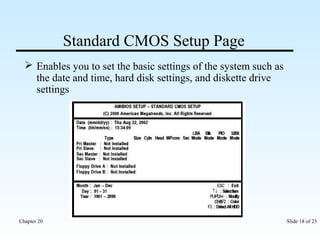
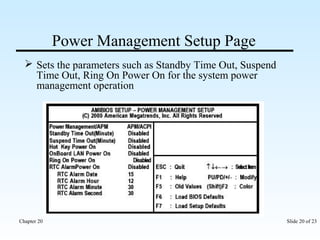
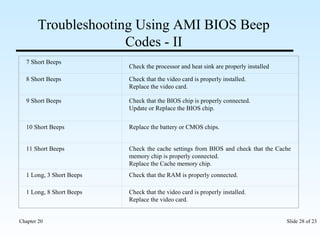
The document discusses the motherboard BIOS and CMOS. It describes how the BIOS is used to control and troubleshoot hardware before an operating system loads. It contains information on BIOS chips, updating the BIOS, using the BIOS setup utility to modify settings stored in CMOS, and troubleshooting hardware issues using BIOS beep codes.