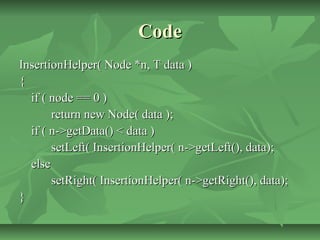
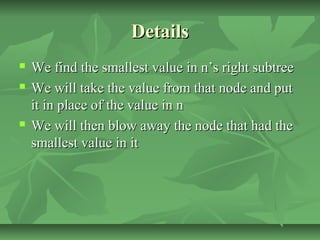
The document discusses binary trees and their properties. It defines binary trees and provides terminology used to describe them, such as nodes, levels, paths, and heights. It describes different types of binary trees like complete, full, and binary search trees. It discusses common traversal methods for binary trees like breadth-first and depth-first. It also covers insertion and deletion of nodes in binary trees, describing approaches like merging subtrees and copying values.