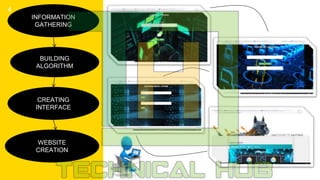
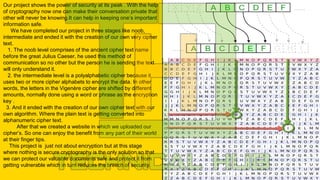
The project titled 'Caesar Cipher' explores various cipher codes, guiding users from basic to advanced encryption techniques. It emphasizes the importance of cryptography for secure communications and data protection, illustrating three stages: ancient ciphers, polyalphabetic ciphers, and creation of a custom cipher algorithm. The culmination of the project includes a website to access these ciphers and promote the benefits of cryptography in enhancing security.