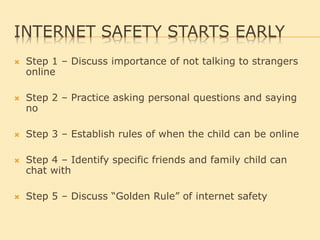
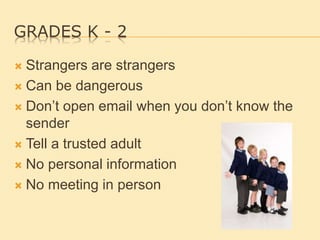
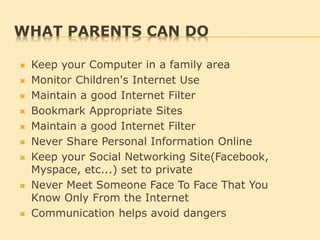
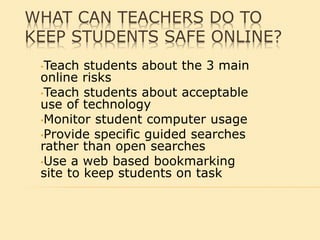
This document provides information and guidance around internet safety for children and teenagers. It outlines specific steps and rules that parents should establish with young children to stay safe online. It also details age-appropriate safety tips for elementary, middle school and high school aged children. The document emphasizes not sharing personal information online, using screen names instead of real names, and establishing open communication with parents so children know who to talk to if they experience anything uncomfortable online.