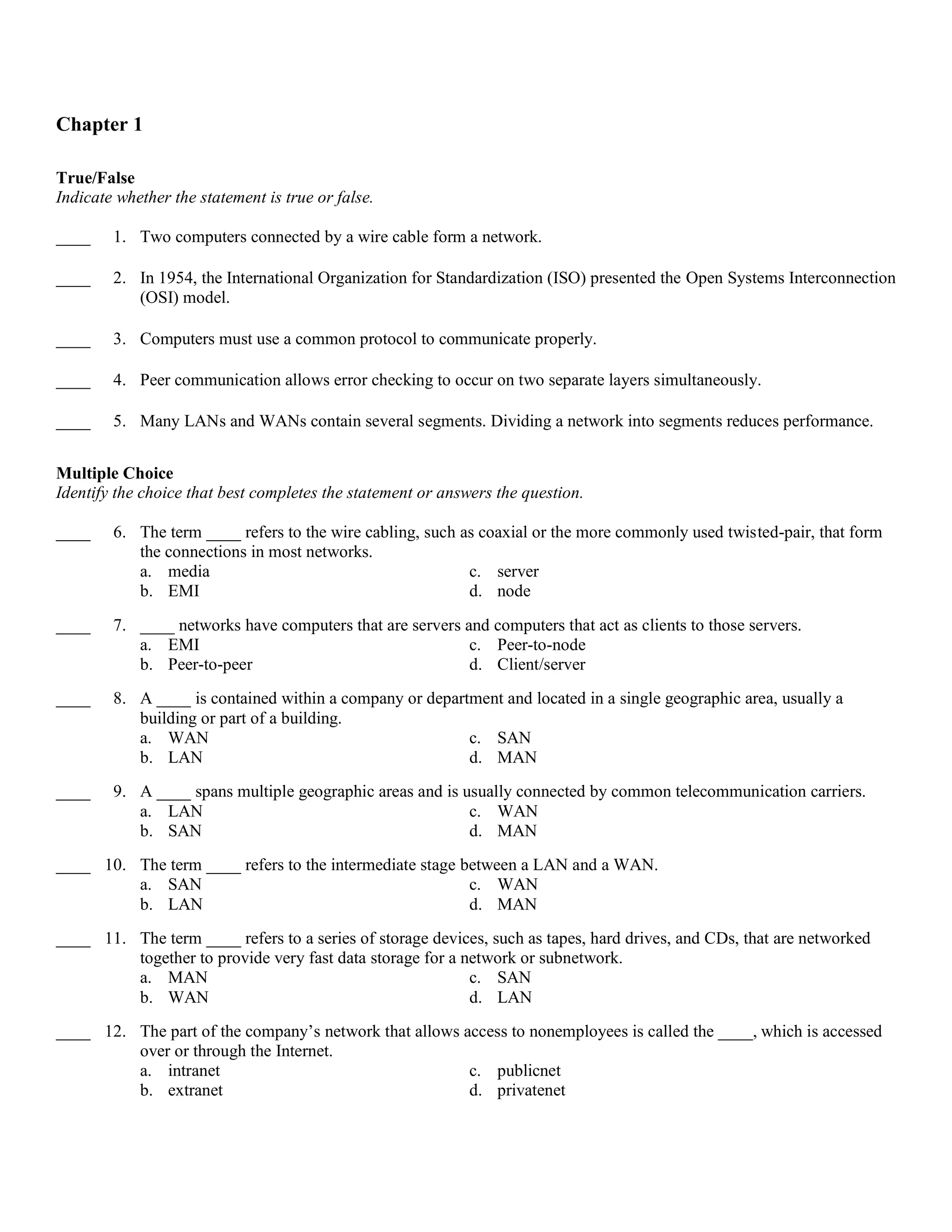
This document contains a chapter of review questions on networking fundamentals including true/false, multiple choice, completion, matching, and short answer questions. The questions cover topics like the layers of the OSI model, network components, network types (LAN, WAN, MAN, SAN), the TCP/IP model, and networking devices.