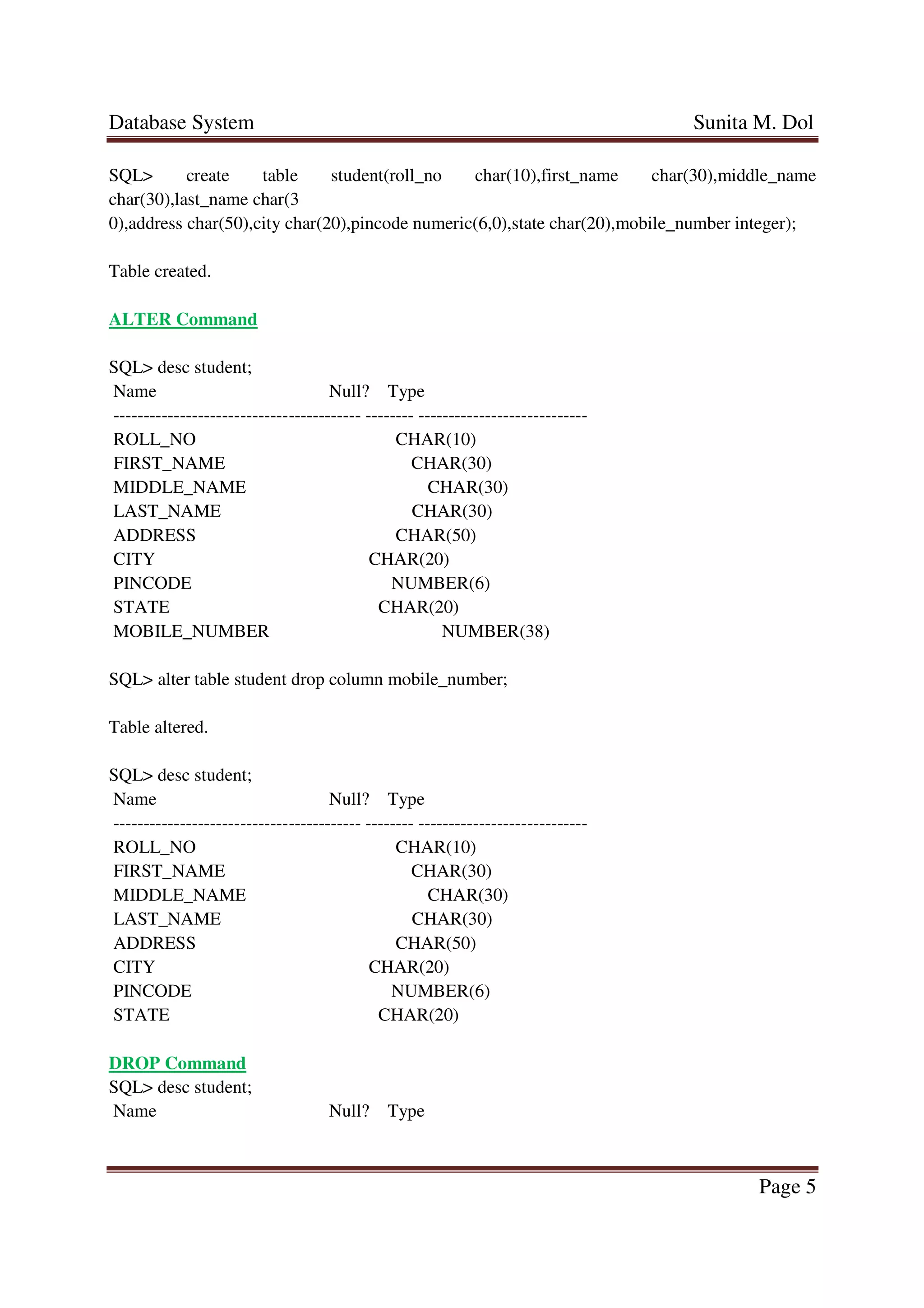
The document outlines the implementation of SQL Data Definition Language (DDL) commands including CREATE, ALTER, and DROP, as well as constraints for relational databases. It explains various aspects of SQL such as primary keys, foreign keys, integrity constraints, and data types. Examples of SQL commands for creating tables, modifying them, and dropping relations are provided to illustrate the concepts discussed.