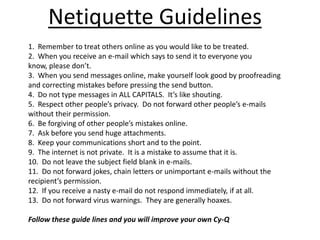
This document provides tips for staying safe online and improving your "Cy-Q" or cyber intelligence quotient. It outlines top safety tips for kids such as not sharing personal information or meeting up with strangers. It also discusses maintaining strong passwords, being careful what emails are opened, and setting social media pages to private. The document advises only giving out emails to people you know and keeping passwords private. Netiquette guidelines include treating others online as you want to be treated, proofreading messages, and respecting people's privacy.