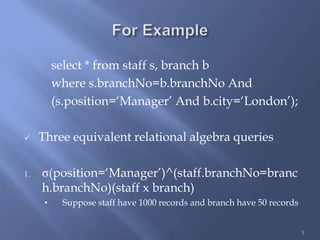
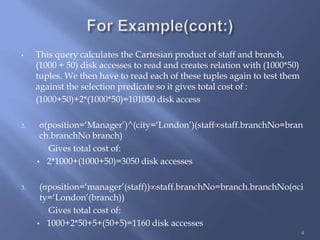
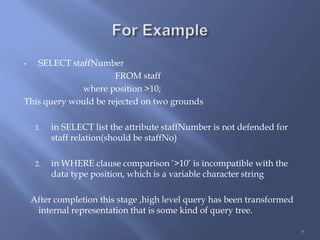
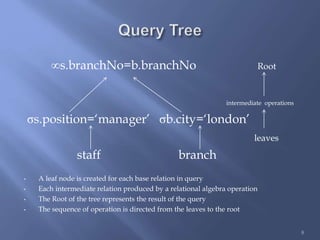
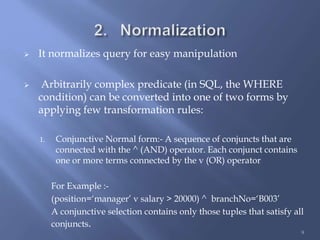
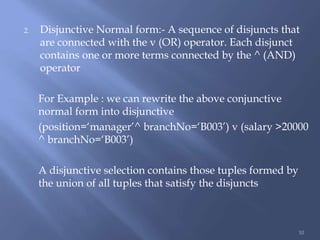
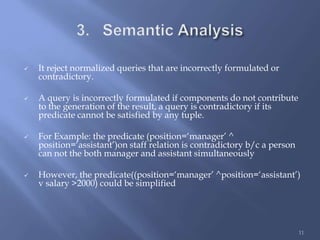
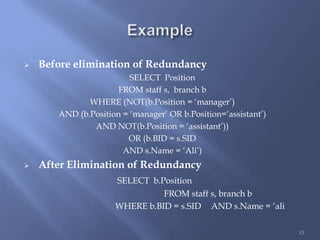
The document discusses the process of query decomposition in databases, which transforms high-level queries into relational algebra queries while ensuring they are syntactically and semantically correct. It explores different methods of query execution, including the costs associated with various query formulations, and highlights the importance of query normalization, simplification, and restructuring for efficiency. The final goal is to optimize and retrieve data effectively, although the decomposition process can be time-consuming.