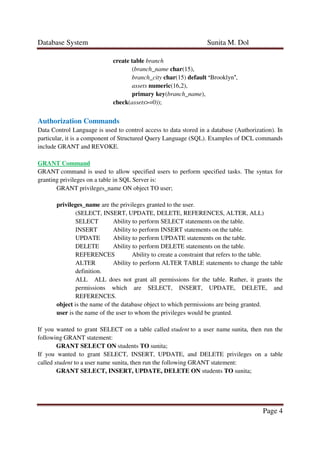
The document discusses various SQL integrity constraints and authorization commands. It describes primary key, foreign key, not null, check, unique, and default constraints that can be applied during table creation. It also covers the GRANT and REVOKE commands used to manage user permissions to tables. Examples are provided for each constraint and command to illustrate their proper syntax.