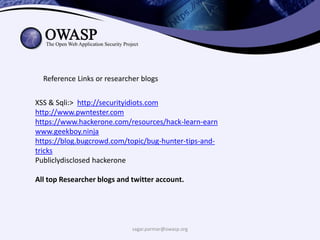
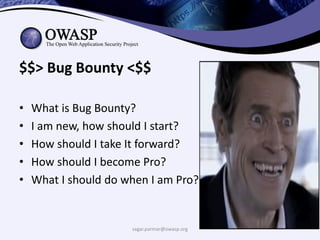
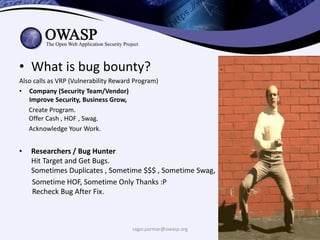
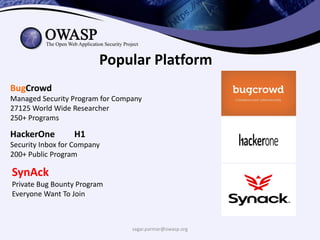
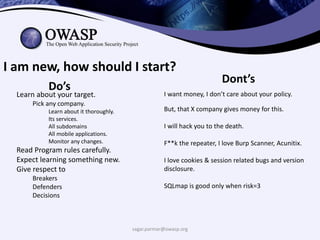
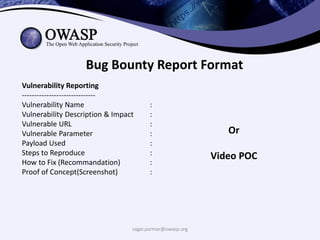
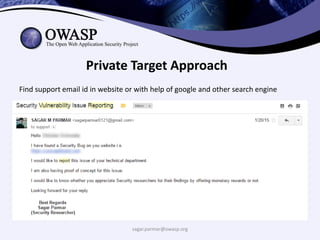
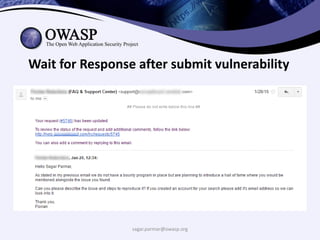
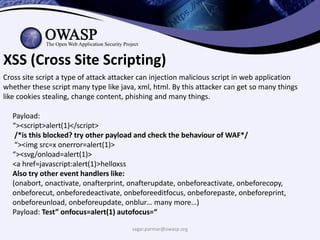
This document provides information for a bug bounty presentation. It introduces the speaker, Sagar Parmar, and his background in security. It then outlines topics to cover, including what a bug bounty is, how to get started as a new bug bounty hunter, tips for progressing, and example vulnerabilities to target like XSS, SQLi, SSRF, LFI, and RCE. Details are given on finding and reporting vulnerabilities with the goal of helping others learn and advance in bug bounty hunting.

![sagar.parmar@owasp.org
SSRF (Server Side Request Forgery)
• Server Side Request Forgery (SSRF) is a vulnerability that appears when an attacker
has the ability to create requests from the vulnerable server.
• Usually, Server Side Request Forgery (SSRF) attacks target internal systems behind the
firewall that are normally inaccessible from the outside world (but using SSRF it’s
possible to access these systems).
• With SSRF it’s also possible to access services from the same server that is
listening on the loopback interface.
How to Look for SSRF?
1.Check For Different Requests where some parameters contains some URL To External/
Internal hostname/IP.
2.We could try putting our own IP/hostname in that parameter and Simply Check your Server
Logs.
3.If there is a Request in logs from their IP then You need to Look for internal services.
4.You can do various stuffs like Port scanning, Fingerprinting Services and also use their Server
As a proxy to attack others.
5.You Can Enter http://localhost:port to check for services or if its blocked then you could use
127.0.0.1 or also you could use IPv6 localhost : http://[::]:port](https://image.slidesharecdn.com/bugbountynullowasp2k17-170430191413/85/Bug-bounty-null_owasp_2k17-26-320.jpg)