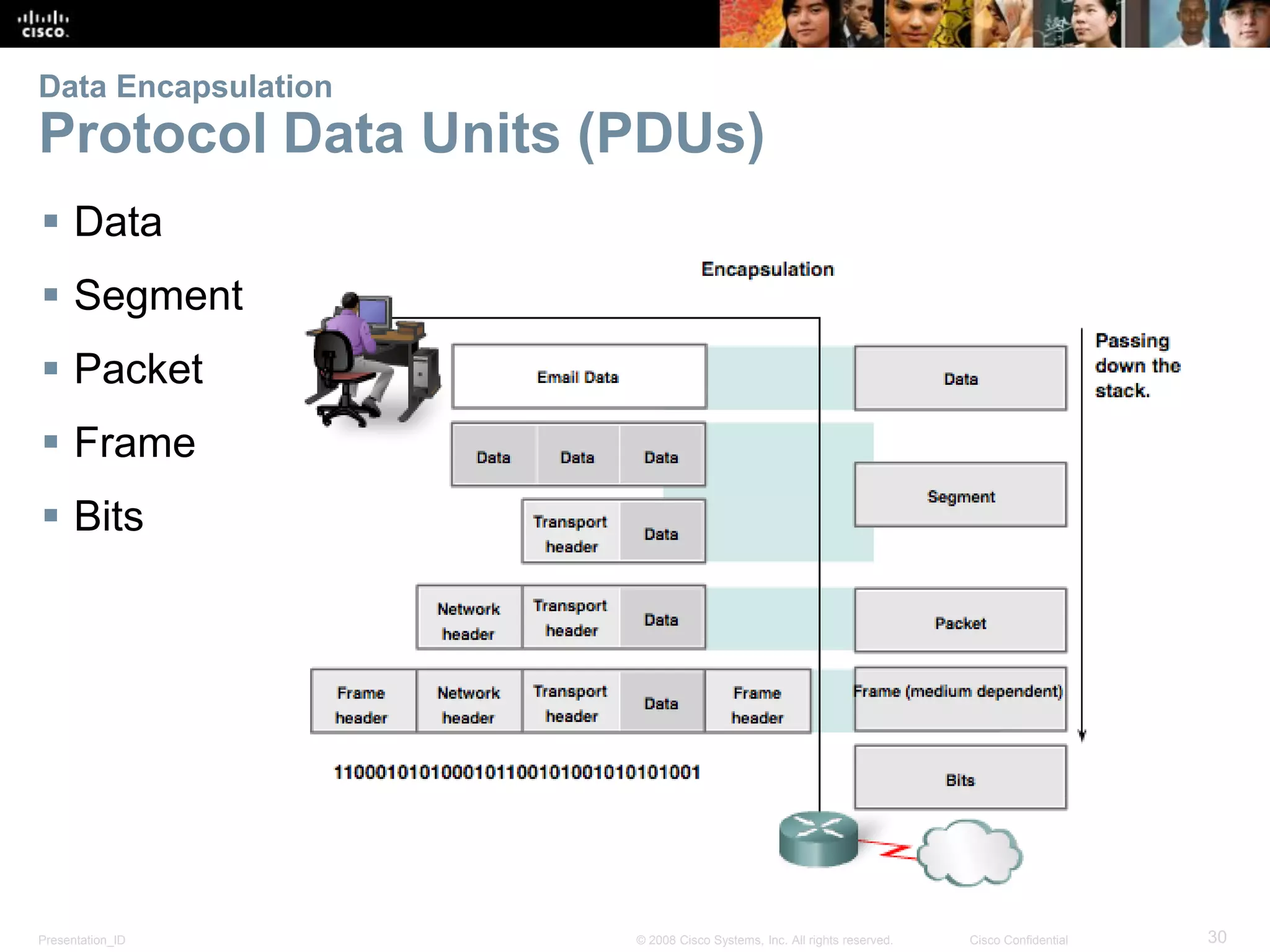
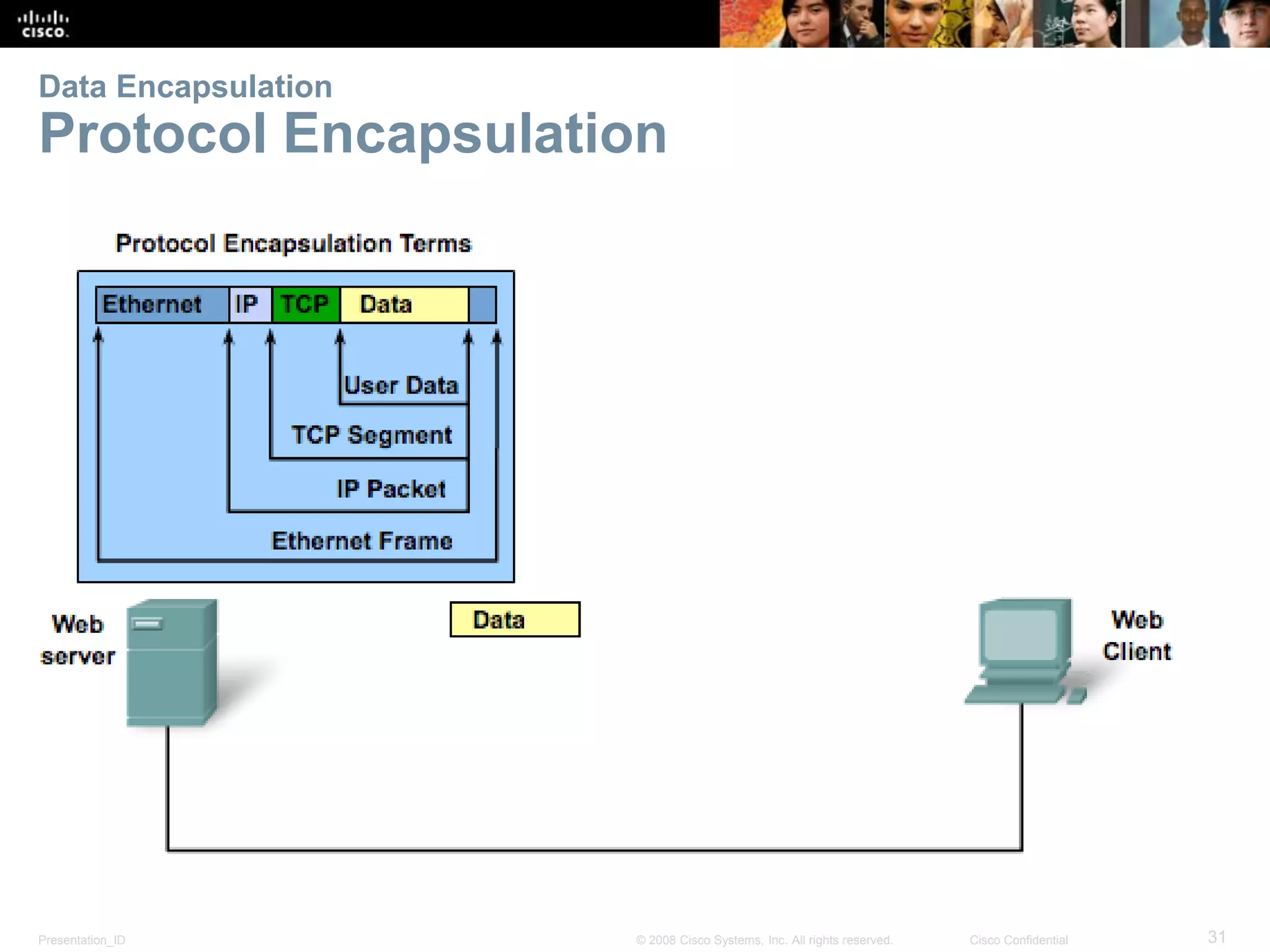
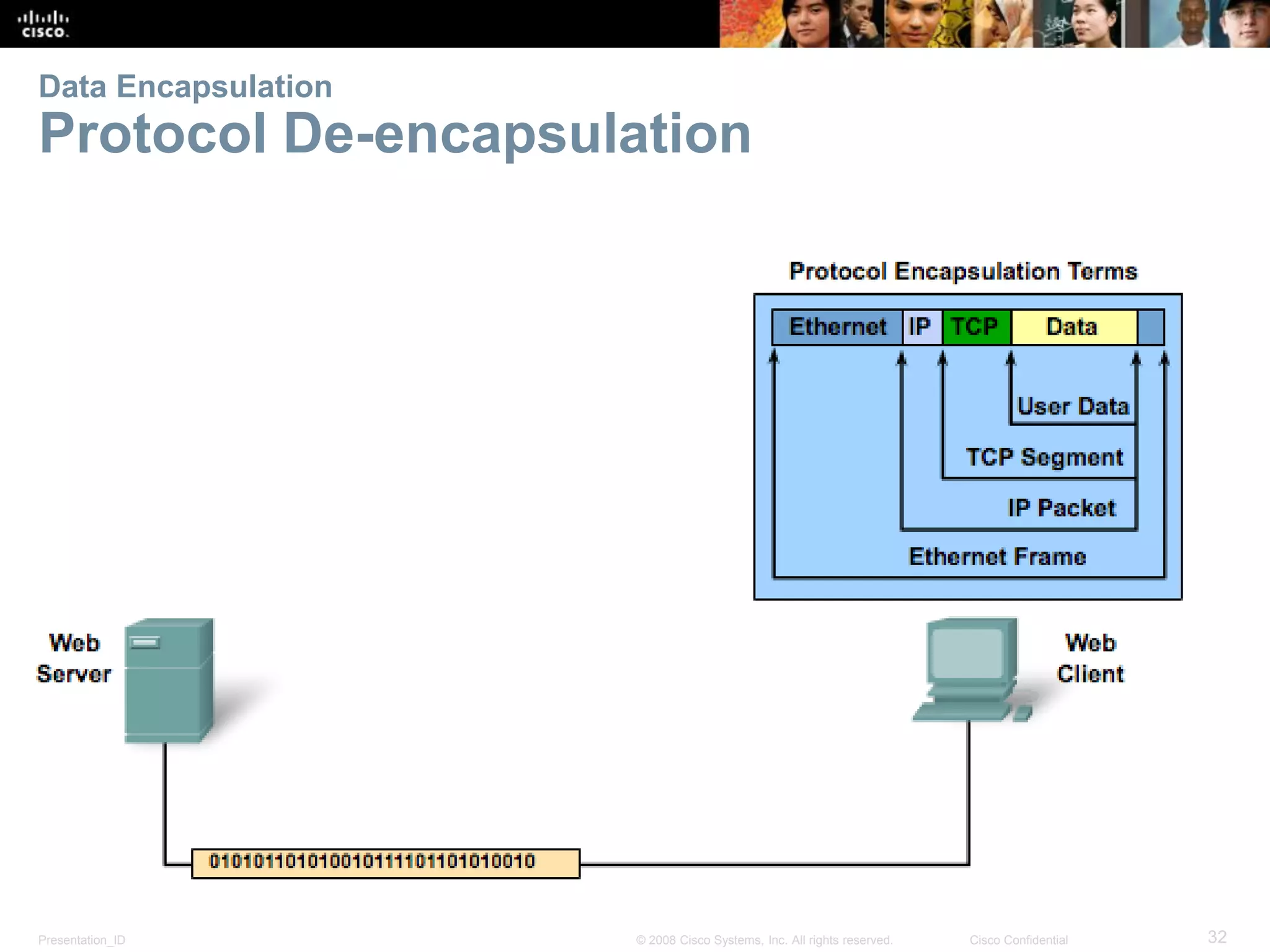
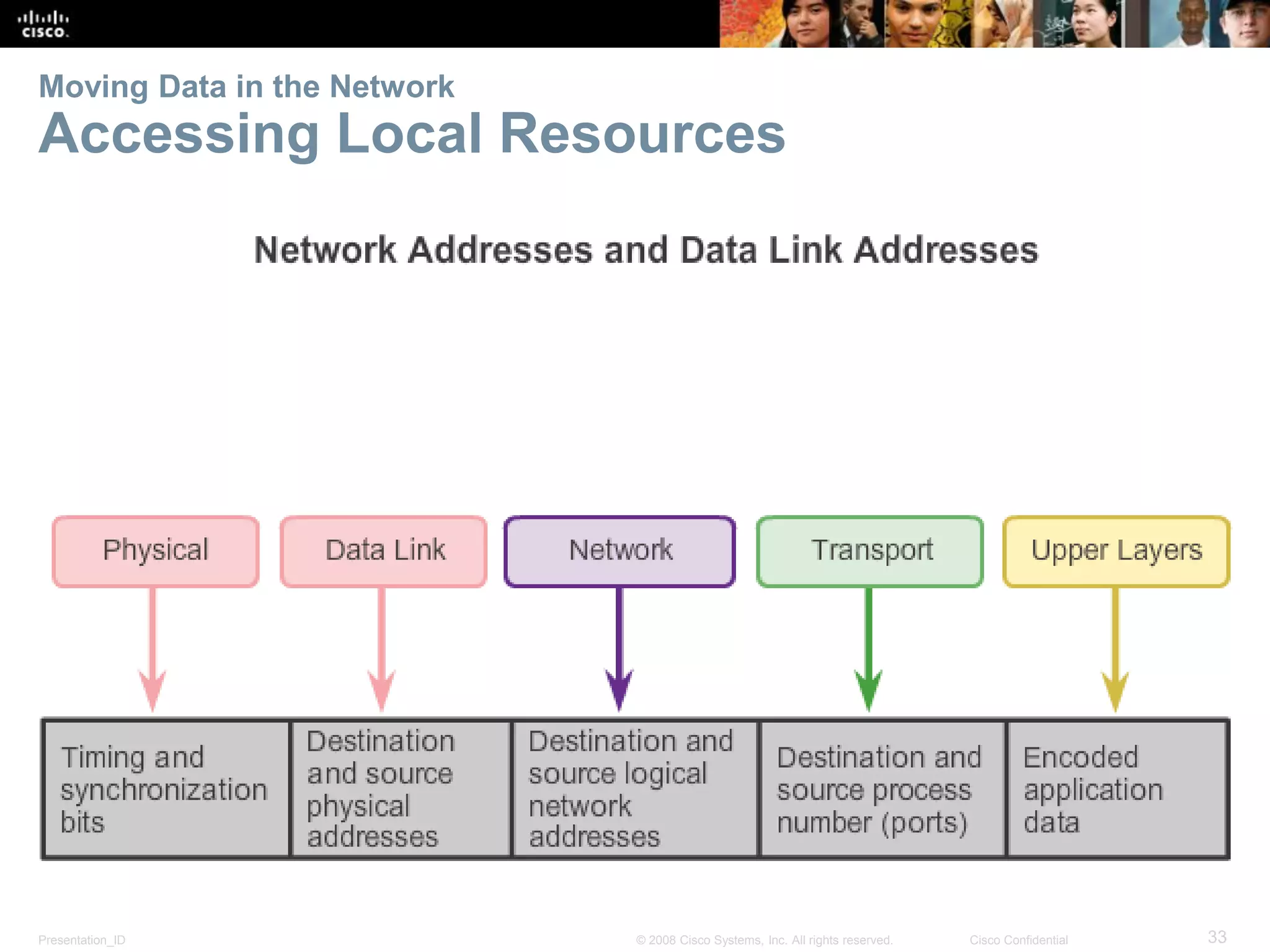
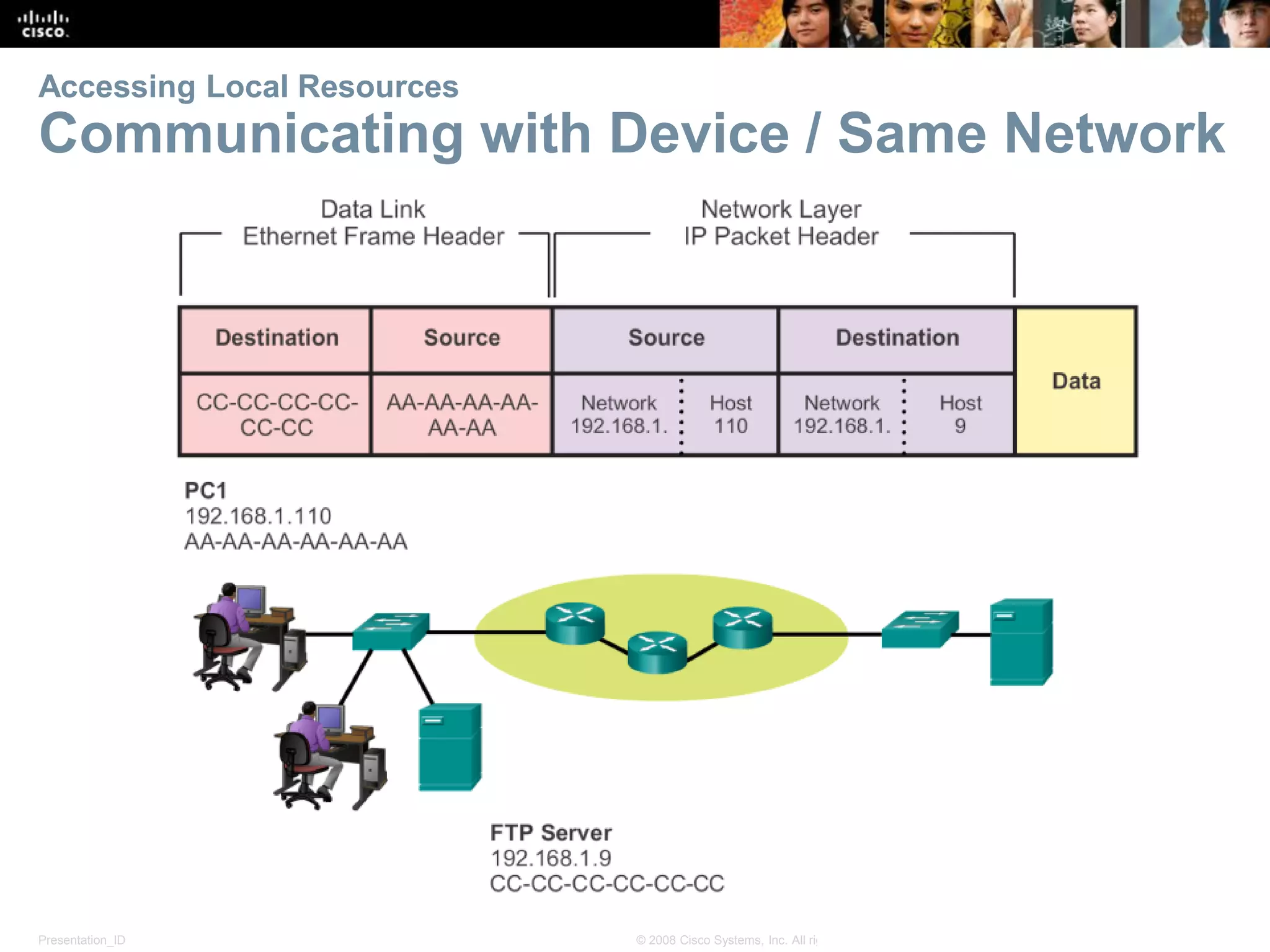
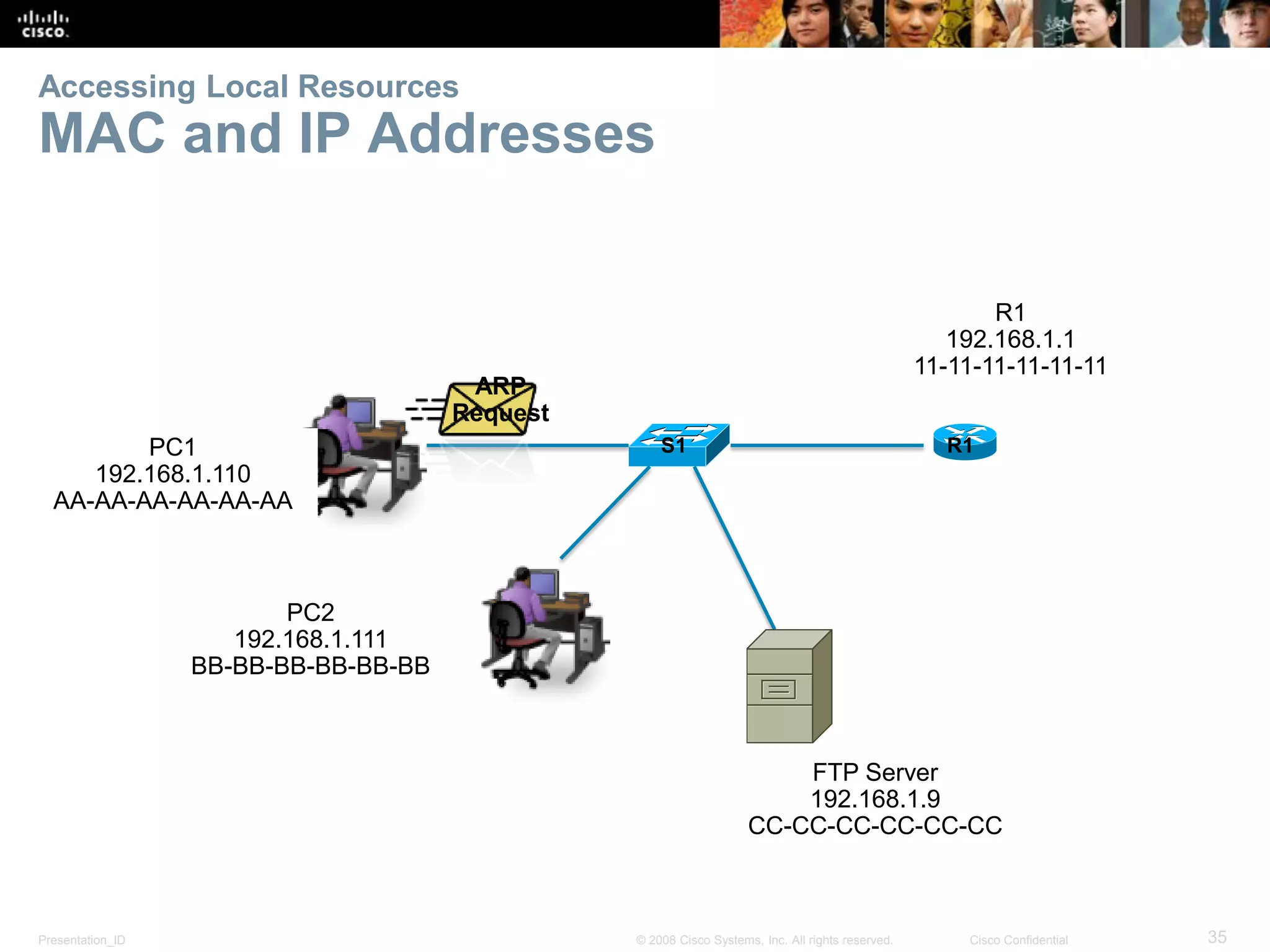
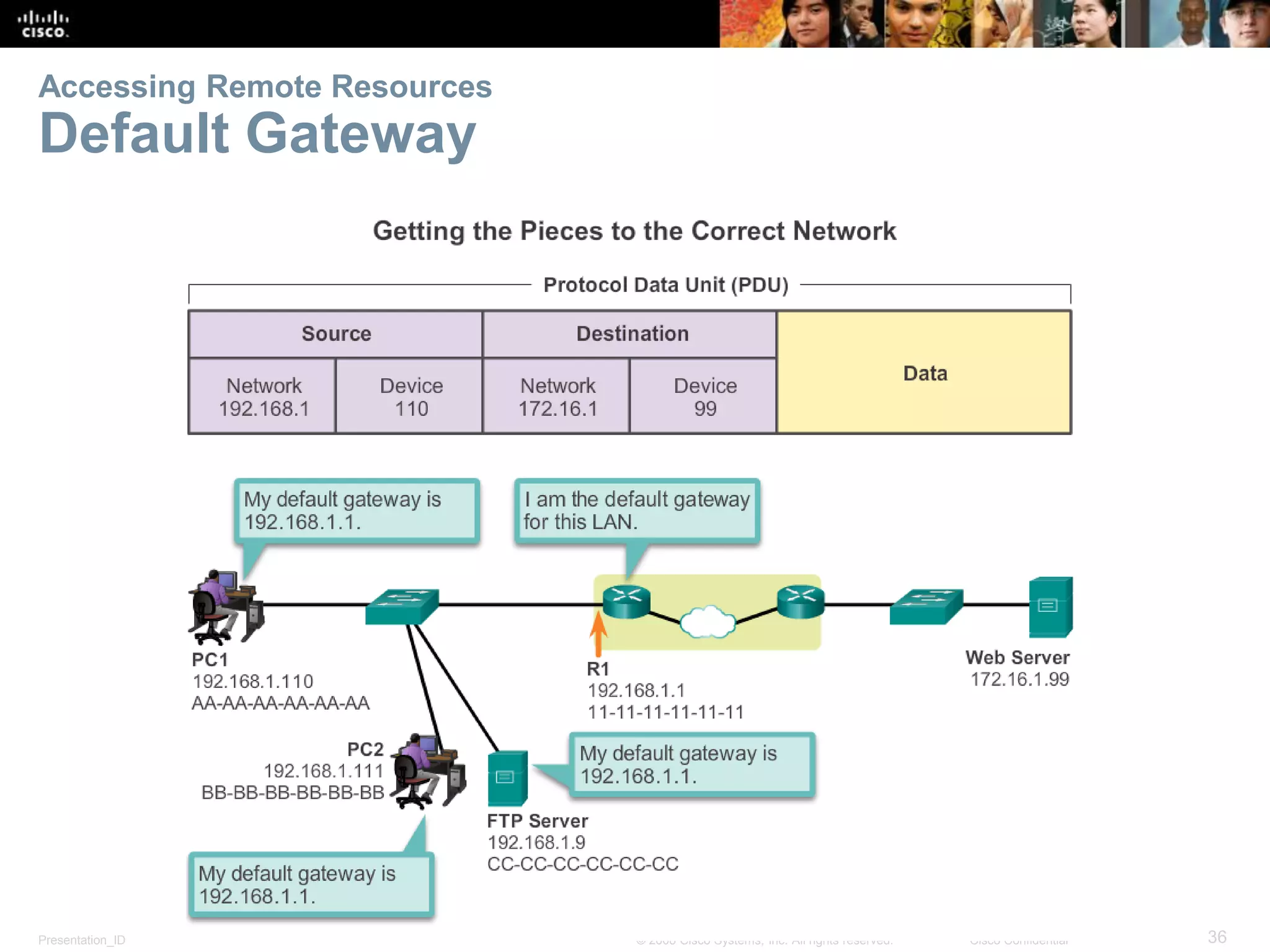
Chapter 3 covers network protocols and communications, explaining the rules necessary for facilitating communication, the role of protocols and standards organizations, and methods for accessing resources in small to medium-sized business networks. It discusses the TCP/IP protocol suite and industry standards as well as the OSI model, emphasizing the importance of encapsulation and segmentation in data transmission. Additionally, the chapter highlights the contribution of various organizations in the development and maintenance of networking standards.