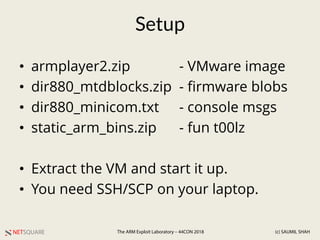
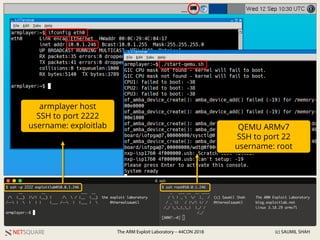
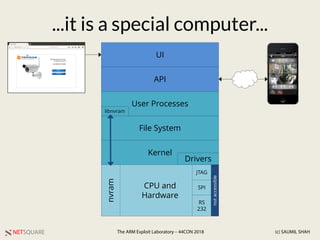
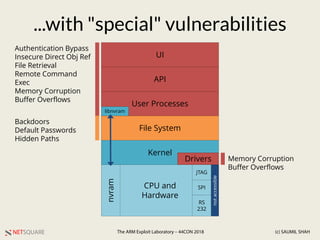
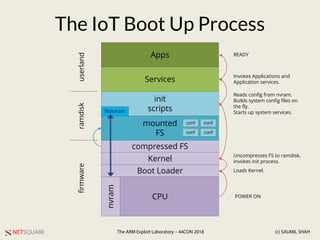
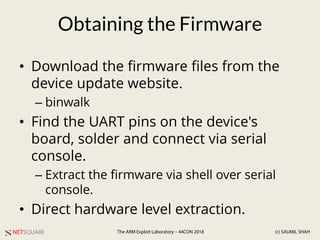
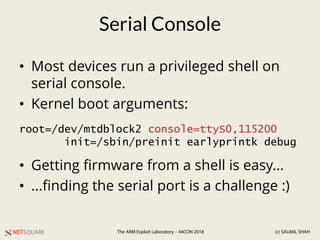
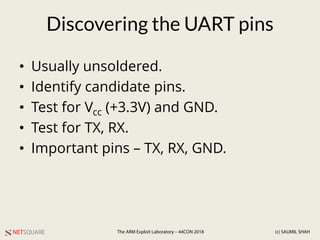
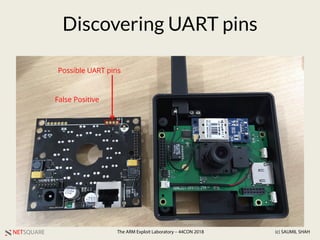
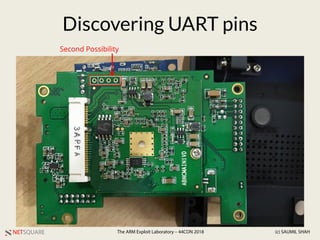
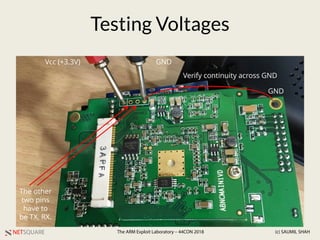
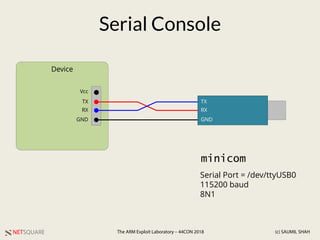
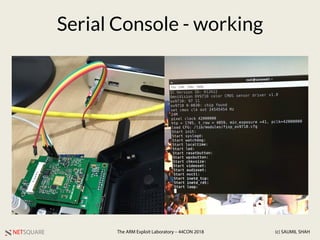
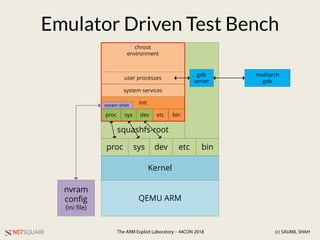
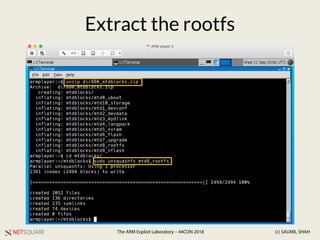
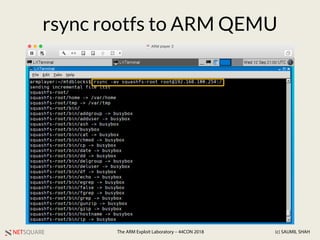
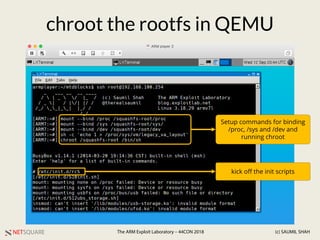
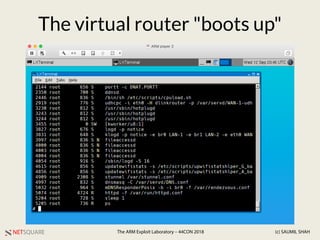
Saumil Shah gives a presentation on extracting firmware from IoT devices and emulating it using QEMU. He discusses obtaining firmware by downloading from the manufacturer's site, extracting over a UART serial connection, or directly from hardware. The case study looks at a DLink DIR-880L router. The extracted firmware is transferred to a QEMU ARM VM and chrooted to emulate the device and allow debugging and testing.